Mwen sèten ke tout moun ki te janm travay avèk yo , te gen yon plent sou enposib pou koreksyon konfigirasyon an soti nan liy lòd la. Sa a se espesyalman etranj pou moun ki te deja travay ak Cisco ASA, kote absoliman tout bagay ka configuré nan CLI la. Avèk Check Point li nan yon lòt fason alantou - tout paramèt sekirite yo te fèt sèlman nan koòdone grafik la. Sepandan, gen kèk bagay ki konplètman enkonvenyan fè atravè entèfas a (menm youn osi pratik ke Check Point a). Pou egzanp, travay la nan ajoute 100 nouvo lame oswa rezo vin tounen yon pwosedi long ak fatigan. Pou chak objè w ap gen klike sou sourit la plizyè fwa epi antre nan adrès IP la. Menm bagay la tou ale pou kreye yon gwoup sit oswa mas pèmèt / enfim siyati IPS. Nan ka sa a, gen yon gwo pwobabilite pou fè yon erè.
Yon "mirak" te rive relativman dènyèman. Avèk liberasyon nouvo vèsyon an Gaia R80 opòtinite a te anonse Itilizasyon API, ki ouvè opòtinite lajè pou otomatize anviwònman, administrasyon, siveyans, elatriye. Kounye a ou kapab:
- kreye objè;
- ajoute oswa modifye lis aksè;
- pèmèt / enfim lam;
- konfigirasyon rezo interfaces;
- enstale règleman yo;
- ak plis ankò.
Pou m onèt, mwen pa konprann ki jan nouvèl sa a te pase pa Habr. Nan atik sa a nou pral yon ti tan dekri kijan pou itilize API a epi bay plizyè egzanp pratik. Anviwònman CheckPoint lè l sèvi avèk scripts.
Mwen ta renmen fè yon rezèvasyon touswit ke API a itilize sèlman pou sèvè Jesyon an. Moun sa yo. Li toujou enposib pou jere pòtay san yon sèvè Jesyon.
Ki moun ki ka itilize API sa a an prensip?
- Administratè sistèm ki vle senplifye oswa otomatize travay woutin konfigirasyon Check Point;
- Konpayi ki vle entegre Check Point ak lòt solisyon (sistèm vityèl, sistèm tikè, sistèm jesyon konfigirasyon, elatriye);
- Entegratè sistèm ki vle estandadize anviwònman oswa kreye pwodwi adisyonèl ki gen rapò ak Check Point.
Konplo tipik
Se konsa, an nou imajine yon konplo tipik ak Check Point:
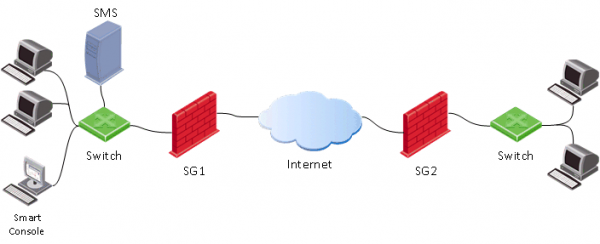
Kòm dabitid nou gen yon pòtay (SG), sèvè jesyon (SMS) ak konsole admin (SmartConsole). Nan ka sa a, pwosesis konfigirasyon pòtay nòmal la sanble sa a:
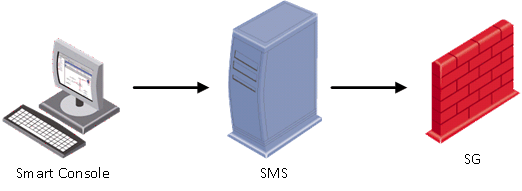
Moun sa yo. Premye ou bezwen kouri sou òdinatè administratè a SmartConsole, ak ki nou konekte ak sèvè Jesyon an (SMS). Anviwònman sekirite yo fèt sou SMS la, epi sèlman lè sa a aplike (enstale politik) to gateway (SG).
