A cikin wannan sakon za mu gaya muku yadda ƙungiyar yanar gizo ta OceanLotus (APT32 da APT-C-00) kwanan nan suka yi amfani da ɗaya daga cikin fa'idodin da ake samu a bainar jama'a. , rashin lahani na ɓarna a ƙwaƙwalwar ajiya a cikin Microsoft Office, da kuma yadda malware ɗin ƙungiyar ke cim ma dagewa kan tsarin da ba su dace ba ba tare da barin wata alama ba. Na gaba, za mu bayyana yadda, tun farkon shekarar 2019, ƙungiyar ke amfani da rumbun adana kayan tarihi don gudanar da lambobi.
OceanLotus ya ƙware kan leƙen asiri ta yanar gizo, tare da fifikon manufofin ƙasashe a kudu maso gabashin Asiya. Maharan suna ƙirƙira takardu waɗanda ke jan hankalin waɗanda abin ya shafa don shawo kansu don aiwatar da bayan gida, kuma suna aiki kan haɓaka kayan aikin. Hanyoyin da ake amfani da su don ƙirƙirar sandunan zuma sun bambanta a ko'ina cikin hare-hare, daga fayilolin "tsawo biyu", rumbun adana bayanan kai, takardu tare da macros, zuwa abubuwan da aka sani.
Amfani da amfani a cikin Microsoft Equation Editan
A tsakiyar 2018, OceanLotus ya gudanar da yaƙin neman zaɓe yana cin gajiyar CVE-2017-11882. Ɗaya daga cikin takardun ɓarna na ƙungiyar yanar gizo an bincika ta ƙwararru daga Cibiyar Nazarin Barazana ta 360 (), gami da cikakken bayanin yadda ake amfani da su. Rubutun da ke ƙasa ya ƙunshi bayyani na irin wannan daftarin ɓarna.
Mataki na farko
Takardar FW Report on demonstration of former CNRP in Republic of Korea.doc (SHA-1: D1357B284C951470066AAA7A8228190B88A5C7C3) yayi kama da wanda aka ambata a cikin binciken da ke sama. Yana da ban sha'awa saboda yana nufin masu amfani da sha'awar siyasar Cambodia (CNRP - Cambodia National Rescue Party, narkar da a ƙarshen 2017). Duk da tsawaita .doc, takardar tana cikin tsarin RTF (duba hoton da ke ƙasa), yana ɗauke da lambar shara, kuma an murɗe ta.
Hoto 1. "Shara" a cikin RTF
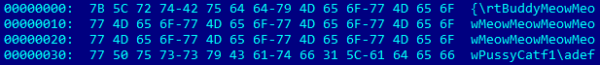
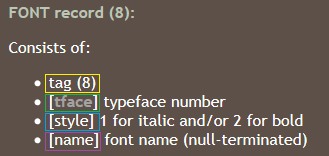
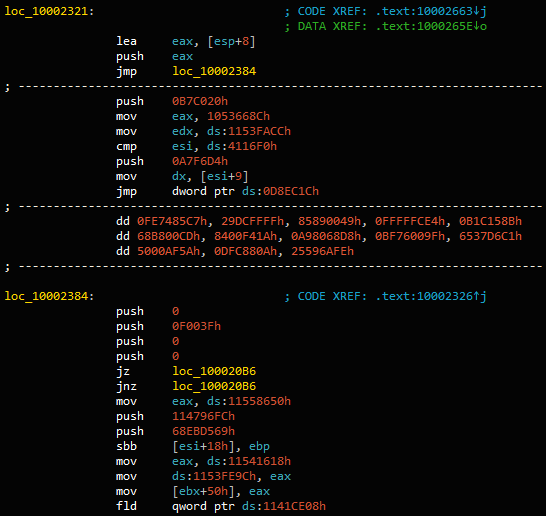
Ko da yake akwai abubuwan da aka yi garble, Word yana buɗe wannan fayil ɗin RTF cikin nasara. Kamar yadda kuke gani a hoto na 2, akwai tsarin EQNOLEFILEHDR a kashe 0xC00, sannan kuma mai taken MTEF, sannan shigarwar MTEF (Hoto 3) na font.
