He maha nga ahuatanga o te mahi DNS kua pa ki te kaituhi i roto i te maha o i whakaputaina hei wahanga o te rangitaki. I te wa ano, ko te mea nui ko te whakapai ake i te haumarutanga o tenei ratonga Ipurangi matua.

Tae noa ki te tata nei, ahakoa te whakaraeraetanga o te hokohoko DNS, kei te noho tonu, mo te nuinga o te waa, ka tukuna i roto i te marama, ki nga mahi kino a nga kaiwhakarato e whai ana ki te whakanui ake i o raatau moni ma te whakauru i nga panui ki roto i nga korero, nga tari haumaru a te kawanatanga me te aukati, me te hunga hara noa, te tukanga , ahakoa te ahua o nga momo hangarau penei i te DNSSEC/DANE, DNScrypt, DNS-over-TLS me DNS-over-HTTPS, kua mutu. A, ki te mea kei te mohiotia nuitia, kei te waatea hoki etahi o nga otinga tūmau, me etahi o era kua roa, ko ta raatau tautoko mai i nga rorohiko a te kiritaki he nui te hiahia.
Waimarie, kei te huri haere te ahuatanga. Ina koa, ko nga kaihanga o te kaitirotiro Firefox rongonui mo nga mahere kia taea te aratau tautoko ma te taunoa (DoH) tata. Ka awhina tenei ki te tiaki i nga hokohoko DNS a te kaiwhakamahi WWW mai i nga whakatumatuma o runga ake nei, engari ka taea pea te whakauru i nga mea hou.
1. Nga raruraru DNS-over-HTTPS
I te titiro tuatahi, ko te timatanga o te whakaurunga papatipu o DNS-over-HTTPS ki roto i te rorohiko Ipurangi ka puta he tauhohenga pai. Heoi, ko te rewera, e ai ki ta ratou, kei roto i nga korero.
Ko te raru tuatahi e whakatiki ana i te whanuitanga o te whakamahi whanui a DoH ko tana aro anake ki te hokohoko tukutuku. Inaa, ko te kawa HTTP me tana putanga o naianei HTTP/2, kei runga nei a DoH te turanga o te WWW. Engari ko te Ipurangi ehara i te paetukutuku anake. He maha nga ratonga rongonui, penei i te imeera, nga momo karere inamata, nga punaha whakawhiti konae, rerenga rongorau, aha atu, kaore e whakamahi HTTP. No reira, ahakoa te whakaaro o te nuinga o te DoH he rongoa, karekau e tika ki te kore he mahi taapiri (me te kore e tika) mo tetahi mea ke atu i nga hangarau tirotiro. Ma te ara, ko te DNS-over-TLS te ahua he kaitono pai ake mo tenei mahi, e whakatinana ana i te whakaurunga o nga waka DNS paerewa i roto i te kawa TLS paerewa haumaru.
Ko te raru tuarua, he mea tino nui ake i te tuatahi, ko te whakarerenga o te whakawhanaungatanga o DNS na roto i te hoahoa ki te whakamahi i tetahi tūmau DoH kua tohua i roto i nga tautuhinga tirotiro. Ina koa, e kii ana a Mozilla ki te whakamahi i tetahi ratonga mai i Cloudflare. He ratonga pera ano i whakarewahia e etahi atu tangata rongonui o te Ipurangi, ina koa a Google. Ka puta ko te whakatinanatanga o DNS-over-HTTPS i roto i te ahua e whakaarohia ana i tenei wa ka piki ake te whakawhirinaki o nga kaiwhakamahi mutunga ki nga ratonga nui rawa atu. Ehara i te mea ngaro ko nga korero ka taea e te wetewete o nga patai DNS te kohi i nga korero mo taua mea, me te whakanui ake i te tika me te whai take.
I runga i tenei whakaaro, ko te kaituhi i tautoko tonu i te whakatinanatanga papatipu ehara i te DNS-over-HTTPS, engari ko te DNS-over-TLS me te DNSSEC/DANE hei kaupapa mo te ao katoa, he haumaru me te kore e pai ki te whakauru i nga tikanga Ipurangi. mo te whakarite i te haumarutanga o te hokohoko DNS. Heoi ano, mo nga take e kitea ana, kaore e taea e tetahi te tumanako kia tere te whakauru mai o te tautoko papatipu mo nga momo rereke a DoH ki roto i nga rorohiko a te kiritaki, a ko te rohe tonu o te hunga kaingākau ki te hangarau haumaru.
