Kule post siza kukuxelela indlela iqela le-cyber i-OceanLotus (APT32 kunye ne-APT-C-00) kutshanje isebenzise enye yezinto ezifumanekayo esidlangalaleni , ubuthathaka borhwaphilizo lwenkumbulo kwi-Microsoft Office, kunye nendlela i-malware yeqela ifezekisa ngayo ukuzingisa kwiinkqubo ezisengozini ngaphandle kokushiya umkhondo. Okulandelayo, siza kuchaza ukuba, ukusukela ekuqaleni kuka-2019, iqela belisebenzisa i-archives yokuzenzela ukwenza ikhowudi.
I-OceanLotus igxile kwi-cyber espionage, ekujoliswe kuyo okuphambili ibe ngamazwe akuMzantsi-mpuma Asia. Abahlaseli benza amaxwebhu omgunyathi atsalela ingqalelo yamaxhoba anokubakho ukubaqinisekisa ukuba baphumeze ucango lwasemva, kwaye basebenzela ukuphuhlisa izixhobo. Iindlela ezisetyenziselwa ukudala i-honeypots ziyahlukahluka kwiintlaselo, ukusuka kwiifayile "zokwandiswa kabini", ii-archives ezizikhuphayo, amaxwebhu ane-macros, ukuxhaphazwa okwaziwayo.
Ukusebenzisa i-exploit ku-Microsoft Equation Editor
Embindini we-2018, i-OceanLotus yenze iphulo lokuxhaphaza ubungozi be-CVE-2017-11882. Elinye lamaxwebhu akhohlakeleyo eqela le-cyber yahlalutywa ziingcali ezivela kwi-360 Threat Intelligence Centre (), kuquka inkcazo eneenkcukacha zokuxhaphaza. Isithuba esingezantsi siqulethe isishwankathelo soxwebhu olunolunya olunjalo.
Inqanaba lokuqala
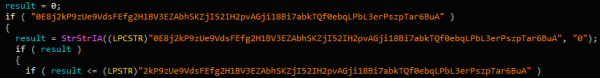
Olu xwebhu FW Report on demonstration of former CNRP in Republic of Korea.doc (SHA-1: D1357B284C951470066AAA7A8228190B88A5C7C3) iyafana naleyo ikhankanywe kuphononongo olungentla. Kuyathakazelisa kuba ijolise kubasebenzisi abanomdla kwiipolitiki zaseCambodia (CNRP - I-Cambodia National Rescue Party, echithwa ekupheleni kwe-2017). Ngaphandle kolwandiso lwe-.doc, uxwebhu lukwifomathi ye-RTF (jonga umfanekiso ongezantsi), iqulethe ikhowudi yenkunkuma, kwaye iphinde igqwethwe.
Umzobo 1. "Inkunkuma" kwi-RTF
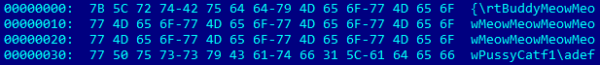
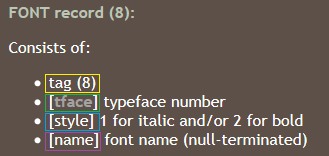
Nangona kukho izinto ezigrunjiweyo, i-Word ivula le fayile ye-RTF ngempumelelo. Njengoko unokubona kuMfanekiso 2, kukho i-EQNOLEFILEHDR isakhiwo kwi-offset 0xC00, ilandelwa yi-header ye-MTEF, kunye nongeniso lwe-MTEF (Umfanekiso 3) wefonti.
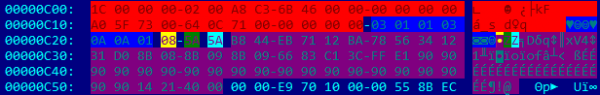
Umfanekiso 2. FONT amaxabiso ongeno
Umfanekiso 3.
