នរណាម្នាក់ដែលបានព្យាយាមដំណើរការម៉ាស៊ីននិម្មិតនៅក្នុងពពក ដឹងយ៉ាងច្បាស់ថាច្រក RDP ស្តង់ដារ ប្រសិនបើបើកទុក នឹងត្រូវបានវាយប្រហារស្ទើរតែភ្លាមៗដោយរលកនៃការព្យាយាមបង្ខំពាក្យសម្ងាត់ពីអាសយដ្ឋាន IP ផ្សេងៗជុំវិញពិភពលោក។
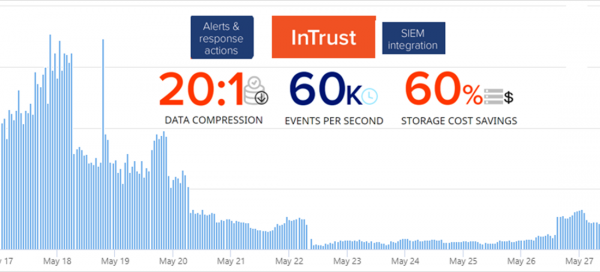
នៅក្នុងអត្ថបទនេះខ្ញុំនឹងបង្ហាញពីរបៀបធ្វើ អ្នកអាចកំណត់រចនាសម្ព័ន្ធការឆ្លើយតបដោយស្វ័យប្រវត្តិចំពោះ brute force ដោយបន្ថែមច្បាប់ថ្មីទៅជញ្ជាំងភ្លើង។ InTrust គឺ សម្រាប់ការប្រមូល វិភាគ និងរក្សាទុកទិន្នន័យដែលមិនមានរចនាសម្ព័ន្ធ ដែលមានប្រតិកម្មកំណត់ជាមុនរាប់រយរួចទៅហើយចំពោះប្រភេទផ្សេងៗនៃការវាយប្រហារ។
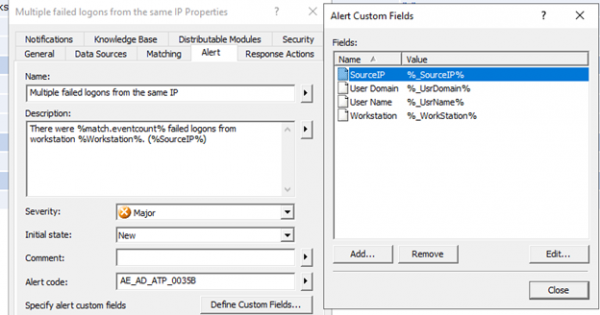
នៅក្នុង Quest InTrust អ្នកអាចកំណត់រចនាសម្ព័ន្ធសកម្មភាពឆ្លើយតប នៅពេលដែលច្បាប់ត្រូវបានកេះ។ ពីភ្នាក់ងារប្រមូលកំណត់ហេតុ InTrust ទទួលបានសារអំពីការប៉ុនប៉ងអនុញ្ញាតមិនបានសម្រេចនៅលើស្ថានីយការងារ ឬម៉ាស៊ីនមេ។ ដើម្បីកំណត់រចនាសម្ព័ន្ធការបន្ថែមអាសយដ្ឋាន IP ថ្មីទៅជញ្ជាំងភ្លើង អ្នកត្រូវចម្លងច្បាប់ផ្ទាល់ខ្លួនដែលមានស្រាប់សម្រាប់រកមើលការអនុញ្ញាតដែលបរាជ័យជាច្រើន ហើយបើកច្បាប់ចម្លងរបស់វាសម្រាប់កែសម្រួល៖
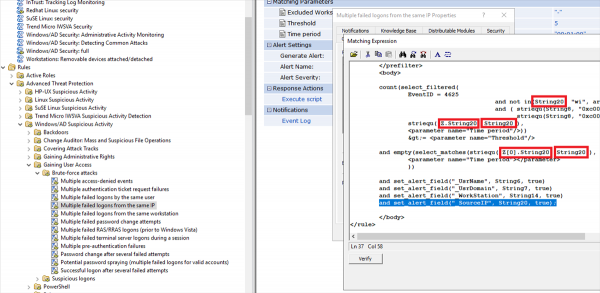
ព្រឹត្តិការណ៍នៅក្នុងទស្សនាវដ្តី Windows ប្រើអ្វីដែលហៅថា InsertionString។ (នេះគឺជាការចូលប្រព័ន្ធដែលមិនជោគជ័យ) ហើយអ្នកនឹងឃើញថាវាលដែលយើងចាប់អារម្មណ៍ត្រូវបានរក្សាទុកនៅក្នុង InsertionString14 (ឈ្មោះកន្លែងធ្វើការ) និង InsertionString20 (អាសយដ្ឋានបណ្តាញប្រភព)។ នៅពេលវាយប្រហារពីអ៊ីនធឺណិត វាលឈ្មោះស្ថានីយការងារនឹងទំនងភាគច្រើន។ ទទេ ដូច្នេះកន្លែងនេះមានសារៈសំខាន់ជំនួសតម្លៃពីអាសយដ្ឋានបណ្តាញប្រភព។
នេះគឺជាអ្វីដែលអត្ថបទនៃព្រឹត្តិការណ៍ 4625 មើលទៅដូចនេះ:
An account failed to log on.
