本文将讨论它是如何工作的 ,并且还将有一个与 Docker 连接的实用部分。
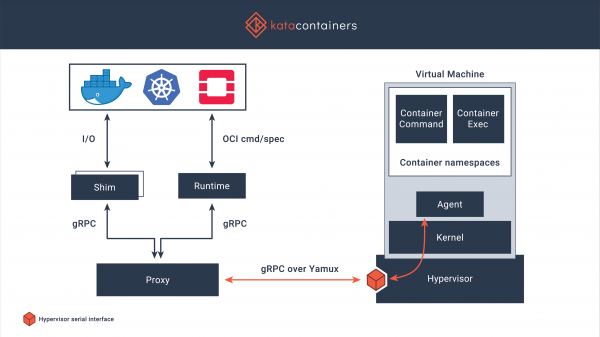
关于 Docker 的常见问题及其解决方案 ,今天我就从Kata Containers简单介绍一下实现。 Kata Containers 是一个基于轻量级虚拟机的安全容器运行时。 使用它们与使用其他容器相同,但除此之外还有使用硬件虚拟化技术的更可靠的隔离。 该项目始于 2017 年,当时同名社区完成了 Intel Clear Containers 和 Hyper.sh RunV 最佳创意的合并,此后继续支持各种架构,包括 AMD64、ARM、IBM p- 和 z -系列。 此外,在管理程序 QEMU、Firecracker 内部支持工作,并且还与 containerd 集成。 该代码可在 在麻省理工学院的许可下。
主要特点
- 与单独的核心一起工作,从而提供网络、内存和 I/O 隔离,可以强制使用基于虚拟化扩展的硬件隔离
- 支持行业标准,包括 OCI(容器格式)、Kubernetes CRI
- 传统容器的稳定性能 Linux在不影响普通虚拟机性能的前提下,提高隔离度。
- 无需在成熟的虚拟机中运行容器,通用接口简化了集成和启动
安装
有 安装选项方面,我会根据操作系统考虑从软件仓库进行安装。 Centos 7.
这一点很重要: Kata Containers 工作仅在硬件上受支持,虚拟化转发并不总是有效,也 需要sse4.1支持 从处理器。
安装 Kata Container 非常简单:
安装用于存储库的实用程序:
# yum -y install yum-utils禁用 Selinux(配置更正确,但为简单起见,我将其禁用):
# setenforce 0
# sed -i 's/^SELINUX=enforcing$/SELINUX=permissive/' /etc/selinux/config我们连接存储库并执行安装
# source /etc/os-release
# ARCH=$(arch)
# BRANCH="${BRANCH:-stable-1.10}"
# yum-config-manager --add-repo "http://download.opensuse.org/repositories/home:/katacontainers:/releases:/${ARCH}:/${BRANCH}/CentOS_${VERSION_ID}/home:katacontainers:releases:${ARCH}:${BRANCH}.repo"
# yum -y install kata-runtime kata-proxy kata-shim调整
我将设置与 docker 一起工作,它的安装是典型的,我不会更详细地描述它:
# rpm -qa | grep docker
docker-ce-cli-19.03.6-3.el7.x86_64
docker-ce-19.03.6-3.el7.x86_64
# docker -v
Docker version 19.03.6, build 369ce74a3c我们对 daemon.json 进行更改:
# cat <<EOF > /etc/docker/daemon.json
{
"default-runtime": "kata-runtime",
"runtimes": {
"kata-runtime": {
"path": "/usr/bin/kata-runtime"
}
}
}
EOF重启泊坞窗:
# service docker restart功能测试
如果在重启docker之前启动容器,可以看到uname会给出主系统上运行的内核版本:
# docker run busybox uname -a
Linux 19efd7188d06 3.10.0-1062.12.1.el7.x86_64 #1 SMP Tue Feb 4 23:02:59 UTC 2020 x86_64 GNU/Linux重新启动后,内核版本如下所示:
# docker run busybox uname -a
Linux 9dd1f30fe9d4 4.19.86-5.container #1 SMP Sat Feb 22 01:53:14 UTC 2020 x86_64 GNU/Linux更多球队!