Ukuphuphuma okunokwenzeka ebaleni igama, kuba ubungakanani bayo abukhangelwa phambi kokukopa. Igama elide kakhulu libangela ukuba ube sesichengeni. Njengoko unokubona kwimixholo yefayile yeRTF (i-offset 0xC26 kuMfanekiso 2), isithinteli sizaliswe yikhowudi yeqokobhe elandelwa ngumyalelo wedummy (0x90) kunye nedilesi yokubuyisela 0x402114. Idilesi yinxalenye yencoko yababini EQNEDT32.exe, ebonisa imiyalelo RET. Oku kubangela ukuba i-EIP yalathe ekuqaleni kwebala igamaiqulathe ikhowudi yeqokobhe.
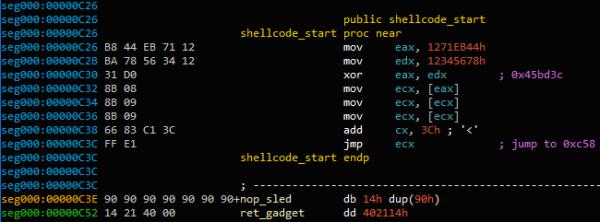
Umfanekiso 4. Ukuqala kwe-exploit shellcode
Idilesi 0x45BD3C igcina uguqulo olurhoxisiweyo de ifike kwisalathisi kwisakhiwo esilayishiweyo ngoku MTEFData. Enye i-shellcode ilapha.
Injongo yekhowudi yeqokobhe kukuphumeza iqhekeza lesibini lekhowudi yekhowudi efakwe kuxwebhu oluvuliweyo. Ikhowudi yoqobo yeqokobhe izama kuqala ukufumana inkcazo yefayile yoxwebhu oluvuliweyo ngokuphinda-phinda phezu kwazo zonke izichazi zenkqubo (NtQuerySystemInformation ngengxoxo SystemExtendedHandleInformation) kunye nokujonga ukuba ziyahambelana na PID isichazi kunye PID inkqubo WinWord kwaye ingaba uxwebhu luvulwe ngesigqubuthelo sofikelelo - 0x12019F.
Ukuqinisekisa ukuba isiphatho esichanekileyo sifunyenwe (kwaye hayi isiphatho kwelinye uxwebhu oluvulekileyo), imixholo yefayile iboniswa kusetyenziswa umsebenzi. CreateFileMapping, kwaye ikhowudi yeqokobhe ijonga ukuba iibytes ezine zokugqibela zoxwebhu ziyahambelana na "yyyy"(Indlela yokuzingela iqanda). Nje ukuba umdlalo ufunyenwe, uxwebhu lukhutshelwa kwisilawulo sexeshana (GetTempPath) Njani ole.dll. Emva koko i-12 bytes yokugqibela yoxwebhu iyafundwa.
![]()
Umzobo 5. Isiphelo seempawu zoxwebhu
32-bit ixabiso phakathi kweziphawuli AABBCCDD и yyyy lulungiso lwekhowudi elandelayo yeqokobhe. Kubizwa ngokuba kusetyenziswa umsebenzi CreateThread. Kutsalwe ikhowudi yeqokobhe efanayo eyayisetyenziswa liqela le-OceanLotus ngaphambili. , esiyikhuphe ngo-Matshi 2018, isasebenza kwindawo yokulahla inqanaba lesibini.
