Nkhaniyi ikumaliza zofalitsa zathu zowunika za pulogalamu yaumbanda. Tidasanthula mwatsatanetsatane fayilo yomwe ili ndi kachilombo yomwe kampani yaku Europe idalandira ndi imelo ndikupeza pulogalamu yaukazitape ya AgentTesla mmenemo. adalongosola zotsatira za kusanthula kwapang'onopang'ono kwa gawo lalikulu la AgentTesla.
Lero, Ilya Pomerantsev, katswiri wofufuza za pulogalamu yaumbanda ku CERT Gulu-IB, akambirana gawo loyamba la kusanthula kwa pulogalamu yaumbanda-kutsegula kokhazikika kwa zitsanzo za AgentTesla-pogwiritsa ntchito maphunziro atatu a mini-case kuchokera kwa akatswiri a CERT Gulu-IB.
Nthawi zambiri, gawo loyamba pakuwunika kwa pulogalamu yaumbanda ndikuchotsa chitetezo monga chopakira, cryptor, protector, kapena loader. Nthawi zambiri, vutoli limathetsedwa poyambitsa pulogalamu yaumbanda ndikutaya, koma nthawi zina njira iyi ndi yosayenera. Mwachitsanzo, ngati pulogalamu yaumbanda ndi encryptor, ngati imateteza madera ake okumbukira kuti asatayike, ngati nambalayo ili ndi njira zodziwira makina, kapena pulogalamu yaumbandayo ikangoyambiranso. Zikatero, kutulutsa kotchedwa "semi-automated" kumagwiritsidwa ntchito, kutanthauza kuti wofufuzayo ali ndi mphamvu zonse pa ndondomekoyi ndipo akhoza kulowererapo nthawi iliyonse. Tiyeni tiwone njirayi pogwiritsa ntchito zitsanzo zitatu za banja la AgentTesla monga chitsanzo. Pulogalamu yaumbandayi ilibe vuto lililonse ngati netiweki yake yazimitsidwa.
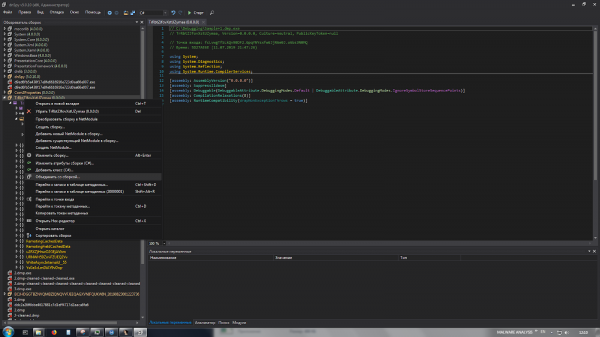
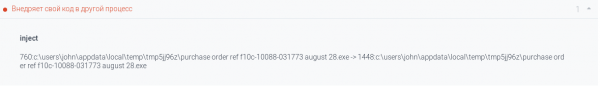
Chitsanzo #1
Fayilo yochokera ndi chikalata cha MS Word chomwe chimagwiritsa ntchito chiwopsezo cha CVE-2017-11882.
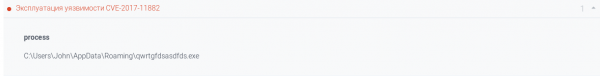
Zotsatira zake, zolipira zimatsitsidwa ndikuyambitsidwa.
Kuwunika kwa mtengo wa ndondomeko ndi zizindikiro zamakhalidwe zimawulula jekeseni mu ndondomekoyi RegAsm.exe.


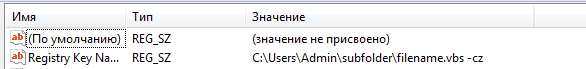
Pali zolembera zamakhalidwe a AgentTesla.

