作者在多篇文章中多次談到 DNS 操作的各個方面。 作為部落格的一部分發布。同時,重點始終放在提高這項關鍵網路服務的安全性。

直到最近,儘管 DNS 流量存在明顯的脆弱性(大部分仍以明文形式傳輸),但仍容易受到提供者透過在內容中嵌入廣告來增加收入、政府安全機構和審查制度的惡意行為的影響,以及簡單的犯罪分子,這個過程 儘管有 DNSSEC/DANE、DNScrypt、DNS-over-TLS 和 DNS-over-HTTPS 等各種技術,但仍停滯不前。如果伺服器解決方案(其中一些已經存在了相當長的時間)廣為人知且可用,那麼它們對客戶端軟體的支援還有很多不足之處。
幸運的是,情況正在改變。特別是流行的 Firefox 瀏覽器的開發者 關於預設啟用支援模式的計劃 (衛生部)很快。這應該有助於保護 WWW 用戶的 DNS 流量免受上述威脅,但也可能引入新的威脅。
1. DNS-over-HTTPS 問題
乍一看,將 DNS-over-HTTPS 大規模引入互聯網軟體僅引起了積極的反應。然而,正如人們所說,細節決定成敗。
限制 DoH 廣泛使用範圍的第一個問題是它只關注網路流量。事實上,HTTP 協定及其目前版本 HTTP/2(DoH 所基於的)是 WWW 的基礎。但網路不只是網路。有許多受歡迎的服務,例如電子郵件、各種即時訊息、檔案傳輸系統、多媒體串流等,都不使用HTTP。因此,儘管許多衛生部將其視為萬能藥,但事實證明,如果沒有對瀏覽器技術以外的任何其他方面進行額外(且不必要的)努力,它是不適用的。順便說一句,DNS-over-TLS 看起來更適合這個角色,它在安全標準 TLS 協定中實現了標準 DNS 流量的封裝。
第二個問題可能比第一個問題更重要,它實際上放棄了 DNS 固有的去中心化設計,轉而使用瀏覽器設定中指定的單一 DoH 伺服器。 Mozilla 特別建議使用 Cloudflare 的服務。其他知名網路公司也推出了類似的服務,特別是Google。事實證明,以目前提議的形式實施 DNS-over-HTTPS 只會增加最終用戶對最大服務的依賴。眾所周知,DNS 查詢分析可以提供的資訊可以收集更多有關它的數據,並提高其準確性和相關性。
在這方面,作者過去和現在仍然支持大規模實施DNS-over-TLS,而不是DNS-over-HTTPS,而是DNS-over-TLS 與DNSSEC/DANE 一起作為通用、安全且不利於互聯網進一步集中化的手段以確保 DNS 流量的安全。不幸的是,由於顯而易見的原因,人們不能指望客戶端軟體能夠快速引入對 DoH 替代方案的大規模支持,而且它仍然是安全技術愛好者的領域。
但既然我們現在有了 DoH,為什麼不在逃避公司透過他們的伺服器對我們自己的 DNS-over-HTTPS 伺服器進行潛在監視之後使用它呢?
2. DNS-over-HTTPS 協議
如果你看標準 描述 DNS-over-HTTPS 協議,您可以看到它實際上是一個 Web API,可讓您在 HTTP/2 協定中封裝標準 DNS 套件。這是透過特殊的 HTTP 標頭以及傳輸的 DNS 資料的二進位格式的轉換來實現的(請參閱. 和後續文件)轉換為允許您傳輸和接收它們以及使用必要的元資料的形式。
根據標準,僅支援 HTTP/2 和安全 TLS 連線。
可以使用標準 GET 和 POST 方法發送 DNS 請求。在第一種情況下,請求被轉換為 base64URL 編碼的字串,在第二種情況下,透過二進位形式的 POST 請求正文。在這種情況下,在 DNS 請求和回應期間使用特殊的 MIME 資料類型 應用程式/dns 訊息.
root@eprove:~ # curl -H 'accept: application/dns-message' 'https://my.domaint/dns-query?dns=q80BAAABAAAAAAAAB2V4YW1wbGUDY29tAAABAAE' -v
* Trying 2001:100:200:300::400:443...