Lè lè l sèvi avèk la Jesyon API, nou ka fondamantalman sote premye pwen an (lanse SmartConsole) epi sèvi ak Kòmandman API dirèkteman nan sèvè Jesyon an (SMS).
Fason yo sèvi ak API a
Gen kat fason prensipal yo modifye konfigirasyon an lè l sèvi avèk API a:
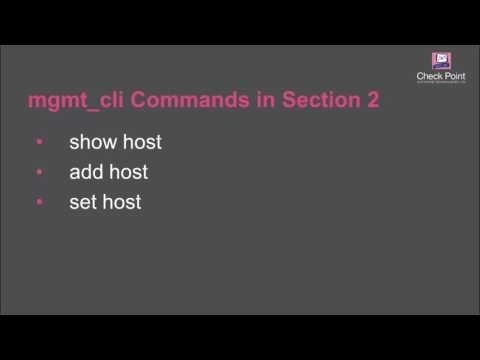
1) Sèvi ak sèvis piblik mgmt_cli
Egzanp - # mgmt_cli ajoute non lame host1 adrès ip 192.168.2.100
Kòmand sa a kouri soti nan liy lòd sèvè Jesyon (SMS). Mwen panse ke sentaks kòmandman an klè - host1 kreye ak adrès 192.168.2.100.
2) Antre kòmandman API atravè clish (nan mòd ekspè)
Fondamantalman, tout sa ou bezwen fè se konekte nan liy lòd la (mgmt konekte) anba kont ki itilize lè w konekte atravè SmartConsole (oswa kont rasin). Lè sa a, ou ka antre Kòmandman API (nan ka sa a pa gen okenn bezwen sèvi ak sèvis piblik la anvan chak lòd mgmt_cli). Ou ka kreye plen véritable Scripts BASH. Yon egzanp yon script ke lame a kreye:
bash script
#!/bin/bash
main() {
clear
#LOGIN (don't ask for username and password, user is already logged in to Management server as 'root' user)
mgmt_cli login --root true > id_add_host.txt
on_error_print_and_exit "Error: Failed to login, check that the server is up and running (run 'api status')"
#READ HOST NAME
printf "Enter host name:n"
read -e host_name
on_empty_input_print_and_exit "$host_name" "Error: The host's name cannot be empty."
#READ IP ADDRESS
printf "nEnter host IP address:n"
read -e ip
on_empty_input_print_and_exit "$ip" "Error: The host's IP address cannot be empty."
#CREATE HOST
printf "Creating new host: $host_name with IP address: $ipn"
new_host_response=$(mgmt_cli add host name $host_name ip-address $ip -s id_add_host.txt 2> /dev/null)
on_error_print_and_exit "Error: Failed to create host object. n$new_host_response"
#PUBLISH THE CHANGES
printf "nPublishing the changesn"
mgmt_cli publish --root true -s id_add_host.txt &> /dev/null
on_error_print_and_exit "Error: Failed to publish the changes."
#LOGOUT
logout
printf "Done.n"
}
logout(){
mgmt_cli logout --root true -s id_add_host.txt &> /dev/null
}
on_error_print_and_exit(){
if [ $? -ne 0 ]; then
handle_error "$1"
fi
}
handle_error(){
printf "n$1n" #print error message
mgmt_cli discard --root true -s id_add_host.txt &> /dev/null
logout
exit 1
}
on_empty_input_print_and_exit(){
if [ -z "$1" ]; then
printf "$2n" #print error message
logout
exit 0
fi
}
# Script starts here. Call function "main".
main
Si w enterese, ou ka gade videyo ki koresponn lan:
3) Via SmartConsole lè w louvri fenèt CLI a
Tout sa ou bezwen fè se louvri fenèt la Klima dwat soti SmartConsole, jan yo montre nan foto ki anba a.