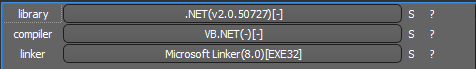
Chitsanzo chotsitsidwa chikhoza kuchitika .NET- fayilo yotetezedwa ndi chitetezo NET Reactor.
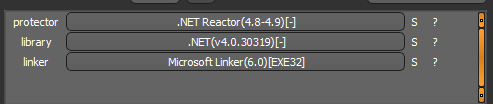
Tiyeni titsegule muzothandizira dnSpy x86 ndipo tiyeni tipite kumalo olowera.
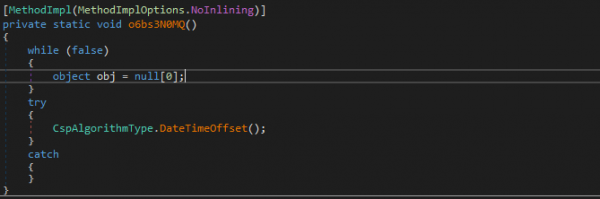
Kupita ku ntchito DateTimeOffset, tipeza nambala yoyambira yatsopano .NET- module. Tiyeni tiyike kuswa pamzere womwe timakonda ndikuyendetsa fayilo.
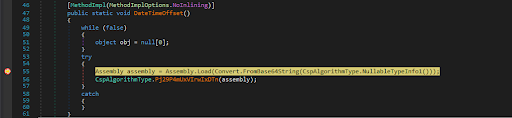
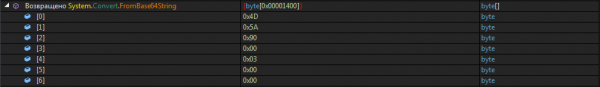
Mu imodzi mwazosungira zomwe zabwezedwa mutha kuwona siginecha ya MZ (0x4D 0x5A). Tiyeni tisunge.
Fayilo yomwe yatayidwa ndi laibulale yamphamvu yomwe imagwira ntchito ngati chotsitsa, mwachitsanzo, imatulutsa zolipira kuchokera pagawo lazinthu ndikuziyambitsa.
Komabe, zinthu zofunika nazonso zikusoweka pamalo otayapo. Iwo ali mu chitsanzo makolo.
Zothandiza dnSpy ili ndi zinthu ziwiri zothandiza kwambiri zomwe zingatithandize kupanga "Frankenstein" kuchokera pamafayilo awiri ogwirizana mwachangu.
- Yoyamba imakulolani "kuyika" laibulale yosinthika mu chitsanzo cha makolo.

- Chachiwiri ndikulembanso kachidindo kantchito pamalo olowera kuti muyitane njira yofunikira yalaibulale yamphamvu yoyikidwa.

Timasunga "Frankenstein" yathu ndikuyiyika kuswa pamzere womwe umabweza buffer ndi zida zotsitsidwa, ndipo timapanga kutaya kofanana ndi sitepe yapitayi.
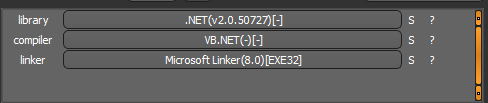
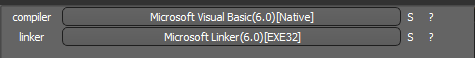
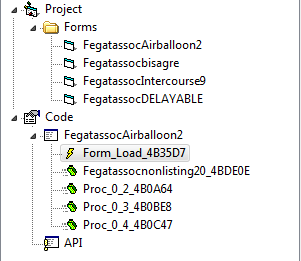
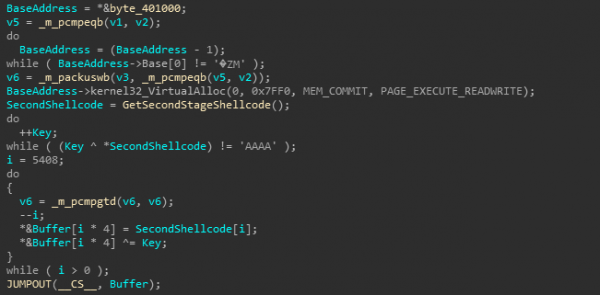
Kutaya kwachiwiri kumalembedwamo VB.NET fayilo yotheka kutetezedwa ndi chitetezo chomwe timachidziwa bwino Zithunzi za ConfuserEx.