Engari i te mea kei a tatou inaianei a DoH, he aha e kore ai e whakamahi i muri i te mawhiti atu i te tirotiro a nga kaporeihana na roto i o raatau kaitoro ki a maatau ake DNS-over-HTTPS server?
2. Kawa DNS-over-HTTPS
Mena ka titiro koe ki te paerewa e whakaahua ana i te kawa DNS-over-HTTPS, ka kite koe he pono, he API tukutuku ka taea e koe te whakauru i tetahi putea DNS paerewa i roto i te kawa HTTP/2. Ka whakatinanahia tenei ma nga pane HTTP motuhake, me te whakarereketanga o te whakatakotoranga rua o nga raraunga DNS kua tukuna (tirohia. me nga tuhinga o muri mai) ki tetahi puka ka taea e koe te tuku me te tango i a raatau, me te mahi me nga metadata e tika ana.
E ai ki te paerewa, ko te HTTP/2 anake me te hononga TLS haumaru e tautokohia ana.
Ka taea te tuku tono DNS ma te whakamahi i nga tikanga GET me te POST paerewa. I roto i te take tuatahi, ka hurihia te tono ki te aho-whakawaehere base64URL, me te tuarua, na roto i te tinana o te tono POST i roto i te ahua rua. I tenei keehi, ka whakamahia he momo raraunga MIME motuhake i te wa e tono ana me te whakautu DNS tono/dns-karere.
root@eprove:~ # curl -H 'accept: application/dns-message' 'https://my.domaint/dns-query?dns=q80BAAABAAAAAAAAB2V4YW1wbGUDY29tAAABAAE' -v
* Trying 2001:100:200:300::400:443...
* TCP_NODELAY set
* Connected to eprove.net (2001:100:200:300::400) port 443 (#0)
* ALPN, offering h2
* ALPN, offering http/1.1
* successfully set certificate verify locations:
* CAfile: /usr/local/share/certs/ca-root-nss.crt
CApath: none
* TLSv1.3 (OUT), TLS handshake, Client hello (1):
* TLSv1.3 (IN), TLS handshake, Server hello (2):
* TLSv1.3 (IN), TLS handshake, Encrypted Extensions (8):
* TLSv1.3 (IN), TLS handshake, Certificate (11):
* TLSv1.3 (IN), TLS handshake, CERT verify (15):
* TLSv1.3 (IN), TLS handshake, Finished (20):
* TLSv1.3 (OUT), TLS change cipher, Change cipher spec (1):
* TLSv1.3 (OUT), TLS handshake, Finished (20):
* SSL connection using TLSv1.3 / TLS_AES_256_GCM_SHA384
* ALPN, server accepted to use h2
* Server certificate:
* subject: CN=my.domain
* start date: Jul 22 00:07:13 2019 GMT
* expire date: Oct 20 00:07:13 2019 GMT
* subjectAltName: host "my.domain" matched cert's "my.domain"
* issuer: C=US; O=Let's Encrypt; CN=Let's Encrypt Authority X3
* SSL certificate verify ok.
* Using HTTP2, server supports multi-use
* Connection state changed (HTTP/2 confirmed)
* Copying HTTP/2 data in stream buffer to connection buffer after upgrade: len=0
* Using Stream ID: 1 (easy handle 0x801441000)
> GET /dns-query?dns=q80BAAABAAAAAAAAB2V4YW1wbGUDY29tAAABAAE HTTP/2
> Host: eprove.net
> User-Agent: curl/7.65.3
> accept: application/dns-message
>
* TLSv1.3 (IN), TLS handshake, Newsession Ticket (4):
* Connection state changed (MAX_CONCURRENT_STREAMS == 100)!
< HTTP/2 200
< server: h2o/2.3.0-beta2
< content-type: application/dns-message
< cache-control: max-age=86274
< date: Thu, 12 Sep 2019 13:07:25 GMT
< strict-transport-security: max-age=15768000; includeSubDomains; preload
< content-length: 45
<
Warning: Binary output can mess up your terminal. Use "--output -" to tell
Warning: curl to output it to your terminal anyway, or consider "--output
Warning: <FILE>" to save to a file.
