In the post, we will tell you how the OceanLotus cybergroup (APT32 and APT-C-00) recently used one of the publicly available exploits for , memory corruption vulnerabilities in Microsoft Office, and how the group's malware ensures persistence on compromised systems without leaving traces. Next, we describe how, since the beginning of 2019, the group has been using self-extracting archives to run code.
OceanLotus specializes in cyber espionage, the priority targets are the countries of Southeast Asia. Attackers forge documents that attract the attention of potential victims in order to convince them to carry out a backdoor, and also work on the development of tools. The methods used to create honeypots vary in different attacks - from "double extension" files, self-extracting archives, macro documents, to well-known exploits.
Using the exploit in Microsoft Equation Editor
In mid-2018, OceanLotus ran a campaign exploiting the CVE-2017-11882 vulnerability. One of the malicious documents of the cybergroup was analyzed by 360 Threat Intelligence Center specialists (), including a detailed description of the exploit. The post below is an overview of such a malicious document.
The first stage
Document FW Report on demonstration of former CNRP in Republic of Korea.doc (sha-1: D1357B284C951470066AAA7A8228190B88A5C7C3) is similar to that mentioned in the study above. It is interesting in that it is aimed at users who are interested in Cambodian politics (CNRP - Cambodia National Salvation Party, dissolved at the end of 2017). Despite the .doc extension, the document is in RTF format (see the figure below), contains junk code, and is also garbled.
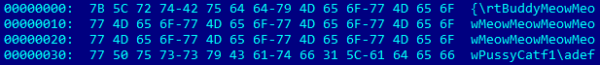
Figure 1. Garbage in RTF
Despite the presence of malformed elements, Word successfully opens this RTF file. As you can see in Figure 2, here is an EQNOLEFILEHDR structure at offset 0xC00 followed by an MTEF header and then an MTEF entry (Figure 3) for the font.
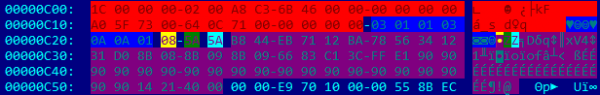
Figure 2. FONT Record Values
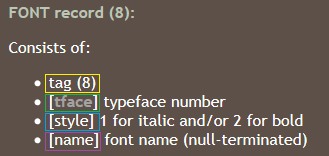
Figure 3.
Possible field overflow name, because its size is not checked before copying. Too long name triggers the vulnerability. As you can see from the contents of the RTF file (offset 0xC26 in Figure 2), the buffer is filled with shellcode followed by a dummy command (0x90) and return address 0x402114. The address is a dialog element in EQNEDT32.exepointing to instructions RET. This causes EIP to point to the start of the field nameThe containing the shellcode.
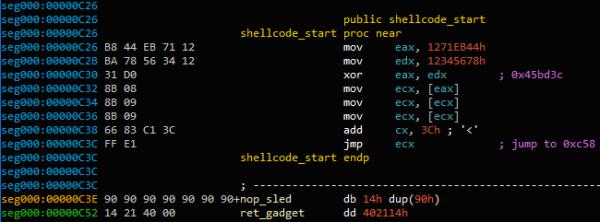
Figure 4. Beginning of the exploit shellcode
Address 0x45BD3C stores a variable that is dereferenced until it reaches a pointer to the currently loaded structure MTEFData. Here is the rest of the shellcode.
The purpose of the shellcode is to execute the second piece of shellcode embedded in the open document. First, the original shellcode tries to find the file descriptor of the open document by iterating over all system descriptors (NtQuerySystemInformation with argument SystemExtendedHandleInformation) and checking if they match PID descriptor and PID process WinWord and whether the document was opened with an access mask - 0x12019F.
To confirm that the correct handle was found (and not the handle of another open document), the contents of the file are displayed using the function CreateFileMapping, and the shellcode checks if the last four bytes of the document match "yyyy» (Egg Hunting method). Once a match is found, the document is copied to a temporary folder (GetTempPath) as ole.dll. Then the last 12 bytes of the document are read.
