TL; DR: Yon gid apèsi pou konpare kad pou kouri aplikasyon nan resipyan. Kapasite Docker ak lòt sistèm menm jan an pral konsidere.
Yon ti istwa kote tout bagay soti
Istwa
Premye metòd ki byen koni pou izole yon aplikasyon se chroot. Rele sistèm nan menm non an asire ke anyè rasin lan chanje - konsa asire ke pwogram ki rele li a gen aksè sèlman nan dosye ki nan anyè sa a. Men, si yo bay yon pwogram privilèj rasin anndan an, li ka potansyèlman "chape" chroot la ak jwenn aksè nan sistèm opere prensipal la. Epitou, anplis chanje anyè rasin lan, lòt resous (RAM, processeur), osi byen ke aksè rezo, yo pa limite.
Pwochen metòd la se pou fè yon sistèm operasyon konplèt kouri andedan yon kontenè, lè l sèvi avèk mekanis nwayo sistèm operasyon an. Metòd sa a gen diferan non nan diferan sistèm operasyon, men sans lan se menm bagay la: kouri plizyè sistèm operasyon endepandan, chak ap kouri menm nwayo ak sistèm operasyon prensipal la. Sa gen ladan FreeBSD Jails, Solaris Zones, OpenVZ, ak LXC pou LinuxIzolasyon an pa sèlman bay pa espas ki sou disk la, men tou pa lòt resous; an patikilye, chak kontenè ka gen limit sou tan CPU, RAM, ak bandwidth rezo a. Konpare ak chroot, sòti nan yon kontenè pi difisil, paske sipè itilizatè ki nan kontenè a gen aksè sèlman nan eleman entèn kontenè a. Sepandan, akòz bezwen pou kenbe sistèm operasyon ki andedan kontenè a ajou ak itilizasyon vèsyon nwayo ki pi ansyen yo (ki enpòtan pou Linux, nan yon pi piti mezi FreeBSD) gen yon pwobabilite ki pa zewo pou "kraze" sistèm izolasyon nwayo a epi jwenn aksè nan sistèm operasyon prensipal la.
Olye pou yo lanse yon sistèm operasyon konplè nan yon veso (avèk yon sistèm inisyalizasyon, manadjè pake, elatriye), ou ka lanse aplikasyon imedyatman, bagay prensipal la se bay aplikasyon yo ak yon opòtinite konsa (prezans bibliyotèk ki nesesè yo). ak lòt dosye). Lide sa a te sèvi kòm baz pou Virtualization aplikasyon nan kontenè, reprezantan ki pi enpòtan ak byen koni se Docker. Konpare ak sistèm anvan yo, mekanis izolasyon ki pi fleksib, makonnen ak sipò entegre pou rezo vityèl ant resipyan yo ak swivi eta aplikasyon an nan veso a, sa ki lakòz kapasite nan bati yon sèl anviwònman aderan nan yon gwo kantite sèvè fizik pou kouri resipyan yo - san yo pa bezwen pou jesyon resous manyèl.
Koupre
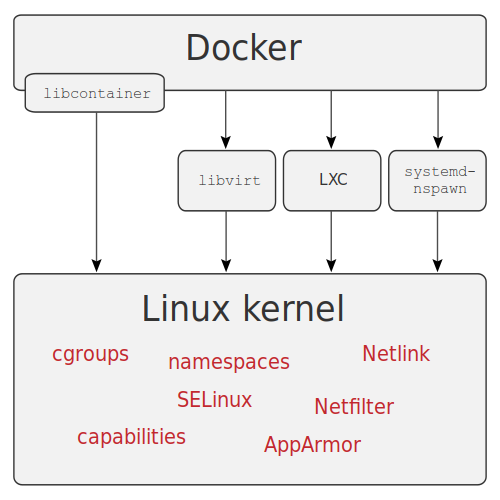
Docker se lojisyèl kontenè aplikasyon ki pi byen koni an. Li ekri nan langaj Go a epi li itilize kapasite nwayo natif natal la. Linux — gwoup c, espas non, kapasite, elatriye, ansanm ak sistèm fichye Aufs ak lòt menm jan an pou ekonomize espas sou disk la.
Sous: wikimedia
achitekti
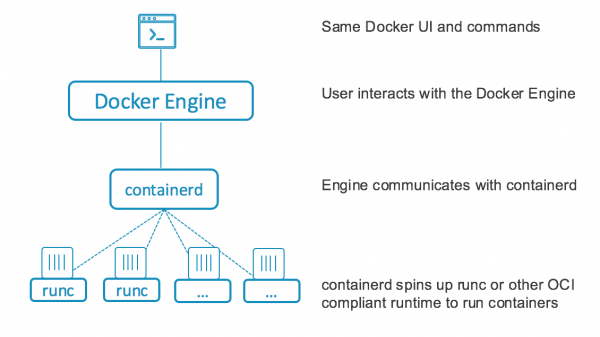
Anvan vèsyon 1.11, Docker te fonksyone kòm yon sèl sèvis ki te jere tout operasyon kontenè yo: telechaje imaj kontenè yo, lansman kontenè yo, ak jesyon demann API yo. Apati vèsyon 1.11, Docker te divize an plizyè pati ki te kominike youn ak lòt: containerd, ki jere tout sik lavi kontenè a (alokasyon disk, telechaje imaj, koneksyon rezo, lansman, enstalasyon, ak siveyans estati kontenè a), ak runC, yon anviwònman ekzekisyon kontenè ki baze sou gwoup c ak lòt karakteristik nwayo a. LinuxSèvis Docker la li menm rete la, men kounye a li sèlman sèvi pou trete demann API ki transmèt bay containerd.
Enstalasyon ak konfigirasyon
Fason pi renmen m 'yo enstale Docker se Docker-machine, ki, anplis dirèkteman enstale ak konfigirasyon Docker sou sèvè aleka (ki gen ladan nyaj divès kalite), fè li posib yo travay ak sistèm dosye nan sèvè aleka epi li ka tou kouri kòmandman divès kalite.
