Salvete omnes, nuper legit de quomodo accelerare possis OpenVPN In itinere, encryptionem ad separatam partem machinae intra ipsum itinerem conglutinatam transfero. Similem condicionem auctoris habeo—TP-Link WDR3500 cum 128 MB memoriae RAM et processore imbecilli qui encryptionem cuniculi omnino tractare non potest. Attamen, omnino nolebam in itinerem cum ferro ad conglutinandum ingredi. Mea experientia infra limitem est. OpenVPN ad separatam partem apparati cum subsidio in router in casu necessitatis.
negotium
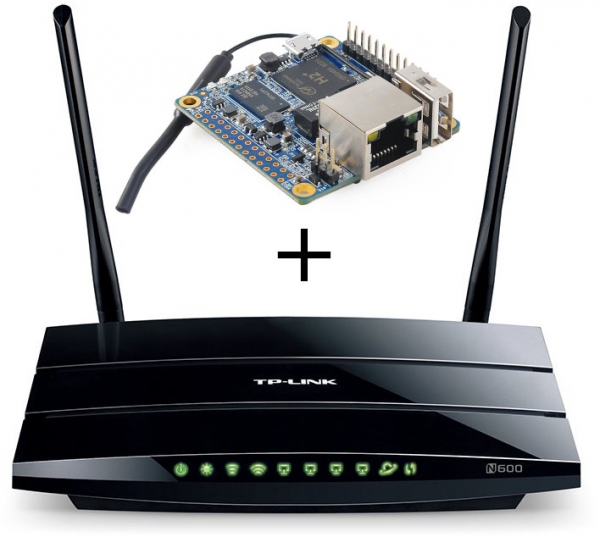
Habemus encaminatorem TP-Link WDR3500 et Orange Pi Zero H2. Volumus Orange Pi encryptionem cuniculi in modo normali tractare, sed si quid ei acciderit, processus a Pi curabitur. VPN Ad encaminatorem remittetur. Omnes configurationes muri ignis in encaminatore ut antea fungi debent. Et in universum, additio apparatuum additorum perspicua et omnibus imperceptibilis esse debet. OpenVPN Per TCP, adaptorem TAP in modo pontis (pons-servitoris) operatur.
arbitrium
Loco connectendi via USB, unum portum itineris uti constitui et omnia subnalia coniungere quae pontem VPN ad Orange Pi habent. Evenit ut ferramenta corporaliter in iisdem retiacula ac VPN server in iter pendeant. Post hoc, eosdem ministros in Auriaco Pi instituimus et in itinere aliquem procuratorem constituimus ut omnes hospites advenientes mittat ad servitorem externum, et si Orange Pi mortuus est vel perpendat, tunc ad internus fallback server. Cepi HAProxy.
Sic evenit;
- A clientis advenit
- Si server externus unavailable
- Si available, clientis accipitur ab Auriaco Pi
- VPN in Aureum Pi decryptis facis et exspuens eos in iter
- Iter itineris illis alicubi
Exemplum exsequendam
Dicamus igitur nos duas retia in itinere habere - principalem (1) et hospitem (2), pro utraque earum est... OpenVPN servitor ad connexionem ab externo.
Configuratione Network
Ambas retiacula per unum portum ad iter faciendum opus, sic 2 VLANs creamus.
Iter itineris, in sectione Network/Translate, VLANs crea (exempli gratia 1 et 2) easque in tagged modus in optatum portum, eth0.1 et eth0.2 ad retiacula correspondentia adde recentia creata (exempli gratia; eos brigde add).
In Orange Pi duos interfaces VLAN creamus (Habeo Archlinux ARM + netctl);
/etc/netctl/vlan-main
Description='Main VLAN on eth0'
Interface=vlan-main
Connection=vlan
BindsToInterfaces=eth0
VLANID=1
IP=no
/etc/netctl/vlan-guest
Description='Guest VLAN on eth0'
Interface=vlan-guest
Connection=vlan
BindsToInterfaces=eth0
VLANID=2
IP=no
Et statim duos pontes eis creamus;
/etc/netctl/br-main
Description="Main Bridge connection"
Interface=br-main
Connection=bridge
BindsToInterfaces=(vlan-main)
IP=dhcp
/etc/netctl/br-guest
Description="Guest Bridge connection"
Interface=br-guest
Connection=bridge
BindsToInterfaces=(vlan-guest)
IP=dhcp
Admitte autostart pro omnibus 4 profiles (netctl enable). Nunc post reboot, Aureum Pi pendet in duobus ligula eget. Inscriptiones interfacies in Pi Orange in Static Leases itineris itineris configuramus.