Inqanaba lesibini
Ukususa Amacandelo
Amagama efayile kunye nolawulo akhethwa ngamandla. Ikhowudi ikhetha ngokungenamkhethe igama lefayile ephunyeziweyo okanye yeDLL C:Windowssystem32. Emva koko yenza isicelo kwimithombo yayo kwaye ikhuphe intsimi FileDescription ukusebenzisa njengegama lesiqulathi seefayili. Ukuba oku akusebenzi, ikhowudi ikhetha ngokungakhethiyo igama lesiqulathi seefayili kubalawuli %ProgramFiles% okanye C:Windows (из GetWindowsDirectoryW). Он избегает использования имени, которое может конфликтовать с существующими файлами, и следит за тем, чтобы оно не содержало следующие слова: windows, Microsoft, desktop, system, system32 okanye syswow64. Ukuba uvimba weefayili sele ekhona, "NLS_{6 oonobumba}" ihlonyelwa kwigama.
ubutyebi 0x102 iyahlalutywa kwaye iifayile zilahlwa kuyo %ProgramFiles% okanye %AppData%, kulawulo olukhethiweyo ngokungenamkhethe. Ixesha lokudala elitshintshiweyo ukuze libe namaxabiso afanayo kernel32.dll.
Umzekelo, nantsi incwadi eneenkcukacha kunye noluhlu lweefayile ezenziwe ngokukhetha ephunyeziweyo C:Windowssystem32TCPSVCS.exe njengomthombo wedatha.
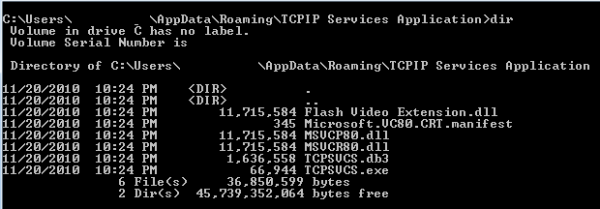
Umzobo 6. Ukukhupha amacandelo ahlukeneyo
Ubume bobutyebi 0x102 kwidropper inzima kakhulu. Ngamafutshane, iqulethe:
— Amagama eefayile
— Ubungakanani befayile kunye nomxholo
-Ifomati yoxinzelelo (COMPRESSION_FORMAT_LZNT1, esetyenziswa ngumsebenzi RtlDecompressBuffer)
Ifayile yokuqala iphinda imiselwe njenge TCPSVCS.exe, esemthethweni AcroTranscoder.exe (ngoku ka FileDescription, SHA-1: 2896738693A8F36CC7AD83EF1FA46F82F32BE5A3).
Usenokuba uqaphele ukuba ezinye iifayile zeDLL zinkulu kuno-11 MB. Oku kungenxa yokuba isithinteli esikhulu esidibanayo sedatha engakhethiyo ibekwe ngaphakathi kwifayile ephunyezwayo. Kungenzeka ukuba le yindlela yokuphepha ukubonwa ngezinye iimveliso zokhuseleko.
Ukuqinisekisa ukuzingisa
ubutyebi 0x101 kwidropper iqulathe ii-32-bit integers ezimbini ezichaza ukuba ukuzingisa kufuneka kunikelwe njani. Ixabiso lokuqala lixela ukuba i-malware iya kuqhubeka njani ngaphandle kwamalungelo omlawuli.
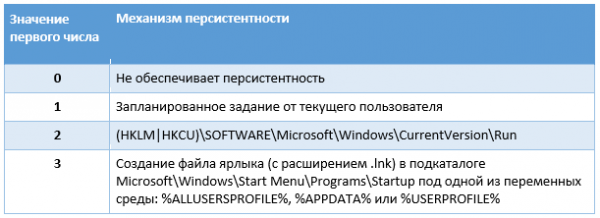
Itheyibhile 1. Indlela yokuzingisa ngaphandle kwamalungelo omlawuli
Ixabiso lenani elipheleleyo lesibini lixela ukuba i-malware kufuneka ifikelele njani ukuzingisa xa isebenza ngamalungelo omlawuli.
