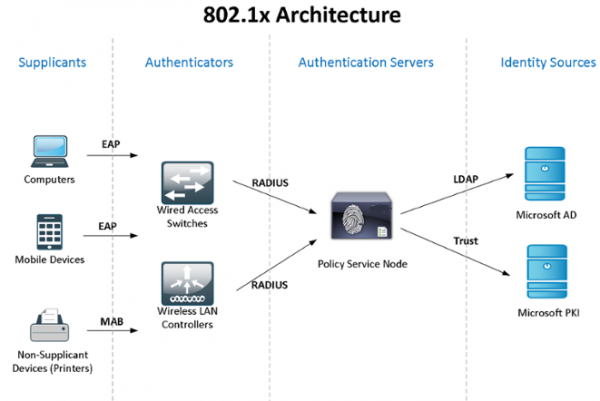
Consideremus in praxi usum Fenestra Active Directory + NPS (2 servientes ut culpae tolerantiae curent) + 802.1x norma ad accessum moderandi et authenticas utentium - domain computatorum - machinis. Theoriam cognoscere potes secundum vexillum in Vicipaedia, ad nexum:
Cum "laboratorium meum" in opibus limitatur, partes NPS ac moderatoris dominii compatiuntur, sed commendo te adhuc eiusmodi officia critica separare.
Mores normas ignoro ut Fenestra NPS configurationes (polities) synchronas (policies), sic utemur Scriptis PowerShell emissis a munere schedularum (auctor meus est collega pristinus). Ad authenticas of domain computers et adinventiones quae non possunt 802.1x (phone, impressores, etc.), coetus policy configurabitur et coetus securitatis creabuntur.
In fine articuli, dicam tibi de aliquibus subtilitatibus operandi cum 802.1x - quomodo potes uti infatigabili virgas, dynamicas ACLs, etc. informationes communicabo de "glitches" quae deprehensae sunt. .
Incipere incipiamus cum deficientibus NPS in Fenestra Servo 2012R2 instituendis et configurandis (omnia in 2016 eadem sunt): per Servo Procurator -> Adauge muneribus et Features Veneficus, elige tantum Servo Network Policy.
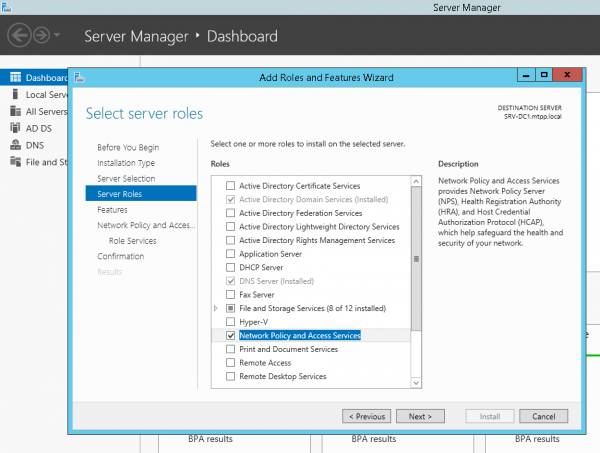
aut per PowerShell:
Install-WindowsFeature NPAS -IncludeManagementToolsDeclaratio parva - cum pro EAP Protectus (PEAP) certo opus erit libellum confirmantis authenticitatem ministri (congruis iuribus utendi), quod in computatoribus clientis fidebitur, tunc verisimillimum opus erit munus instituere. Certification auctoritati. Sed ponamus CA iam iam non installed...