IP ostende addr
4: vlan-main@eth0: <BROADCAST,MULTICAST,PROMISC,UP,LOWER_UP> mtu 1500 qdisc noqueue master br-main state UP group default qlen 1000
link/ether 02:42:f0:f8:23:c8 brd ff:ff:ff:ff:ff:ff
inet6 fe80::42:f0ff:fef8:23c8/64 scope link
valid_lft forever preferred_lft forever
5: vlan-guest@eth0: <BROADCAST,MULTICAST,PROMISC,UP,LOWER_UP> mtu 1500 qdisc noqueue master br-guest state UP group default qlen 1000
link/ether 02:42:f0:f8:23:c8 brd ff:ff:ff:ff:ff:ff
inet6 fe80::42:f0ff:fef8:23c8/64 scope link
valid_lft forever preferred_lft forever
6: br-main: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default qlen 1000
link/ether 52:c7:0f:89:71:6e brd ff:ff:ff:ff:ff:ff
inet 192.168.1.3/24 brd 192.168.1.255 scope global dynamic noprefixroute br-main
valid_lft 29379sec preferred_lft 21439sec
inet6 fe80::50c7:fff:fe89:716e/64 scope link
valid_lft forever preferred_lft forever
7: br-guest: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default qlen 1000
link/ether ee:ea:19:31:34:32 brd ff:ff:ff:ff:ff:ff
inet 192.168.2.3/24 brd 192.168.2.255 scope global br-guest
valid_lft forever preferred_lft forever
inet6 fe80::ecea:19ff:fe31:3432/64 scope link
valid_lft forever preferred_lft forever
VPN erigas
Deinde, configurationes ex itinere (vel "router") exscribimus pro OpenVPN et claves. Optiones plerumque ex /tmp/etc/openvpn*.conf
Defalta, openvpn currens in TAP modum et pons server-continuum suum custodit iners. Omnia enim operantur, necesse est scripturam addere currentem cum reducitur nexus.
/etc/openvpn/main.conf
dev vpn-main
dev-type tap
client-to-client
persist-key
persist-tun
ca /etc/openvpn/main/ca.crt
cert /etc/openvpn/main/main.crt
cipher AES-256-CBC
comp-lzo yes
dh /etc/openvpn/main/dh2048.pem
ifconfig-pool-persist /etc/openvpn/ipp_main.txt
keepalive 10 60
key /etc/openvpn/main/main.key
port 443
proto tcp
push "redirect-gateway"
push "dhcp-option DNS 192.168.1.1"
server-bridge 192.168.1.3 255.255.255.0 192.168.1.200 192.168.1.229
status /tmp/openvpn.main.status
verb 3
setenv profile_name main
script-security 2
up /etc/openvpn/vpn-up.sh
/etc/openvpn/vpn-up.sh
#!/bin/sh
ifconfig vpn-${profile_name} up
brctl addif br-${profile_name} vpn-${profile_name}
Quo fit, ut primum nexus incidit, vpn-main interface addatur br-main. Requisitores hospites - similiter, usque ad nomen interface et inscriptio in server-ponte.
Petitiones externas et proxying profectus
Ad hunc gradum, Orange Pi, iam hospites accipere et clientes ad retiacula requisita coniungere potest. Reliquum est ut ineuntes nexus in itinere configurare procurationem.
Servientes iter itineris VPN ad alios portus transfermus, HAProxy instituimus in iter et configuramus:
/etc/haproxy.cfg
global
maxconn 256
uid 0
gid 0
daemon
defaults
retries 1
contimeout 1000
option splice-auto
listen guest_vpn
bind :444
mode tcp
server 0-orange 192.168.2.3:444 check
server 1-local 127.0.0.1:4444 check backup
listen main_vpn
bind :443
mode tcp
server 0-orange 192.168.1.3:443 check
server 1-local 127.0.0.1:4443 check backup
Fruere
Si omnia secundum consilium iverunt, clientes ad Orange Pi et processus iter itineris amplius non calefaciet, et celeritas VPN signanter augebit. Eodem tempore omnes regulae retis quae in itinere commemorantur pertinentes manebunt. In casu accidentis in Orange Pi, defluet et HAProxy clientes ad loci servitores transferet.
Gratias tibi agimus propter diligentiam tuam, suggestiones et correctiones gratae sunt.
Source: www.habr.com


