Kab lus no tau sau nrog lub hom phiaj ntawm kev nthuav dav ntawm qhov twb muaj lawm , tab sis tham txog cov yam ntxwv ntawm kev sib txuas tshwj xeeb nrog Microsoft ActiveDirectory, thiab kuj ntxiv rau nws.
Hauv tsab xov xwm no kuv yuav qhia koj yuav ua li cas rau nruab thiab teeb tsa:
- keycloak yog ib qhov project qhib. Uas muab ib qho chaw nkag rau cov ntawv thov. Ua haujlwm nrog ntau cov txheej txheem, suav nrog LDAP thiab OpenID, uas yog qhov txaus siab rau peb.
- Keycloak gatekeeper - daim ntawv thov rov qab tso cai tso cai rau koj los ua ke kev tso cai ntawm Keycloak.
- Gangway - ib daim ntawv thov uas tsim cov config rau kubectl uas koj tuaj yeem nkag rau hauv OpenID thiab txuas mus rau Kubernetes API.
Kev tso cai ua haujlwm li cas hauv Kubernetes.
Peb tuaj yeem tswj hwm cov neeg siv / pab pawg txoj cai siv RBAC, ib pawg ntawm cov ntawv twb tau tsim txog qhov no, Kuv yuav tsis nyob ntawm qhov no kom ntxaws. Qhov teeb meem yog tias koj tuaj yeem siv RBAC txwv cov neeg siv txoj cai, tab sis Kubernetes tsis paub dab tsi txog cov neeg siv. Nws hloov tawm tias peb xav tau tus neeg siv khoom xa khoom hauv Kubernetes. Txhawm rau ua qhov no, peb yuav ntxiv ib tus neeg muab kev pabcuam rau Kuberntes OpenID, uas yuav qhia tau tias tus neeg siv no muaj tiag, thiab Kubernetes nws tus kheej yuav muab txoj cai rau nws.
Kev cob qhia
- Koj yuav xav tau Kubernetes pawg lossis minikube
- Active Directory
- Domains:
keycloak.example.org
kubernetes-dashboard.example.org
gangway.example.org - Daim ntawv pov thawj rau domains lossis daim ntawv pov thawj tus kheej kos npe
Kuv yuav tsis mus rau hauv kev nthuav dav yuav ua li cas los tsim ib daim ntawv pov thawj tus kheej kos npe; koj yuav tsum tsim 2 daim ntawv pov thawj, qhov no yog lub hauv paus (Certification Authority) thiab tus neeg siv khoom wildcard rau *.example.org domain.
Tom qab koj tau txais / sau cov ntawv pov thawj, koj yuav tsum ntxiv daim ntawv pov thawj tus neeg siv khoom rau Kubernetes; ua qhov no, tsim ib qho zais cia rau nws:
kubectl create secret tls tls-keycloak --cert=example.org.crt --key=example.org.pemTom ntej no peb yuav siv nws rau peb Ingress controller
Kev teeb tsa ntawm Keycloak
Kuv txiav txim siab tias txoj kev yooj yim tshaj plaws yog siv cov kev daws teeb meem npaj txhij rau qhov no, uas yog cov kab kos duab.
Nruab lub repository thiab hloov kho nws:
helm repo add codecentric https://codecentric.github.io/helm-charts
helm repo updateTsim cov ntaub ntawv keycloak.yml nrog cov ntsiab lus hauv qab no:
keycloak.yml
keycloak:
# Имя администратора
username: "test_admin"
# Пароль администратор
password: "admin"
# Эти флаги нужны что бы позволить загружать в Keycloak скрипты прямо через web морду. Это нам
понадобиться что бы починить один баг, о котором ниже.