* Failed writing body (0 != 45)
* stopped the pause stream!
* Connection #0 to host eprove.net left intactKia tupato ano ki te taitara mana keteroki: i te whakautu mai i te tūmau tukutuku. I roto i te tawhā max-tau kei roto te uara TTL mo te rekoata DNS e whakahokia ana (te uara iti rawa ranei mena ka whakahokia mai he huinga).
I runga i nga korero o runga ake nei, he maha nga waahanga o te mahi a te tūmau DoH.
- Whiwhi tono HTTP. Mena he GET tenei ka wetewetehia te paatete mai i te whakawaehere base64URL.
- Tukuna tenei kete ki te tūmau DNS.
- Tikina he whakautu mai i te tūmau DNS
- Kimihia te uara TTL iti i roto i nga rekoata kua riro.
- Whakahokia he whakautu ki te kiritaki ma te HTTP.
3. Tou ake tūmau DNS-over-HTTPS
Ko te huarahi ngawari, tere me te tino whai hua ki te whakahaere i to ake tūmau DNS-over-HTTPS ko te whakamahi i te tūmau tukutuku HTTP/2 , he mea poto kua tuhia e te kaituhi (tirohia "").
Ka tautokohia tenei kowhiri e te meka ka taea te whakatinana katoa nga waehere katoa o to ake tūmau DoH ma te whakamahi i te kaiwhakamaori kua whakauruhia ki roto i a H2O ano. . I tua atu i nga whare pukapuka paerewa, hei whakawhiti raraunga me te tūmau DNS, me hiahia koe ki te whare pukapuka (mrbgem) Socket, he waimarie, kua whakauruhia ki roto i te putanga whanaketanga o naianei o H2O 2.3.0-beta2 i roto i nga tauranga FreeBSD. Heoi, ehara i te mea uaua ki te taapiri atu ki tetahi putanga o mua ma te kati i te putunga ki te pukapuka /deps i mua i te whakahiato.
root@beta:~ # uname -v
FreeBSD 12.0-RELEASE-p10 GENERIC
root@beta:~ # cd /usr/ports/www/h2o
root@beta:/usr/ports/www/h2o # make extract
===> License MIT BSD2CLAUSE accepted by the user
===> h2o-2.2.6 depends on file: /usr/local/sbin/pkg - found
===> Fetching all distfiles required by h2o-2.2.6 for building
===> Extracting for h2o-2.2.6.
=> SHA256 Checksum OK for h2o-h2o-v2.2.6_GH0.tar.gz.
===> h2o-2.2.6 depends on file: /usr/local/bin/ruby26 - found
root@beta:/usr/ports/www/h2o # cd work/h2o-2.2.6/deps/
root@beta:/usr/ports/www/h2o/work/h2o-2.2.6/deps # git clone https://github.com/iij/mruby-socket.git
Клонирование в «mruby-socket»…
remote: Enumerating objects: 385, done.
remote: Total 385 (delta 0), reused 0 (delta 0), pack-reused 385
Получение объектов: 100% (385/385), 98.02 KiB | 647.00 KiB/s, готово.
Определение изменений: 100% (208/208), готово.