Idem faciamus secundo servo. Faciamus folder pro C: Scripta scripta in utroque servers et retis folder in secundo servo SRV2NPS-about$
Faciamus PowerShell scriptor in primo servo C: ScriptsExport-NPS-config.ps1 cum sequenti contenti:
Export-NpsConfiguration -Path "SRV2NPS-config$NPS.xml"Postea negotium configurare in Task Sheduler: "Export-NpsConfiguration"
powershell -executionpolicy unrestricted -f "C:ScriptsExport-NPS-config.ps1" Curre pro omnibus users - Curre summa iura
Quotidie - Repetere negotium omne 10 minuta. intra VIII horas
In tergum NPS, significatum configurationis (politiae);
Faciamus scriptor PowerShell:
echo Import-NpsConfiguration -Path "c:NPS-configNPS.xml" >> C:ScriptsImport-NPS-config.ps1et omne munus exsequi X minuta;
powershell -executionpolicy unrestricted -f "C:ScriptsImport-NPS-config.ps1" Curre pro omnibus users - Curre summa iura
Quotidie - Repetere negotium omne 10 minuta. intra VIII horas
Nunc, ut reprimendam, addere NPS unum e servientibus(!) duas virgas in clientibus RADIUS (IP et Secret Shared), duas nexus rationes agendi: Wired-Iungo (Condition: "NAS portum genus est Aer") et WiFi-Enterprise (Condition: "NAS portus genus est IEEE 802.11"), necnon consilium retis Access Cisco Network machinae (Admins Network):
Условия:
Группы Windows - domainsg-network-admins
Ограничения:
Методы проверки подлинности - Проверка открытым текстом (PAP, SPAP)
Параметры:
Атрибуты RADIUS: Стандарт - Service-Type - Login
Зависящие от поставщика - Cisco-AV-Pair - Cisco - shell:priv-lvl=15In latere switch, sequentia occasus:
aaa new-model
aaa local authentication attempts max-fail 5
!
!
aaa group server radius NPS
server-private 192.168.38.151 auth-port 1812 acct-port 1813 key %shared_secret%
server-private 192.168.10.151 auth-port 1812 acct-port 1813 key %shared_secret%
!
aaa authentication login default group NPS local
aaa authentication dot1x default group NPS
aaa authorization console
aaa authorization exec default group NPS local if-authenticated
aaa authorization network default group NPS
!
aaa session-id common
!
identity profile default
!
dot1x system-auth-control
!
!
line vty 0 4
exec-timeout 5 0
transport input ssh
escape-character 99
line vty 5 15
exec-timeout 5 0
logging synchronous
transport input ssh
escape-character 99Post configurationem, post 10 minuta, omnes clientespolicyparametri appareant in tergum NPS et in virgas utentes rationi ActiveDirectory inire poterimus, membrum coetus ditionumg-retis-admins (quam ante creavimus).
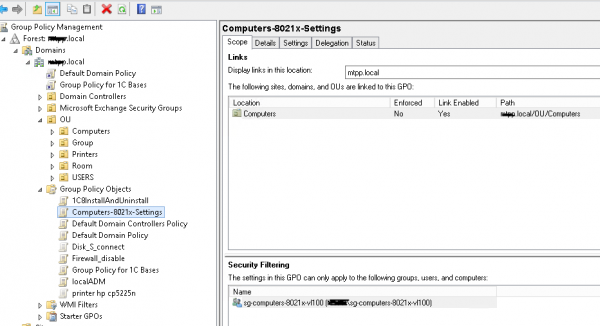
Transeamus ad constituendum Directorium Active - coetus ac tesserae rationes creo, coetus necessarios crea.
humus Excolo Computers-8021x-Optiones:
Computer Configuration (Enabled)
Policies
Windows Settings
Security Settings
System Services
Wired AutoConfig (Startup Mode: Automatic)
Wired Network (802.3) Policies
NPS-802-1x
Name NPS-802-1x
Description 802.1x
Global Settings
SETTING VALUE
Use Windows wired LAN network services for clients Enabled
Shared user credentials for network authentication Enabled
Network Profile
Security Settings
Enable use of IEEE 802.1X authentication for network access Enabled
Enforce use of IEEE 802.1X authentication for network access Disabled
IEEE 802.1X Settings
Computer Authentication Computer only
Maximum Authentication Failures 10
Maximum EAPOL-Start Messages Sent
Held Period (seconds)
Start Period (seconds)
Authentication Period (seconds)
Network Authentication Method Properties