extraArgs: "-Dkeycloak.profile.feature.script=enabled -Dkeycloak.profile.feature.upload_scripts=enabled"
# Включаем ingress, указываем имя хоста и сертификат который мы предварительно сохранили в secrets
ingress:
enabled: true
path: /
annotations:
kubernetes.io/ingress.class: nginx
ingress.kubernetes.io/affinity: cookie
hosts:
- keycloak.example.org
tls:
- hosts:
- keycloak.example.org
secretName: tls-keycloak
# Keycloak для своей работы требует базу данных, в тестовых целях я разворачиваю Postgresql прямо в Kuberntes, в продакшене так лучше не делать!
persistence:
deployPostgres: true
dbVendor: postgres
postgresql:
postgresUser: keycloak
postgresPassword: ""
postgresDatabase: keycloak
persistence:
enabled: trueKev teeb tsa Federation
Tom ntej no, mus rau lub web interface
Nyob rau sab laug ces kaum nyem Ntxiv realm
Ntsiab
Tus nqi
lub npe
kub
Zaub Lub Npe
Kubernetes
Disable tus neeg siv email kev lees paub kuaj xyuas:
Client scopes —> Email —> Mappers —> Email verified (Delete)
Peb tab tom teeb tsa lub koom haum los import cov neeg siv los ntawm ActiveDirectory, Kuv yuav tawm hauv cov screenshots hauv qab no, kuv xav tias nws yuav pom tseeb dua.
User federation —> Add provider… —> ldap
Kev teeb tsa Federation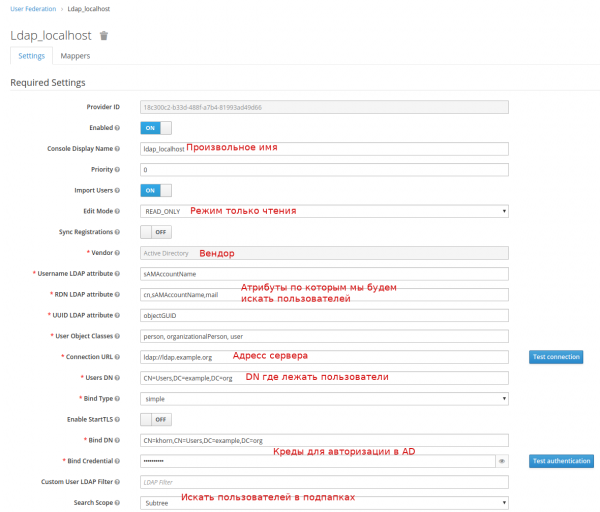
Yog tias txhua yam zoo, ces tom qab nias lub pob Synchronize tag nrho cov neeg siv Koj yuav pom cov lus qhia txog kev vam meej ntawm cov neeg siv.
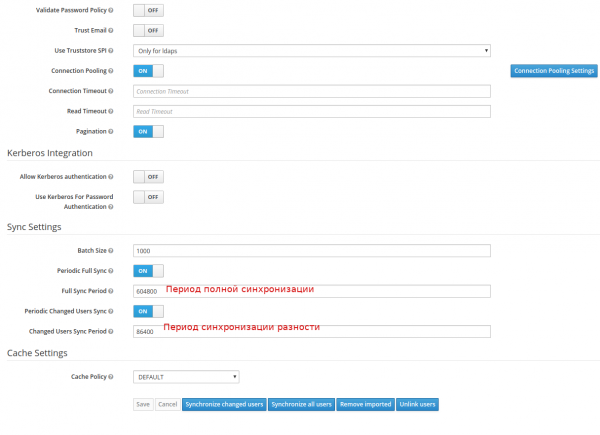
Tom ntej no peb yuav tsum tau daim ntawv qhia peb pab pawg
User federation -> ldap_localhost -> Mappers -> Tsim
Tsim ib tug mapper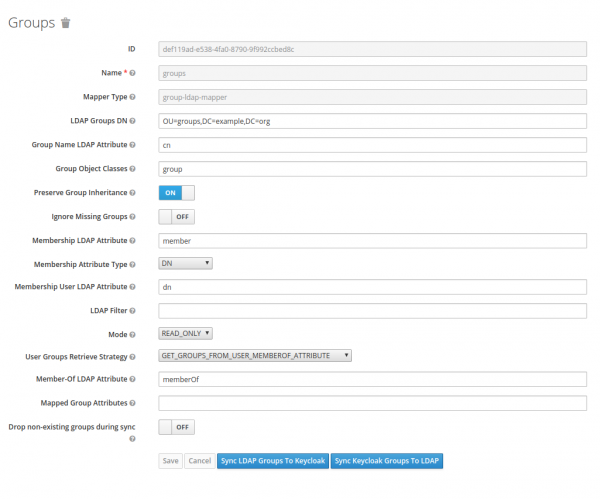
Kev teeb tsa tus neeg siv khoom
Koj yuav tsum tsim ib tus neeg siv khoom, hais txog Keycloak qhov no yog daim ntawv thov uas yuav tau tso cai los ntawm nws. Kuv yuav qhia cov ntsiab lus tseem ceeb hauv liab hauv lub screenshot.