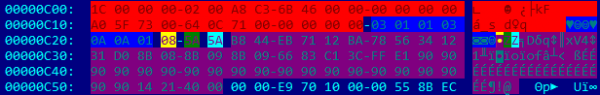
Hoto 2. Ƙimar shigar FONT
Hoto 3.
Yiwuwar ambaliya a cikin filin sunan, domin ba a duba girmansa kafin a kwafa. Sunan da ya yi tsayi da yawa yana haifar da rauni. Kamar yadda kuke gani daga abubuwan da ke cikin fayil ɗin RTF (kayyade 0xC26 a cikin Hoto 2), buffer yana cike da lambar ƙira ta bin umarnin dummy (0x90) da kuma mayar address 0x402114. Adireshin shine sashin tattaunawa a ciki EQNEDT32.exe, nuna umarni RET. Wannan yana sa EIP ya nuna farkon filin sunanmai dauke da lambar shell.
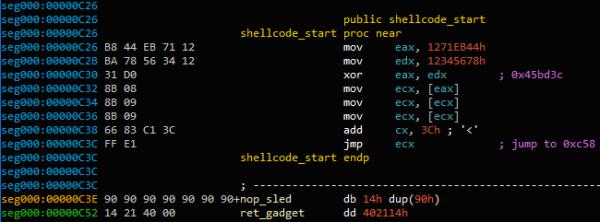
Hoto 4. Farkon amfani da shellcode
Adireshin 0x45BD3C yana adana mabambantan da aka yi watsi da shi har sai ya kai ga mai nuni ga tsarin da aka loda a halin yanzu MTEFData. Sauran shelcode yana nan.
Manufar lambar lambar ita ce aiwatar da yanki na biyu na shellcode da aka saka a cikin buɗaɗɗen daftarin aiki. Asalin lambar shell ɗin ta fara ƙoƙarin nemo mai siffanta fayil ɗin buɗaɗɗen daftarin aiki ta hanyar maimaita duk bayanan tsarin (NtQuerySystemInformation tare da jayayya SystemExtendedHandleInformation) da kuma duba idan sun dace PID siffantawa da PID tsari WinWord kuma ko an buɗe takardar da abin rufe fuska - 0x12019F.
Don tabbatar da cewa an samo hannun daidai (kuma ba hannun zuwa wani buɗaɗɗen takarda ba), ana nuna abubuwan da ke cikin fayil ɗin ta amfani da aikin. CreateFileMapping, kuma lambar harsashi tana bincika ko baiti huɗu na ƙarshe na daftarin aiki ya dace da shi"yyyy"(Hanyar farauta kwai). Da zarar an sami wasa, ana kwafin takardar zuwa babban fayil na wucin gadi (GetTempPath) Yaya ole.dll. Sannan ana karanta bytes 12 na ƙarshe na takaddar.
![]()
Hoto 5. Ƙarshen alamun daftarin aiki
Ƙimar 32-bit tsakanin alamomi AABBCCDD и yyyy shine kashe na gaba shellcode. Ana kiran shi ta amfani da aikin CreateThread. An fitar da lambar harsashi iri ɗaya wadda ƙungiyar OceanLotus ta yi amfani da ita a baya. , wanda muka saki a cikin Maris 2018, har yanzu yana aiki don juji mataki na biyu.