* TCP_NODELAY set
* Connected to eprove.net (2001:100:200:300::400) port 443 (#0)
* ALPN, offering h2
* ALPN, offering http/1.1
* successfully set certificate verify locations:
* CAfile: /usr/local/share/certs/ca-root-nss.crt
CApath: none
* TLSv1.3 (OUT), TLS handshake, Client hello (1):
* TLSv1.3 (IN), TLS handshake, Server hello (2):
* TLSv1.3 (IN), TLS handshake, Encrypted Extensions (8):
* TLSv1.3 (IN), TLS handshake, Certificate (11):
* TLSv1.3 (IN), TLS handshake, CERT verify (15):
* TLSv1.3 (IN), TLS handshake, Finished (20):
* TLSv1.3 (OUT), TLS change cipher, Change cipher spec (1):
* TLSv1.3 (OUT), TLS handshake, Finished (20):
* SSL connection using TLSv1.3 / TLS_AES_256_GCM_SHA384
* ALPN, server accepted to use h2
* Server certificate:
* subject: CN=my.domain
* start date: Jul 22 00:07:13 2019 GMT
* expire date: Oct 20 00:07:13 2019 GMT
* subjectAltName: host "my.domain" matched cert's "my.domain"
* issuer: C=US; O=Let's Encrypt; CN=Let's Encrypt Authority X3
* SSL certificate verify ok.
* Using HTTP2, server supports multi-use
* Connection state changed (HTTP/2 confirmed)
* Copying HTTP/2 data in stream buffer to connection buffer after upgrade: len=0
* Using Stream ID: 1 (easy handle 0x801441000)
> GET /dns-query?dns=q80BAAABAAAAAAAAB2V4YW1wbGUDY29tAAABAAE HTTP/2
> Host: eprove.net
> User-Agent: curl/7.65.3
> accept: application/dns-message
>
* TLSv1.3 (IN), TLS handshake, Newsession Ticket (4):
* Connection state changed (MAX_CONCURRENT_STREAMS == 100)!
< HTTP/2 200
< server: h2o/2.3.0-beta2
< content-type: application/dns-message
< cache-control: max-age=86274
< date: Thu, 12 Sep 2019 13:07:25 GMT
< strict-transport-security: max-age=15768000; includeSubDomains; preload
< content-length: 45
<
Warning: Binary output can mess up your terminal. Use "--output -" to tell
Warning: curl to output it to your terminal anyway, or consider "--output
Warning: <FILE>" to save to a file.
* Failed writing body (0 != 45)
* stopped the pause stream!
* Connection #0 to host eprove.net left intact也要注意標題 快取控制: 在網路伺服器的回應中。在參數中 最大年齡 包含所傳回的 DNS 記錄的 TTL 值(如果傳回一組記錄,則為最小值)。
基於上述,DoH 伺服器的功能由幾個階段組成。
- 接收 HTTP 請求。如果這是 GET,則從 base64URL 編碼解碼封包。
- 將此資料包傳送到 DNS 伺服器。
- 從 DNS 伺服器取得回應
- 尋找收到的記錄中的最小 TTL 值。
- 透過 HTTP 回傳回應給客戶端。
3.您自己的 DNS-over-HTTPS 伺服器
運行您自己的 DNS-over-HTTPS 伺服器的最簡單、最快且最有效的方法是使用 HTTP/2 Web 伺服器 ,作者已經對此進行了簡要介紹(參見“«)。
這一選擇得到了以下事實的支持:您自己的 DoH 伺服器的所有程式碼都可以使用整合到 H2O 本身的解釋器來完全實現 。除了標準庫之外,要與 DNS 伺服器交換數據,還需要 (mrbgem) Socket 庫,幸運的是,該庫已經包含在目前開發版本的 H2O 2.3.0-beta2 中 在 FreeBSD 連接埠中。但是,透過克隆儲存庫將其添加到任何先前的版本並不困難 到目錄 /deps 編譯之前。
root@beta:~ # uname -v
FreeBSD 12.0-RELEASE-p10 GENERIC
root@beta:~ # cd /usr/ports/www/h2o
root@beta:/usr/ports/www/h2o # make extract
===> License MIT BSD2CLAUSE accepted by the user
===> h2o-2.2.6 depends on file: /usr/local/sbin/pkg - found
===> Fetching all distfiles required by h2o-2.2.6 for building
===> Extracting for h2o-2.2.6.
=> SHA256 Checksum OK for h2o-h2o-v2.2.6_GH0.tar.gz.
