Wannan labarin ya ƙare jerin wallafe-wallafen da aka keɓe don nazarin malware. Mun gudanar da cikakken bincike game da fayil ɗin da ya kamu da cutar wanda wani kamfani na Turai ya karɓa ta imel kuma ya sami shirin AgentTesla kayan leken asiri a ciki. ya bayyana sakamakon binciken mataki-mataki na babban tsarin AgentTesla.
A yau, Ilya Pomerantsev, kwararre kan nazarin malware a CERT Group-IB, zai tattauna mataki na farko na nazarin malware-kwana-daki-daki-daki-daki-daki na AgentTesla-ta amfani da karamin karami uku daga kwararrun CERT Group-IB.
Yawanci, mataki na farko a cikin binciken malware shine cire kariya kamar fakiti, cryptor, kariya, ko loda. A mafi yawan lokuta, ana magance wannan matsalar ta hanyar ƙaddamar da malware da yin juji, amma akwai yanayin da wannan hanyar ba ta dace ba. Misali, idan malware ɗin mai ɓoye ne, idan yana kare yankunan ƙwaƙwalwar ajiyarsa daga zubarwa, idan lambar ta ƙunshi hanyoyin gano injin kama-da-wane, ko kuma idan malware ɗin ya sake yin aiki nan da nan bayan farawa. A irin waɗannan lokuta, ana amfani da abin da ake kira "Semi-automated" cire kayan aiki, ma'ana mai binciken yana da cikakken iko akan tsarin kuma yana iya shiga tsakani a kowane lokaci. Bari mu bincika wannan hanya ta amfani da samfurori guda uku daga dangin AgentTesla a matsayin misali. Wannan malware ba shi da lahani idan an kashe hanyar sadarwar sa.
Misali #1
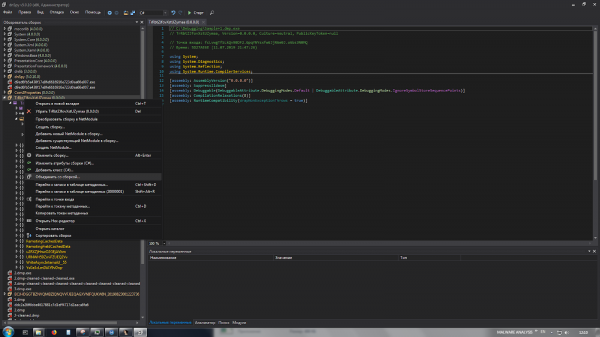
Fayil ɗin tushen takaddar MS Word ce wacce ke amfani da raunin CVE-2017-11882.
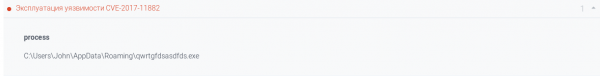
A sakamakon haka, ana zazzage kayan da aka biya kuma an ƙaddamar da shi.
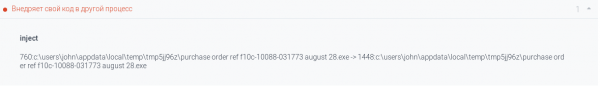
Binciken bishiyar tsari da alamomin ɗabi'a suna nuna allura a cikin tsarin RegAsm.exe.


Akwai alamomin halayen halayen AgentTesla.

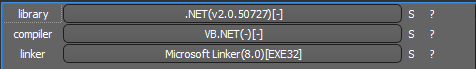
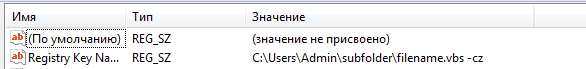
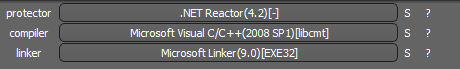
Samfurin da aka zazzage yana iya aiwatarwa .NET- fayil mai kariya ta kariya NET Reactor.
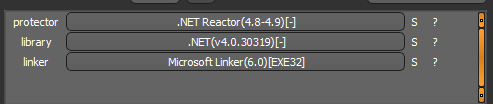
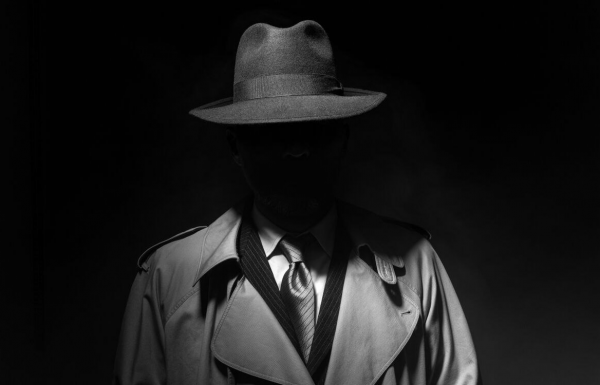
Bari mu bude shi a cikin mai amfani dnSpy x86 kuma mu matsa zuwa wurin shiga.