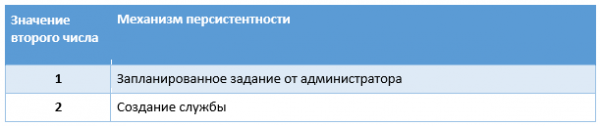
Uluhlu 2. Indlela yokuzingisa enamalungelo omlawuli
Igama lenkonzo ligama lefayile ngaphandle kolwandiso; Igama elibonisiweyo ligama lolawulo, kodwa ukuba sele likhona, umtya " udityaniselwe kuyoRevision 1” (inani liyanda de kufumaneke igama elingasetyenziswanga). Abaqhubi baqinisekisa ukuba ukuzingisa ngenkonzo kwakunamandla - kwimeko yokungaphumeleli, inkonzo kufuneka iqaliswe kwakhona emva kwe-1 yesibini. Emva koko ixabiso WOW64 Iqhosha elitsha lobhaliso lwenkonzo limiselwe ku-4, libonisa ukuba yinkonzo ye-32-bit.
Umsebenzi ocwangcisiweyo wenziwa ngokusebenzisa ujongano oluninzi lweCOM: ITaskScheduler, ITask, ITaskTrigger, IPersistFile и ITaskScheduler. Ngokukodwa, i-malware idala umsebenzi ofihliweyo, ibeka ulwazi lwe-akhawunti kunye nomsebenzisi wangoku okanye ulwazi lomlawuli, kwaye emva koko usete i-trigger.
Lo ngumsebenzi wemihla ngemihla onobude beeyure ezingama-24 kunye nekhefu phakathi kokubulawa kabini kwemizuzu eli-10, okuthetha ukuba kuya kuqhuba ngokuqhubekayo.
Intwana ekhohlakeleyo
Kumzekelo wethu, ifayile ephunyeziweyo TCPSVCS.exe (AcroTranscoder.exe) yisoftware esemthethweni elayisha iiDLL ezisetwe ngokutsha kunye nayo. Kule meko, inomdla Flash Video Extension.dll.
Umsebenzi wayo DLLMain ubiza nje omnye umsebenzi. Kukho ezinye izibhengezo ezingaqondakaliyo:
Umfanekiso 7. Izivakalisi ezingaqondakaliyo
Emva kwezi zitshekisho zilahlekisayo, ikhowudi ifumana icandelo .text ifayile TCPSVCS.exe, itshintshe ukukhusela kwayo PAGE_EXECUTE_READWRITE kwaye uyibhale kwakhona ngokongeza imiyalelo ye-dummy:
Umfanekiso 8. Ulandelelwano lwemiyalelo
Ekupheleni kwidilesi yomsebenzi FLVCore::Uninitialize(void), ithunyelwe ngaphandle Flash Video Extension.dll, kongezwa umyalelo CALL. Oku kuthetha ukuba emva kokuba i-DLL enobungozi ilayishiwe, xa ixesha lokugijima libiza WinMain в TCPSVCS.exe, isalathisi somyalelo siya kwalatha kwi-NOP, ebangela FLVCore::Uninitialize(void), inqanaba elilandelayo.
Umsebenzi wenza ngokulula isimumu ukuqala nge {181C8480-A975-411C-AB0A-630DB8B0A221}ilandelwa ligama lomsebenzisi langoku. Ifunda ke ifayile elahliweyo *.db3, equlathe indawo-ezimeleyo ikhowudi, kunye nokusetyenziswa CreateThread ukwenza umxholo.
Imixholo yefayile *.db3 yikhowudi yeqokobhe esetyenziswa liqela le-OceanLotus. Siphinde sawukhulula ngempumelelo umthwalo wayo wokuhlawula sisebenzisa iscript esisipapashayo .