![]()
Figure 5. End-of-Document Markers
32-bit value between markers AABBCCDD и yyyy is the offset of the next shellcode. It is called with a function CreateThread. Extracted the same shellcode used by the OceanLotus group earlier. , which we released in March 2018, is still running for the second stage dump.
The second stage
Extracting Components
File and directory names are chosen dynamically. The code randomly chooses the name of an executable or DLL file in C:Windowssystem32. It then makes a request to its resources and retrieves the field FileDescription to use as the folder name. If that doesn't work, the code randomly selects a folder name from the directories %ProgramFiles% or C:Windows (from GetWindowsDirectoryW). It avoids using a name that might conflict with existing files and ensures that it does not contain the following words: windows, Microsoft, desktop, system, system32 or syswow64. If the directory already exists, "NLS_{6 characters}" is appended to the name.
Resource 0x102 parsed and files dumped into %ProgramFiles% or %AppData%, to a folder selected at random. Creation time changed to have the same values as kernel32.dll.
For example, here is the folder and list of files created by selecting the executable C:Windowssystem32TCPSVCS.exe as a data source.
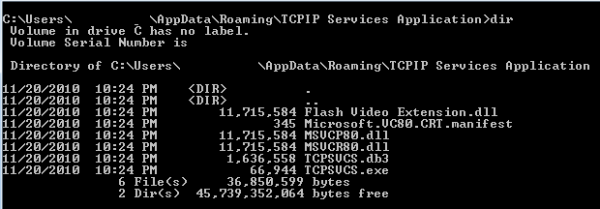
Figure 6. Extraction of various components
Resource Structure 0x102 in a dropper is quite complicated. In a nutshell, it contains:
- filenames
— File size and content
— Compression format (COMPRESSION_FORMAT_LZNT1used by the function RtlDecompressBuffer)
The first file is dumped as TCPSVCS.exe, which is legitimate AcroTranscoder.exe (according to FileDescription, SHA-1: 2896738693A8F36CC7AD83EF1FA46F82F32BE5A3).
You may have noticed that some DLL files are larger than 11MB. This is because a large contiguous buffer of random data is placed inside the executable. It is possible that this is a way to avoid detection by some security products.
Ensuring persistence
Resource 0x101 in the dropper contains two 32-bit integers that specify how persistence should be enforced. The value of the first specifies how the malware will persist without administrator rights.
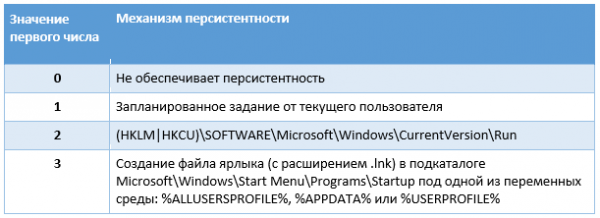
Table 1. Non-Administrator Persistence Mechanism
The value of the second integer specifies how the malware should ensure persistence by running with administrative privileges.
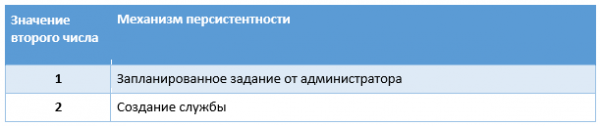
Table 2. Administrator Persistence Mechanism
The service name is the file name without the extension; the display name is the name of the folder, but if it already exists, the string “Revision 1” (the number increases until an unused name is found). The operators have taken care that the persistence through the service is resilient - in case of a failure, the service must be restarted after 1 second. Then the value WOW64 The new registry key for the service is set to 4, indicating that this is a 32-bit service.
A scheduled task is created through several COM interfaces: ITaskScheduler, ITask, ITaskTrigger, IPersistFile и ITaskScheduler. Essentially, the malware creates a hidden task, sets the account information along with the current user or administrator information, and then sets the trigger.
This is a daily task with a duration of 24 hours and intervals between two runs of 10 minutes, which means that it will run constantly.
Malicious Bit
In our example, the executable TCPSVCS.exe (AcroTranscoder.exe) is legitimate software that loads the DLLs that are dropped with it. In this case, it is of interest Flash Video Extension.dll.