Pambuyo pochotsa woteteza, timagwiritsa ntchito malamulo a YARA omwe adalembedwa kale ndikutsimikizira kuti pulogalamu yaumbanda yosatulutsidwa ndi AgentTesla.
![]()
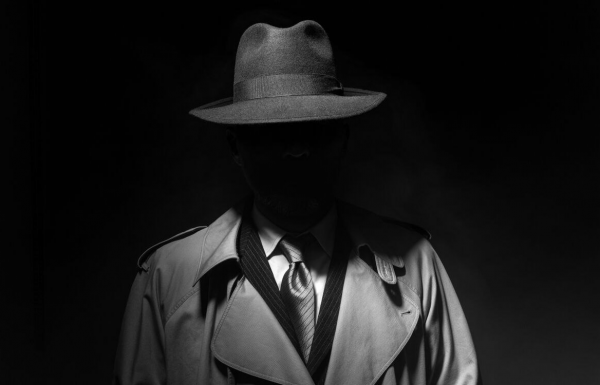
Chitsanzo #2
Fayilo yoyambira ndi chikalata cha MS Excel. Ma macro ophatikizidwa amachititsa kuti code yoyipa iwonongeke.
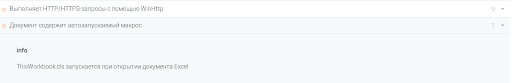
Izi zimapangitsa kuti script ya PowerShell ikhazikitsidwe.
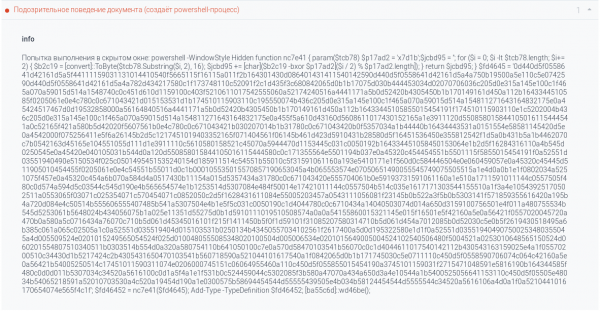
Cholembacho chimachotsa kachidindo ya C # ndikusamutsira kuwongolera. Khodiyo yokha ndi yonyamula katundu, monga zikuwonekera kuchokera ku lipoti la sandbox.
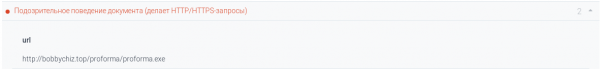
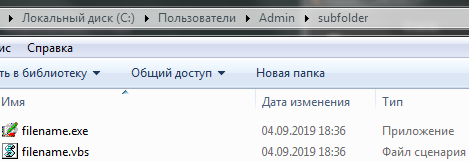
Malipiro amatha kuchitidwa .NET-fayilo.
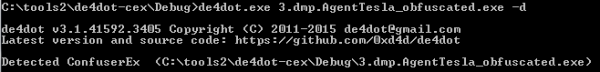
Kutsegula fayilo mu dnSpy x86, mukuwona kuti ndizosamveka. Timachotsa obfuscation pogwiritsa ntchito zofunikira de4dot ndipo tikubwerera ku kusanthula.