Isikripthi sikhupha inqanaba lokugqibela. Eli candelo liyi-backdoor, esele siyihlalutye . Oku kunokumiselwa yi GUID {A96B020F-0000-466F-A96D-A91BBF8EAC96} ifayile yokubini. Ubumbeko lwe-malware lusafihliwe kwisixhobo se-PE. Inolungelelwaniso olufanayo, kodwa iiseva zeC&C zahlukile kwezo zangaphambili:
- andreagahuvrauvin[.]com
- byronorenstein[.]com
- stienollmache[.]xyz
Iqela le-OceanLotus liphinda libonise indibaniselwano yeendlela ezahlukeneyo zokuthintela ukubhaqwa. Babuya nomzobo "ococekileyo" wenkqubo yosulelo. Ngokukhetha amagama angahleliweyo kunye nokuzalisa izinto eziphunyeziweyo ngedatha engacwangciswanga, banciphisa inani le-IoCs ethembekileyo (esekelwe kwi-hashes kunye namagama efayile). Ngaphezu koko, enkosi ekusebenziseni i-DLL yomntu wesithathu, abahlaseli kufuneka basuse kuphela i-binary esemthethweni. AcroTranscoder.
Uzikhuphela ngokwawo oovimba
Emva kweefayile ze-RTF, iqela liye lafudukela ekuzikhupheleni ngokwalo (i-SFX) koovimba abanee-iyikhoni zamaxwebhu aqhelekileyo ukuze babhideke ngakumbi umsebenzisi. I-threatbook ibhale malunga noku (). Ekuqalisweni, iifayile ze-RAR ezizikhuphayo ziyalahlwa kwaye ii-DLL ezinolwandiso lwe-.ocx ziye zaphunyezwa, umthwalo wokugqibela oye wabhalwa ngaphambili. {A96B020F-0000-466F-A96D-A91BBF8EAC96}.dll. Ukusukela phakathi kuJanuwari ka-2019, i-OceanLotus ibiphinda isebenzisa obu buchule, kodwa itshintsha uhlengahlengiso oluthile ngokuhamba kwexesha. Kweli candelo siza kuthetha ngobuchule kunye notshintsho.
Ukwenza iLure
Olu xwebhu THICH-THONG-LAC-HANH-THAP-THIEN-VIET-NAM (1).EXE (SHA-1: AC10F5B1D5ECAB22B7B418D6E98FA18E32BBDEAB) yafunyanwa okokuqala ngo-2018. Le fayile ye-SFX yenziwe ngobulumko-kwinkcazo (Ulwazi lohlobo) ithi lo ngumfanekiso weJPEG. Iskripthi se-SFX sijongeka ngolu hlobo:
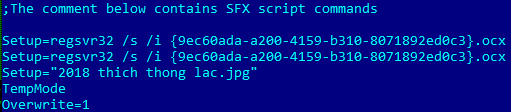
Umzobo 9. Imiyalelo ye-SFX
I-malware iphinda isetyenziselwe {9ec60ada-a200-4159-b310-8071892ed0c3}.ocx (SHA-1: EFAC23B0E6395B1178BCF7086F72344B24C04DCC), kunye nomfanekiso 2018 thich thong lac.jpg.
Umfanekiso we-decoy ujongeka ngolu hlobo:
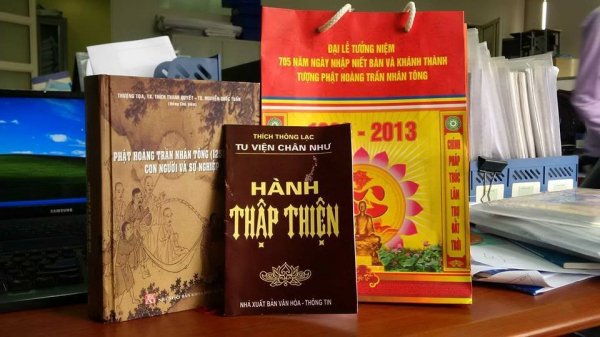
Umzobo 10. Umfanekiso we-Decoy
Usenokuba uqaphele ukuba imigca emibini yokuqala kwiskripthi se-SFX ibiza ifayile ye-OCX kabini, kodwa oku akuyompazamo.