Mataki na biyu
Cire abubuwan da aka gyara
Fayil da sunayen kundin adireshi an zaɓi su da ƙarfi. Lambar ta zaɓi sunan mai aiwatarwa ko DLL a ciki ba da gangan ba C:Windowssystem32. Daga nan sai ta nemi albarkatunta kuma ta kwaso filin FileDescription don amfani azaman sunan babban fayil. Idan wannan bai yi aiki ba, lambar za ta zaɓi sunan babban fayil ba da gangan ba daga kundayen adireshi %ProgramFiles% ko C:Windows (из GetWindowsDirectoryW). Он избегает использования имени, которое может конфликтовать с существующими файлами, и следит за тем, чтобы оно не содержало следующие слова: windows, Microsoft, desktop, system, system32 ko syswow64. Idan kundin adireshi ya riga ya wanzu, "NLS_{6 characters}" an haɗa shi da sunan.
hanya 0x102 ana bincika kuma ana zubar da fayiloli a ciki %ProgramFiles% ko %AppData%, zuwa babban fayil da aka zaɓa ba da gangan ba. Canza lokacin halitta don samun ƙima iri ɗaya kamar kernel32.dll.
Misali, ga babban fayil da jerin fayilolin da aka ƙirƙira ta zaɓin mai aiwatarwa C:Windowssystem32TCPSVCS.exe a matsayin tushen bayanai.
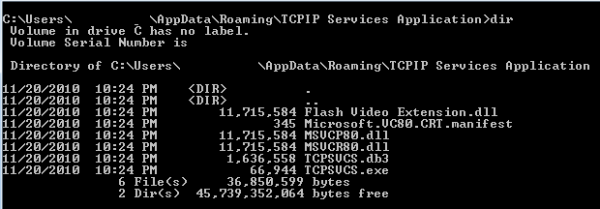
Hoto 6. Cire sassa daban-daban
Tsarin albarkatu 0x102 a dropper ne quite hadaddun. A taƙaice, ya ƙunshi:
- Sunayen fayil
- Girman fayil da abun ciki
- Tsarin matsawa (COMPRESSION_FORMAT_LZNT1, aikin da ake amfani dashi RtlDecompressBuffer)
An sake saita fayil ɗin farko azaman TCPSVCS.exe, wanda ya halatta AcroTranscoder.exe (bisa lafazin FileDescriptionSHA-1: 2896738693A8F36CC7AD83EF1FA46F82F32BE5A3).
Wataƙila kun lura cewa wasu fayilolin DLL sun fi 11 MB girma. Wannan saboda an sanya babban madaidaicin bayanan bazuwar a cikin fayil ɗin da za a iya aiwatarwa. Yana yiwuwa wannan wata hanya ce ta guje wa gano wasu samfuran tsaro.
Tabbatar da dagewa
hanya 0x101 a cikin dropper yana ƙunshe da lamba 32-bit guda biyu waɗanda ke ƙayyadad da yadda yakamata a samar da dagewa. Ƙimar ta farko tana ƙayyadaddun yadda malware zai ci gaba ba tare da haƙƙin mai gudanarwa ba.
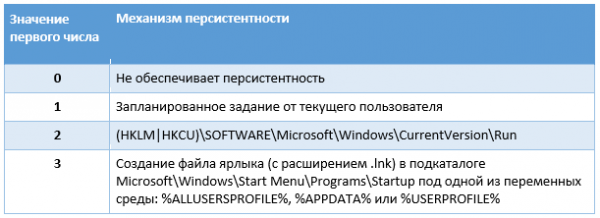
Tebur 1. Tsarin dagewa ba tare da haƙƙin gudanarwa ba
Ƙimar lamba ta biyu tana ƙayyadaddun yadda malware ya kamata ya cim ma nacewa yayin aiki tare da haƙƙin gudanarwa.
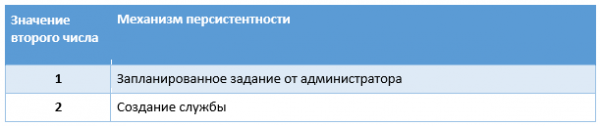
Tebur 2. Tsarin dagewa tare da haƙƙin gudanarwa
Sunan sabis shine sunan fayil ba tare da tsawo ba; sunan nuni shine sunan babban fayil ɗin, amma idan ya riga ya wanzu, an haɗa kirtani “Revision 1” (lambar tana ƙaruwa har sai an sami sunan da ba a yi amfani da shi ba). Masu aiki sun tabbatar da cewa dagewa ta hanyar sabis ɗin ya yi ƙarfi - idan akwai gazawa, yakamata a sake kunna sabis bayan 1 seconds. Sai darajar WOW64 An saita maɓallin rajista na sabon sabis zuwa 4, yana nuna cewa sabis ne na 32-bit.