===> h2o-2.2.6 depends on file: /usr/local/bin/ruby26 - found
root@beta:/usr/ports/www/h2o # cd work/h2o-2.2.6/deps/
root@beta:/usr/ports/www/h2o/work/h2o-2.2.6/deps # git clone https://github.com/iij/mruby-socket.git
Клонирование в «mruby-socket»…
remote: Enumerating objects: 385, done.
remote: Total 385 (delta 0), reused 0 (delta 0), pack-reused 385
Получение объектов: 100% (385/385), 98.02 KiB | 647.00 KiB/s, готово.
Определение изменений: 100% (208/208), готово.
root@beta:/usr/ports/www/h2o/work/h2o-2.2.6/deps # ll
total 181
drwxr-xr-x 9 root wheel 18 12 авг. 16:09 brotli/
drwxr-xr-x 2 root wheel 4 12 авг. 16:09 cloexec/
drwxr-xr-x 2 root wheel 5 12 авг. 16:09 golombset/
drwxr-xr-x 4 root wheel 35 12 авг. 16:09 klib/
drwxr-xr-x 2 root wheel 5 12 авг. 16:09 libgkc/
drwxr-xr-x 4 root wheel 26 12 авг. 16:09 libyrmcds/
drwxr-xr-x 13 root wheel 32 12 авг. 16:09 mruby/
drwxr-xr-x 5 root wheel 11 12 авг. 16:09 mruby-digest/
drwxr-xr-x 5 root wheel 10 12 авг. 16:09 mruby-dir/
drwxr-xr-x 5 root wheel 10 12 авг. 16:09 mruby-env/
drwxr-xr-x 4 root wheel 9 12 авг. 16:09 mruby-errno/
drwxr-xr-x 5 root wheel 14 12 авг. 16:09 mruby-file-stat/
drwxr-xr-x 5 root wheel 10 12 авг. 16:09 mruby-iijson/
drwxr-xr-x 5 root wheel 11 12 авг. 16:09 mruby-input-stream/
drwxr-xr-x 6 root wheel 11 12 авг. 16:09 mruby-io/
drwxr-xr-x 5 root wheel 10 12 авг. 16:09 mruby-onig-regexp/
drwxr-xr-x 4 root wheel 10 12 авг. 16:09 mruby-pack/
drwxr-xr-x 5 root wheel 10 12 авг. 16:09 mruby-require/
drwxr-xr-x 6 root wheel 10 12 сент. 16:10 mruby-socket/
drwxr-xr-x 2 root wheel 9 12 авг. 16:09 neverbleed/
drwxr-xr-x 2 root wheel 13 12 авг. 16:09 picohttpparser/
drwxr-xr-x 2 root wheel 4 12 авг. 16:09 picotest/
drwxr-xr-x 9 root wheel 16 12 авг. 16:09 picotls/
drwxr-xr-x 4 root wheel 8 12 авг. 16:09 ssl-conservatory/
drwxr-xr-x 8 root wheel 18 12 авг. 16:09 yaml/
drwxr-xr-x 2 root wheel 8 12 авг. 16:09 yoml/
root@beta:/usr/ports/www/h2o/work/h2o-2.2.6/deps # cd ../../..
root@beta:/usr/ports/www/h2o # make install clean
...Web 伺服器設定通常是標準的。
root@beta:/usr/ports/www/h2o # cd /usr/local/etc/h2o/
root@beta:/usr/local/etc/h2o # cat h2o.conf
# this sample config gives you a feel for how h2o can be used
# and a high-security configuration for TLS and HTTP headers
# see https://h2o.examp1e.net/ for detailed documentation
# and h2o --help for command-line options and settings
# v.20180207 (c)2018 by Max Kostikov http://kostikov.co e-mail: max@kostikov.co
user: www
pid-file: /var/run/h2o.pid
access-log:
path: /var/log/h2o/h2o-access.log
format: "%h %v %l %u %t "%r" %s %b "%{Referer}i" "%{User-agent}i""
error-log: /var/log/h2o/h2o-error.log
expires: off
compress: on
file.dirlisting: off
file.send-compressed: on
file.index: [ 'index.html', 'index.php' ]
listen:
port: 80
listen:
port: 443
ssl:
cipher-suite: ECDHE-ECDSA-CHACHA20-POLY1305:ECDHE-RSA-CHACHA20-POLY1305:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:DHE-RSA-AES128-GCM-SHA256:DHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-AES128-SHA256:ECDHE-RSA-AES128-SHA256:ECDHE-ECDSA-AES128-SHA:ECDHE-RSA-AES256-SHA384:ECDHE-RSA-AES128-SHA:ECDHE-ECDSA-AES256-SHA384:ECDHE-ECDSA-AES256-SHA:ECDHE-RSA-AES256-SHA:DHE-RSA-AES128-SHA256:DHE-RSA-AES128-SHA:DHE-RSA-AES256-SHA256:DHE-RSA-AES256-SHA:ECDHE-ECDSA-DES-CBC3-SHA:ECDHE-RSA-DES-CBC3-SHA:EDH-RSA-DES-CBC3-SHA:AES128-GCM-SHA256:AES256-GCM-SHA384:AES128-SHA256:AES256-SHA256:AES128-SHA:AES256-SHA:DES-CBC3-SHA:!DSS
cipher-preference: server
dh-file: /etc/ssl/dhparams.pem
certificate-file: /usr/local/etc/letsencrypt/live/eprove.net/fullchain.pem
key-file: /usr/local/etc/letsencrypt/live/my.domain/privkey.pem
hosts:
"*.my.domain":
paths: &go_tls
"/":
redirect:
status: 301
url: https://my.domain/
"my.domain:80":
paths: *go_tls
"my.domain:443":
header.add: "Strict-Transport-Security: max-age=15768000; includeSubDomains; preload"
paths:
"/dns-query":
mruby.handler-file: /usr/local/etc/h2o/h2odoh.rb唯一的例外是 URL 處理程序 / dns查詢 我們的 DNS-over-HTTPS 伺服器(用 mruby 編寫並透過處理程序選項呼叫)實際上負責 mruby.handler-文件.
root@beta:/usr/local/etc/h2o # cat h2odoh.rb
# H2O HTTP/2 web server as DNS-over-HTTP service
# v.20190908 (c)2018-2019 Max Kostikov https://kostikov.co e-mail: max@kostikov.co
proc {|env|
if env['HTTP_ACCEPT'] == "application/dns-message"
case env['REQUEST_METHOD']
when "GET"
req = env['QUERY_STRING'].gsub(/^dns=/,'')
# base64URL decode
req = req.tr("-_", "+/")
if !req.end_with?("=") && req.length % 4 != 0
req = req.ljust((req.length + 3) & ~3, "=")
end
req = req.unpack1("m")
when "POST"
req = env['rack.input'].read
else
req = ""
end
if req.empty?
[400, { 'content-type' => 'text/plain' }, [ "Bad Request" ]]
else
# --- ask DNS server
sock = UDPSocket.new
sock.connect("localhost", 53)
sock.send(req, 0)
str = sock.recv(4096)
sock.close
# --- find lowest TTL in response
nans = str[6, 2].unpack1('n') # number of answers
if nans > 0 # no DNS failure
shift = 12
ttl = 0
while nans > 0
# process domain name compression
if str[shift].unpack1("C") < 192
shift = str.index("x00", shift) + 5
if ttl == 0 # skip question section
next
end
end
shift += 6
curttl = str[shift, 4].unpack1('N')
shift += str[shift + 4, 2].unpack1('n') + 6 # responce data size
if ttl == 0 or ttl > curttl
ttl = curttl
end
nans -= 1
end
cc = 'max-age=' + ttl.to_s
else
cc = 'no-cache'
end
[200, { 'content-type' => 'application/dns-message', 'content-length' => str.size, 'cache-control' => cc }, [ str ] ]
end
else
[415, { 'content-type' => 'text/plain' }, [ "Unsupported Media Type" ]]
end
}請注意,本機快取伺服器負責處理 DNS 封包,在本例中 來自標準 FreeBSD 發行版。從安全的角度來看,這是最優的解決方案。但是,沒有什麼可以阻止您更換 本地 到您想要使用的不同 DNS 位址。
root@beta:/usr/local/etc/h2o # local-unbound verison
usage: local-unbound [options]
start unbound daemon DNS resolver.
-h this help
-c file config file to read instead of /var/unbound/unbound.conf
file format is described in unbound.conf(5).
-d do not fork into the background.
-p do not create a pidfile.
-v verbose (more times to increase verbosity)
Version 1.8.1
linked libs: mini-event internal (it uses select), OpenSSL 1.1.1a-freebsd 20 Nov 2018
linked modules: dns64 respip validator iterator
BSD licensed, see LICENSE in source package for details.