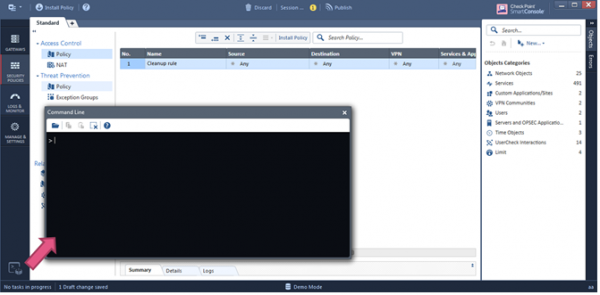
Nan fenèt sa a, ou ka imedyatman kòmanse antre nan kòmandman API.
4) Sèvis Entènèt. Sèvi ak HTTPS Post demann (REST API)
Nan opinyon nou an, sa a se youn nan metòd ki pi pwomèt, paske pèmèt ou "konstwi" tout aplikasyon ki baze sou jesyon sèvè jesyon (rekize pou tautoloji a). Anba a nou pral gade nan metòd sa a nan yon ti kras plis detay.
Pou rezime:
- API + cli plis apwopriye pou moun ki itilize Cisco;
- API + koki pou aplike scripts ak fè travay woutin;
- REST API pou automatisation.
Pèmèt API a
Pa default, API a aktive sou serveurs jesyon ki gen plis pase 4GB RAM ak konfigirasyon otonòm ak plis pase 8GB RAM. Ou ka tcheke estati a lè l sèvi avèk kòmandman an: estati api
Si li vire soti ke api a enfim, Lè sa a, li se byen fasil yo aktive li atravè SmartConsole: Jere & Anviwònman > Lam > Jesyon API > Anviwònman Avanse
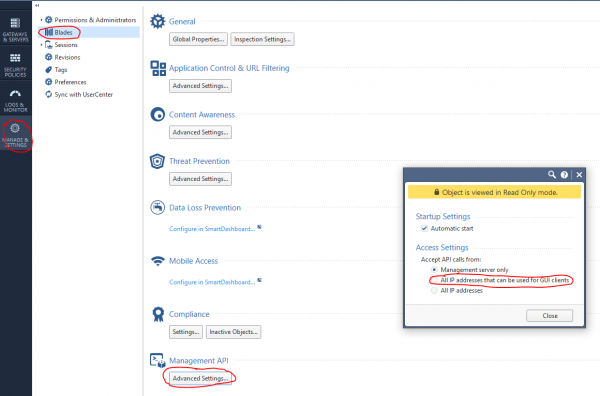
Lè sa a, pibliye (Pibliye) chanje epi kouri lòd la api rekòmanse.
Demann entènèt + Python
Pou egzekite kòmandman API, ou ka itilize demann entènèt lè l sèvi avèk Piton ak bibliyotèk demann, JSON. An jeneral, estrikti yon demann entènèt konsiste de twa pati:
1) Adrès
(https://<managemenet server>:<port>/web_api/<command>)
2) Tèt HTTP
content-Type: application/json
x-chkp-sid: <session ID token as returned by the login command>
3) Mande chaj
Tèks nan fòma JSON ki gen diferan paramèt yo
Egzanp pou rele plizyè kòmandman:
def api_call(ip_addr, port, command, json_payload, sid):
url = 'https://' + ip_addr + ':' + str(port) + '/web_api/' + command
if sid == “”:
request_headers = {'Content-Type' : 'application/json'}
else:
request_headers = {'Content-Type' : 'application/json', 'X-chkp-sid' : sid}
r = requests.post(url,data=json.dumps(json_payload), headers=request_headers,verify=False)
return r.json()
'xxx.xxx.xxx.xxx' -> Ip address GAIA
Men kèk travay tipik ke ou rankontre pi souvan lè w ap administre Check Point.