Authentication method Protected EAP (PEAP)
Validate server certificate Enabled
Connect to these servers
Do not prompt user to authorize new servers or trusted certification authorities Disabled
Enable fast reconnect Enabled
Disconnect if server does not present cryptobinding TLV Disabled
Enforce network access protection Disabled
Authentication Method Configuration
Authentication method Secured password (EAP-MSCHAP v2)
Automatically use my Windows logon name and password(and domain if any) Enabled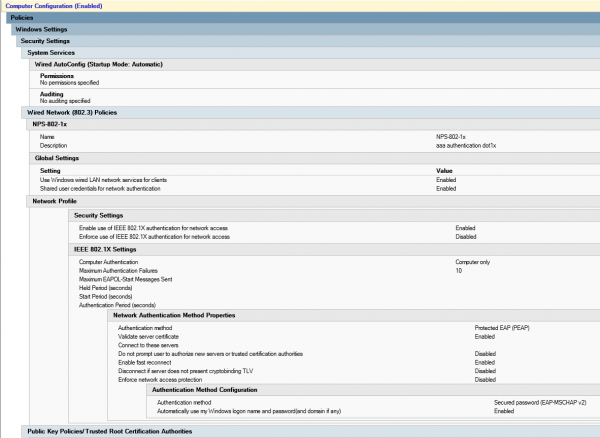
Sit scriptor coetus securitatem creare sg-computers-8021x-vl100, ubi computatores addemus quos in vlan 100 distribuere volumus et eliquare pro catervae coetus antea creato consilium huius coetus conformare volumus:
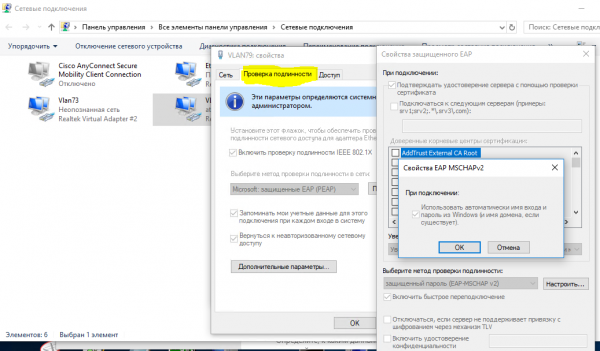
Potes cognoscere consilium bene operatum esse aperiendo "Network et Centrum Socius (Network et Internet Occasus) - Mutans adaptor occasus (configurans occasus adaptor) - Adaptor Properties", ubi videre possumus "authenticationem" tab:
Cum persuasum tibi est consilium bene applicari posse, consilium retis in NPS constituere potes et accessus ad portus graduum transitum.
Faciamus network consilium neag-computers-8021x-vl100:
Conditions:
Windows Groups - sg-computers-8021x-vl100
NAS Port Type - Ethernet
Constraints:
Authentication Methods - Microsoft: Protected EAP (PEAP) - Unencrypted authentication (PAP, SPAP)
NAS Port Type - Ethernet
Settings:
Standard:
Framed-MTU 1344
TunnelMediumType 802 (includes all 802 media plus Ethernet canonical format)
TunnelPrivateGroupId 100
TunnelType Virtual LANs (VLAN) 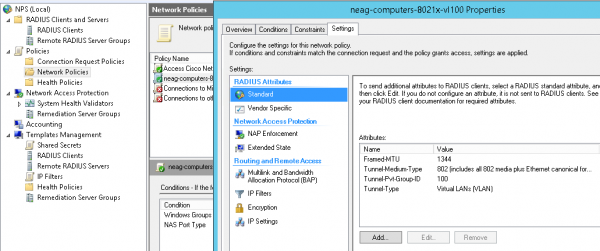
Typical occasus pro portum transitum (placere nota quod "multi-domain" authenticas typus adhibetur - Data & vox, et est etiam possibilitas authenticationis per mac electronicam. Per "tempus transitus" sensum facit uti in parametri:
authentication event fail action authorize vlan 100
authentication event no-response action authorize vlan 100
Vlan id non est "quarantina" una, sed eadem est ubi computatorium usoris post feliciter colligationem in se debet - donec confidimus omnia prout oportet operari. Iisdem parametris in aliis missionibus adhiberi possunt, exempli gratia, cum in hunc portum insanabilis commutatio inplenda est et omnes machinae cum eo coniunctae vis, quae authenticas non praeterierunt, in quamdam vlan ("quarantinam" cadere possunt.
switch portum occasus in 802.1x hospes modus multi domain modus
default int range Gi1/0/39-41
int range Gi1/0/39-41
shu
des PC-IPhone_802.1x
switchport mode access
switchport nonegotiate
switchport voice vlan 55
switchport port-security maximum 2
authentication event fail action authorize vlan 100
authentication event no-response action authorize vlan 100
authentication host-mode multi-domain
authentication port-control auto
authentication violation restrict
mab
dot1x pae authenticator
dot1x timeout quiet-period 15
dot1x timeout tx-period 3
storm-control broadcast level pps 100
storm-control multicast level pps 110
no vtp
lldp receive
lldp transmit
spanning-tree portfast
no shu
exitFacere potes ut computatrum tuum et telephonum prospere transeant authenticas cum mandato:
sh authentication sessions int Gi1/0/39 detNunc catervam faciamus (exempli gratia: sg-fgpp-mab ) in Active Directory per phones et unam fabricam ei addis experiendi (me in casu it's Grandis amnis GXP2160 cum mas oratio 000b.82ba.a7b1 et resp. propter domain 00b82baa7b1).