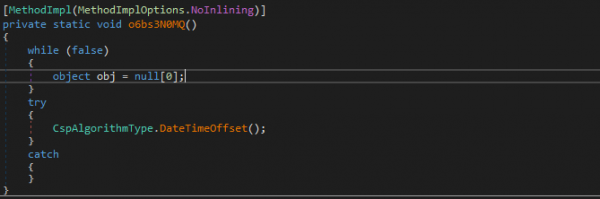
Shiga cikin aikin DateTimeOffset, za mu sami lambar farawa na sabon .NET- module. Bari mu shigar karya akan layin da muke sha'awar kuma muna gudanar da fayil ɗin.
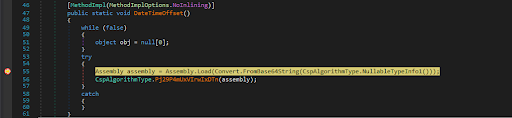
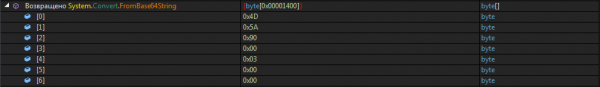
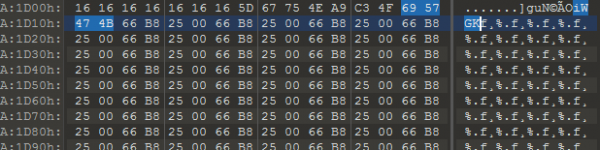
A cikin ɗaya daga cikin buffers ɗin da aka dawo za ku iya ganin sa hannun MZ (0x4D 0x5A). Mu ajiye shi.
Fayil ɗin da za a iya zubar da shi babban ɗakin karatu ne mai ƙarfi wanda ke aiki azaman mai ɗaukar kaya, watau, yana fitar da kayan aiki daga sashin albarkatun kuma ya ƙaddamar da shi.
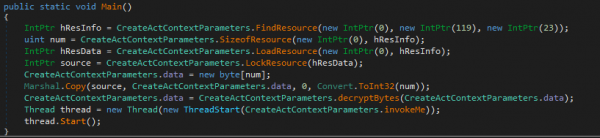
Koyaya, abubuwan da ake buƙata da kansu sun ɓace daga juji. Suna cikin samfurin iyaye.
Mai amfani dnSpy yana da fasaloli masu fa'ida guda biyu waɗanda zasu taimaka mana ƙirƙirar "Frankenstein" daga fayiloli guda biyu masu alaƙa da sauri.
- Na farko yana ba ku damar "manna" ɗakin karatu mai ƙarfi a cikin samfurin iyaye.

- Na biyu shine sake rubuta lambar aiki a wurin shigarwa don kiran hanyar da ake buƙata na shigar da ɗakin karatu mai ƙarfi.

Mun ajiye "Frankenstein" mu kuma sanya shi karya akan layin da ke dawo da buffer tare da abubuwan da aka ɓoye, kuma muna samar da juji mai kama da matakin da ya gabata.
An rubuta juji na biyu a ciki VB.NET fayil mai aiwatarwa wanda majiɓinci wanda muka saba da shi ya kiyaye shi ConfuserEx.
Bayan cire mai karewa, muna amfani da dokokin YARA da aka rubuta a baya kuma muna tabbatar da cewa malware ɗin da ba a tattara ba lallai ne AgentTesla.
![]()
Misali #2
Fayil ɗin tushen takaddar MS Excel ce. Macro da aka saka yana haifar da aiwatar da lambar mugunta.
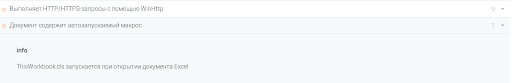
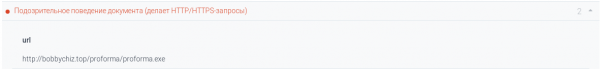
Wannan yana haifar da ƙaddamar da rubutun PowerShell.