Cov neeg siv khoom -> Tsim
Kev teeb tsa tus neeg siv khoom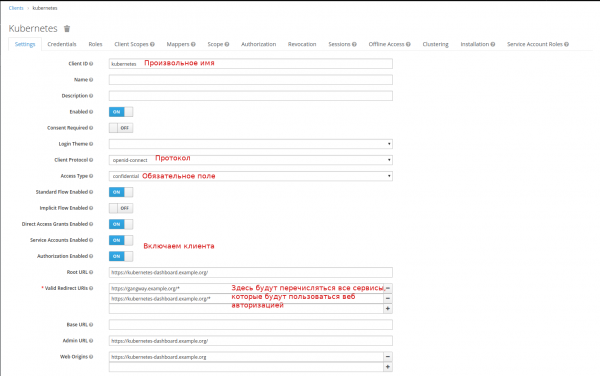
Wb tsim ib tug scoupe rau pab pawg:
Client Scopes -> Tsim
Tsim kom muaj kev thaj yeeb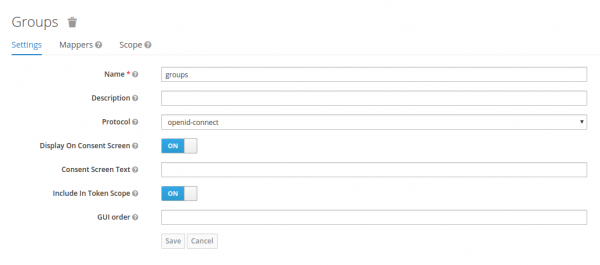
Thiab teeb ib daim ntawv qhia rau lawv:
Client Scopes -> pawg -> Mappers -> Tsim
Daim ntawv qhia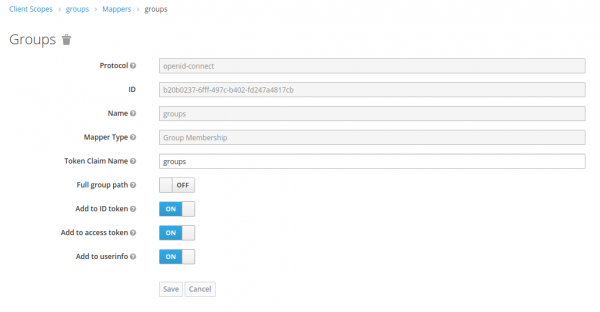
Peb ntxiv daim ntawv qhia ntawm peb pab pawg rau Default Client Scopes:
Client -> kubernetes -> Client Scopes -> Default Client Scopes
Xaiv pawg в Muaj Client Scopes, xovxwm Ntxiv xaiv
Peb tau txais cov ntaub ntawv zais cia (thiab sau nws hauv qhov chaw) uas peb yuav siv rau kev tso cai hauv Keycloak:
Client -> kubernetes -> Credentials -> Secret
Qhov no ua tiav qhov teeb tsa, tab sis kuv muaj qhov yuam kev thaum, tom qab kev tso cai ua tiav, kuv tau txais qhov yuam kev 403. .