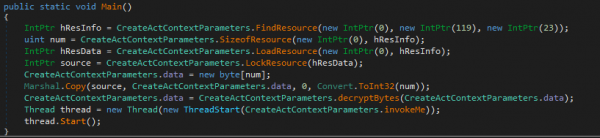
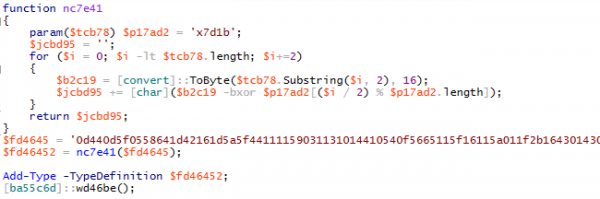
Mukuyang'ana code, mutha kupeza zotsatirazi:
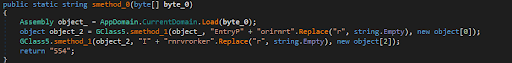
Mizere yama code ndi yodabwitsa EntryPoint и Ikani. Timayika kuswa pamzere woyamba, thamangani ndikusunga mtengo wa buffer bati_0.
Kutaya ndi ntchito kachiwiri .NET ndi kutetezedwa Zithunzi za ConfuserEx.
![]()
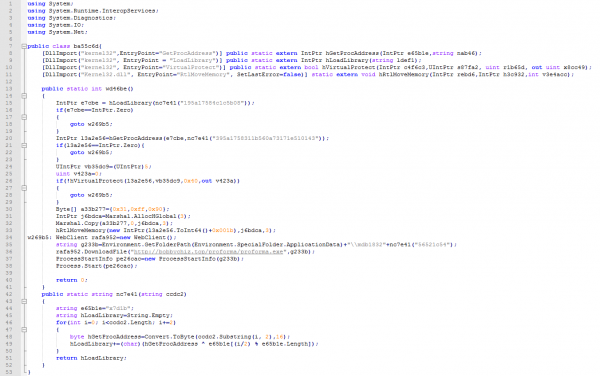
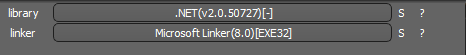
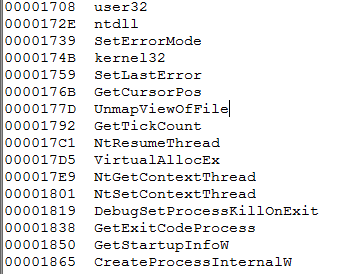
Kuchotsa obfuscation pogwiritsa ntchito de4dot ndikulowetsamo dnSpyKuchokera pamafotokozedwe a fayilo timamvetsetsa kuti tikukumana nawo CyaX-Sharp loader.
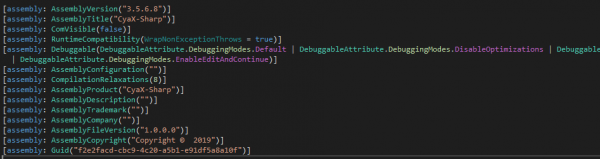
Izi downloader ali kwambiri odana kusanthula magwiridwe antchito.
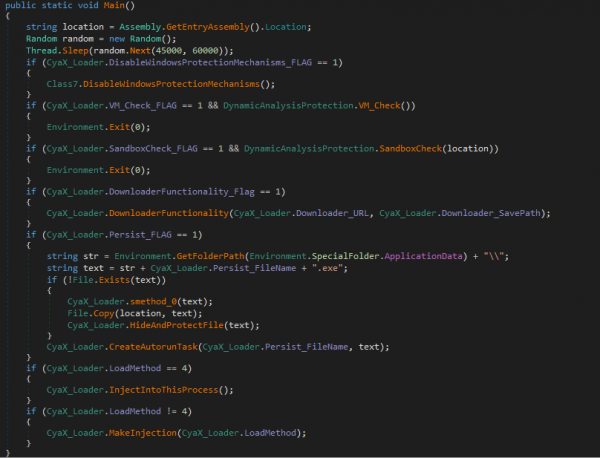
Kugwira ntchito kumeneku kumaphatikizapo kudutsa machitidwe otetezedwa a Windows, kuletsa Windows Defender, ndikuwona mabokosi a mchenga ndi makina enieni. Ikhoza kukopera malipiro kuchokera pa intaneti kapena kusunga mu gawo lazinthu. Kukhazikitsa kumachitika kudzera munjira yakeyake, kubwereza kwa njira yakeyake, kapena njira zake. MSBuild.exe, vbc.exe и RegSvcs.exe kutengera parameter yosankhidwa ndi wowukirayo.