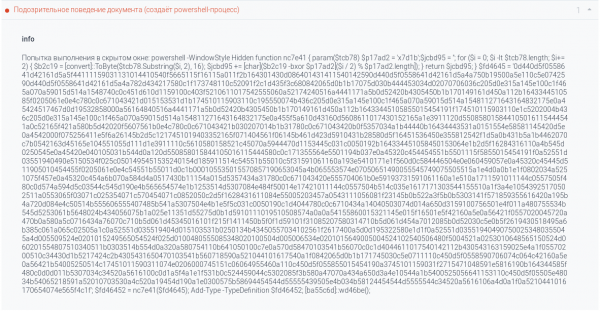
Rubutun yana ɓata lambar C # kuma yana canja wurin sarrafawa zuwa gare shi. Lambar ita kanta mai ɗaukar nauyi ce, kamar yadda ake iya gani daga rahoton sandbox.
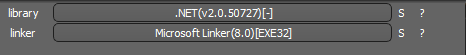
Abin da aka biya shi ne mai aiwatarwa .NET- fayil.
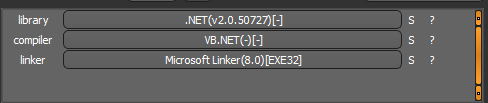
Buɗe fayil ɗin a ciki dnSpy x86, za ka ga an rufe ta. Muna cire obfuscation ta amfani da mai amfani di4 digo kuma mu koma ga bincike.
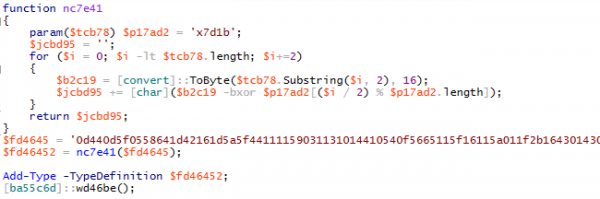
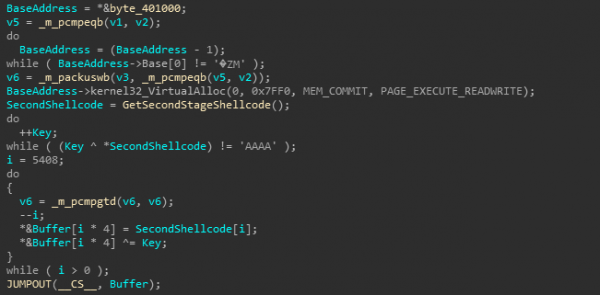
Yayin nazarin lambar, zaku iya samun aikin mai zuwa:
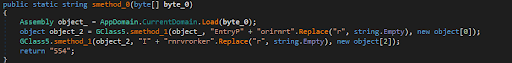
Layukan da aka ƙulla suna da ban mamaki EntryPoint и Kira. Mun sanya karya a layin farko, gudu kuma ajiye ƙimar buffer byte_0.
Juji kuma shine aikace-aikace akan .NET da kuma kariya ConfuserEx.
![]()
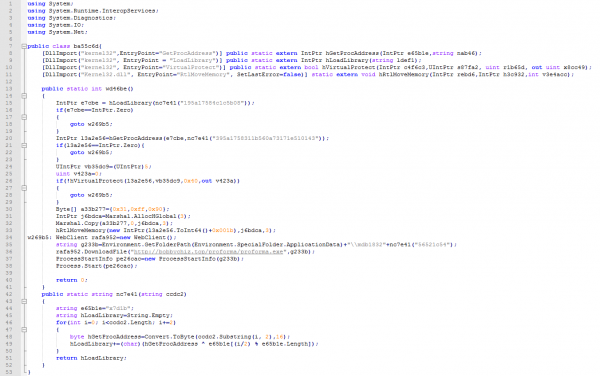
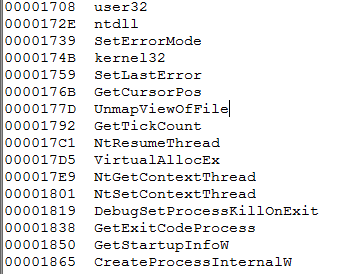
Cire abin rufe fuska ta amfani da di4 digo da loda shi dnSpyDaga bayanin fayil mun fahimci cewa muna fuskantar CyaX-Sharp Loader.