Report bugs to unbound-bugs@nlnetlabs.nl
root@eprove:/usr/local/etc/h2o # sockstat -46 | grep unbound
unbound local-unbo 69749 3 udp6 ::1:53 *:*
unbound local-unbo 69749 4 tcp6 ::1:53 *:*
unbound local-unbo 69749 5 udp4 127.0.0.1:53 *:*
unbound local-unbo 69749 6 tcp4 127.0.0.1:53 *:*剩下的就是重新啟動 H2O 並看看會發生什麼。
root@beta:/usr/local/etc/h2o # service h2o restart
Stopping h2o.
Waiting for PIDS: 69871.
Starting h2o.
start_server (pid:70532) starting now...4. 測試
因此,讓我們再次發送測試請求並使用該實用程式查看網路流量來檢查結果 轉儲.
root@beta/usr/local/etc/h2o # curl -H 'accept: application/dns-message' 'https://my.domain/dns-query?dns=q80BAAABAAAAAAAAB2V4YW1wbGUDY29tAAABAAE'
Warning: Binary output can mess up your terminal. Use "--output -" to tell
Warning: curl to output it to your terminal anyway, or consider "--output
Warning: <FILE>" to save to a file.
...
root@beta:~ # tcpdump -n -i lo0 udp port 53 -xx -XX -vv
tcpdump: listening on lo0, link-type NULL (BSD loopback), capture size 262144 bytes
16:32:40.420831 IP (tos 0x0, ttl 64, id 37575, offset 0, flags [none], proto UDP (17), length 57, bad cksum 0 (->e9ea)!)
127.0.0.1.21070 > 127.0.0.1.53: [bad udp cksum 0xfe38 -> 0x33e3!] 43981+ A? example.com. (29)
0x0000: 0200 0000 4500 0039 92c7 0000 4011 0000 ....E..9....@...
0x0010: 7f00 0001 7f00 0001 524e 0035 0025 fe38 ........RN.5.%.8
0x0020: abcd 0100 0001 0000 0000 0000 0765 7861 .............exa
0x0030: 6d70 6c65 0363 6f6d 0000 0100 01 mple.com.....
16:32:40.796507 IP (tos 0x0, ttl 64, id 37590, offset 0, flags [none], proto UDP (17), length 73, bad cksum 0 (->e9cb)!)
127.0.0.1.53 > 127.0.0.1.21070: [bad udp cksum 0xfe48 -> 0x43fa!] 43981 q: A? example.com. 1/0/0 example.com. A 93.184.216.34 (45)
0x0000: 0200 0000 4500 0049 92d6 0000 4011 0000 ....E..I....@...
0x0010: 7f00 0001 7f00 0001 0035 524e 0035 fe48 .........5RN.5.H
0x0020: abcd 8180 0001 0001 0000 0000 0765 7861 .............exa
0x0030: 6d70 6c65 0363 6f6d 0000 0100 01c0 0c00 mple.com........
0x0040: 0100 0100 0151 8000 045d b8d8 22 .....Q...].."
^C
2 packets captured
23 packets received by filter
0 packets dropped by kernel輸出顯示請求如何解析位址 example.com DNS 伺服器已接收並成功處理。
現在剩下的就是在 Firefox 瀏覽器中啟動我們的伺服器。為此,您需要更改配置頁面上的多項設置 about:config中.
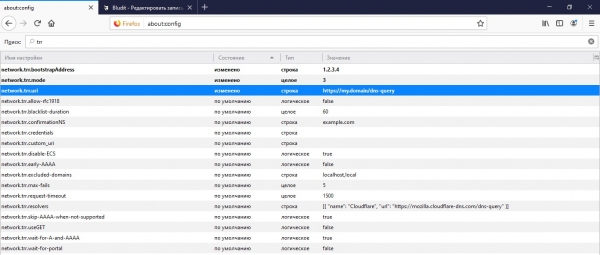
首先,這是我們 API 的位址,瀏覽器將在該位址請求 DNS 訊息 網絡.trr.uri。也建議從此 URL 指定網域 IP,以便使用瀏覽器本身進行安全 IP 解析,而無需存取 DNS 網路.trr.bootstrapAddress。最後是參數本身 網路.trr.模式 包括使用衛生部。將值設為「3」將強制瀏覽器僅使用 DNS-over-HTTPS 進行名稱解析,而更可靠且安全的「2」將優先考慮 DoH,將標準 DNS 查找作為後備選項。
5. 利潤!
這篇文章有幫助嗎?那麼請不要害羞,透過捐款表格(如下)提供資金支持。
來源: www.habr.com