Komabe, kwa ife iwo ndi ocheperapo AntiDump-ntchito yomwe imawonjezera Zithunzi za ConfuserExMagwero ake angapezeke pa .
Kuti tiletse chitetezo, tidzagwiritsa ntchito mwayiwu dnSpy, zomwe zimakulolani kuti musinthe IL- kodi.
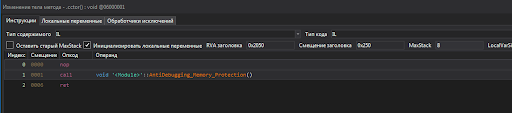
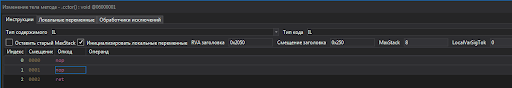
Timasunga ndikuyika kuswa ku chingwe choyimba foni ya payload decryption. Ili mu omanga kalasi yayikulu.
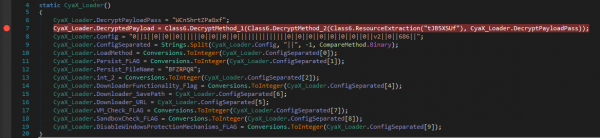
Timayamba ndi kutaya malipiro. Pogwiritsa ntchito malamulo olembedwa kale a YARA, timatsimikizira kuti uyu ndi AgentTesla.
![]()
Chitsanzo #3
Fayilo yoyambira ndiyotheka VB Native PE32-fayilo.
Kusanthula kwa Entropy kumawonetsa kupezeka kwa kagawo kakang'ono ka deta yobisika.

Mukasanthula fomu yofunsira mu VB Decompiler Mutha kuwona mbiri yachilendo ya pixelated.
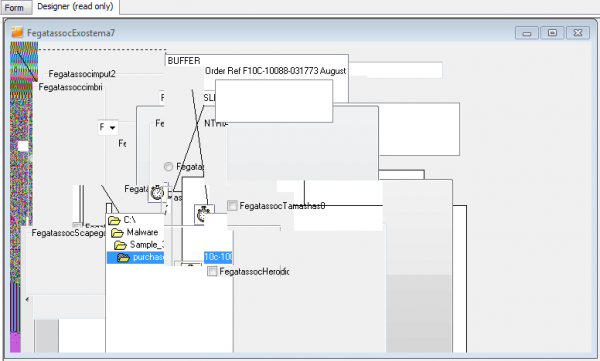
Chithunzi cha Entropy bmp- chithunzicho ndi chofanana ndi chithunzi cha entropy cha fayilo yoyambirira, ndipo kukula kwake ndi 85% ya kukula kwa fayilo.
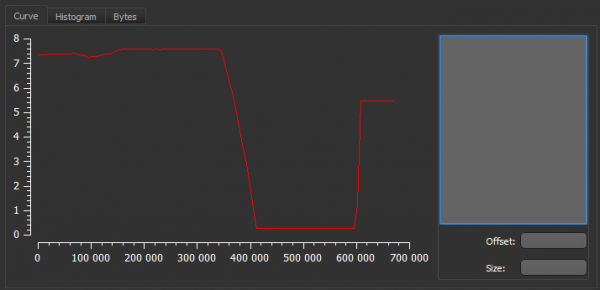
Maonekedwe onse a chithunzicho akuwonetsa kugwiritsa ntchito steganography.