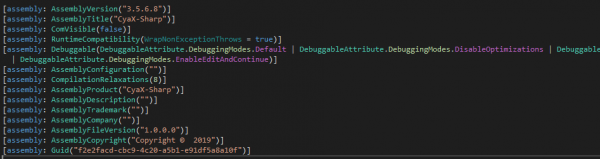
Wannan mai saukewa yana da ayyuka masu yawa na anti-bincike.
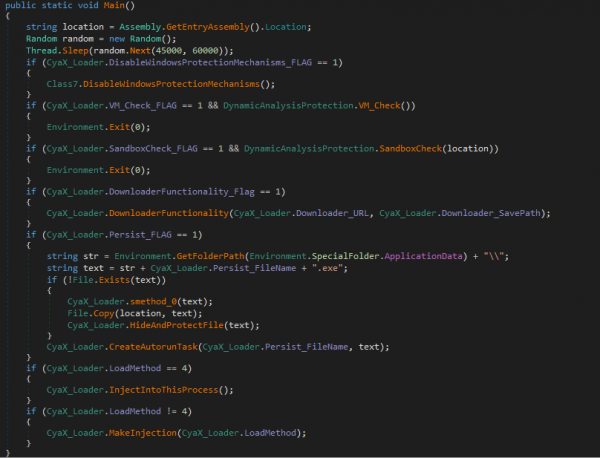
Wannan aikin ya haɗa da ƙetare ginannen tsarin tsaro na Windows, kashe Windows Defender, da gano akwatunan yashi da injuna. Yana iya sauke nauyin da aka biya daga cibiyar sadarwa ko adana shi a cikin sashin albarkatun. Ana ƙaddamar da ƙaddamarwa ta hanyar allura zuwa tsarin nata, kwafin nasa tsarin, ko tafiyar matakai. MSBuild.exe, vbc.exe и RegSvcs.exe dangane da sigar da maharin ya zaba.
Koyaya, a gare mu ba su da mahimmanci fiye da AntiDump-aiki wanda ya kara ConfuserExAna iya samun lambar tushe a .
Don musaki kariya, za mu yi amfani da damar dnSpy, wanda ke ba ka damar gyarawa IL- code.
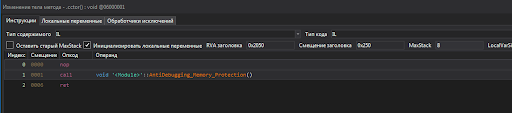
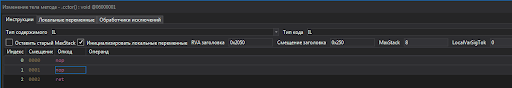
Muna ajiyewa da girka karya zuwa kitin kira na aikin ɓarnar kuɗin biya. Yana cikin babban maginin aji.
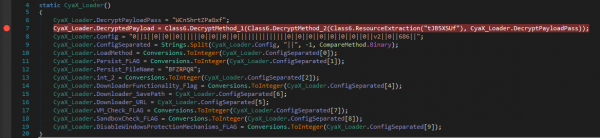
Muna kaddamar da zubar da kaya. Amfani da dokokin YAR da aka rubuta a baya, mun tabbatar da cewa wannan AgentTesla ne.
![]()
Misali #3
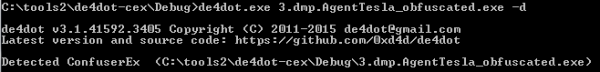
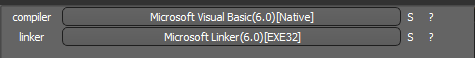
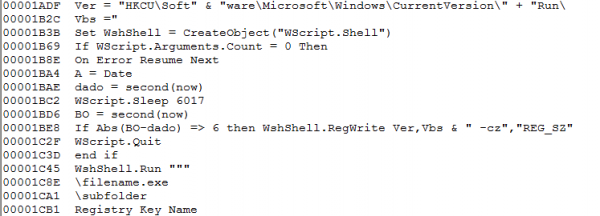
Fayil ɗin tushen abin aiwatarwa ne VB 'Yan Asalin PE32- fayil.
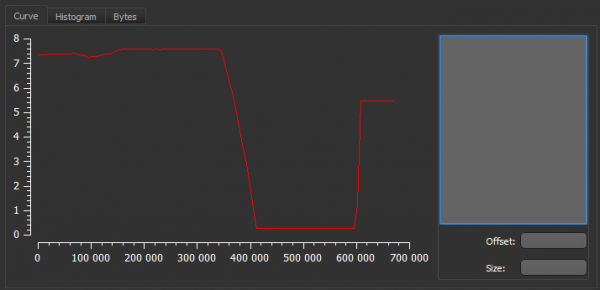
Binciken Entropy yana nuna kasancewar babban guntun ɓoyayyen bayanai.