Circulus creatus, consilium exigentias tesserae inferiora dabimus (usura per Active Directory administrativus Centre -> domain -> System -> Password Occasus continens) cum sequentibus parametris Password-Optiones-pro-MAB:
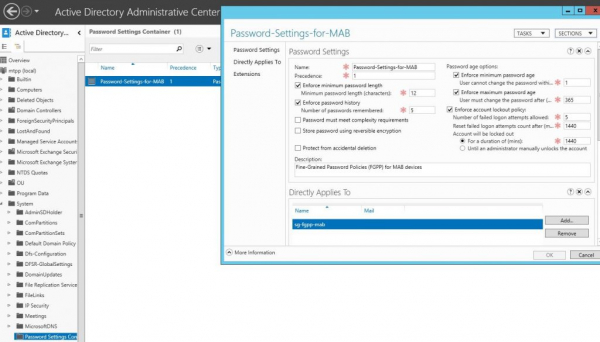
Ita dabimus usum inscriptionum machinarum sicut passwords. Post hoc consilium retis creare possumus pro methodo authenticas 802.1x mab, eam neag-machinis-8021x-voce vocemus. Parametri sunt:
- NAS Portus Type - Ethernet
- Windows Groups - sg-fgpp-mab
- EAP Genera: Unencrypted authenticas (PAP, SPAP)
- RADIUS attributa - Vendor Imprimis: Cisco - Cisco-AV-Pair - valorem attributum: fabrica-negotiationis genus = vox
Post felix authenticas (portum transitum configurare noli), inspiciamus ex portu:
sh authenticas se int Gi1/0/34
----------------------------------------
Interface: GigabitEthernet1/0/34
MAC Address: 000b.82ba.a7b1
IP Address: 172.29.31.89
User-Name: 000b82baa7b1
Status: Authz Success
Domain: VOICE
Oper host mode: multi-domain
Oper control dir: both
Authorized By: Authentication Server
Session timeout: N/A
Idle timeout: N/A
Common Session ID: 0000000000000EB2000B8C5E
Acct Session ID: 0x00000134
Handle: 0xCE000EB3
Runnable methods list:
Method State
dot1x Failed over
mab Authc SuccessNunc, ut pollicitus est, duos condiciones non omnino apertas inspiciamus. Exempli gratia, necesse est per insanabilem transitum (switch). Hic, portus uncinis prospicietur sic:
switch portum occasus in 802.1x exercitum modus multi auth modus
interface GigabitEthernet1/0/1
description *SW – 802.1x – 8 mac*
shu
switchport mode access
switchport nonegotiate
switchport voice vlan 55
switchport port-security maximum 8 ! увеличиваем кол-во допустимых мас-адресов
authentication event fail action authorize vlan 100
authentication event no-response action authorize vlan 100
authentication host-mode multi-auth ! – режим аутентификации
authentication port-control auto
authentication violation restrict
mab
dot1x pae authenticator
dot1x timeout quiet-period 15
dot1x timeout tx-period 3
storm-control broadcast level pps 100
storm-control multicast level pps 110
no vtp
spanning-tree portfast
no shuPS animadvertimus glitch valde mirabilem - si fabrica per talem transitum connexa erat, et tunc in transitum incisum ingestum erat, tunc non laborabit donec reboot transitum. Alias vias non inveni. hoc problema adhuc solvere.
Alterum punctum affinis ad DHCP (si IP dhcp adiicitur leo snooping) — sine optione tali;
ip dhcp snooping vlan 1-100
no ip dhcp snooping information optionAliquot de causa recte IP locum habere non possum... licet hoc sit proprium DHCP servientis nostri
Et Mac OS & Linux (quae patria 802.1x sustentationem habent) usorem authenticitatis dare conantur, etiamsi authenticas Mac inscriptionis configuratur.
In altera parte articuli, usum 802.1x pro Wireless videbimus (prout coetus ad quem ratio usoris pertinet, eam "iicere" in retis correspondentibus (vlan) mittemus, cum ipsi coniungemus. eodem SSID).
Source: www.habr.com