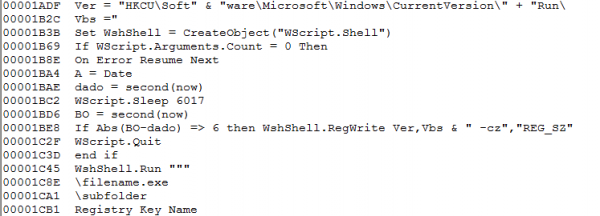
Tiyeni tiyang'ane pa maonekedwe a mtengo wa ndondomeko, komanso kukhalapo kwa chizindikiro cha jekeseni.
![]()
Izi zikusonyeza kuti kumasula kuli mkati. Kwa Visual Basic loaders (aka Zithunzi za VBKrypt kapena Chithunzi cha VBInjector) imadziwika ndi kugwiritsa ntchito shell kodi kuyambitsa malipiro, komanso kupanga jekeseni yokha.
Analysis mu VB Decompiler adawonetsa kukhalapo kwa chochitika katundu pa fomu FegatassocAirballoon2.
Tiyeni tipitirire IDA pro Tiyeni tipite ku adilesi yotchulidwa ndikuwunika ntchitoyo. Codeyo imakhudzidwa kwambiri. Chidutswa chomwe timachikonda chili pansipa.
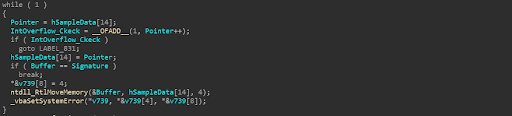
Apa, malo adiresi ya ndondomekoyi amafufuzidwa kuti asayine. Njira imeneyi ndi yokayikitsa kwambiri.
Choyamba, jambulani adilesi yoyambira 0x400100Mtengo uwu ndi wosasunthika ndipo susintha pamene maziko asinthidwa. Pansi pa mikhalidwe yabwino ya wowonjezera kutentha, idzalozera kumapeto PE- mutu wapamwamba wa fayilo. Komabe, nkhokweyo siimakhazikika; mtengo wake ukhoza kusintha, ndipo kufunafuna adiresi yeniyeni ya siginecha yomwe mukufuna, ngakhale kuti sichidzasefukira kusinthasintha, kungatenge nthawi yaitali kwambiri.
Kachiwiri, tanthauzo la siginecha iWGKNdikuganiza kuti ndizodziwikiratu kuti ma byte 4 ndi ang'ono kwambiri kuti asatsimikizire zapadera. Ndipo kupatsidwa mfundo yoyamba, kuthekera kwa cholakwika ndikwambiri.
M’malo mwake, kachidutswa kamene kakukambidwako kumangiriridwa kumapeto kwa zomwe zapezedwa kale bmp- zithunzi ndi offset 0xA1D0D.
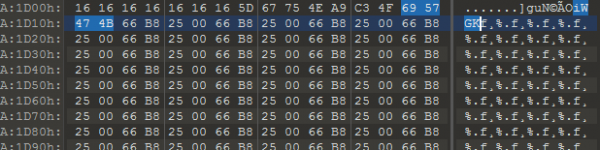
Kuphedwa Shellcode Ikuchitika mu magawo awiri. Yoyamba ikukhudza decrypting the main body. Pankhaniyi, fungulo limatsimikiziridwa ndi mphamvu yankhanza.
Tiyeni titayire yomwe yasinthidwa Shellcode ndipo tiyeni tiwone mizere.
Choyamba, tikudziwa tsopano ntchito yopangira njira ya mwana: PanganiProcessInternalW.
Kachiwiri, tidazindikira momwe zimakhalira mu dongosolo.
Tiyeni tibwerere ku ndondomeko yoyamba. Tiyeni tiyike kuswa pa PanganiProcessInternalW ndi kupitiriza kuphedwa. Pambuyo pake, timawona kugwirizana NtGetContextThread/NtSetContextThread, yomwe imasintha adilesi yoyambira kupha ku adilesi ShellCode.