Sepandan, depi 2018 pwojè a prèske pa devlope, kidonk nou pral enstale li lè l sèvi avèk metòd estanda pou pifò distribisyon yo. Linux metòd - lè w ajoute yon depo epi enstale pakè ki nesesè yo.
Metòd sa a tou itilize pou enstalasyon otomatik, pou egzanp lè l sèvi avèk Ansible oswa lòt sistèm menm jan an, men mwen pa pral konsidere li nan atik sa a.
Enstalasyon an pral fèt sou Centos 7, mwen pral itilize yon machin vityèl kòm yon sèvè, pou enstalasyon li sifi pou egzekite kòmandman ki anba yo:
# yum install -y yum-utils
# yum-config-manager --add-repo https://download.docker.com/linux/centos/docker-ce.repo
# yum install docker-ce docker-ce-cli containerd.ioApre enstalasyon, ou bezwen kòmanse sèvis la epi mete l nan demaraj:
# systemctl enable docker
# systemctl start docker
# firewall-cmd --zone=public --add-port=2377/tcp --permanentAnplis de sa, ou ka kreye yon gwoup docker, ki gen itilizatè yo pral kapab travay avèk docker san yo pa sudo, mete kanpe antre, pèmèt aksè nan API a soti deyò, epi pa bliye konfigirasyon firewall la pi presizeman (tout sa ki pa pèmèt. se entèdi nan egzanp ki anwo yo ak anba a - mwen te omisyon sa a pou senplisite ak klè), men mwen pa pral antre nan plis detay isit la.
Lòt karakteristik
Anplis machin docker mansyone anwo a, gen tou rejis docker, yon zouti pou estoke imaj pou resipyan, osi byen ke konpoze docker, yon zouti pou otomatize deplwaman aplikasyon yo nan resipyan yo, dosye YAML yo itilize pou konstwi ak konfigirasyon resipyan yo. ak lòt bagay ki gen rapò (pa egzanp, rezo, sistèm dosye ki pèsistan pou done depo).
Li kapab tou itilize pou òganize transporteurs pou CICD. Yon lòt karakteristik enteresan ap travay nan mòd gwoup, sa yo rele mòd swarm (anvan vèsyon 1.12 li te konnen kòm Docker Swarm), ki pèmèt ou rasanble yon enfrastrikti sèl soti nan plizyè serveurs pou kouri kontenè. Gen sipò pou yon rezo vityèl sou tèt tout sèvè, gen yon balanse chaj entegre, osi byen ke sipò pou sekrè pou resipyan yo.
Fichye YAML ki soti nan Docker konpoze, ak modifikasyon minè, yo ka itilize pou grap sa yo, konplètman otomatize antretyen nan grap ti ak mwayen gwosè pou divès rezon. Pou gwo grap, Kubernetes pi preferab paske depans antretyen mòd swarm ka depase sa yo nan Kubernetes. Anplis runC, ou ka enstale, pou egzanp, kòm anviwònman an ekzekisyon veso
Travay ak Docker
Apre enstalasyon ak konfigirasyon, nou pral eseye rasanble yon gwoup kote nou pral deplwaye GitLab ak Docker Rejis pou ekip devlopman an. Mwen pral sèvi ak twa machin vityèl kòm sèvè, sou ki mwen pral anplis deplwaye distribiye FS GlusterFS la; Mwen pral sèvi ak li kòm yon depo docker volumes, pou egzanp, kouri yon vèsyon ki toleran defo nan rejis docker. Konpozan kle pou kouri: Docker Registry, Postgresql, Redis, GitLab ak sipò pou GitLab Runner sou tèt Swarm. Nou pral lanse Postgresql ak clustering , kidonk ou pa bezwen sèvi ak GlusterFS pou estoke done Postgresql. Done kritik ki rete yo pral estoke sou GlusterFS.
Pou deplwaye GlusterFS sou tout sèvè (yo rele yo node1, node2, node3), ou bezwen enstale pakè, pèmèt firewall la, epi kreye repèrtwar ki nesesè yo:
# yum -y install centos-release-gluster7
# yum -y install glusterfs-server
# systemctl enable glusterd
# systemctl start glusterd
# firewall-cmd --add-service=glusterfs --permanent
# firewall-cmd --reload
# mkdir -p /srv/gluster
# mkdir -p /srv/docker
# echo "$(hostname):/docker /srv/docker glusterfs defaults,_netdev 0 0" >> /etc/fstabApre enstalasyon, travay sou konfigirasyon GlusterFS dwe kontinye soti nan yon sèl ne, pou egzanp node1:
# gluster peer probe node2
# gluster peer probe node3
# gluster volume create docker replica 3 node1:/srv/gluster node2:/srv/gluster node3:/srv/gluster force
# gluster volume start dockerLè sa a, ou bezwen monte volim ki kapab lakòz (dwe lòd la dwe egzekite sou tout sèvè):
# mount /srv/dockerSe mòd nan swarm configuré sou youn nan sèvè yo, ki pral lidè a, rès la pral gen yo rantre nan gwoup la, kidonk rezilta a nan egzekite kòmandman an sou sèvè a premye ap bezwen kopye ak egzekite sou lòt yo.
Premye konfigirasyon gwoup, mwen kouri lòd la sou node1:
# docker swarm init
Swarm initialized: current node (a5jpfrh5uvo7svzz1ajduokyq) is now a manager.
To add a worker to this swarm, run the following command:
docker swarm join --token SWMTKN-1-0c5mf7mvzc7o7vjk0wngno2dy70xs95tovfxbv4tqt9280toku-863hyosdlzvd76trfptd4xnzd xx.xx.xx.xx:2377
To add a manager to this swarm, run 'docker swarm join-token manager' and follow the instructions.
