We continue our series of articles about NGFW for small businesses, let me remind you that we are considering a new model range of the 1500 series. IN cycle I mentioned one of the most useful options when buying an SMB device - the supply of gateways with built-in Mobile Access licenses (from 100 to 200 users, depending on the model). In this article, we will look at configuring VPN for 1500 series gateways that come with Gaia 80.20 Embedded preinstalled. Here is a summary:
- VPN capabilities for SMB.
- Organization of Remote Access for a small office.
- Available clients to connect.
1. VPN features for SMB
In order to prepare today's material, the official version R80.20.05 (up-to-date at the time of publication of the article). Accordingly, in terms of VPN with Gaia 80.20 Embedded, there is support for:
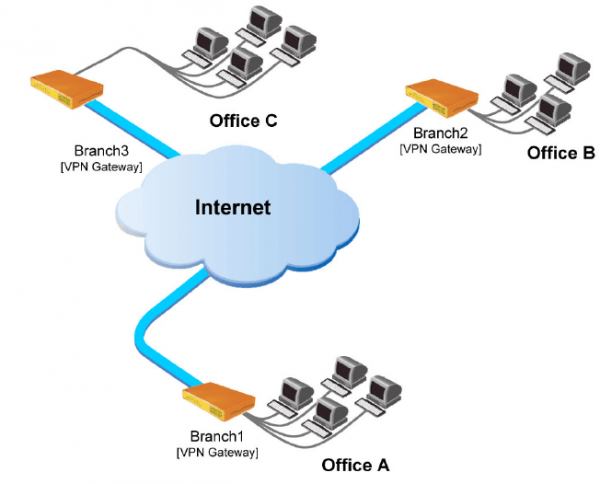
- site-to-site. Creation of VPN tunnels between your offices, where users can work as if they were on the same “local” network.

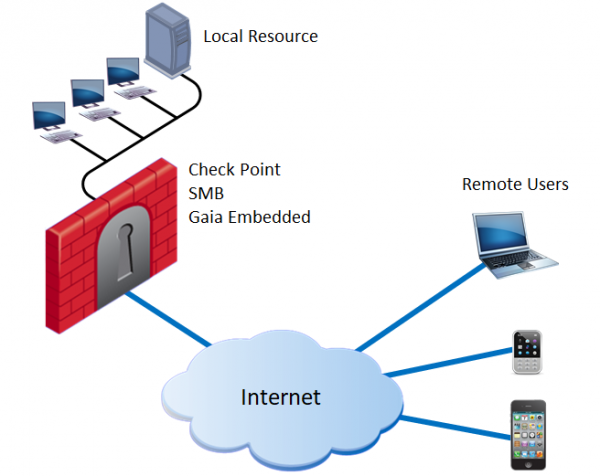
- remote access. Remote connection to your office resources using user end devices (PCs, mobile phones, etc.). Additionally, there is SSL Network Extender, it allows you to publish individual applications and run them using the Java Applet by connecting via SSL. Note: not to be confused with Mobile Access Portal (no support on Gaia Embedded).

Additional features I highly recommend the author's course TS Solution - it reveals Check Point technologies in terms of VPN, touches on licensing issues and contains detailed configuration instructions.
2. Remote Access for Small Office
We will start organizing a remote connection to your office:
- In order for users to be able to build a VPN tunnel with a gateway, you need to have a public IP address. If you have already gone through the initial setup ( from the cycle), then, as a rule, the External Link is already active. Information can be found by going to the Gaia Portal: Device → Network → Internet

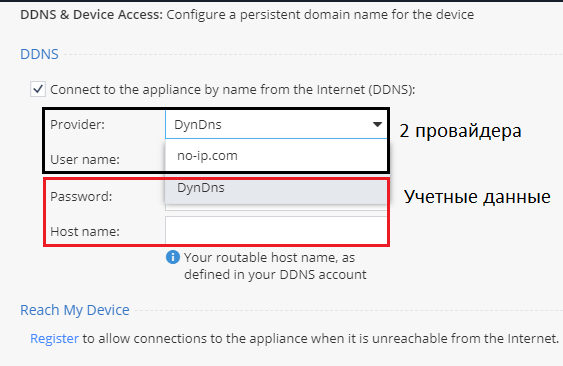
In the event that your company uses a dynamic public IP address, then you can set Dynamic DNS. Go to Device → DDNS & Device Access