root@beta:/usr/ports/www/h2o/work/h2o-2.2.6/deps # ll
total 181
drwxr-xr-x 9 root wheel 18 12 авг. 16:09 brotli/
drwxr-xr-x 2 root wheel 4 12 авг. 16:09 cloexec/
drwxr-xr-x 2 root wheel 5 12 авг. 16:09 golombset/
drwxr-xr-x 4 root wheel 35 12 авг. 16:09 klib/
drwxr-xr-x 2 root wheel 5 12 авг. 16:09 libgkc/
drwxr-xr-x 4 root wheel 26 12 авг. 16:09 libyrmcds/
drwxr-xr-x 13 root wheel 32 12 авг. 16:09 mruby/
drwxr-xr-x 5 root wheel 11 12 авг. 16:09 mruby-digest/
drwxr-xr-x 5 root wheel 10 12 авг. 16:09 mruby-dir/
drwxr-xr-x 5 root wheel 10 12 авг. 16:09 mruby-env/
drwxr-xr-x 4 root wheel 9 12 авг. 16:09 mruby-errno/
drwxr-xr-x 5 root wheel 14 12 авг. 16:09 mruby-file-stat/
drwxr-xr-x 5 root wheel 10 12 авг. 16:09 mruby-iijson/
drwxr-xr-x 5 root wheel 11 12 авг. 16:09 mruby-input-stream/
drwxr-xr-x 6 root wheel 11 12 авг. 16:09 mruby-io/
drwxr-xr-x 5 root wheel 10 12 авг. 16:09 mruby-onig-regexp/
drwxr-xr-x 4 root wheel 10 12 авг. 16:09 mruby-pack/
drwxr-xr-x 5 root wheel 10 12 авг. 16:09 mruby-require/
drwxr-xr-x 6 root wheel 10 12 сент. 16:10 mruby-socket/
drwxr-xr-x 2 root wheel 9 12 авг. 16:09 neverbleed/
drwxr-xr-x 2 root wheel 13 12 авг. 16:09 picohttpparser/
drwxr-xr-x 2 root wheel 4 12 авг. 16:09 picotest/
drwxr-xr-x 9 root wheel 16 12 авг. 16:09 picotls/
drwxr-xr-x 4 root wheel 8 12 авг. 16:09 ssl-conservatory/
drwxr-xr-x 8 root wheel 18 12 авг. 16:09 yaml/
drwxr-xr-x 2 root wheel 8 12 авг. 16:09 yoml/
root@beta:/usr/ports/www/h2o/work/h2o-2.2.6/deps # cd ../../..
root@beta:/usr/ports/www/h2o # make install clean
...He paerewa noa te whirihoranga tūmau tukutuku.
root@beta:/usr/ports/www/h2o # cd /usr/local/etc/h2o/
root@beta:/usr/local/etc/h2o # cat h2o.conf
# this sample config gives you a feel for how h2o can be used
# and a high-security configuration for TLS and HTTP headers
# see https://h2o.examp1e.net/ for detailed documentation
# and h2o --help for command-line options and settings
# v.20180207 (c)2018 by Max Kostikov http://kostikov.co e-mail: max@kostikov.co
user: www
pid-file: /var/run/h2o.pid
access-log:
path: /var/log/h2o/h2o-access.log
format: "%h %v %l %u %t "%r" %s %b "%{Referer}i" "%{User-agent}i""
error-log: /var/log/h2o/h2o-error.log
expires: off
compress: on
file.dirlisting: off
file.send-compressed: on
file.index: [ 'index.html', 'index.php' ]
listen:
port: 80
listen:
port: 443
ssl:
cipher-suite: ECDHE-ECDSA-CHACHA20-POLY1305:ECDHE-RSA-CHACHA20-POLY1305:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:DHE-RSA-AES128-GCM-SHA256:DHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-AES128-SHA256:ECDHE-RSA-AES128-SHA256:ECDHE-ECDSA-AES128-SHA:ECDHE-RSA-AES256-SHA384:ECDHE-RSA-AES128-SHA:ECDHE-ECDSA-AES256-SHA384:ECDHE-ECDSA-AES256-SHA:ECDHE-RSA-AES256-SHA:DHE-RSA-AES128-SHA256:DHE-RSA-AES128-SHA:DHE-RSA-AES256-SHA256:DHE-RSA-AES256-SHA:ECDHE-ECDSA-DES-CBC3-SHA:ECDHE-RSA-DES-CBC3-SHA:EDH-RSA-DES-CBC3-SHA:AES128-GCM-SHA256:AES256-GCM-SHA384:AES128-SHA256:AES256-SHA256:AES128-SHA:AES256-SHA:DES-CBC3-SHA:!DSS
cipher-preference: server
dh-file: /etc/ssl/dhparams.pem
certificate-file: /usr/local/etc/letsencrypt/live/eprove.net/fullchain.pem
key-file: /usr/local/etc/letsencrypt/live/my.domain/privkey.pem
hosts:
"*.my.domain":
paths: &go_tls
"/":
redirect:
status: 301
url: https://my.domain/
"my.domain:80":
paths: *go_tls
"my.domain:443":
header.add: "Strict-Transport-Security: max-age=15768000; includeSubDomains; preload"
paths:
"/dns-query":
mruby.handler-file: /usr/local/etc/h2o/h2odoh.rbKo te mea anake ko te kaiwhakahaere URL /dns-uiui ko ta matou tūmau DNS-over-HTTPS, i tuhia ki te mruby ka karangahia ma te whiringa kaihautu, te kawenga mruby.handler-file.