An ƙirƙiri aikin da aka tsara ta hanyar mu'amalar COM da yawa: ITaskScheduler, ITask, ITaskTrigger, IPersistFile и ITaskScheduler. Mahimmanci, malware ɗin yana ƙirƙirar aiki mai ɓoye, yana saita bayanan asusun tare da mai amfani ko bayanin mai gudanarwa na yanzu, sannan saita faɗakarwa.
Wannan aiki ne na yau da kullun tare da tsawon sa'o'i 24 da tazara tsakanin kisa biyu na mintuna 10, wanda ke nufin zai ci gaba da gudana.
Abun mugunta
A cikin misalinmu, fayil ɗin da za a iya aiwatarwa TCPSVCS.exe (AcroTranscoder.exe) software ce ta halal wacce ke loda DLLs waɗanda aka sake saita su tare da ita. A wannan yanayin, yana da sha'awa Flash Video Extension.dll.
Ayyukansa DLLMain kawai kiran wani aiki. Wasu ma'anoni masu ban mamaki suna nan:
Hoto 7. Fuzzy predicates
Bayan waɗannan bincike na yaudara, lambar ta sami sashe .text fayil TCPSVCS.exe, canza kariya zuwa PAGE_EXECUTE_READWRITE kuma ya sake rubuta shi ta hanyar ƙara umarni masu ƙima:
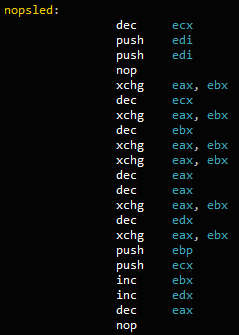
Hoto 8. Jerin umarni
A ƙarshen adireshin aikin FLVCore::Uninitialize(void), fitarwa Flash Video Extension.dll, an ƙara wa'azi CALL. Wannan yana nufin cewa bayan an ɗora DLL ɗin ɓarna, lokacin da ake kira lokacin aiki WinMain в TCPSVCS.exe, Ma'anar koyarwa za ta nuna NOP, haifar da FLVCore::Uninitialize(void), mataki na gaba.
Ayyukan kawai yana haifar da ɓata lokaci yana farawa da {181C8480-A975-411C-AB0A-630DB8B0A221}biye da sunan mai amfani na yanzu. Sannan yana karanta fayilolin * .db3 da aka zubar, wanda ya ƙunshi lambar mai zaman kanta, da amfani CreateThread don aiwatar da abun ciki.
Abin da ke cikin fayil * .db3 shine lambar shell wanda ƙungiyar OceanLotus ke amfani da ita. Mun sake samun nasarar cire kayan aikin sa ta amfani da rubutun kwaikwaiyo da muka buga .
Rubutun yana fitar da matakin ƙarshe. Wannan bangaren kofa ce ta baya, wacce muka riga muka yi nazari a ciki . Ana iya ƙaddara wannan ta GUID {A96B020F-0000-466F-A96D-A91BBF8EAC96} binary fayil. Tsarin malware har yanzu yana ɓoye a cikin albarkatun PE. Yana da kusan tsari iri ɗaya, amma sabobin C&C sun bambanta da waɗanda suka gabata:
- andreagahuvrauvin[.]com
- byronorenstein[.]com
- stienollmache[.]xyz
Ƙungiyar OceanLotus ta sake nuna haɗin fasaha daban-daban don guje wa ganowa. Sun dawo tare da tsarin "mai ladabi" na tsarin kamuwa da cuta. Ta zabar sunaye bazuwar da cika masu aiwatarwa tare da bayanan bazuwar, suna rage adadin amintattun IoCs (bisa hashes da sunayen fayil). Bugu da ƙari, godiya ga yin amfani da nauyin DLL na ɓangare na uku, maharan kawai suna buƙatar cire halaltaccen binary. AcroTranscoder.