Currently, there is support from two providers: DynDns and no-ip.com. To activate the option, you need to enter your credentials (login, password).
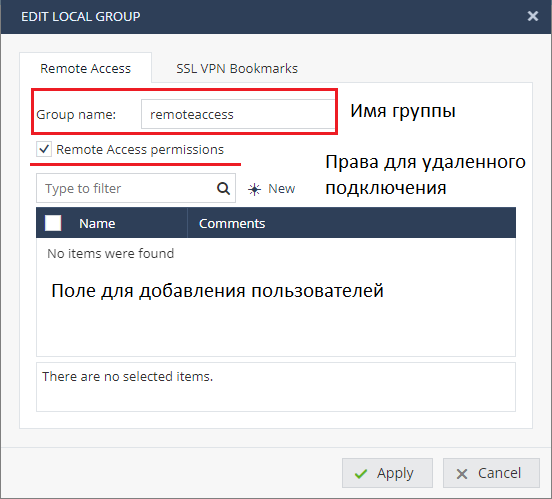
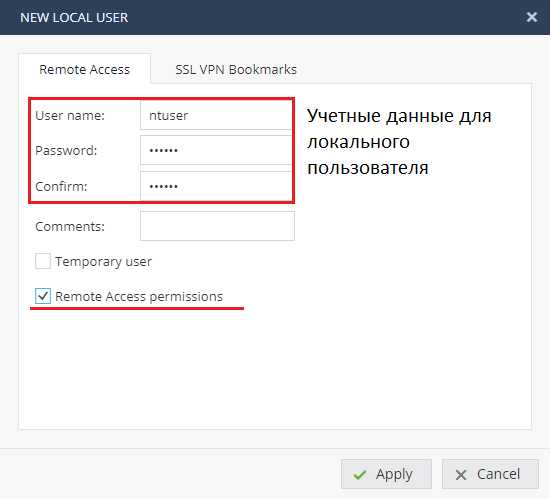
- Next, create a user account, it will come in handy for testing the settings: VPN → Remote Access → Remote Access Users

In the group (for example: remoteaccess) we will create a user following the instructions on the screenshot. The account setup is standard, we set the login and password, and additionally enable the Remote Access permissions option.

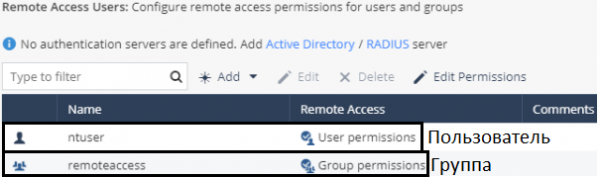
If you successfully applied the settings, then two objects should appear: local user, local group of users.

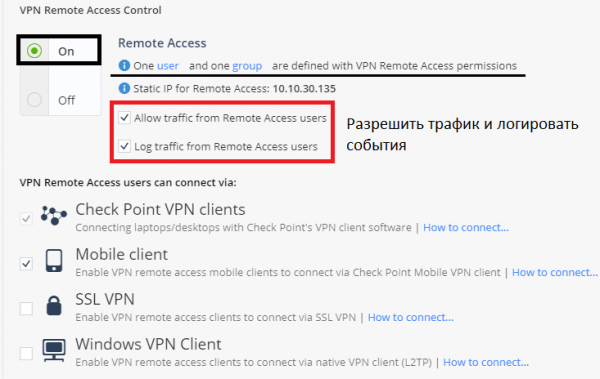
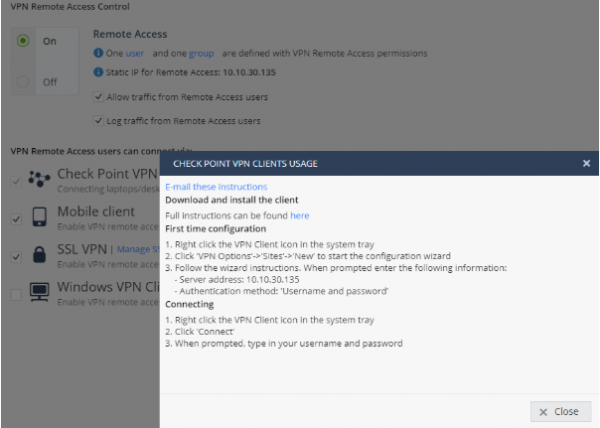
- The next step is to go to VPN → Remote Access → Blade Control. Make sure you have the blade enabled and allow traffic from remote users.

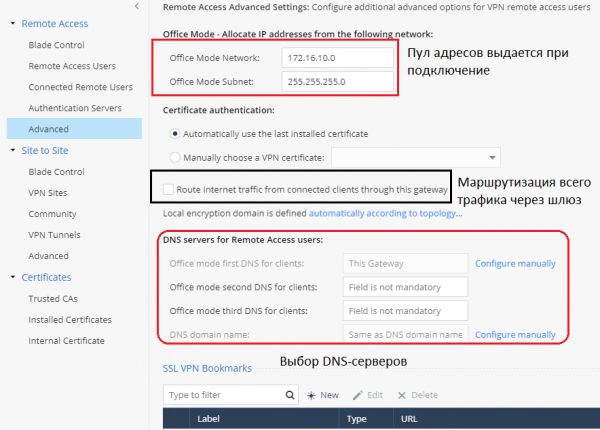
- *The above is a minimum set of steps to set up Remote Access. But before we test the connection, let's explore additional settings by going to the tab VPN → Remote Access → Advanced