Lokacin nazarin fam ɗin aikace-aikacen a Mai Rarraba VB Kuna iya lura da wani bakon bangon pixel.
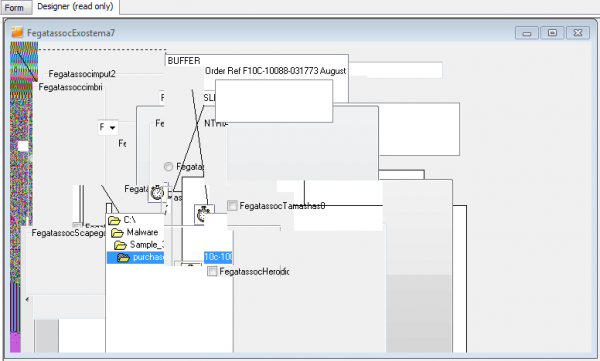
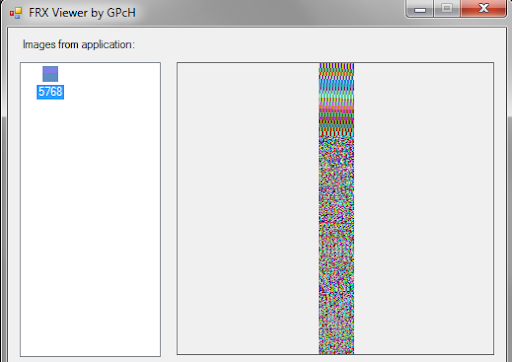
Entropy jadawali bmp- Hoton yayi kama da zanen entropy na ainihin fayil ɗin, kuma girman shine 85% na girman fayil ɗin.
Gaba ɗaya bayyanar hoton yana nuna amfani da steganography.
Bari mu kula da bayyanar itacen tsari, da kuma kasancewar alamar allurar.
![]()
Wannan yana nuna cewa ana ci gaba da kwashe kayan. Don masu lodin Kayayyakin Kaya (aka VBKrypt ko Farashin VBI) yana da alaƙa da amfani shellcode don fara aikin biya, da kuma yin allurar kanta.
Analysis a Mai Rarraba VB ya nuna gaban wani taron load a form FegatassocAirballoon2.
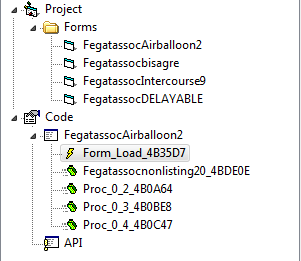
Mu ci gaba zuwa IDA pro Bari mu je zuwa ƙayyadadden adireshin kuma mu bincika aikin. An rufaffen lambar sosai. An gabatar da guntun da muke sha'awar a ƙasa.
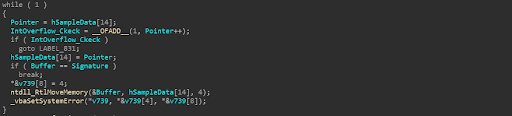
Anan, ana bincika sararin adireshin tsarin don sa hannu. Wannan tsarin yana da matukar tambaya.
Na farko, da scan fara adireshin 0x400100Wannan ƙimar tana tsaye kuma baya daidaitawa lokacin da aka matsa tushe. A karkashin yanayi mai kyau na greenhouse, zai nuna ƙarshen PE- babban fayil mai aiwatarwa. Duk da haka, bayanan ba a tsaye ba; darajarsa na iya canzawa, kuma neman ainihin adireshin sa hannun da ake so, kodayake ba zai cika ma'aunin ba, yana iya ɗaukar lokaci mai tsawo.
Na biyu, ma'anar sa hannu iWGKIna tsammanin a bayyane yake cewa 4 bytes ya yi ƙanƙanta don tabbatar da keɓantacce. Kuma idan aka ba da batu na farko, yiwuwar kuskure ya yi yawa.
A gaskiya ma, guntun da ake tambaya yana haɗe zuwa ƙarshen abin da aka samo a baya bmp- hotuna ta hanyar biya diyya 0xA1D0D.
Ayyuka Shellcode Ana aiwatar da shi a matakai biyu. Na farko ya haɗa da ƙaddamar da babban jiki. A wannan yanayin, maɓalli yana ƙayyade ta ƙarfin ƙarfi.