Kho:
Client Scopes -> luag hauj lwm -> Mappers -> Tsim
Daim ntawv qhia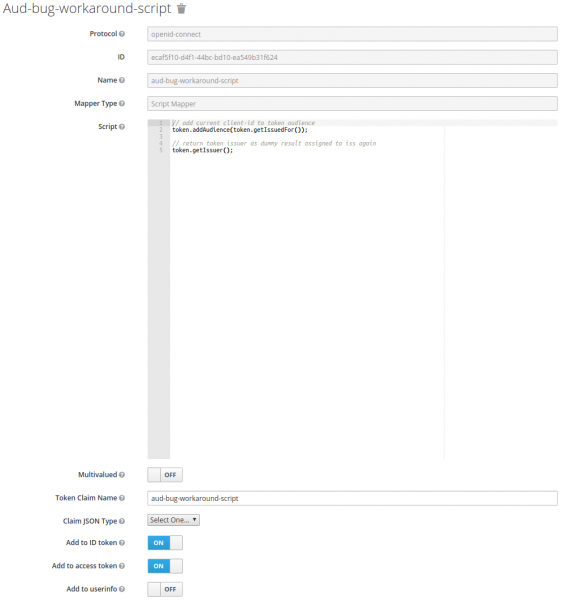
Script code
// add current client-id to token audience
token.addAudience(token.getIssuedFor());
// return token issuer as dummy result assigned to iss again
token.getIssuer();
Configuring Kubernetes
Peb yuav tsum qhia qhov twg peb daim ntawv pov thawj hauv paus los ntawm qhov chaw nyob, thiab qhov chaw muab kev pabcuam ODC nyob.
Ua li no, hloov cov ntaub ntawv /etc/kubernetes/manifests/kube-apiserver.yaml
kube-apiserver.yaml
...
spec:
containers:
- command:
- kube-apiserver
...
- --oidc-ca-file=/var/lib/minikube/certs/My_Root.crt
- --oidc-client-id=kubernetes
- --oidc-groups-claim=groups
- --oidc-issuer-url=https://keycloak.example.org/auth/realms/kubernetes
- --oidc-username-claim=email
...
Hloov kho kubeadm config hauv pawg:
kub config
kubectl edit -n kube-system configmaps kubeadm-config
...
data:
ClusterConfiguration: |
apiServer:
extraArgs:
oidc-ca-file: /var/lib/minikube/certs/My_Root.crt
oidc-client-id: kubernetes
oidc-groups-claim: groups
oidc-issuer-url: https://keycloak.example.org/auth/realms/kubernetes
oidc-username-claim: email
...
Kev teeb tsa auth-proxy
Txhawm rau tiv thaiv koj daim ntawv thov web, koj tuaj yeem siv keycloak gatekeeper. Ntxiv rau qhov tseeb tias qhov rov qab tso cai no yuav tso cai rau tus neeg siv ua ntej qhia nplooj ntawv, nws tseem yuav xa cov ntaub ntawv hais txog koj hauv cov ntawv headers mus rau qhov kawg daim ntawv thov. Yog li, yog tias koj daim ntawv thov txhawb OpenID, tus neeg siv tau tso cai tam sim ntawd. Cia peb saib tus piv txwv ntawm Kubernetes Dashboard
Txhim kho Kubernetes Dashboard
helm install stable/kubernetes-dashboard --name dashboard -f values_dashboard.yaml
values_dashboard.yaml
enableInsecureLogin: true
service:
externalPort: 80
rbac:
clusterAdminRole: true
create: true
serviceAccount:
create: true
name: 'dashboard-test'
Teeb tsa txoj cai nkag:
Cia peb tsim ClusterRoleBinding uas yuav muab cov cai tswj hwm pawg (tus qauv ClusterRole pawg-admin) rau cov neeg siv hauv pawg DataOPS.