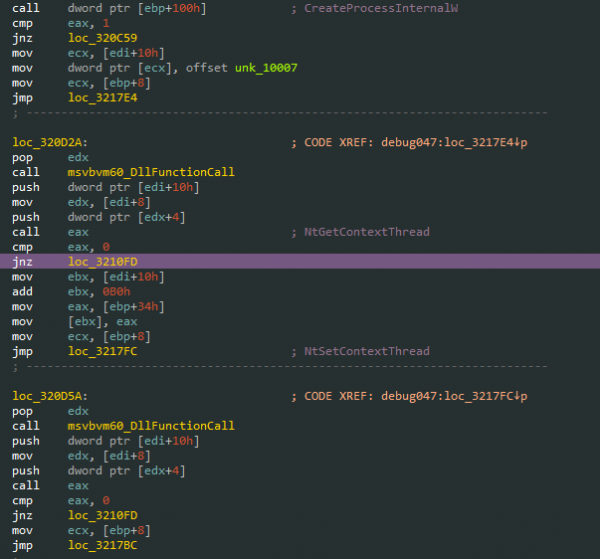
Timagwirizanitsa ndi ndondomeko yopangidwa ndi debugger ndikuyambitsa chochitikacho. Imitsani pa libraryu load/unload, timayambiranso ndondomekoyi ndikudikirira kutsitsa .NET-malaibulale.
Kenako, mothandizidwa ndi ProcessHucker taya zigawo zomwe zili ndi mawonekedwe osapakidwa .NET- ntchito.
Timayimitsa njira zonse ndikuchotsa pulogalamu yaumbanda yomwe idakhazikika m'dongosolo.
Fayilo yotayidwa imatetezedwa ndi chitetezo. NET Reactor, yomwe imatha kuchotsedwa mosavuta pogwiritsa ntchito zofunikira de4dot.
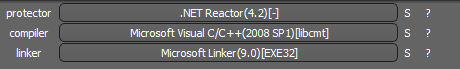
Pogwiritsa ntchito malamulo a YARA omwe adalembedwa kale, titha kutsimikizira kuti tikuchita ndi AgentTesla.
Tiyeni tifotokozere mwachidule
Chifukwa chake, tawonetsa njira yotulutsira zitsanzo zodziwikiratu mwatsatanetsatane pogwiritsa ntchito ma mini-milandu atatu, komanso tidasanthula pulogalamu yaumbanda kutengera mlandu wathunthu, kuzindikiritsa chitsanzo chomwe chikufufuzidwa ngati AgentTesla, kukhazikitsa magwiridwe antchito ake, ndikuzindikira mndandanda wathunthu wazizindikiro za kunyengerera.
Kusanthula kwaumbanda komwe tidapanga kumafuna nthawi ndi khama lalikulu, ndipo ntchitoyi iyenera kuchitidwa ndi wogwira ntchito wodzipereka mkati mwakampani, koma si makampani onse omwe ali okonzeka kugwiritsa ntchito katswiri.
Chimodzi mwazinthu zomwe zimaperekedwa ndi Gulu-IB's Computer Forensics and Malware Analysis Lab ndikuyankha pazochitika za cyber. Pofuna kupewa makasitomala kuwononga nthawi kugwirizanitsa zikalata ndikukambirana nawo mkati mwa cyberattack, Gulu-IB idayambitsa. Wosunga Mayankho a Zochitika, ntchito yoyankha musanalembetse zomwe zikuphatikizanso kusanthula pulogalamu yaumbanda. Zambiri za izi zitha kupezeka apa. .
Ngati mukufuna kuphunzira momwe mungatulutsire zitsanzo za AgentTesla nokha ndikuwona momwe katswiri wa Gulu-IB CERT amachitira, mutha kutsitsa zojambulidwa zamawebusayiti pamutuwu. .
Source: www.habr.com