1) Egzanp fonksyon otorizasyon ak dekonekte:
Script
payload = {‘user’: ‘your_user’, ‘password’ : ‘your_password’}
response = api_call('xxx.xxx.xxx.xxx', 443, 'login',payload, '')
return response["sid"]
response = api_call('xxx.xxx.xxx.xxx', 443,'logout', {} ,sid)
return response["message"]
2) Limen lam yo epi mete rezo a:
Script
new_gateway_data = {'name':'CPGleb','anti-bot':True,'anti-virus' : True,'application-control':True,'ips':True,'url-filtering':True,'interfaces':
[{'name':"eth0",'topology':'external','ipv4-address': 'xxx.xxx.xxx.xxx',"ipv4-network-mask": "255.255.255.0"},
{'name':"eth1",'topology':'internal','ipv4-address': 'xxx.xxx.xxx.xxx',"ipv4-network-mask": "255.255.255.0"}]}
new_gateway_result = api_call('xxx.xxx.xxx.xxx', 443,'set-simple-gateway', new_gateway_data ,sid)
print(json.dumps(new_gateway_result))
3) Chanje règ firewall:
Script
new_access_data={'name':'Cleanup rule','layer':'Network','action':'Accept'}
new_access_result = api_call('xxx.xxx.xxx.xxx', 443,'set-access-rule', new_access_data ,sid)
print(json.dumps(new_access_result))
4) Ajoute kouch aplikasyon:
Script
add_access_layer_application={ 'name' : 'application123',"applications-and-url-filtering" : True,"firewall" : False}
add_access_layer_application_result = api_call('xxx.xxx.xxx.xxx', 443,'add-access-layer', add_access_layer_application ,sid)
print(json.dumps(add_access_layer_application_result))
set_package_layer={"name" : "Standard","access":True,"access-layers" : {"add" : [ { "name" : "application123","position" :2}]} ,"installation-targets" : "CPGleb"}
set_package_layer_result = api_call('xxx.xxx.xxx.xxx', 443,'set-package', set_package_layer ,sid)
print(json.dumps(set_package_layer_result))
5) Pibliye epi mete politik la, tcheke ekzekisyon kòmandman an (task-id):
Script
publish_result = api_call('xxx.xxx.xxx.xxx', 443,"publish", {},sid)
print("publish result: " + json.dumps(publish_result))
new_policy = {'policy-package':'Standard','access':True,'targets':['CPGleb']}
new_policy_result = api_call('xxx.xxx.xxx.xxx', 443,'install-policy', new_policy ,sid)
print(json.dumps(new_policy_result)
task_id=(json.dumps(new_policy_result ["task-id"]))
len_str=len(task_id)
task_id=task_id[1:(len_str-1)]
show_task_id ={'task-id':(task_id)}
show_task=api_call('xxx.xxx.xxx.xxx',443,'show-task',show_task_id,sid)
print(json.dumps(show_task))
6) Ajoute lame:
Script
new_host_data = {'name':'JohnDoePc', 'ip-address': '192.168.0.10'}
new_host_result = api_call('xxx.xxx.xxx.xxx', 443,'add-host', new_host_data ,sid)
print(json.dumps(new_host_result))
7) Ajoute yon jaden prevansyon menas:
Script
set_package_layer={'name':'Standard','threat-prevention' :True,'installation-targets':'CPGleb'}
set_package_layer_result = api_call('xxx.xxx.xxx.xxx', 443,'set-package',set_package_layer,sid)
print(json.dumps(set_package_layer_result))
8) Gade lis sesyon yo
Script
new_session_data = {'limit':'50', 'offset':'0','details-level' : 'standard'}
new_session_result = api_call('xxx.xxx.xxx.xxx', 443,'show-sessions', new_session_data ,sid)
print(json.dumps(new_session_result))