kubectl apply -f rbac.yaml
rbac yam
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: dataops_group
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: cluster-admin
subjects:
- apiGroup: rbac.authorization.k8s.io
kind: Group
name: DataOPS
Txhim kho keycloak gatekeeper:
helm repo add gabibbo97 https://gabibbo97.github.io/charts/
helm repo update
helm install gabibbo97/keycloak-gatekeeper --version 2.1.0 --name keycloak-gatekeeper -f values_proxy.yaml
values_proxy.yaml
# Включаем ingress
ingress:
enabled: true
annotations:
kubernetes.io/ingress.class: nginx
path: /
hosts:
- kubernetes-dashboard.example.org
tls:
- secretName: tls-keycloak
hosts:
- kubernetes-dashboard.example.org
# Говорим где мы будем авторизовываться у OIDC провайдера
discoveryURL: "https://keycloak.example.org/auth/realms/kubernetes"
# Имя клиента которого мы создали в Keycloak
ClientID: "kubernetes"
# Secret который я просил записать
ClientSecret: "c6ec03b8-d0b8-4cb6-97a0-03becba1d727"
# Куда перенаправить в случае успешной авторизации. Формат <SCHEMA>://<SERVICE_NAME>.><NAMESAPCE>.<CLUSTER_NAME>
upstreamURL: "http://dashboard-kubernetes-dashboard.default.svc.cluster.local"
# Пропускаем проверку сертификата, если у нас самоподписанный
skipOpenidProviderTlsVerify: true
# Настройка прав доступа, пускаем на все path если мы в группе DataOPS
rules:
- "uri=/*|groups=DataOPS"
Tom qab ntawd, thaum koj sim nkag rau hauv , kev xa rov qab mus rau Keycloak yuav tshwm sim thiab yog tias kev tso cai ua tiav, peb yuav raug coj mus rau Dashboard twb tau nkag rau hauv.
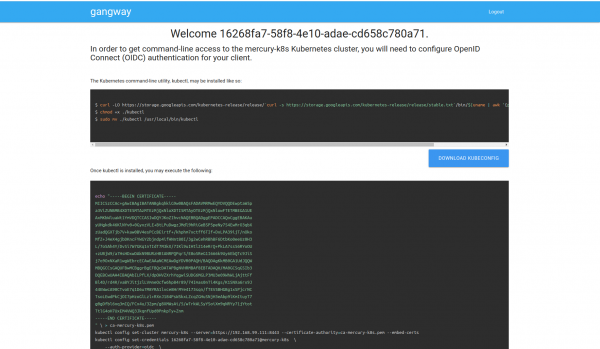
Gangway installation
Txhawm rau kom yooj yim, koj tuaj yeem ntxiv qhov gangway uas yuav tsim cov ntaub ntawv config rau kubectl, nrog kev pab los ntawm peb yuav nkag mus rau Kubernetes hauv qab peb cov neeg siv.
helm install --name gangway stable/gangway -f values_gangway.yaml
values_gangway.yaml
gangway:
# Произвольное имя кластера
clusterName: "my-k8s"
# Где у нас OIDC провайдер
authorizeURL: "https://keycloak.example.org/auth/realms/kubernetes/protocol/openid-connect/auth"
tokenURL: "https://keycloak.example.org/auth/realms/kubernetes/protocol/openid-connect/token"
audience: "https://keycloak.example.org/auth/realms/kubernetes/protocol/openid-connect/userinfo"
# Теоритически сюда можно добавить groups которые мы замапили
scopes: ["openid", "profile", "email", "offline_access"]
redirectURL: "https://gangway.example.org/callback"
# Имя клиента
clientID: "kubernetes"
# Секрет
clientSecret: "c6ec03b8-d0b8-4cb6-97a0-03becba1d727"
# Если оставить дефолтное значние, то за имя пользователя будет братья <b>Frist name</b> <b>Second name</b>, а при "sub" его логин
usernameClaim: "sub"
# Доменное имя или IP адресс API сервера
apiServerURL: "https://192.168.99.111:8443"
# Включаем Ingress
ingress:
enabled: true
annotations:
kubernetes.io/ingress.class: nginx
nginx.ingress.kubernetes.io/proxy-buffer-size: "64k"
path: /
hosts:
- gangway.example.org
tls:
- secretName: tls-keycloak
hosts:
- gangway.example.org
# Если используем самоподписанный сертификат, то его(открытый корневой сертификат) надо указать.
trustedCACert: |-
-----BEGIN CERTIFICATE-----
MIIDVzCCAj+gAwIBAgIBATANBgkqhkiG9w0BAQsFADA1MQswCQYDVQQGEwJVUzEQMA4GA1UEChMHRGF0YU9QUzEUMBIGA1UEAxMLbXkgcm9vdCBrZXkwHhcNMjAwMjE0MDkxODAwWhcNMzAwMjE0MDkxODAwWjA1MQswCQYDVQQGEwJVUzEQMA4GA1UEChMHRGF0YU9QUzEUMBIGA1UEAxMLbXkgcm9vdCBrZXkwggEiMA0GCSqGSIb3DQEBAQUAA4IBDwAwggEKAoIBAQDyP749PqqIRwNSqaK6qr0Zsi03G4PTCUlgaYTPZuMrwUVPK8xX2dWWs9MPRMOdXpgr8aSTZnVfmelIlVz4D7o2vK5rfmAe9GPcK0WbwKwXyhFU0flS9sU/g46ogHFrk03SZxQAeJhMLfEmAJm8LF5HghtGDs3t4uwGsB95o+lqPLiBvxRB8ZS3jSpYpvPgXAuZWKdZUQ3UUZf0X3hGLp7uIcIwJ7i4MduOGaQEO4cePeEJy9aDAO6qV78YmHbyh9kaW+1DL/Sgq8NmTgHGV6UOnAPKHTnMKXl6KkyUz8uLBGIdVhPxrlzG1EzXresJbJenSZ+FZqm3oLqZbw54Yp5hAgMBAAGjcjBwMA8GA1UdEwEB/wQFMAMBAf8wHQYDVR0OBBYEFHISTOU/6BQqqnOZj+1xJfxpjiG0MAsGA1UdDwQEAwIBBjARBglghkgBhvhCAQEEBAMCAAcwHgYJYIZIAYb4QgENBBEWD3hjYSBjZXJ0aWZpY2F0ZTANBgkqhkiG9w0BAQsFAAOCAQEAj7HC8ObibwOLT4ZYmISJZwub9lcE0AZ5cWkPW39j/syhdbbqjK/6jy2D3WUEbR+s1Vson5Ov7JhN5In2yfZ/ByDvBnoj7CP8Q/ZMjTJgwN7j0rgmEb3CTZvnDPAz8Ijw3FP0cjxfoZ1Z0V2F44Ry7gtLJWr06+MztXVyto3aIz1/XbMQnXYlzc3c3B5yUQIy44Ce5aLRVsAjmXNqVRmDJ2QPNLicvrhnUJsO0zFWI+zZ2hc4Ge1RotCrjfOc9hQY63jZJ17myCZ6QCD7yzMzAob4vrgmkD4q7tpGrhPY/gDcE+lUNhC7DO3l0oPy2wsnT2TEn87eyWmDiTFG9zWDew==
-----END CERTIFICATE-----
Nws zoo li no. Tso cai rau koj tam sim rub tawm cov ntaub ntawv config thiab tsim nws siv cov lus txib:
Tau qhov twg los: www.hab.com