Taskokin cire kansu
Bayan fayilolin RTF, ƙungiyar ta koma rumbun adana bayanan kai (SFX) tare da gumakan daftarin aiki gama gari don ƙara rikitar da mai amfani. Threadbook ya rubuta game da wannan (). Bayan ƙaddamarwa, ana sauke fayilolin RAR masu cire kansu kuma ana aiwatar da DLLs masu tsawo na .ocx, nauyin ƙarshe wanda aka rubuta a baya. {A96B020F-0000-466F-A96D-A91BBF8EAC96}.dll. Tun tsakiyar watan Janairu 2019, OceanLotus ke sake yin amfani da wannan dabarar, amma tana canza wasu jeri akan lokaci. A cikin wannan sashe za mu yi magana game da fasaha da canje-canje.
Ƙirƙirar Lure
Takardar THICH-THONG-LAC-HANH-THAP-THIEN-VIET-NAM (1).EXE (SHA-1: AC10F5B1D5ECAB22B7B418D6E98FA18E32BBDEAB) an fara gano shi a cikin 2018. An ƙirƙiri wannan fayil ɗin SFX cikin hikima - a cikin bayanin (Bayanin Sigogi) ya ce wannan hoton JPEG ne. Rubutun SFX yayi kama da haka:
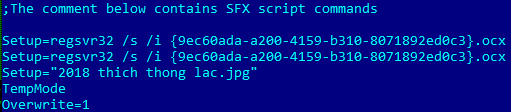
Hoto 9. Umurnin SFX
An sake saita malware {9ec60ada-a200-4159-b310-8071892ed0c3}.ocx (SHA-1: EFAC23B0E6395B1178BCF7086F72344B24C04DCC), da kuma hoto 2018 thich thong lac.jpg.
Hoton yaudara yayi kama da haka:
Hoto 10. Hoton lalata
Wataƙila kun lura cewa layi biyu na farko a cikin rubutun SFX suna kiran fayil ɗin OCX sau biyu, amma wannan ba kuskure ba ne.
{9ec60ada-a200-4159-b310-8071892ed0c3}.ocx (ShLd.dll)
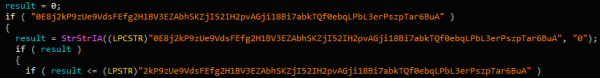
Gudun sarrafawa na fayil ɗin OCX yayi kama da sauran abubuwan OceanLotus - jerin umarni da yawa JZ/JNZ и PUSH/RET, musanya tare da lambar shara.
Hoto 11. Lambar da aka ɓoye
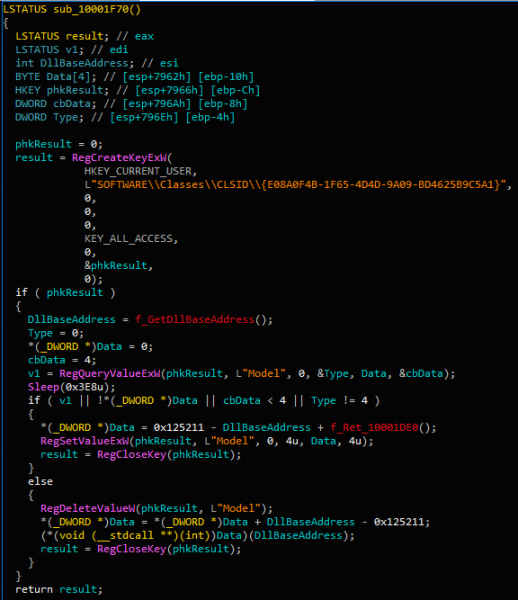
Bayan tace lambar takarce, fitarwa DllRegisterServer, ake kira regsvr32.exe, mai bi:
Hoto 12. Lambar mai sakawa na asali
Ainihin, akan kiran farko DllRegisterServer fitarwa yana saita ƙimar rajista HKCUSOFTWAREClassesCLSID{E08A0F4B-1F65-4D4D-9A09-BD4625B9C5A1}Model don ɓoye ɓoyayyen ɓoyayyen a cikin DLL (0x10001DE0).