Its function DLLMain just calls another function. There are some fuzzy predicates:
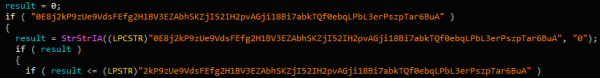
Figure 7. Fuzzy predicates
After these misleading checks, the code gets a section .text File TCPSVCS.exe, changes its protection to PAGE_EXECUTE_READWRITE and overwrites it with dummy instructions:
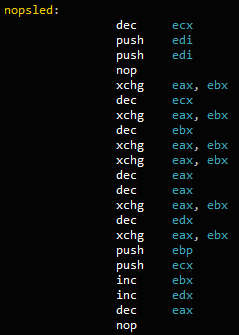
Figure 8. Sequence of instructions
At the end to the address of the function FLVCore::Uninitialize(void), exported Flash Video Extension.dll, the instruction is added CALL. This means that after the malicious DLL is loaded, when the runtime calls WinMain в TCPSVCS.exe, the instruction pointer will point to NOP, resulting in calling FLVCore::Uninitialize(void), next stage.
The function simply creates a mutex starting with {181C8480-A975-411C-AB0A-630DB8B0A221}followed by the current username. It then reads the dumped *.db3 file, which contains position-independent code, and uses CreateThread to execute content.
The content of the *.db3 file is the shellcode that the OceanLotus team typically uses. We again successfully decompressed its payload using the emulator script we published. .
The script retrieves the final stage. This component is a backdoor that we have already analyzed in . This can be determined by the GUID {A96B020F-0000-466F-A96D-A91BBF8EAC96} binary file. The malware configuration is still encrypted in the PE resource. It has roughly the same configuration, but the C&C servers are different from the previous ones:
- andreagahuvrauvin[.]com
- byronorenstein[.]com
- stienollmache[.]xyz
The OceanLotus group again demonstrates a combination of different techniques to avoid detection. They returned with a "finished" scheme of the infection process. By choosing random names and filling executables with random data, they reduce the number of reliable IoCs (based on hashes and filenames). Moreover, by using third party DLL loading, attackers only need to remove the legitimate binary AcroTranscoder.
Self-extracting archives
After RTF files, the group switched to self-extracting (SFX) archives with common document icons to further confuse the user. Threatbook wrote about it (). Upon startup, self-extracting RAR files are dumped and DLLs with the .ocx extension are executed, the final payload of which was previously documented {A96B020F-0000-466F-A96D-A91BBF8EAC96}.dll. Since mid-January 2019, OceanLotus has been reusing this technique, but changing some configurations over time. In this section, we will talk about the technique and changes.
Creating a lure
Document THICH-THONG-LAC-HANH-THAP-THIEN-VIET-NAM (1).EXE (sha-1: AC10F5B1D5ECAB22B7B418D6E98FA18E32BBDEAB) was first found in 2018. This SFX file was created with the mind - in the description (Version info) says it's a JPEG image. The SFX script looks like this:
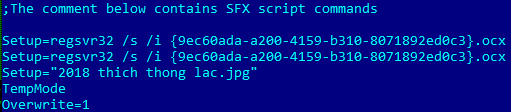
Figure 9. SFX Commands
The malware resets {9ec60ada-a200-4159-b310-8071892ed0c3}.ocx (sha-1: EFAC23B0E6395B1178BCF7086F72344B24C04DCC), as well as a picture 2018 thich thong lac.jpg.
The decoy image looks like this:
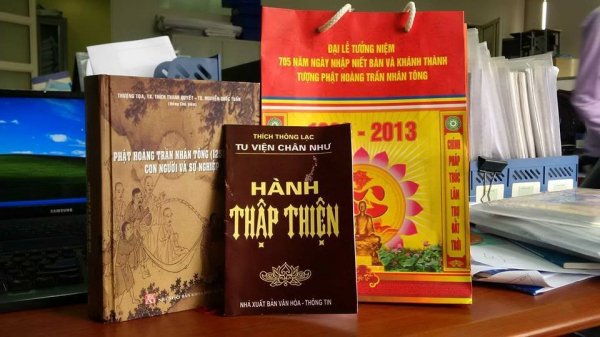
Figure 10. Decoy Image
You may have noticed that the first two lines in the SFX script call the OCX file twice, but this is not an error.