# docker swarm join-token managerNou kopye rezilta dezyèm kòmandman an epi egzekite li sou node2 ak node3:
# docker swarm join --token SWMTKN-x-xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx-xxxxxxxxx xx.xx.xx.xx:2377
This node joined a swarm as a manager.Nan pwen sa a, konfigirasyon preliminè nan sèvè yo fini, ann kontinye nan mete kanpe sèvis yo; kòmandman yo dwe egzekite yo pral lanse soti nan node1, sof si otreman espesifye.
Premye a tout, se pou yo kreye rezo pou resipyan:
# docker network create --driver=overlay etcd
# docker network create --driver=overlay pgsql
# docker network create --driver=overlay redis
# docker network create --driver=overlay traefik
# docker network create --driver=overlay gitlabLè sa a, nou make serveurs yo, sa a nesesè yo mare kèk sèvis nan serveurs yo:
# docker node update --label-add nodename=node1 node1
# docker node update --label-add nodename=node2 node2
# docker node update --label-add nodename=node3 node3Apre sa, nou kreye anyè pou estoke done etcd, depo KV, ki nesesè pou Traefik ak Stolon. Menm jan ak Postgresql, sa yo pral resipyan ki mare ak sèvè, kidonk nou kouri lòd sa a sou tout sèvè:
# mkdir -p /srv/etcdApre sa, kreye yon dosye pou configure etcd epi sèvi ak li:
00etcd.yml
version: '3.7'
services:
etcd1:
image: quay.io/coreos/etcd:latest
hostname: etcd1
command:
- etcd
- --name=etcd1
- --data-dir=/data.etcd
- --advertise-client-urls=http://etcd1:2379
- --listen-client-urls=http://0.0.0.0:2379
- --initial-advertise-peer-urls=http://etcd1:2380
- --listen-peer-urls=http://0.0.0.0:2380
- --initial-cluster=etcd1=http://etcd1:2380,etcd2=http://etcd2:2380,etcd3=http://etcd3:2380
- --initial-cluster-state=new
- --initial-cluster-token=etcd-cluster
networks:
- etcd
volumes:
- etcd1vol:/data.etcd
deploy:
replicas: 1
placement:
constraints: [node.labels.nodename == node1]
etcd2:
image: quay.io/coreos/etcd:latest
hostname: etcd2
command:
- etcd
- --name=etcd2
- --data-dir=/data.etcd
- --advertise-client-urls=http://etcd2:2379
- --listen-client-urls=http://0.0.0.0:2379
- --initial-advertise-peer-urls=http://etcd2:2380
- --listen-peer-urls=http://0.0.0.0:2380
- --initial-cluster=etcd1=http://etcd1:2380,etcd2=http://etcd2:2380,etcd3=http://etcd3:2380
- --initial-cluster-state=new
- --initial-cluster-token=etcd-cluster
networks:
- etcd
volumes:
- etcd2vol:/data.etcd
deploy:
replicas: 1
placement:
constraints: [node.labels.nodename == node2]
etcd3:
image: quay.io/coreos/etcd:latest
hostname: etcd3
command:
- etcd
- --name=etcd3
- --data-dir=/data.etcd
- --advertise-client-urls=http://etcd3:2379
- --listen-client-urls=http://0.0.0.0:2379
- --initial-advertise-peer-urls=http://etcd3:2380
- --listen-peer-urls=http://0.0.0.0:2380
- --initial-cluster=etcd1=http://etcd1:2380,etcd2=http://etcd2:2380,etcd3=http://etcd3:2380
- --initial-cluster-state=new
- --initial-cluster-token=etcd-cluster
networks:
- etcd
volumes:
- etcd3vol:/data.etcd
deploy:
replicas: 1
placement:
constraints: [node.labels.nodename == node3]
volumes:
etcd1vol:
driver: local
driver_opts:
type: none
o: bind
device: "/srv/etcd"
etcd2vol:
driver: local
driver_opts:
type: none
o: bind
device: "/srv/etcd"
etcd3vol:
driver: local
driver_opts:
type: none
o: bind
device: "/srv/etcd"
networks:
etcd:
external: true# docker stack deploy --compose-file 00etcd.yml etcdApre kèk tan, nou tcheke si gwoup etcd la leve:
# docker exec $(docker ps | awk '/etcd/ {print $1}') etcdctl member list
ade526d28b1f92f7: name=etcd1 peerURLs=http://etcd1:2380 clientURLs=http://etcd1:2379 isLeader=false
bd388e7810915853: name=etcd3 peerURLs=http://etcd3:2380 clientURLs=http://etcd3:2379 isLeader=false
d282ac2ce600c1ce: name=etcd2 peerURLs=http://etcd2:2380 clientURLs=http://etcd2:2379 isLeader=true
# docker exec $(docker ps | awk '/etcd/ {print $1}') etcdctl cluster-health
member ade526d28b1f92f7 is healthy: got healthy result from http://etcd1:2379
member bd388e7810915853 is healthy: got healthy result from http://etcd3:2379
member d282ac2ce600c1ce is healthy: got healthy result from http://etcd2:2379
cluster is healthyNou kreye anyè pou Postgresql, egzekite lòd la sou tout sèvè:
# mkdir -p /srv/pgsqlApre sa, kreye yon dosye pou konfigirasyon Postgresql:
01pgsql.yml
version: '3.7'
services:
pgsentinel:
image: sorintlab/stolon:master-pg10
command:
- gosu
- stolon
- stolon-sentinel
- --cluster-name=stolon-cluster
- --store-backend=etcdv3
- --store-endpoints=http://etcd1:2379,http://etcd2:2379,http://etcd3:2379
- --log-level=debug
networks:
- etcd
- pgsql
deploy:
replicas: 3
update_config:
parallelism: 1
delay: 30s
order: stop-first
failure_action: pause
pgkeeper1:
image: sorintlab/stolon:master-pg10
hostname: pgkeeper1
command:
- gosu
- stolon
- stolon-keeper
- --pg-listen-address=pgkeeper1
- --pg-repl-username=replica
- --uid=pgkeeper1
- --pg-su-username=postgres
- --pg-su-passwordfile=/run/secrets/pgsql
- --pg-repl-passwordfile=/run/secrets/pgsql_repl
- --data-dir=/var/lib/postgresql/data
- --cluster-name=stolon-cluster
- --store-backend=etcdv3
- --store-endpoints=http://etcd1:2379,http://etcd2:2379,http://etcd3:2379
networks:
- etcd
- pgsql
environment:
- PGDATA=/var/lib/postgresql/data
volumes:
- pgkeeper1:/var/lib/postgresql/data
secrets:
- pgsql
- pgsql_repl
deploy:
replicas: 1
placement:
constraints: [node.labels.nodename == node1]
pgkeeper2:
image: sorintlab/stolon:master-pg10
hostname: pgkeeper2
command:
- gosu
- stolon
- stolon-keeper
- --pg-listen-address=pgkeeper2
- --pg-repl-username=replica
- --uid=pgkeeper2
- --pg-su-username=postgres
- --pg-su-passwordfile=/run/secrets/pgsql
- --pg-repl-passwordfile=/run/secrets/pgsql_repl
- --data-dir=/var/lib/postgresql/data
- --cluster-name=stolon-cluster
- --store-backend=etcdv3
- --store-endpoints=http://etcd1:2379,http://etcd2:2379,http://etcd3:2379
networks:
- etcd
- pgsql
environment:
- PGDATA=/var/lib/postgresql/data
volumes:
- pgkeeper2:/var/lib/postgresql/data
secrets:
- pgsql
- pgsql_repl
deploy:
replicas: 1
placement:
constraints: [node.labels.nodename == node2]
pgkeeper3:
image: sorintlab/stolon:master-pg10
hostname: pgkeeper3
command:
- gosu
- stolon
- stolon-keeper
- --pg-listen-address=pgkeeper3
- --pg-repl-username=replica
- --uid=pgkeeper3
- --pg-su-username=postgres
- --pg-su-passwordfile=/run/secrets/pgsql
- --pg-repl-passwordfile=/run/secrets/pgsql_repl
- --data-dir=/var/lib/postgresql/data
- --cluster-name=stolon-cluster
- --store-backend=etcdv3
- --store-endpoints=http://etcd1:2379,http://etcd2:2379,http://etcd3:2379
networks:
- etcd
- pgsql
environment:
- PGDATA=/var/lib/postgresql/data
volumes:
- pgkeeper3:/var/lib/postgresql/data
secrets:
- pgsql
- pgsql_repl
deploy:
replicas: 1
placement:
constraints: [node.labels.nodename == node3]
postgresql:
image: sorintlab/stolon:master-pg10
command: gosu stolon stolon-proxy --listen-address 0.0.0.0 --cluster-name stolon-cluster --store-backend=etcdv3 --store-endpoints http://etcd1:2379,http://etcd2:2379,http://etcd3:2379
networks:
- etcd
- pgsql
deploy:
replicas: 3
update_config:
parallelism: 1
delay: 30s
order: stop-first
failure_action: rollback
volumes:
pgkeeper1:
driver: local
driver_opts:
type: none
o: bind
device: "/srv/pgsql"
pgkeeper2:
driver: local
driver_opts:
type: none
o: bind
device: "/srv/pgsql"
pgkeeper3:
driver: local
driver_opts:
type: none
o: bind
device: "/srv/pgsql"
secrets:
pgsql:
file: "/srv/docker/postgres"
pgsql_repl:
file: "/srv/docker/replica"
networks:
etcd:
external: true
pgsql:
external: trueNou jenere sekrè epi sèvi ak dosye a:
# </dev/urandom tr -dc 234567890qwertyuopasdfghjkzxcvbnmQWERTYUPASDFGHKLZXCVBNM | head -c $(((RANDOM%3)+15)) > /srv/docker/replica
# </dev/urandom tr -dc 234567890qwertyuopasdfghjkzxcvbnmQWERTYUPASDFGHKLZXCVBNM | head -c $(((RANDOM%3)+15)) > /srv/docker/postgres
# docker stack deploy --compose-file 01pgsql.yml pgsqlApre kèk tan (gade pwodiksyon an nan lòd la sèvis docker lske tout sèvis yo moute) nou inisyalize gwoup Postgresql la:
# docker exec $(docker ps | awk '/pgkeeper/ {print $1}') stolonctl --cluster-name=stolon-cluster --store-backend=etcdv3 --store-endpoints=http://etcd1:2379,http://etcd2:2379,http://etcd3:2379 initTcheke preparasyon pou gwoup Postgresql la:
# docker exec $(docker ps | awk '/pgkeeper/ {print $1}') stolonctl --cluster-name=stolon-cluster --store-backend=etcdv3 --store-endpoints=http://etcd1:2379,http://etcd2:2379,http://etcd3:2379 status
=== Active sentinels ===
ID LEADER
26baa11d false
74e98768 false
a8cb002b true
=== Active proxies ===
ID
4d233826
9f562f3b
b0c79ff1
=== Keepers ===
UID HEALTHY PG LISTENADDRESS PG HEALTHY PG WANTEDGENERATION PG CURRENTGENERATION
pgkeeper1 true pgkeeper1:5432 true 2 2
pgkeeper2 true pgkeeper2:5432 true 2 2
pgkeeper3 true pgkeeper3:5432 true 3 3
=== Cluster Info ===
Master Keeper: pgkeeper3
===== Keepers/DB tree =====
pgkeeper3 (master)
├─pgkeeper2
└─pgkeeper1
Nou konfigirasyon traefik pou louvri aksè nan resipyan soti deyò:
03traefik.yml
version: '3.7'
services:
traefik:
image: traefik:latest
command: >
--log.level=INFO