{9ec60ada-a200-4159-b310-8071892ed0c3}.ocx (ShLd.dll)
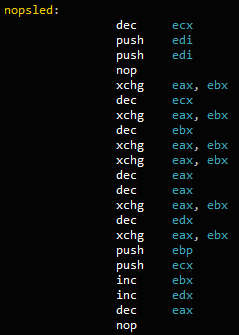
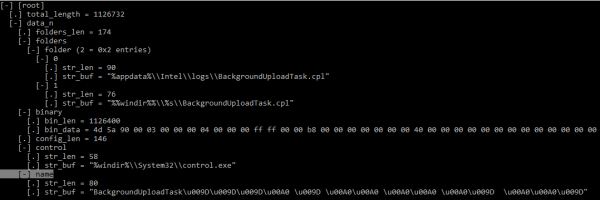
Ukulawulwa kokuhamba kwefayile ye-OCX kufana kakhulu namanye amacandelo e-OceanLotus - ulandelelwano oluninzi lomyalelo JZ/JNZ и PUSH/RET, ukutshintshisana nekhowudi yenkunkuma.
Umzobo 11. Ikhowudi ecacileyo
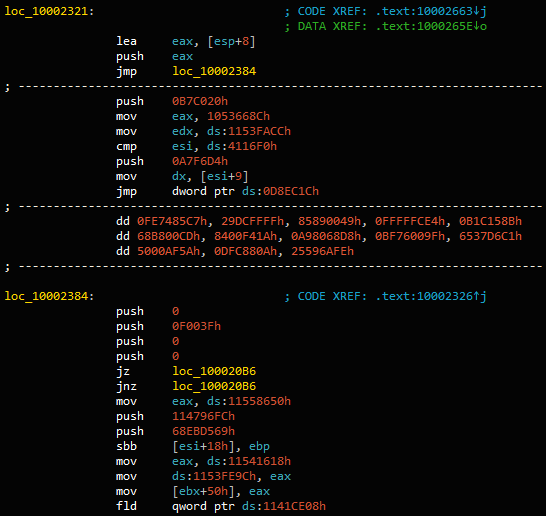
Emva kokucoca ikhowudi yenkunkuma, thumela ngaphandle DllRegisterServer, ebizwa regsvr32.exe, ngoku Landelayo:
Umzobo 12. Ikhowudi yokufaka isiseko
Ngokusisiseko, kwifowuni yokuqala DllRegisterServer thumela ngaphandle ibeka ixabiso lobhaliso HKCUSOFTWAREClassesCLSID{E08A0F4B-1F65-4D4D-9A09-BD4625B9C5A1}Model ye-encrypted offset kwi-DLL (0x10001DE0).
Xa umsebenzi ubizwa okwesibini, ifunda ixabiso elifanayo kwaye iphumeze kuloo dilesi. Ukusuka apha isibonelelo kunye nezenzo ezininzi kwi-RAM ziyafundwa kwaye zenziwa.
I-shellcode ikwayi-PE isilayishi esisetyenziswa kumaphulo adlulileyo e-OceanLotus. Inokuxeliswa kusetyenziswa . Ekugqibeleni uyaphinda db293b825dcc419ba7dc2c49fa2757ee.dll, ilayisha kwinkumbulo kwaye iphumeze DllEntry.
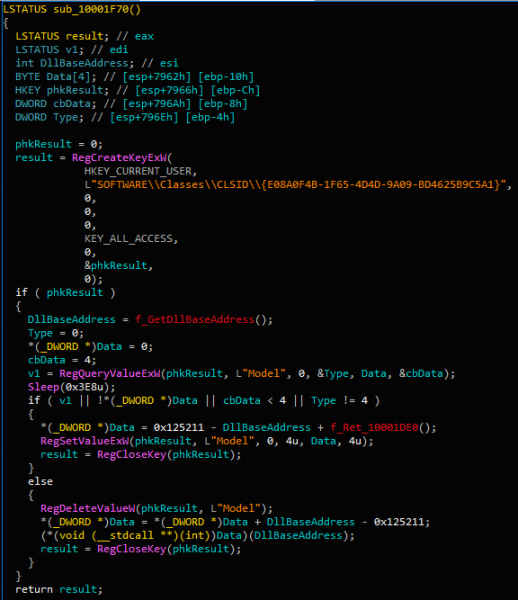
I-DLL ikhupha imixholo yomthombo wayo, i-decrypts (AES-256-CBC) kunye ne-decompresses (LZMA) kuyo. Isixhobo sinefomathi ethile ekulula ukuyiqhawula.