{9ec60ada-a200-4159-b310-8071892ed0c3}.ocx (ShLd.dll)
The control flow of the OCX file is very similar to other OceanLotus components - many command sequences JZ/JNZ и PUSH/RETinterleaved with junk code.
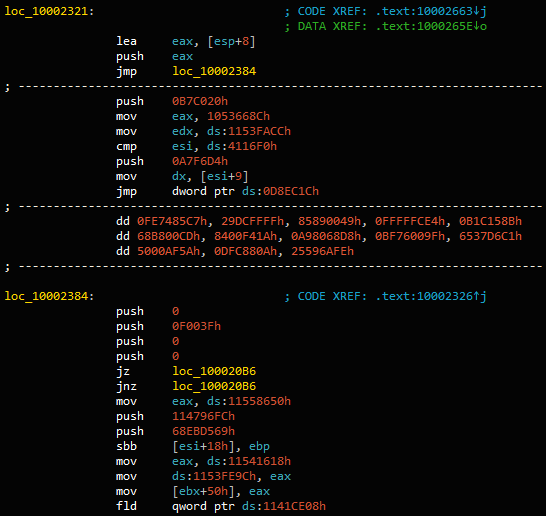
Figure 11. Obfuscated code
After filtering the garbage code, the export DllRegisterServer, called regsvr32.exe, as follows:
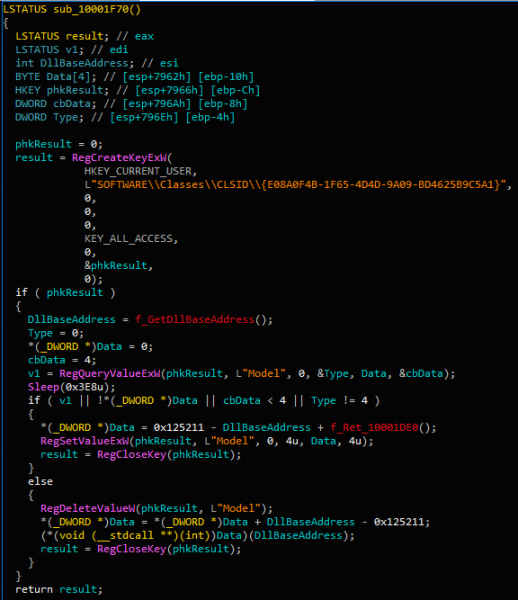
Figure 12. Main installer code
Basically, the first time you call DllRegisterServer export sets registry value HKCUSOFTWAREClassesCLSID{E08A0F4B-1F65-4D4D-9A09-BD4625B9C5A1}Model for encrypted offset in DLL (0x10001DE0).
When the function is called a second time, it reads the same value and executes at that address. From here, the resource is read and executed, and many actions are performed in RAM.
The shellcode is the same PE loader used in past OceanLotus campaigns. It can be emulated with . In the end, he drops db293b825dcc419ba7dc2c49fa2757ee.dll, loads it into memory and executes DllEntry.
The DLL extracts the contents of its resource, decrypts (AES-256-CBC) and decompresses (LZMA) it. The resource has a specific format that is easy to decompile.
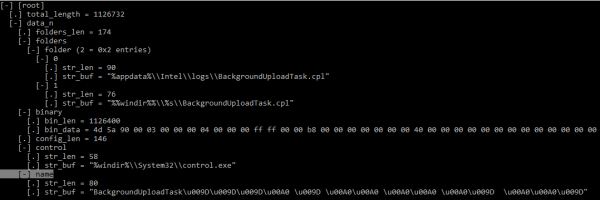
Figure 13. Installer configuration structure (KaitaiStruct Visualizer)
The configuration is set explicitly - depending on the privilege level, binary data will be written to %appdata%IntellogsBackgroundUploadTask.cpl or %windir%System32BackgroundUploadTask.cpl (or SysWOW64 for 64-bit systems).
Further persistence is ensured by creating a task named BackgroundUploadTask[junk].jobWhere [junk] is a set of bytes 0x9D и 0xA0.