# time docker run busybox mount
kataShared on / type 9p (rw,dirsync,nodev,relatime,mmap,access=client,trans=virtio)
proc on /proc type proc (rw,nosuid,nodev,noexec,relatime)
tmpfs on /dev type tmpfs (rw,nosuid,size=65536k,mode=755)
devpts on /dev/pts type devpts (rw,nosuid,noexec,relatime,gid=5,mode=620,ptmxmode=666)
sysfs on /sys type sysfs (ro,nosuid,nodev,noexec,relatime)
tmpfs on /sys/fs/cgroup type tmpfs (ro,nosuid,nodev,noexec,relatime,mode=755)
cgroup on /sys/fs/cgroup/systemd type cgroup (ro,nosuid,nodev,noexec,relatime,xattr,name=systemd)
cgroup on /sys/fs/cgroup/cpu,cpuacct type cgroup (ro,nosuid,nodev,noexec,relatime,cpu,cpuacct)
cgroup on /sys/fs/cgroup/blkio type cgroup (ro,nosuid,nodev,noexec,relatime,blkio)
cgroup on /sys/fs/cgroup/memory type cgroup (ro,nosuid,nodev,noexec,relatime,memory)
cgroup on /sys/fs/cgroup/devices type cgroup (ro,nosuid,nodev,noexec,relatime,devices)
cgroup on /sys/fs/cgroup/perf_event type cgroup (ro,nosuid,nodev,noexec,relatime,perf_event)
cgroup on /sys/fs/cgroup/net_cls,net_prio type cgroup (ro,nosuid,nodev,noexec,relatime,net_cls,net_prio)
cgroup on /sys/fs/cgroup/freezer type cgroup (ro,nosuid,nodev,noexec,relatime,freezer)
cgroup on /sys/fs/cgroup/pids type cgroup (ro,nosuid,nodev,noexec,relatime,pids)
cgroup on /sys/fs/cgroup/cpuset type cgroup (ro,nosuid,nodev,noexec,relatime,cpuset)
mqueue on /dev/mqueue type mqueue (rw,nosuid,nodev,noexec,relatime)
shm on /dev/shm type tmpfs (rw,nosuid,nodev,noexec,relatime,size=65536k)
kataShared on /etc/resolv.conf type 9p (rw,dirsync,nodev,relatime,mmap,access=client,trans=virtio)
kataShared on /etc/hostname type 9p (rw,dirsync,nodev,relatime,mmap,access=client,trans=virtio)
kataShared on /etc/hosts type 9p (rw,dirsync,nodev,relatime,mmap,access=client,trans=virtio)
proc on /proc/bus type proc (ro,relatime)
proc on /proc/fs type proc (ro,relatime)
proc on /proc/irq type proc (ro,relatime)
proc on /proc/sys type proc (ro,relatime)
tmpfs on /proc/acpi type tmpfs (ro,relatime)
tmpfs on /proc/timer_list type tmpfs (rw,nosuid,size=65536k,mode=755)
tmpfs on /sys/firmware type tmpfs (ro,relatime)
real 0m2.381s
user 0m0.066s
sys 0m0.039s# time docker run busybox free -m
total used free shared buff/cache available
Mem: 1993 30 1962 0 1 1946
Swap: 0 0 0
real 0m3.297s
user 0m0.086s
sys 0m0.050s快速负载测试
为了评估虚拟化的损失——我运行 sysbench,作为主要示例 .
使用 Docker+containerd 运行 sysbench
处理器测试
sysbench 1.0: multi-threaded system evaluation benchmark
Running the test with following options:
Number of threads: 1
Initializing random number generator from current time
Prime numbers limit: 20000
Initializing worker threads...
Threads started!
General statistics:
total time: 36.7335s
total number of events: 10000
total time taken by event execution: 36.7173s
response time:
min: 3.43ms
avg: 3.67ms
max: 8.34ms
approx. 95 percentile: 3.79ms
Threads fairness:
events (avg/stddev): 10000.0000/0.00
execution time (avg/stddev): 36.7173/0.00内存测试
sysbench 1.0: multi-threaded system evaluation benchmark
Running the test with following options:
Number of threads: 1
Initializing random number generator from current time
Initializing worker threads...
Threads started!
Operations performed: 104857600 (2172673.64 ops/sec)
102400.00 MiB transferred (2121.75 MiB/sec)
General statistics:
total time: 48.2620s
total number of events: 104857600
total time taken by event execution: 17.4161s
response time:
min: 0.00ms
avg: 0.00ms
max: 0.17ms
approx. 95 percentile: 0.00ms
Threads fairness:
events (avg/stddev): 104857600.0000/0.00
execution time (avg/stddev): 17.4161/0.00使用 Docker+Kata 容器运行 sysbench
处理器测试
sysbench 1.0: multi-threaded system evaluation benchmark
Running the test with following options:
Number of threads: 1
Initializing random number generator from current time
Prime numbers limit: 20000
Initializing worker threads...
Threads started!
General statistics:
total time: 36.5747s
total number of events: 10000
total time taken by event execution: 36.5594s
response time:
min: 3.43ms
avg: 3.66ms
max: 4.93ms
approx. 95 percentile: 3.77ms
Threads fairness:
events (avg/stddev): 10000.0000/0.00
execution time (avg/stddev): 36.5594/0.00内存测试
sysbench 1.0: multi-threaded system evaluation benchmark
Running the test with following options:
Number of threads: 1
Initializing random number generator from current time
Initializing worker threads...
Threads started!
Operations performed: 104857600 (2450366.94 ops/sec)
102400.00 MiB transferred (2392.94 MiB/sec)
General statistics:
total time: 42.7926s
total number of events: 104857600
total time taken by event execution: 16.1512s
response time:
min: 0.00ms
avg: 0.00ms
max: 0.43ms
approx. 95 percentile: 0.00ms
Threads fairness:
events (avg/stddev): 104857600.0000/0.00
execution time (avg/stddev): 16.1512/0.00原则上,情况已经很清楚了,但最好多次运行测试,去除异常值并对结果进行平均,所以我还没有做更多的测试。
发现
尽管这样的容器启动时间大约要长五到十倍(使用 containerd 时运行类似命令的典型时间不到三分之一秒),但如果我们采用绝对启动时间,它们仍然工作得非常快(上面有例子,命令平均执行三秒)。 好吧,CPU 和 RAM 的快速测试结果显示几乎相同的结果,这不能不令人高兴,特别是考虑到隔离是使用像 kvm 这样运行良好的机制提供的。
公告
这篇文章是一篇评论,但它让你有机会感受替代运行时。 许多应用领域没有涵盖,例如,该站点描述了在 Kata 容器之上运行 Kubernetes 的能力。 此外,您还可以运行一系列测试,重点是发现安全问题、设置限制和其他有趣的事情。
我请所有在这里阅读和回顾的人参与调查,未来关于该主题的出版物将取决于调查。
只有注册用户才能参与调查。 拜托
我应该继续发表关于 Kata Containers 的文章吗?
80,0%是的,多写点!28
20,0%不,不要……7
35 位用户投票。 7 名用户弃权。
来源: habr.com