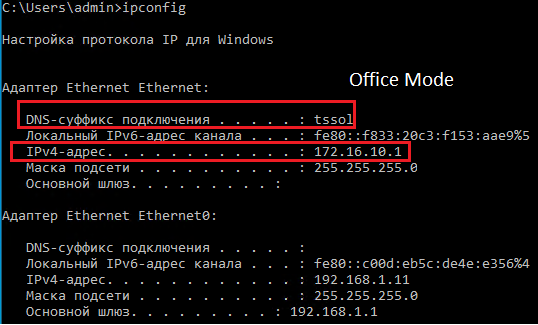
Based on the current settings, we see that when connecting, remote users will receive an IP address from the 172.16.11.0/24 network, thanks to the Office Mode option. This is more than enough to use 200 competitive licenses (listed for 1590 NGFW Check Point).
Option "Route Internet traffic from connected clients through this gateway" is optional and is responsible for routing all traffic from the remote user through the gateway (including Internet connections). This allows you to inspect the user's traffic and protect his workstation from various threats and malware.
- *Working with Access Policies for Remote Access
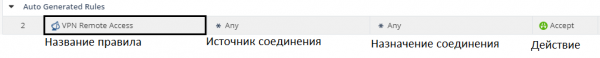
After we configured Remote Access, an automatic access rule was created at the Firewall level, to view it you need to go to the tab: Access Policy → Firewall → Policy

In this case, remote users included in the previously created group will be able to access all internal company resources, I note that the rule is located in the general section “Incoming, Internal and VPN traffic”. In order to allow traffic from VPN users to the Internet, you will need to create a separate rule in the general section “Outgoing access to the Internet".
Finally, we need to make sure that the user can successfully create a VPN tunnel to our NGFW gateway and access the company's internal resources. To do this, you need to install a VPN client on the host being tested, the help is attached For loading. After installation, you will need to carry out the standard procedure for adding a new site (the public IP address of your gateway is indicated). For convenience, the process is presented as a GIF

When the connection is already established, check the received IP address on the host machine using the command in CMD: ipconfig
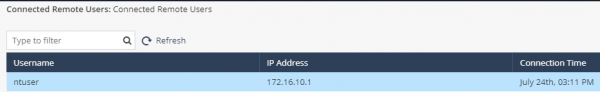
We made sure that the virtual network adapter received an IP address from the Office Mode of our NGFW, packets are sent successfully. To complete, we can go to the Gaia Portal: VPN → Remote Access → Connected Remote Users

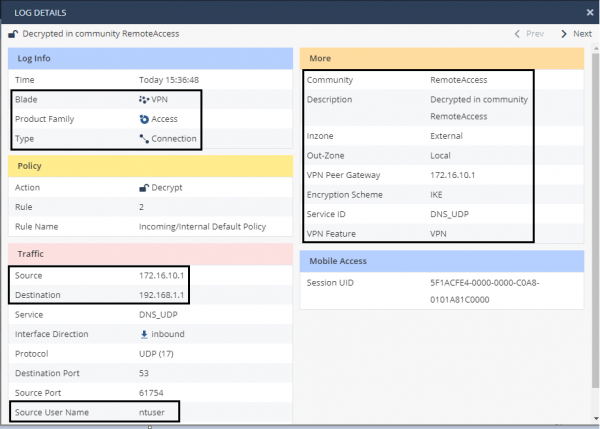
The user “ntuser” is displayed as connected, check the event logging by going to Logs & Monitoring → Security Logs

The connection is logged, the source is the IP address: 172.16.10.1 - this is the address received by our user through the Office Mode.
3. Supported Clients for Remote Access
After we have reviewed the procedure for setting up a remote connection to your office using NGFW Check Point of the SMB family, I would like to write about client support for various devices:
- Mobile Client ( / )
- L2TP Native Client (Check Point claims support for Microsoft's native VPN application).
A variety of supported operating systems and devices will allow you to use your license that comes with NGFW to the fullest. In order to configure a separate device there is a convenient option “How to connect”

It automatically generates steps according to your settings, which will allow administrators to easily install new clients.
Conclusion: Summing up this article, we examined the VPN capabilities for NGFW Check Point of the SMB family. Next, we described the steps for setting up Remote Access, in the case of a remote connection of users to the office, after studying the monitoring tools. At the end of the article, we talked about the available clients and connection options for Remote Access. Thus, your branch office will be able to ensure the continuity and security of employees using VPN technologies, despite various external threats and factors.
. Stay tuned (, , , , ).
Source: habr.com