--providers.docker=true
--entryPoints.web.address=:80
--providers.providersThrottleDuration=2
--providers.docker.watch=true
--providers.docker.swarmMode=true
--providers.docker.swarmModeRefreshSeconds=15s
--providers.docker.exposedbydefault=false
--accessLog.bufferingSize=0
--api=true
--api.dashboard=true
--api.insecure=true
networks:
- traefik
ports:
- 80:80
volumes:
- /var/run/docker.sock:/var/run/docker.sock
deploy:
replicas: 3
placement:
constraints:
- node.role == manager
preferences:
- spread: node.id
labels:
- traefik.enable=true
- traefik.http.routers.traefik.rule=Host(`traefik.example.com`)
- traefik.http.services.traefik.loadbalancer.server.port=8080
- traefik.docker.network=traefik
networks:
traefik:
external: true# docker stack deploy --compose-file 03traefik.yml traefikNou lanse Redis Cluster, pou fè sa nou kreye yon anyè depo sou tout nœuds:
# mkdir -p /srv/redis05redis.yml
version: '3.7'
services:
redis-master:
image: 'bitnami/redis:latest'
networks:
- redis
ports:
- '6379:6379'
environment:
- REDIS_REPLICATION_MODE=master
- REDIS_PASSWORD=xxxxxxxxxxx
deploy:
mode: global
restart_policy:
condition: any
volumes:
- 'redis:/opt/bitnami/redis/etc/'
redis-replica:
image: 'bitnami/redis:latest'
networks:
- redis
ports:
- '6379'
depends_on:
- redis-master
environment:
- REDIS_REPLICATION_MODE=slave
- REDIS_MASTER_HOST=redis-master
- REDIS_MASTER_PORT_NUMBER=6379
- REDIS_MASTER_PASSWORD=xxxxxxxxxxx
- REDIS_PASSWORD=xxxxxxxxxxx
deploy:
mode: replicated
replicas: 3
update_config:
parallelism: 1
delay: 10s
restart_policy:
condition: any
redis-sentinel:
image: 'bitnami/redis:latest'
networks:
- redis
ports:
- '16379'
depends_on:
- redis-master
- redis-replica
entrypoint: |
bash -c 'bash -s <<EOF
"/bin/bash" -c "cat <<EOF > /opt/bitnami/redis/etc/sentinel.conf
port 16379
dir /tmp
sentinel monitor master-node redis-master 6379 2
sentinel down-after-milliseconds master-node 5000
sentinel parallel-syncs master-node 1
sentinel failover-timeout master-node 5000
sentinel auth-pass master-node xxxxxxxxxxx
sentinel announce-ip redis-sentinel
sentinel announce-port 16379
EOF"
"/bin/bash" -c "redis-sentinel /opt/bitnami/redis/etc/sentinel.conf"
EOF'
deploy:
mode: global
restart_policy:
condition: any
volumes:
redis:
driver: local
driver_opts:
type: 'none'
o: 'bind'
device: "/srv/redis"
networks:
redis:
external: true# docker stack deploy --compose-file 05redis.yml redisAjoute Docker Rejis:
06registry.yml
version: '3.7'
services:
registry:
image: registry:2.6
networks:
- traefik
volumes:
- registry_data:/var/lib/registry
deploy:
replicas: 1
placement:
constraints: [node.role == manager]
restart_policy:
condition: on-failure
labels:
- traefik.enable=true
- traefik.http.routers.registry.rule=Host(`registry.example.com`)
- traefik.http.services.registry.loadbalancer.server.port=5000
- traefik.docker.network=traefik
volumes:
registry_data:
driver: local
driver_opts:
type: none
o: bind
device: "/srv/docker/registry"
networks:
traefik:
external: true# mkdir /srv/docker/registry
# docker stack deploy --compose-file 06registry.yml registryEpi finalman - GitLab:
08gitlab-runner.yml
version: '3.7'
services:
gitlab:
image: gitlab/gitlab-ce:latest
networks:
- pgsql
- redis
- traefik
- gitlab
ports:
- 22222:22
environment:
GITLAB_OMNIBUS_CONFIG: |
postgresql['enable'] = false
redis['enable'] = false
gitlab_rails['registry_enabled'] = false
gitlab_rails['db_username'] = "gitlab"
gitlab_rails['db_password'] = "XXXXXXXXXXX"
gitlab_rails['db_host'] = "postgresql"
gitlab_rails['db_port'] = "5432"
gitlab_rails['db_database'] = "gitlab"
gitlab_rails['db_adapter'] = 'postgresql'
gitlab_rails['db_encoding'] = 'utf8'
gitlab_rails['redis_host'] = 'redis-master'
gitlab_rails['redis_port'] = '6379'
gitlab_rails['redis_password'] = 'xxxxxxxxxxx'
gitlab_rails['smtp_enable'] = true
gitlab_rails['smtp_address'] = "smtp.yandex.ru"
gitlab_rails['smtp_port'] = 465
gitlab_rails['smtp_user_name'] = "noreply@example.com"
gitlab_rails['smtp_password'] = "xxxxxxxxx"
gitlab_rails['smtp_domain'] = "example.com"
gitlab_rails['gitlab_email_from'] = 'noreply@example.com'
gitlab_rails['smtp_authentication'] = "login"
gitlab_rails['smtp_tls'] = true
gitlab_rails['smtp_enable_starttls_auto'] = true
gitlab_rails['smtp_openssl_verify_mode'] = 'peer'
external_url 'http://gitlab.example.com/'
gitlab_rails['gitlab_shell_ssh_port'] = 22222
volumes:
- gitlab_conf:/etc/gitlab
- gitlab_logs:/var/log/gitlab
- gitlab_data:/var/opt/gitlab
deploy:
mode: replicated