Lokacin da aka kira aikin a karo na biyu, yana karanta ƙimar ɗaya kuma yana aiwatarwa a wannan adireshin. Daga nan ana karantawa kuma ana aiwatar da albarkatun da ayyuka da yawa a cikin RAM.
Lambar shell ɗin ita ce mai ɗaukar nauyin PE ɗaya da aka yi amfani da ita a yakin OceanLotus da suka gabata. Ana iya yin koyi da shi ta amfani da shi . A ƙarshe ya sake saitawa db293b825dcc419ba7dc2c49fa2757ee.dll, yana loda shi cikin ƙwaƙwalwar ajiya kuma yana aiwatarwa DllEntry.
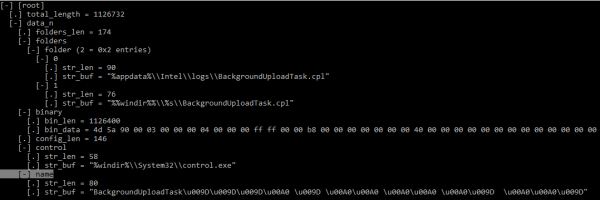
DLL tana fitar da abubuwan da ke cikin albarkatunta, ta yanke (AES-256-CBC) kuma tana ragewa (LZMA). Kayan yana da ƙayyadaddun tsari wanda ke da sauƙin rarrabawa.
Hoto 13. Tsarin saitin mai sakawa (KaitaiStruct Visualizer)
An ƙayyadadden ƙayyadaddun ƙayyadaddun ƙayyadaddun bayanai - ya danganta da matakin gata, za a rubuta bayanan binary zuwa ga %appdata%IntellogsBackgroundUploadTask.cpl ko %windir%System32BackgroundUploadTask.cpl (ko SysWOW64 don tsarin 64-bit).
Ana tabbatar da ƙarin dagewa ta hanyar ƙirƙirar ɗawainiya tare da sunan BackgroundUploadTask[junk].jobinda [junk] yana wakiltar saitin bytes 0x9D и 0xA0.
Sunan Aikace-aikacen Aiki %windir%System32control.exe, kuma ƙimar siga ita ce hanyar zuwa fayil ɗin binary da aka sauke. Ayyukan ɓoye yana gudana kowace rana.
A tsari, fayil ɗin CPL DLL ne mai suna na ciki ac8e06de0a6c4483af9837d96504127e.dll, wanda ke fitar da aiki CPlApplet. Wannan fayil ɗin yana ɓata albarkatun sa kawai {A96B020F-0000-466F-A96D-A91BBF8EAC96}.dll, sannan ya loda wannan DLL kuma ya kira fitarwa kawai DllEntry.
Fayil ɗin daidaitawar kofa
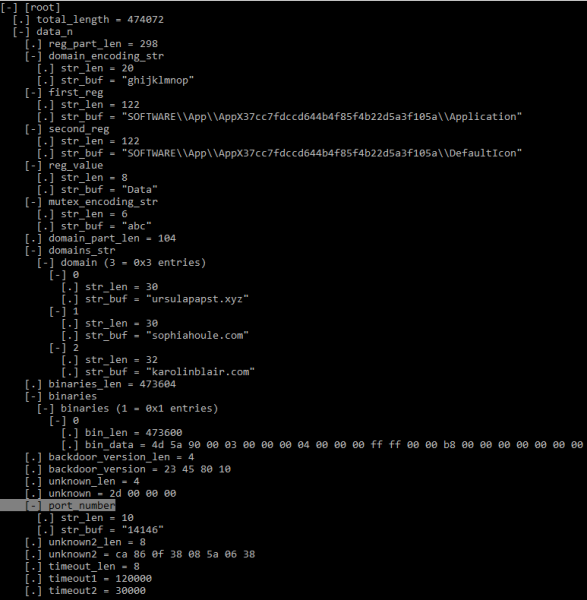
Ƙofar bayan gida yana ɓoye kuma an saka shi cikin albarkatunsa. Tsarin fayil ɗin daidaitawa yayi kama da na baya.