Subject:
Security ID: S-1-5-21-1135140816-2109348461-2107143693-500
Account Name: ALebovsky
Account Domain: LOGISTICS
Logon ID: 0x2a88a
Logon Type: 2
Account For Which Logon Failed:
Security ID: S-1-0-0
Account Name: Paul
Account Domain: LOGISTICS
Failure Information:
Failure Reason: Account locked out.
Status: 0xc0000234
Sub Status: 0x0
Process Information:
Caller Process ID: 0x3f8
Caller Process Name: C:WindowsSystem32svchost.exe
Network Information:
Workstation Name: DCC1
Source Network Address: ::1
Source Port: 0
Detailed Authentication Information:
Logon Process: seclogo
Authentication Package: Negotiate
Transited Services: -
Package Name (NTLM only): -
Key Length: 0
This event is generated when a logon request fails. It is generated on the computer where access was attempted.
The Subject fields indicate the account on the local system which requested the logon. This is most commonly a service such as the Server service, or a local process such as Winlogon.exe or Services.exe.
The Logon Type field indicates the kind of logon that was requested. The most common types are 2 (interactive) and 3 (network).
The Process Information fields indicate which account and process on the system requested the logon.
The Network Information fields indicate where a remote logon request originated. Workstation name is not always available and may be left blank in some cases.
The authentication information fields provide detailed information about this specific logon request.
- Transited services indicate which intermediate services have participated in this logon request.
- Package name indicates which sub-protocol was used among the NTLM protocols.
- Key length indicates the length of the generated session key. This will be 0 if no session key was requested.
លើសពីនេះ យើងនឹងបន្ថែមតម្លៃអាសយដ្ឋានបណ្តាញប្រភពទៅអត្ថបទព្រឹត្តិការណ៍។
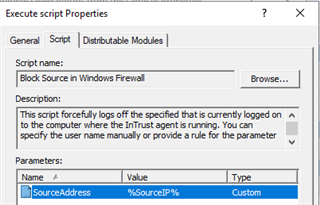
បន្ទាប់មកអ្នកត្រូវបន្ថែមស្គ្រីបដែលនឹងរារាំងអាសយដ្ឋាន IP នៅក្នុងជញ្ជាំងភ្លើង Windowsខាងក្រោមនេះជាឧទាហរណ៍មួយដែលអាចប្រើបានសម្រាប់រឿងនេះ។
ស្គ្រីបសម្រាប់ដំឡើងជញ្ជាំងភ្លើង
param(
[Parameter(Mandatory = $true)]
[ValidateNotNullOrEmpty()]
[string]
$SourceAddress
)
$SourceAddress = $SourceAddress.Trim()