replicas: 1
placement:
constraints:
- node.role == manager
labels:
- traefik.enable=true
- traefik.http.routers.gitlab.rule=Host(`gitlab.example.com`)
- traefik.http.services.gitlab.loadbalancer.server.port=80
- traefik.docker.network=traefik
gitlab-runner:
image: gitlab/gitlab-runner:latest
networks:
- gitlab
volumes:
- gitlab_runner_conf:/etc/gitlab
- /var/run/docker.sock:/var/run/docker.sock
deploy:
mode: replicated
replicas: 1
placement:
constraints:
- node.role == manager
volumes:
gitlab_conf:
driver: local
driver_opts:
type: none
o: bind
device: "/srv/docker/gitlab/conf"
gitlab_logs:
driver: local
driver_opts:
type: none
o: bind
device: "/srv/docker/gitlab/logs"
gitlab_data:
driver: local
driver_opts:
type: none
o: bind
device: "/srv/docker/gitlab/data"
gitlab_runner_conf:
driver: local
driver_opts:
type: none
o: bind
device: "/srv/docker/gitlab/runner"
networks:
pgsql:
external: true
redis:
external: true
traefik:
external: true
gitlab:
external: true# mkdir -p /srv/docker/gitlab/conf
# mkdir -p /srv/docker/gitlab/logs
# mkdir -p /srv/docker/gitlab/data
# mkdir -p /srv/docker/gitlab/runner
# docker stack deploy --compose-file 08gitlab-runner.yml gitlabEta final gwoup la ak sèvis yo:
# docker service ls
ID NAME MODE REPLICAS IMAGE PORTS
lef9n3m92buq etcd_etcd1 replicated 1/1 quay.io/coreos/etcd:latest
ij6uyyo792x5 etcd_etcd2 replicated 1/1 quay.io/coreos/etcd:latest
fqttqpjgp6pp etcd_etcd3 replicated 1/1 quay.io/coreos/etcd:latest
hq5iyga28w33 gitlab_gitlab replicated 1/1 gitlab/gitlab-ce:latest *:22222->22/tcp
dt7s6vs0q4qc gitlab_gitlab-runner replicated 1/1 gitlab/gitlab-runner:latest
k7uoezno0h9n pgsql_pgkeeper1 replicated 1/1 sorintlab/stolon:master-pg10
cnrwul4r4nse pgsql_pgkeeper2 replicated 1/1 sorintlab/stolon:master-pg10
frflfnpty7tr pgsql_pgkeeper3 replicated 1/1 sorintlab/stolon:master-pg10
x7pqqchi52kq pgsql_pgsentinel replicated 3/3 sorintlab/stolon:master-pg10
mwu2wl8fti4r pgsql_postgresql replicated 3/3 sorintlab/stolon:master-pg10
9hkbe2vksbzb redis_redis-master global 3/3 bitnami/redis:latest *:6379->6379/tcp
l88zn8cla7dc redis_redis-replica replicated 3/3 bitnami/redis:latest *:30003->6379/tcp
1utp309xfmsy redis_redis-sentinel global 3/3 bitnami/redis:latest *:30002->16379/tcp
oteb824ylhyp registry_registry replicated 1/1 registry:2.6
qovrah8nzzu8 traefik_traefik replicated 3/3 traefik:latest *:80->80/tcp, *:443->443/tcpKi lòt bagay ki ka amelyore? Asire w ou configure Traefik pou kouri kontenè sou https, ajoute tls cryptage pou Postgresql ak Redis. Men, an jeneral, li ka deja bay devlopè kòm yon PoC. Ann gade kounye a altènativ a Docker.
podman
Yon lòt motè san patipri byen li te ye pou kouri resipyan gwoupe pa gous (gous, gwoup resipyan deplwaye ansanm). Kontrèman ak Docker, li pa bezwen okenn sèvis pou kouri kontenè; tout travay fèt nan bibliyotèk libpod la. Epitou ekri nan Go, mande pou yon OCI-konpatib ègzekutabl kouri kontenè, tankou runC.

Travay ak Podman se jeneralman okoumansman de sa pou Docker, nan pwen ke ou ka fè li tankou sa a (jan sa di pa anpil moun ki te eseye li, ki gen ladan otè a nan atik sa a):
$ alias docker=podmanepi ou ka kontinye travay. An jeneral, sitiyasyon an ak Podman trè enteresan, paske si vèsyon byen bonè nan Kubernetes te travay ak Docker, Lè sa a, alantou 2015, apre normalisation nan mond lan nan resipyan (OCI - Open Container Initiative) ak divizyon an nan Docker nan containerd ak runC, yon altènativ a Docker pou kouri nan Kubernetes te devlope: CRI-O. Podman nan sans sa a se yon altènativ a Docker, bati sou prensip Kubernetes, ki gen ladan resipyan gwoupman, men objektif prensipal pwojè a se lanse resipyan style Docker san sèvis adisyonèl. Pou rezon evidan, pa gen okenn mòd swarm, depi devlopè yo klèman di ke si ou bezwen yon gwoup, pran Kubernetes.
Enstalasyon
Pou enstalasyon nan Centos 7, jis aktive depo Extras la epi enstale tout bagay lè l sèvi avèk kòmandman sa a:
# yum -y install podmanLòt karakteristik
Podman ka jenere inite pou systemd, kidonk rezoud pwoblèm nan kòmanse resipyan apre yon rdemare sèvè. Anplis de sa, systemd deklare travay kòrèkteman kòm pid 1 nan veso a. Gen yon zouti buildah separe pou bati resipyan, gen tou zouti twazyèm pati - analogue nan docker-compose, ki tou jenere fichye konfigirasyon konpatib ak Kubernetes, kidonk tranzisyon an soti nan Podman nan Kubernetes senplifye otank posib.
Travay ak Podman
Depi pa gen okenn mòd swarm (nou sipoze chanje nan Kubernetes si yon grap bezwen), nou pral kolekte li nan resipyan separe.