Hoto 14. Tsarin saitin bayan gida (KaitaiStruct Visualizer)
Kodayake tsarin yana kama da, yawancin ƙimar filin an sabunta su daga waɗanda aka nuna a ciki .
Kashin farko na tsarin binary ya ƙunshi DLL (HttpProv.dll MD5: 2559738D1BD4A999126F900C7357B759), . Amma tunda an cire sunan fitarwa daga binary, hashes ba su daidaita ba.
Ƙarin Bincike
Yayin tattara samfurori, mun lura da wasu halaye. Samfurin da aka bayyana yanzu ya bayyana a kusa da Yuli 2018, da wasu kamarsa sun bayyana a kwanan nan a tsakiyar Janairu zuwa farkon Fabrairu 2019. An yi amfani da ma'ajiyar taswirar SFX azaman ƙwayar cuta, zubar da halaltaccen takaddar yaudara da fayil ɗin OSX mai muni.
Ko da yake OceanLotus yana amfani da tambura na karya, mun lura cewa tamburan lokutan fayilolin SFX da OCX koyaushe iri ɗaya ne (0x57B0C36A (08/14/2016 @ 7:15pm UTC) da 0x498BE80F (02/06/2009 @ 7:34am UTC) bi da bi). Wannan mai yiwuwa yana nuna cewa marubutan suna da wani nau'i na "mai tsarawa" wanda ke amfani da samfurori iri ɗaya kuma kawai ya canza wasu halaye.
Daga cikin takardun da muka yi nazari tun farkon wannan shekara ta 2018, akwai sunaye daban-daban da ke nuni da kasashen da maharan ke da sha'awarsu:
- Sabon Bayanin Tuntuɓar Kambodiya Media(Sabo) .xls.exe
- 李建香 (个人简历).exe (takardun pdf na karya na CV)
- martani, Rally a Amurka daga Yuli 28-29, 2018.exe
Tunda aka gano kofar baya {A96B020F-0000-466F-A96D-A91BBF8EAC96}.dll da kuma buga bincikensa ta hanyar masu bincike da yawa, mun lura da wasu canje-canje a cikin bayanan saitin malware.
Da farko, marubutan sun fara cire sunaye daga DLLs masu taimako (DNSprov.dll da iri biyu HttpProv.dll). Daga nan sai masu aiki suka daina tattara DLL na uku (siffa ta biyu HttpProv.dll), zabar saka ɗaya kawai.
Na biyu, an canza filayen daidaitawar kofa da yawa, mai yuwuwa su gujewa ganowa yayin da yawancin IoC suka samu. Muhimman filayen da marubutan suka gyara sun haɗa da:
- An canza maɓallin rajista na AppX (duba IoCs)
- mutex encoding string ("def", "abc", "ghi")
- lambar tashar jiragen ruwa
A ƙarshe, duk sabbin nau'ikan da aka bincika suna da sabbin C&Cs da aka jera a sashin IoCs.
binciken
OceanLotus ya ci gaba da haɓakawa. Ƙungiyar yanar gizo ta mayar da hankali ga tsaftacewa da fadada kayan aiki da lalata. Marubuta suna ɓarna ɓoyayyiyar ɓacin rai ta hanyar amfani da takardu masu ɗaukar hankali waɗanda batunsu ya dace da waɗanda abin ya shafa. Suna haɓaka sabbin tsare-tsare kuma suna amfani da kayan aikin da ake samuwa a bainar jama'a, kamar amfani da Editan Equation. Bugu da ƙari, suna haɓaka kayan aiki don rage adadin kayan tarihi da suka rage a kan injinan waɗanda abin ya shafa, ta yadda za a rage damar ganowa ta software na riga-kafi.
Manuniya na yin sulhu
Ana samun alamun sasantawa da kuma halayen MITER ATT&CK и .
source: www.habr.com