Task application name %windir%System32control.exe, and the value of the parameter is the path to the downloaded binary file. The hidden task runs every day.
Structurally, a CPL file is a DLL with an internal name ac8e06de0a6c4483af9837d96504127e.dll, which exports the function CPlApplet. This file decrypts its only resource {A96B020F-0000-466F-A96D-A91BBF8EAC96}.dll, then loads that DLL and calls its only export DllEntry.
Backdoor configuration file
The backdoor configuration is encrypted and embedded in its resources. The structure of the configuration file is very similar to the previous one.
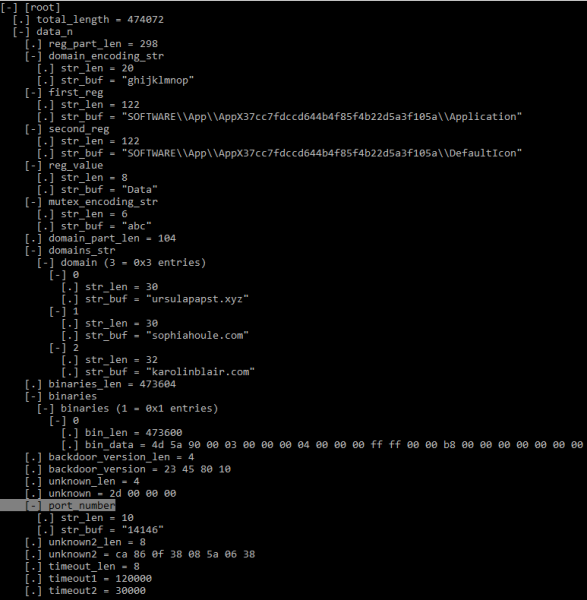
Figure 14. Backdoor configuration structure (KaitaiStruct Visualizer)
Despite the similar structure, the values of many fields have been updated compared to the data shown in .
The first element of the binary array contains the DLL (HttpProv.dll MD5: 2559738D1BD4A999126F900C7357B759), . But since the export name has been removed from the binary, the hashes don't match.
Additional research
Collecting samples, we paid attention to some characteristics. The sample just described appeared around July 2018, and others like it appeared more recently, in mid-January - early February 2019. An SFX archive was used as an infection vector, dropping a legitimate decoy document and a malicious OCX file.
Even though OceanLotus uses fake timestamps, we noticed that the timestamps of SFX and OCX files are always the same (0x57B0C36A (08/14/2016 @ 7:15pm UTC) and 0x498BE80F (02/06/2009 @ 7:34am UTC) respectively). This probably indicates that the authors have some kind of "constructor" that uses the same templates and just changes some characteristics.
Among the documents that we have studied since the beginning of 2018, there are various names indicating the attacking countries of interest:
- The New Contact Information Of Cambodia Media(New).xls.exe
- 李建香 (个人简历).exe (fake pdf document of a CV)
— feedback, Rally in USA from July 28-29, 2018.exe
Since the discovery of the backdoor {A96B020F-0000-466F-A96D-A91BBF8EAC96}.dll and the publication of its analysis by several researchers, we observed some changes in malware configuration data.
First, the authors began to remove names from the helper DLL DLLs (DNSprov.dll and two versions HttpProv.dll). Then the operators stopped packaging the third DLL (second version HttpProv.dll), choosing to embed just one.
Secondly, many backdoor configuration fields have been changed, probably to avoid detection as many IoCs have become available. Among the important fields modified by the authors are the following:
- changed registry key AppX (see IoCs)
- mutex encoding string ("def", "abc", "ghi")
- port number
Finally, all new versions analyzed have new C&Cs listed in the IoCs section.
Conclusions
OceanLotus continues to evolve. The cyber group is focused on refining and expanding the tools and lures. Authors mask malicious payloads with attention-grabbing documents that are relevant to the intended victims. They develop new circuits and also use publicly available tools such as the Equation Editor exploit. Moreover, they are improving the tools to reduce the number of artifacts left on victims' machines, thereby reducing the chance of being detected by antivirus software.
Indicators of compromise
Indicators of compromise as well as MITER ATT&CK attributes are available и .
Source: habr.com