$ErrorActionPreference = 'Stop'
$ruleName = 'Quest-InTrust-Block-Failed-Logons'
$ruleDisplayName = 'Quest InTrust: Blocks IP addresses from failed logons'
function Get-BlockedIps {
(Get-NetFirewallRule -Name $ruleName -ErrorAction SilentlyContinue | get-netfirewalladdressfilter).RemoteAddress
}
$blockedIps = Get-BlockedIps
$allIps = [array]$SourceAddress + [array]$blockedIps | Select-Object -Unique | Sort-Object
if (Get-NetFirewallRule -Name $ruleName -ErrorAction SilentlyContinue) {
Set-NetFirewallRule -Name $ruleName -RemoteAddress $allIps
} else {
New-NetFirewallRule -Name $ruleName -DisplayName $ruleDisplayName -Direction Inbound -Action Block -RemoteAddress $allIps
}
ឥឡូវនេះ អ្នកអាចប្តូរឈ្មោះច្បាប់ និងការពិពណ៌នា ដើម្បីជៀសវាងការភាន់ច្រលំនៅពេលក្រោយ។
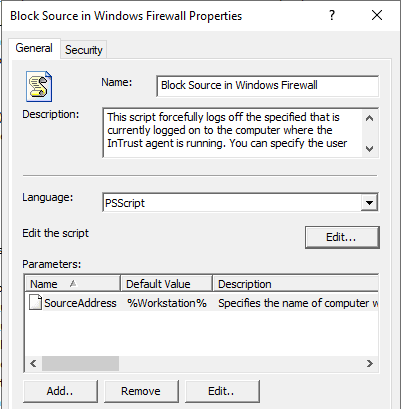
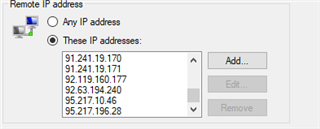
ឥឡូវអ្នកត្រូវបន្ថែមស្គ្រីបនេះជាសកម្មភាពឆ្លើយតបទៅនឹងច្បាប់ បើកដំណើរការច្បាប់ និងធានាថាច្បាប់ដែលត្រូវគ្នាត្រូវបានបើកនៅក្នុងគោលការណ៍ត្រួតពិនិត្យពេលវេលាជាក់ស្តែង។ ភ្នាក់ងារត្រូវតែត្រូវបានបើកដើម្បីដំណើរការស្គ្រីបឆ្លើយតប ហើយត្រូវតែមានប៉ារ៉ាម៉ែត្រត្រឹមត្រូវដែលបានបញ្ជាក់។
បន្ទាប់ពីការកំណត់ត្រូវបានបញ្ចប់ ចំនួននៃការអនុញ្ញាតដែលមិនជោគជ័យបានថយចុះ 80%។ ចំណេញ? អស្ចារ្យណាស់!
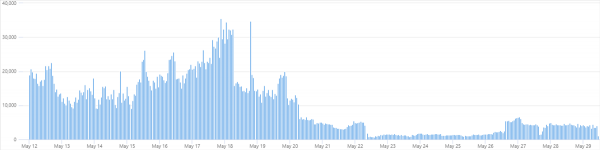
ជួនកាលការកើនឡើងតិចតួចកើតឡើងម្តងទៀត ប៉ុន្តែនេះគឺដោយសារតែការលេចឡើងនៃប្រភពថ្មីនៃការវាយប្រហារ។ បន្ទាប់មកអ្វីគ្រប់យ៉ាងចាប់ផ្តើមធ្លាក់ចុះម្តងទៀត។
ក្នុងរយៈពេលមួយសប្តាហ៍នៃការងារ អាសយដ្ឋាន IP ចំនួន 66 ត្រូវបានបន្ថែមទៅក្នុងច្បាប់ជញ្ជាំងភ្លើង។
ខាងក្រោមនេះគឺជាតារាងដែលមានឈ្មោះអ្នកប្រើប្រាស់ទូទៅចំនួន 10 ដែលត្រូវបានប្រើសម្រាប់ការព្យាយាមអនុញ្ញាត។
ឈ្មោះអ្នកប្រើ
ចំនួន
ជាភាគរយ
អ្នកគ្រប់គ្រង
1220235
40.78
គ្រប់គ្រង
672109
22.46
អ្នកប្រើ
219870
7.35
កុងតូសូ
126088
4.21
contoso.com
73048
2.44
អ្នកគ្រប់គ្រង
55319
1.85
ម៉ាស៊ីនបម្រើ
39403
1.32
sgazlabdc01.contoso.com
32177
1.08
អ្នកគ្រប់គ្រង
32377
1.08
sgazlabdc01
31259
1.04
ប្រាប់យើងនៅក្នុងមតិយោបល់ពីរបៀបដែលអ្នកឆ្លើយតបទៅនឹងការគំរាមកំហែងសុវត្ថិភាពព័ត៌មាន។ តើប្រព័ន្ធអ្វីដែលអ្នកប្រើ ហើយវាងាយស្រួលប៉ុណ្ណា?
ប្រសិនបើអ្នកចាប់អារម្មណ៍ចង់ឃើញ InTrust នៅក្នុងសកម្មភាព, នៅក្នុងទម្រង់មតិត្រឡប់នៅលើគេហទំព័ររបស់យើង ឬសរសេរមកខ្ញុំក្នុងសារផ្ទាល់ខ្លួន។
សូមអានអត្ថបទផ្សេងទៀតរបស់យើងស្តីពីសុវត្ថិភាពព័ត៌មាន៖
(អត្ថបទពេញនិយម)
ប្រភព: www.habr.com