9) Kreye yon nouvo pwofil:
Script
add_threat_profile={'name':'Apeiron', "active-protections-performance-impact" : "low","active-protections-severity" : "low or above","confidence-level-medium" : "prevent",
"confidence-level-high" : "prevent", "threat-emulation" : True,"anti-virus" : True,"anti-bot" : True,"ips" : True,
"ips-settings" : { "newly-updated-protections" : "staging","exclude-protection-with-performance-impact" : True,"exclude-protection-with-performance-impact-mode" : "High or lower"},
"overrides" : [ {"protection" : "3Com Network Supervisor Directory Traversal","capture-packets" : True,"action" : "Prevent","track" : "Log"},
{"protection" : "7-Zip ARJ Archive Handling Buffer Overflow", "capture-packets" : True,"action" : "Prevent","track" : "Log"} ]}
add_threat_profile_result=api_call('xxx.xxx.xxx.xxx',443,'add-threat-profile',add_threat_profile,sid)
print(json.dumps(add_threat_profile_result))
10) Chanje aksyon an pou siyati IPS la:
Script
set_threat_protection={
"name" : "3Com Network Supervisor Directory Traversal",
"overrides" : [{ "profile" : "Apeiron","action" : "Detect","track" : "Log","capture-packets" : True},
{ "profile" : "Apeiron", "action" : "Detect", "track" : "Log", "capture-packets" : False} ]}
set_threat_protection_result=api_call('xxx.xxx.xxx.xxx',443,'set-threat-protection',set_threat_protection,sid)
print(json.dumps(set_threat_protection_result))
11) Ajoute sèvis ou a:
Script
add_service_udp={ "name" : "Dota2_udp", "port" : '27000-27030',
"keep-connections-open-after-policy-installation" : False,
"session-timeout" : 0, "match-for-any" : True,
"sync-connections-on-cluster" : True,
"aggressive-aging" : {"enable" : True, "timeout" : 360,"use-default-timeout" : False },
"accept-replies" : False}
add_service_udp_results=api_call('xxx.xxx.xxx.xxx',443,"add-service-udp",add_service_udp,sid)
print(json.dumps(add_service_udp_results))
12) Ajoute yon kategori, sit oswa gwoup:
Script
add_application_site_category={ "name" : "Valve","description" : "Valve Games"}
add_application_site_category_results=api_call('xxx.xxx.xxx.xxx',443,"add-application-site-category",add_application_site_category,sid)
print(json.dumps(add_application_site_category_results))
add_application_site={ "name" : "Dota2", "primary-category" : "Valve", "description" : "Dotka",
"url-list" : [ "www.dota2.ru" ], "urls-defined-as-regular-expression" : False}
add_application_site_results=api_call('xxx.xxx.xxx.xxx',443,"add-application-site " ,
add_application_site , sid)
print(json.dumps(add_application_site_results))
add_application_site_group={"name" : "Games","members" : [ "Dota2"]}
add_application_site_group_results=api_call('xxx.xxx.xxx.xxx',443,"add-application-site-group",add_application_site_group,sid)
print(json.dumps(add_application_site_group_results))
Anplis de sa, avèk èd la WebAPI ou ka ajoute epi retire rezo, lame, wòl aksè, elatriye. Lam yo ka Customized Antivirus, Antibot, IPS, VPN. Li se menm posib enstale lisans lè l sèvi avèk lòd la kouri-script. Ou ka jwenn tout kòmandman API Check Point isit la .