Umzobo 13. Ubume bobume bomfaki (i-KaitaiStruct Visualizer)
Uqwalaselo luchazwe ngokucacileyo - ngokuxhomekeke kwinqanaba lelungelo, idata yokubini iya kubhalelwa %appdata%IntellogsBackgroundUploadTask.cpl okanye %windir%System32BackgroundUploadTask.cpl (okanye SysWOW64 kwiinkqubo ze-64-bit).
Ukuzingisa okuqhubekayo kuqinisekiswa ngokudala umsebenzi ngegama BackgroundUploadTask[junk].jobphi [junk] imele iseti yee-bytes 0x9D и 0xA0.
Igama lesicelo soMsebenzi %windir%System32control.exe, kwaye ixabiso leparameter yindlela eya kwifayile yokubini ekhutshelweyo. Umsebenzi ofihliweyo uqhuba yonke imihla.
Ngokwesakhiwo, ifayile yeCPL yiDLL enegama langaphakathi ac8e06de0a6c4483af9837d96504127e.dll, ethumela ngaphandle umsebenzi CPlApplet. Le fayile isusa uguqulelo oluntsonkothileyo kwisixhobo sayo kuphela {A96B020F-0000-466F-A96D-A91BBF8EAC96}.dll, emva koko ilayishe le DLL kwaye ibize ukuthumela ngaphandle kwayo kuphela DllEntry.
Ifayile yoqwalaselo lwangasemva
Ubumbeko lwe-backdoor lufihliwe kwaye lufakwe kwimithombo yalo. Ulwakhiwo lwefayile yoqwalaselo lufana kakhulu noludlulileyo.
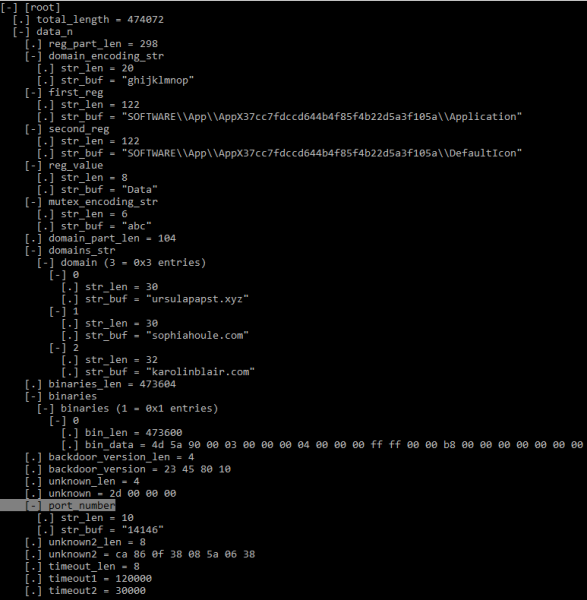
Umzobo 14. Ulwakhiwo lwe-Backdoor configuration (KaitaiStruct Visualizer)
Nangona ulwakhiwo lufana, uninzi lwamaxabiso entsimi luye lwahlaziywa kulawo aboniswe kuwo .
Into yokuqala yoluhlu lokubini iqulathe iDLL (HttpProv.dll MD5: 2559738D1BD4A999126F900C7357B759), . Kodwa ekubeni igama lokuthumela ngaphandle lisusiwe kwi-binary, i-hashes ayihambelani.