root@beta:/usr/local/etc/h2o # cat h2odoh.rb
# H2O HTTP/2 web server as DNS-over-HTTP service
# v.20190908 (c)2018-2019 Max Kostikov https://kostikov.co e-mail: max@kostikov.co
proc {|env|
if env['HTTP_ACCEPT'] == "application/dns-message"
case env['REQUEST_METHOD']
when "GET"
req = env['QUERY_STRING'].gsub(/^dns=/,'')
# base64URL decode
req = req.tr("-_", "+/")
if !req.end_with?("=") && req.length % 4 != 0
req = req.ljust((req.length + 3) & ~3, "=")
end
req = req.unpack1("m")
when "POST"
req = env['rack.input'].read
else
req = ""
end
if req.empty?
[400, { 'content-type' => 'text/plain' }, [ "Bad Request" ]]
else
# --- ask DNS server
sock = UDPSocket.new
sock.connect("localhost", 53)
sock.send(req, 0)
str = sock.recv(4096)
sock.close
# --- find lowest TTL in response
nans = str[6, 2].unpack1('n') # number of answers
if nans > 0 # no DNS failure
shift = 12
ttl = 0
while nans > 0
# process domain name compression
if str[shift].unpack1("C") < 192
shift = str.index("x00", shift) + 5
if ttl == 0 # skip question section
next
end
end
shift += 6
curttl = str[shift, 4].unpack1('N')
shift += str[shift + 4, 2].unpack1('n') + 6 # responce data size
if ttl == 0 or ttl > curttl
ttl = curttl
end
nans -= 1
end
cc = 'max-age=' + ttl.to_s
else
cc = 'no-cache'
end
[200, { 'content-type' => 'application/dns-message', 'content-length' => str.size, 'cache-control' => cc }, [ str ] ]
end
else
[415, { 'content-type' => 'text/plain' }, [ "Unsupported Media Type" ]]
end
}Kia mahara ko te tūmau keteroki a rohe te kawenga mo te tukatuka i nga putea DNS, i tenei keehi mai i te tohatoha FreeBSD paerewa. Mai i te tirohanga haumarutanga, koinei te otinga tino pai. Heoi, kaore he mea e aukati i a koe ki te whakakapi localhost ki tetahi wahitau DNS rereke e hiahia ana koe ki te whakamahi.
root@beta:/usr/local/etc/h2o # local-unbound verison
usage: local-unbound [options]
start unbound daemon DNS resolver.
-h this help
-c file config file to read instead of /var/unbound/unbound.conf
file format is described in unbound.conf(5).
-d do not fork into the background.
-p do not create a pidfile.
-v verbose (more times to increase verbosity)
Version 1.8.1
linked libs: mini-event internal (it uses select), OpenSSL 1.1.1a-freebsd 20 Nov 2018
linked modules: dns64 respip validator iterator
BSD licensed, see LICENSE in source package for details.
Report bugs to unbound-bugs@nlnetlabs.nl
root@eprove:/usr/local/etc/h2o # sockstat -46 | grep unbound
unbound local-unbo 69749 3 udp6 ::1:53 *:*
unbound local-unbo 69749 4 tcp6 ::1:53 *:*
unbound local-unbo 69749 5 udp4 127.0.0.1:53 *:*
unbound local-unbo 69749 6 tcp4 127.0.0.1:53 *:*Ko nga mea e toe ana ko te whakaara ano i te H2O me te kite he aha nga hua.
root@beta:/usr/local/etc/h2o # service h2o restart
Stopping h2o.
Waiting for PIDS: 69871.