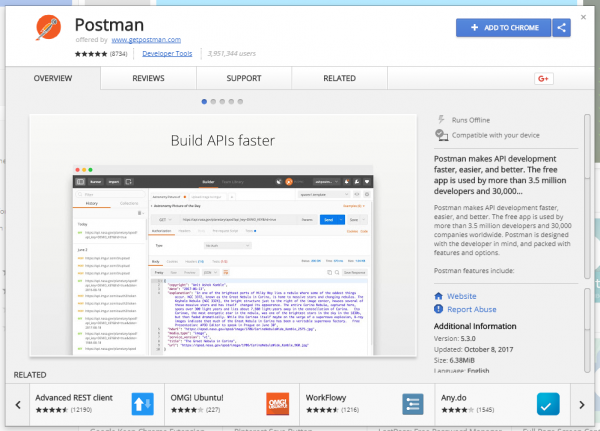
Check Point API + Postman
Epitou pratik yo sèvi ak Check Point Web API an konjonksyon avèk Postman gen vèsyon òdinatè pou Windows, Linux ak MacOS. Genyen tou yon plugin pou Google Chrome, ke nou pral itilize. Premyèman, jwenn Postman nan Google Chrome Store la epi enstale li:
Sèvi ak sèvis piblik sa a, nou pral kapab jenere demann entènèt nan Check Point API a. Nan lòd pa sonje tout kòmandman API yo, li posib pou enpòte sa yo rele koleksyon (modèl), ki deja gen tout kòmandman ki nesesè yo:
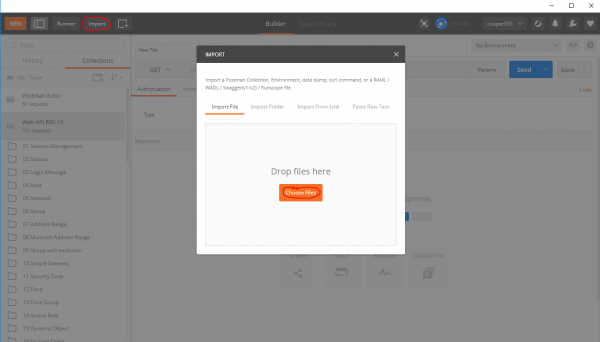
ou pral jwenn koleksyon pou R80.10. Apre enpòte, modèl kòmand API yo ap vin disponib pou nou:
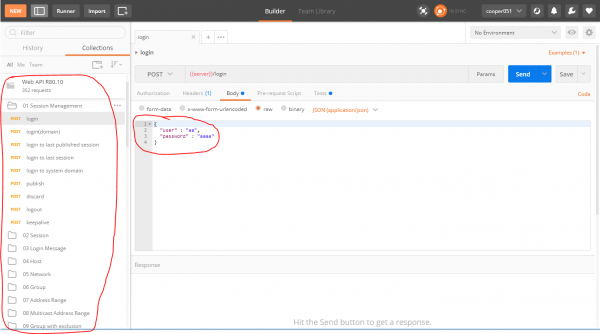
Dapre mwen, sa a trè pratik. Ou ka byen vit kòmanse devlope aplikasyon lè l sèvi avèk Check Point API la.
Check Point + Ansible
Mwen ta renmen tou note ke genyen Ansible pou CheckPoint API. Modil la pèmèt ou jere konfigirasyon, men li pa tèlman pratik pou rezoud pwoblèm ekzotik. Ekri scripts nan nenpòt lang pwogramasyon bay solisyon pi fleksib ak pratik.
Sòti
Sa a se kote nou pral pwobableman fini revizyon kout nou an nan Check Point API a. Dapre mwen, karakteristik sa a te trè long dire ak nesesè. Aparisyon API a louvri opòtinite trè laj pou tou de administratè sistèm ak entegratè sistèm ki travay ak pwodwi Check Point. Orchestration, automatisation, SIEM commentaires... tout posib koulye a.
PS Plis atik sou kòm toujou ou ka jwenn li sou blog nou an oswa sou blog la nan .
PSS Pou kesyon teknik ki gen rapò ak etabli Check Point, ou kapab
Se sèlman itilizatè ki anrejistre ki ka patisipe nan sondaj la. , tanpri.
Èske w planifye pou itilize API a?
70,6%Wi12
23,5%Non4
5,9%Deja itilize 1
17 itilizatè yo te vote. 3 itilizatè te absteni.
Sous: www.habr.com