Za mu zubar da wanda aka ɓoye Shellcode kuma mu kalli layin.
Na farko, yanzu mun san aikin don ƙirƙirar tsarin yaro: Ƙirƙirar Tsarin CikiW.
Abu na biyu, mun fahimci tsarin gyarawa a cikin tsarin.
Bari mu koma ga ainihin tsari. Mu saka karya a kan Ƙirƙirar Tsarin CikiW kuma a ci gaba da aiwatar da hukuncin kisa. Na gaba, muna lura da haɗin gwiwa NtGetContextThread/NtSetContextThread, wanda ke canza adireshin farawa na aiwatarwa zuwa adireshin ShellCode.
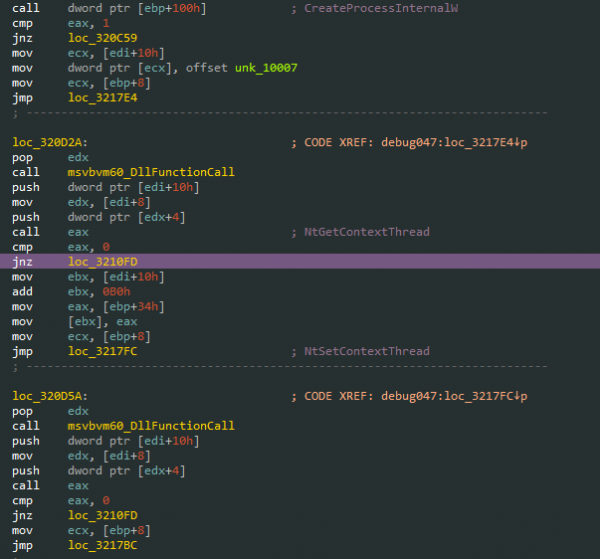
Muna haɗi zuwa tsarin da aka ƙirƙira tare da mai cirewa kuma kunna taron. Dakatar da load/cire kayan karatu, mu ci gaba da aiwatar da jira da zazzagewa .NET- dakunan karatu.
Na gaba, tare da taimakon Tsarin Hucker jujjuya yankunan da ke kunshe a cikin sigar da ba a cika kaya ba .NET- aikace-aikace.
Muna dakatar da duk matakai kuma muna cire kwafin malware wanda ya kasance mai tushe a cikin tsarin.
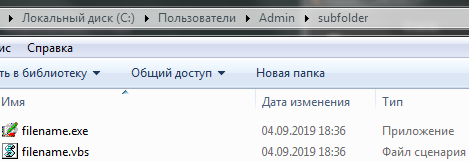
Fayil ɗin da aka zubar yana da kariya ta mai tsaro. NET Reactor, wanda za'a iya cirewa cikin sauƙi ta amfani da kayan aiki di4 digo.
Yin amfani da dokokin YARA da aka rubuta a baya, za mu iya tabbatar da cewa muna ma'amala da AgentTesla.
Bari mu taƙaita
Don haka, mun nuna tsarin cire kayan aiki na atomatik daki-daki ta amfani da ƙananan ƙararraki guda uku, sannan kuma mun gudanar da bincike na malware dangane da cikakken shari'ar, gano samfurin da ke ƙarƙashin bincike kamar AgentTesla, tabbatar da aikinsa, da kuma gano cikakken jerin alamomin sasantawa.
Binciken malware da muka gudanar yana buƙatar lokaci mai yawa da ƙoƙari, kuma wannan aikin ya kamata ya kasance da wani ma'aikaci mai sadaukarwa a cikin kamfanin, amma ba duk kamfanoni suna shirye su dauki wani manazarci ba.
Ɗayan sabis ɗin da Rukunin-IB's Forensics Computer Forensics da Malware Analysis Lab ke bayarwa shine martanin abin da ya faru ta yanar gizo. Don guje wa abokan ciniki ɓata lokaci don daidaita takardu da tattaunawa da su a tsakiyar harin yanar gizo, ƙungiyar-IB ta ƙaddamar. Mai riƙe da martani, sabis na amsa afkuwar abin da ya faru kafin biyan kuɗi wanda kuma ya haɗa da binciken malware. Ana iya samun ƙarin bayani game da wannan anan. .
Idan kuna son koyon yadda ake cire fakitin samfuran AgentTesla da kanku kuma ku ga yadda ƙwararrun ƙungiyar-IB CERT ke yin ta, zaku iya zazzage rikodi na webinar akan wannan batu. .
source: www.habr.com