Starting h2o.
start_server (pid:70532) starting now...4. Whakamatau
Na, tirohia nga hua ma te tuku ano i te tono whakamatautau me te titiro ki te hokohoko whatunga ma te whakamahi i te taputapu tcpdump.
root@beta/usr/local/etc/h2o # curl -H 'accept: application/dns-message' 'https://my.domain/dns-query?dns=q80BAAABAAAAAAAAB2V4YW1wbGUDY29tAAABAAE'
Warning: Binary output can mess up your terminal. Use "--output -" to tell
Warning: curl to output it to your terminal anyway, or consider "--output
Warning: <FILE>" to save to a file.
...
root@beta:~ # tcpdump -n -i lo0 udp port 53 -xx -XX -vv
tcpdump: listening on lo0, link-type NULL (BSD loopback), capture size 262144 bytes
16:32:40.420831 IP (tos 0x0, ttl 64, id 37575, offset 0, flags [none], proto UDP (17), length 57, bad cksum 0 (->e9ea)!)
127.0.0.1.21070 > 127.0.0.1.53: [bad udp cksum 0xfe38 -> 0x33e3!] 43981+ A? example.com. (29)
0x0000: 0200 0000 4500 0039 92c7 0000 4011 0000 ....E..9....@...
0x0010: 7f00 0001 7f00 0001 524e 0035 0025 fe38 ........RN.5.%.8
0x0020: abcd 0100 0001 0000 0000 0000 0765 7861 .............exa
0x0030: 6d70 6c65 0363 6f6d 0000 0100 01 mple.com.....
16:32:40.796507 IP (tos 0x0, ttl 64, id 37590, offset 0, flags [none], proto UDP (17), length 73, bad cksum 0 (->e9cb)!)
127.0.0.1.53 > 127.0.0.1.21070: [bad udp cksum 0xfe48 -> 0x43fa!] 43981 q: A? example.com. 1/0/0 example.com. A 93.184.216.34 (45)
0x0000: 0200 0000 4500 0049 92d6 0000 4011 0000 ....E..I....@...
0x0010: 7f00 0001 7f00 0001 0035 524e 0035 fe48 .........5RN.5.H
0x0020: abcd 8180 0001 0001 0000 0000 0765 7861 .............exa
0x0030: 6d70 6c65 0363 6f6d 0000 0100 01c0 0c00 mple.com........
0x0040: 0100 0100 0151 8000 045d b8d8 22 .....Q...].."
^C
2 packets captured
23 packets received by filter
0 packets dropped by kernelKo te putanga e whakaatu ana me pehea te tono ki te whakatau i te wahitau example.com i riro mai, i tutuki pai e te tūmau DNS.
Inaianei ko nga mea katoa e toe ana ko te whakahohe i ta maatau tūmau i te pūtirotiro Firefox. Ki te mahi i tenei, me whakarereke e koe etahi tautuhinga i runga i nga wharangi whirihoranga e pā ana ki: whirihora.
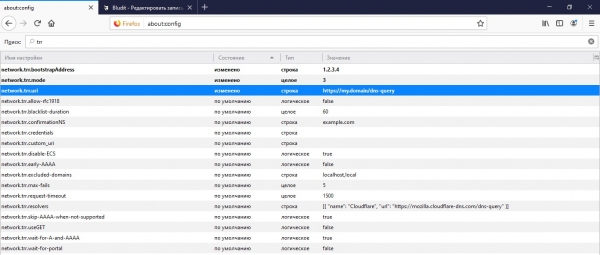
Tuatahi, koinei te wahitau o to tatou API ka tono te kaitirotiro korero DNS ki roto whatunga.trr.uri. E taunaki ana hoki kia tohua te IP rohe mai i tenei URL mo te taumira IP haumaru ma te whakamahi i te kaitirotiro ake me te kore e uru ki te DNS network.trr.bootstrapAddress. Na te mutunga, te tawhā ake whatunga.trr.mode tae atu ki te whakamahi i te DoH. Ma te whakatau i te uara ki te "3" ka kaha te kaitirotiro ki te whakamahi anake i te DNS-over-HTTPS mo te whakatau ingoa, engari ko te "2" tino pono me te haumaru ka whai mana ki te DoH, ka waiho ko te rapunga DNS paerewa hei whiringa whakamuri.
5. PAPUA!
I awhina te tuhinga? Tena koa kaua koe e whakama me te tautoko i te moni ma te puka koha (i raro).
Source: will.com