Enstale podman-compose:
# yum -y install python3-pip
# pip3 install podman-composeFichye a konfigirasyon ki kapab lakòz pou podman se yon ti kras diferan, kidonk pou egzanp nou te oblije deplase yon seksyon komèsan separe dirèkteman nan seksyon an ak sèvis yo.
gitlab-podman.yml
version: '3.7'
services:
gitlab:
image: gitlab/gitlab-ce:latest
hostname: gitlab.example.com
restart: unless-stopped
environment:
GITLAB_OMNIBUS_CONFIG: |
gitlab_rails['gitlab_shell_ssh_port'] = 22222
ports:
- "80:80"
- "22222:22"
volumes:
- /srv/podman/gitlab/conf:/etc/gitlab
- /srv/podman/gitlab/data:/var/opt/gitlab
- /srv/podman/gitlab/logs:/var/log/gitlab
networks:
- gitlab
gitlab-runner:
image: gitlab/gitlab-runner:alpine
restart: unless-stopped
depends_on:
- gitlab
volumes:
- /srv/podman/gitlab/runner:/etc/gitlab-runner
- /var/run/docker.sock:/var/run/docker.sock
networks:
- gitlab
networks:
gitlab:# podman-compose -f gitlab-runner.yml -d upRezilta:
# podman ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
da53da946c01 docker.io/gitlab/gitlab-runner:alpine run --user=gitlab... About a minute ago Up About a minute ago 0.0.0.0:22222->22/tcp, 0.0.0.0:80->80/tcp root_gitlab-runner_1
781c0103c94a docker.io/gitlab/gitlab-ce:latest /assets/wrapper About a minute ago Up About a minute ago 0.0.0.0:22222->22/tcp, 0.0.0.0:80->80/tcp root_gitlab_1Ann wè sa li jenere pou systemd ak kubernetes, pou sa nou bezwen chèche non oswa id gous la:
# podman pod ls
POD ID NAME STATUS CREATED # OF CONTAINERS INFRA ID
71fc2b2a5c63 root Running 11 minutes ago 3 db40ab8bf84bKubernetes:
# podman generate kube 71fc2b2a5c63
# Generation of Kubernetes YAML is still under development!
#
# Save the output of this file and use kubectl create -f to import
# it into Kubernetes.
#
# Created with podman-1.6.4
apiVersion: v1
kind: Pod
metadata:
creationTimestamp: "2020-07-29T19:22:40Z"
labels:
app: root
name: root
spec:
containers:
- command:
- /assets/wrapper
env:
- name: PATH
value: /opt/gitlab/embedded/bin:/opt/gitlab/bin:/assets:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin
- name: TERM
value: xterm
- name: HOSTNAME
value: gitlab.example.com
- name: container
value: podman
- name: GITLAB_OMNIBUS_CONFIG
value: |
gitlab_rails['gitlab_shell_ssh_port'] = 22222
- name: LANG
value: C.UTF-8
image: docker.io/gitlab/gitlab-ce:latest
name: rootgitlab1
ports:
- containerPort: 22
hostPort: 22222
protocol: TCP
- containerPort: 80
hostPort: 80
protocol: TCP
resources: {}
securityContext:
allowPrivilegeEscalation: true
capabilities: {}
privileged: false
readOnlyRootFilesystem: false
volumeMounts:
- mountPath: /var/opt/gitlab
name: srv-podman-gitlab-data
- mountPath: /var/log/gitlab
name: srv-podman-gitlab-logs
- mountPath: /etc/gitlab
name: srv-podman-gitlab-conf
workingDir: /
- command:
- run
- --user=gitlab-runner
- --working-directory=/home/gitlab-runner
env:
- name: PATH
value: /usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin
- name: TERM
value: xterm
- name: HOSTNAME
- name: container
value: podman
image: docker.io/gitlab/gitlab-runner:alpine
name: rootgitlab-runner1
resources: {}
securityContext:
allowPrivilegeEscalation: true
capabilities: {}
privileged: false
readOnlyRootFilesystem: false
volumeMounts:
- mountPath: /etc/gitlab-runner
name: srv-podman-gitlab-runner
- mountPath: /var/run/docker.sock
name: var-run-docker.sock
workingDir: /
volumes:
- hostPath:
path: /srv/podman/gitlab/runner
type: Directory
name: srv-podman-gitlab-runner
- hostPath:
path: /var/run/docker.sock
type: File
name: var-run-docker.sock
- hostPath:
path: /srv/podman/gitlab/data
type: Directory
name: srv-podman-gitlab-data
- hostPath:
path: /srv/podman/gitlab/logs
type: Directory
name: srv-podman-gitlab-logs
- hostPath:
path: /srv/podman/gitlab/conf
type: Directory
name: srv-podman-gitlab-conf
status: {}Sistèm:
# podman generate systemd 71fc2b2a5c63
# pod-71fc2b2a5c6346f0c1c86a2dc45dbe78fa192ea02aac001eb8347ccb8c043c26.service
# autogenerated by Podman 1.6.4
# Thu Jul 29 15:23:28 EDT 2020
[Unit]
Description=Podman pod-71fc2b2a5c6346f0c1c86a2dc45dbe78fa192ea02aac001eb8347ccb8c043c26.service
Documentation=man:podman-generate-systemd(1)
Requires=container-781c0103c94aaa113c17c58d05ddabf8df4bf39707b664abcf17ed2ceff467d3.service container-da53da946c01449f500aa5296d9ea6376f751948b17ca164df438b7df6607864.service
Before=container-781c0103c94aaa113c17c58d05ddabf8df4bf39707b664abcf17ed2ceff467d3.service container-da53da946c01449f500aa5296d9ea6376f751948b17ca164df438b7df6607864.service
[Service]
Restart=on-failure
ExecStart=/usr/bin/podman start db40ab8bf84bf35141159c26cb6e256b889c7a98c0418eee3c4aa683c14fccaa
ExecStop=/usr/bin/podman stop -t 10 db40ab8bf84bf35141159c26cb6e256b889c7a98c0418eee3c4aa683c14fccaa