Uphando olongezelelweyo
Ngelixa siqokelela iisampulu, siye saqaphela iimpawu ezithile. Lo mzekelo usandula ukuchazwa uvele malunga neJulayi 2018, kwaye eminye efana nayo ivele mva nje phakathi kuJanuwari ukuya ekuqaleni kukaFebruwari ka-2019. I-archive ye-SFX yayisetyenziswe njenge-vector yosulelo, ukulahla uxwebhu olusemthethweni lwe-decoy kunye nefayile ye-OSX enobungozi.
Nangona i-OceanLotus isebenzisa izitampu zexesha ezingeyonyani, siye saqaphela ukuba amaxesha e-SFX kunye neefayile ze-OCX zihlala zifana.0x57B0C36A (08/14/2016 @ 7:15pm UTC) kunye 0x498BE80F (02/06/2009 @ 7:34am UTC) ngokulandelelanayo). Oku mhlawumbi kubonisa ukuba ababhali banohlobo oluthile "lomyili" osebenzisa iitemplates ezifanayo kwaye utshintsha ngokulula ezinye iimpawu.
Phakathi kwamaxwebhu esiwafundileyo ukususela ekuqaleni kwe-2018, kukho amagama ahlukeneyo abonisa amazwe anomdla kubahlaseli:
— Ulwazi olutsha loQhagamshelwano lweMedia yaseKhambodiya(entsha) xls.exe
— 李建香 (个人简历).exe (uxwebhu lomgunyathi lwe-PDF lweCV)
- impendulo, i-Rally e-USA ukususela ngoJulayi 28-29, 2018.exe
Ekubeni i-backdoor yafunyanwa {A96B020F-0000-466F-A96D-A91BBF8EAC96}.dll kunye nokupapashwa kohlahlelo lwayo ngabaphandi abaninzi, siye sabona utshintsho oluthile kwidatha yoqwalaselo lwe-malware.
Okokuqala, ababhali baqala ukususa amagama kwii-DLL zomncedisi (DNSprov.dll kunye neenguqulelo ezimbini HttpProv.dll). Abaqhubi baye bayeka ukupakisha i-DLL yesithathu (uguqulelo lwesibini HttpProv.dll), ukhetha ukulungisela enye kuphela.
Okwesibini, iindawo ezininzi zoqwalaselo lwasemva zatshintshwa, kunokwenzeka ukuba ziphephe ukubhaqwa njengoko ii-IoC ezininzi ziye zafumaneka. Imiba ebalulekileyo elungiswe ngababhali ibandakanya:
- Iqhosha lokubhalisa le-AppX litshintshiwe (bona ii-IoCs)
- umtya wekhowudi yemutex ("def", "abc", "ghi")
- inombolo yezibuko
Ekugqibeleni, zonke iinguqulelo ezintsha ezihlalutyiweyo zineeC&C ezintsha ezidweliswe kwicandelo le-IoCs.
ezifunyanisiweyo
I-OceanLotus iyaqhubeka nokuphuhlisa. Iqela le-cyber ligxile ekusulungekiseni nasekukhuliseni izixhobo kunye ne-decoys. Ababhali bafihla imithwalo yentlawulo ekhohlakeleyo besebenzisa amaxwebhu athatha ingqalelo anomxholo ochaphazelekayo kumaxhoba ajoliswe kuwo. Baphuhlisa izikimu ezitsha kwaye basebenzise izixhobo ezifumaneka esidlangalaleni, ezinje ngeEquation Editor exploit. Ngapha koko, baphucula izixhobo zokunciphisa inani lezinto zakudala ezisele koomatshini bamaxhoba, ngaloo ndlela behlisa ithuba lokubhaqwa yisoftware ye-antivirus.
Izalathisi zokulalanisa
Iimpawu zokulalana kunye ne-MITER ATT&CK iimpawu ziyafumaneka и .
umthombo: www.habr.com