KillMode=none
Type=forking
PIDFile=/var/run/containers/storage/overlay-containers/db40ab8bf84bf35141159c26cb6e256b889c7a98c0418eee3c4aa683c14fccaa/userdata/conmon.pid
[Install]
WantedBy=multi-user.target
# container-da53da946c01449f500aa5296d9ea6376f751948b17ca164df438b7df6607864.service
# autogenerated by Podman 1.6.4
# Thu Jul 29 15:23:28 EDT 2020
[Unit]
Description=Podman container-da53da946c01449f500aa5296d9ea6376f751948b17ca164df438b7df6607864.service
Documentation=man:podman-generate-systemd(1)
RefuseManualStart=yes
RefuseManualStop=yes
BindsTo=pod-71fc2b2a5c6346f0c1c86a2dc45dbe78fa192ea02aac001eb8347ccb8c043c26.service
After=pod-71fc2b2a5c6346f0c1c86a2dc45dbe78fa192ea02aac001eb8347ccb8c043c26.service
[Service]
Restart=on-failure
ExecStart=/usr/bin/podman start da53da946c01449f500aa5296d9ea6376f751948b17ca164df438b7df6607864
ExecStop=/usr/bin/podman stop -t 10 da53da946c01449f500aa5296d9ea6376f751948b17ca164df438b7df6607864
KillMode=none
Type=forking
PIDFile=/var/run/containers/storage/overlay-containers/da53da946c01449f500aa5296d9ea6376f751948b17ca164df438b7df6607864/userdata/conmon.pid
[Install]
WantedBy=multi-user.target
# container-781c0103c94aaa113c17c58d05ddabf8df4bf39707b664abcf17ed2ceff467d3.service
# autogenerated by Podman 1.6.4
# Thu Jul 29 15:23:28 EDT 2020
[Unit]
Description=Podman container-781c0103c94aaa113c17c58d05ddabf8df4bf39707b664abcf17ed2ceff467d3.service
Documentation=man:podman-generate-systemd(1)
RefuseManualStart=yes
RefuseManualStop=yes
BindsTo=pod-71fc2b2a5c6346f0c1c86a2dc45dbe78fa192ea02aac001eb8347ccb8c043c26.service
After=pod-71fc2b2a5c6346f0c1c86a2dc45dbe78fa192ea02aac001eb8347ccb8c043c26.service
[Service]
Restart=on-failure
ExecStart=/usr/bin/podman start 781c0103c94aaa113c17c58d05ddabf8df4bf39707b664abcf17ed2ceff467d3
ExecStop=/usr/bin/podman stop -t 10 781c0103c94aaa113c17c58d05ddabf8df4bf39707b664abcf17ed2ceff467d3
KillMode=none
Type=forking
PIDFile=/var/run/containers/storage/overlay-containers/781c0103c94aaa113c17c58d05ddabf8df4bf39707b664abcf17ed2ceff467d3/userdata/conmon.pid
[Install]
WantedBy=multi-user.targetMalerezman, apa de lanse kontenè, inite pwodwi a pou systemd pa fè anyen lòt bagay (pa egzanp, netwaye ansyen veso yo lè yon sèvis konsa rekòmanse), kidonk w ap oblije ekri bagay sa yo tèt ou.
Nan prensip, Podman se ase pou eseye sa ki resipyan yo ye, transfere ansyen konfigirasyon pou Docker-konpoze, ak Lè sa a, deplase nan direksyon Kubernetes, si ou bezwen yon gwoup, oswa jwenn yon altènatif pi fasil-a-itilize nan Docker.
rkt
Pwojè apeprè sis mwa de sa akòz lefèt ke RedHat te achte li, kidonk mwen pa pral rete sou li an plis detay. An jeneral, li te kite yon enpresyon trè bon, men konpare ak Docker ak espesyalman Podman, li sanble yon konbine. Te gen tou yon distribisyon CoreOS bati sou tèt rkt (byenke yo orijinèlman te gen Docker), men sa a te fini tou nan sipò apre RedHat achte a.
Flash
Plis , otè a ki jis te vle bati ak kouri kontenè. Jije pa dokiman an ak kòd, otè a pa t 'swiv estanda yo, men tou senpleman deside ekri aplikasyon pwòp tèt li, ki, nan prensip, li te fè.
Jwenn
Sitiyasyon an ak Kubernetes se byen enteresan: sou yon bò, ak Docker ou ka bati yon gwoup (nan mòd swarm), ak ki ou ka menm kouri anviwònman pwodwi pou kliyan, sa a se laverite espesyalman pou ti ekip (3-5 moun) , oswa ak yon ti chaj jeneral, oswa mank de dezi yo konprann sibtilite yo nan mete kanpe Kubernetes, ki gen ladan pou chaj segondè.
Podman pa bay konpatibilite konplè, men li gen yon avantaj enpòtan - konpatibilite ak Kubernetes, ki gen ladan zouti adisyonèl (buildah ak lòt moun). Se poutèt sa, mwen pral apwoche chwa a nan yon zouti pou travay jan sa a: pou ti ekip, oswa ak yon bidjè limite - Docker (ak yon mòd swarm posib), pou devlope pou tèt mwen sou yon lokalhost pèsonèl - Podman kamarad, ak pou tout lòt moun. - Kubernetes.
Mwen pa sèten sitiyasyon an ak Docker pap chanje nan lavni, apre tou, yo se pyonye, epi piti piti y ap vin estanda, men Podman, malgre tout enpèfeksyon li yo (k ap travay sèlman sou Linux, pa gen okenn aksyon gwoupman, asanblaj ak lòt aksyon ki fèt pa solisyon twazyèm pati) lavni an pi klè, kidonk mwen envite tout moun pou diskite sou rezilta sa yo nan kòmantè yo.
PS Nan dat 3 out nou lanse "", kote ou ka aprann plis sou travay li. Nou pral analize tout zouti li yo: soti nan abstraksyon debaz nan paramèt rezo a, nuans nan travay ak divès sistèm opere ak langaj pwogramasyon. Ou pral vin abitye ak teknoloji a epi konprann ki kote ak ki jan pi bon yo sèvi ak Docker. Nou pral pataje tou ka pi bon pratik yo.
Pri-lòd anvan lage: RUB 5000. Ou ka wè pwogram kou videyo Docker la .
Sous: www.habr.com


