N'ime edemede a, ọ ga-amasị m ịnye ntuziaka nzọụkwụ site na otu ị ga-esi tinye ngwa ngwa ngwa ngwa ngwa ngwa ngwa ugbu a. Nweta ohere VPN nweta dabere AnyConnect na Cisco ASA - Ụyọkọ na-edozi ibu VPN.
Okwu mmalite: Ọtụtụ ụlọ ọrụ gburugburu ụwa, n'ihi ọnọdụ dị ugbu a na COVID-19, na-agba mbọ ibufe ndị ọrụ ha n'ọrụ dịpụrụ adịpụ. N'ihi mgbanwe zuru ebe niile na ọrụ dịpụrụ adịpụ, ibu dị n'ọnụ ụzọ ụlọ ọrụ VPN dị adị na-abawanye nke ukwuu yana a chọrọ ike ngwa ngwa iji tụọ ha. N'aka nke ọzọ, ọtụtụ ụlọ ọrụ na-amanye ngwa ngwa ịmụta echiche nke ọrụ dịpụrụ adịpụ site na mmalite.
Iji nyere ndị azụmaahịa aka ngwa ngwa mejuputa ohere VPN dị mma, echekwara yana scalable maka ndị ọrụ, Cisco na-enye ikikere izu iri na atọ maka onye ahịa AnyConnect SSL-VPN nwere njiri mara. .
.
Akwadebela m ntuziaka nzọụkwụ site na nzọụkwụ maka nhọrọ dị mfe maka ibunye ụyọkọ VPN Load-Balancing dị ka teknụzụ VPN kacha nwee ike.
Ihe atụ dị n'okpuru ebe a ga-adị nnọọ mfe site n'echiche nke nyocha na ikike algọridim ejiri mee ihe, ma ọ ga-abụ nhọrọ dị mma maka mmalite ngwa ngwa (nke bụ ihe ọtụtụ ndị na-enweghị ugbu a) na ohere nke ime mgbanwe dị omimi na mkpa gị n'oge usoro ntinye.
Ozi dị nkenke: Teknụzụ ụyọkọ VPN anaghị adaba ma ọ bụ ọrụ nchịkọta n'echiche obodo ya; teknụzụ a nwere ike ijikọ ụdị ASA dị iche iche (ya na ụfọdụ mmachi) iji kwado njikọ Remote- Access VPN. Enweghị mmekọrịta nke nnọkọ na nhazi n'etiti ọnụ nke ụyọkọ dị otú ahụ, mana ọ ga-ekwe omume na-ebunye njikọ VPN na-akpaghị aka ma hụ na nkwụsị nke njikọ VPN na-ezighị ezi ruo mgbe opekata mpe otu oghere na-arụ ọrụ na-anọgide na ụyọkọ ahụ. A na-edozi ibu dị na ụyọkọ ahụ na-akpaghị aka dabere na ibu ọrụ nke ọnụ ọnụ site na ọnụ ọgụgụ nke oge VPN.
Maka nnabata mmejọ nke ọnụ ụyọkọ kpọmkwem (ọ bụrụ na achọrọ ya), ị nwere ike iji onye na-eme ihe, yabụ njikọ nke na-arụ ọrụ ga-ahazi ya site na ọnụ ụzọ mbụ nke onye na-eme ihe. Fileover abụghị ọnọdụ dị mkpa maka ịhụ na nnabata mmejọ dị n'ime ụyọkọ Load-Balancing; n'ọnọdụ nke ọdịda ọnụ, ụyọkọ ahụ n'onwe ya ga-ebufe oge onye ọrụ na ọnụ ụzọ ndụ ọzọ, mana na-enweghị idobe ọnọdụ njikọ, nke bụ kpọmkwem ihe. onye na-ebu faịlụ na-enye. N'ihi ya, teknụzụ abụọ a nwere ike jikọta ma ọ bụrụ na ọ dị mkpa.
Otu ụyọkọ VPN Load-Balancing nwere ike ịnwe ihe karịrị ọnụ abụọ.
A na-akwado ụyọkọ VPN Load-Balancing na ASA 5512-X na karịa.
Ebe ọ bụ na ASA ọ bụla n'ime ụyọkọ VPN Load-Balancing bụ ngalaba nọọrọ onwe ya n'ihe gbasara ntọala, anyị na-eme usoro nhazi niile n'otu n'otu na ngwaọrụ ọ bụla.
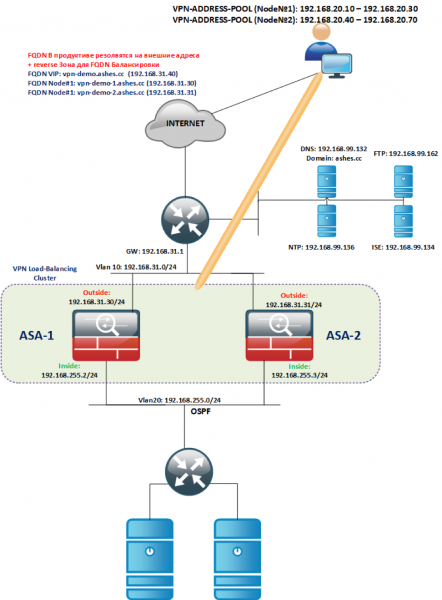
Topology ezi uche dị na ihe atụ e nyere bụ:
Nbunye izizi:
Anyị na-ebuga ihe atụ ASAv nke ndebiri anyị chọrọ (ASAv5/10/30/50) site na onyonyo a.
Anyị na-ekenye oghere dị n'ime / n'èzí na otu VLAN (N'èzí na VLAN nke ya, ININIDE na nke ya, ma na-emekarị n'ime ụyọkọ ahụ, lee topology), ọ dị mkpa na interfaces nke otu ụdị dị n'otu akụkụ L2.
Ikikere:
- N'oge echichi, ASAv agaghị enwe ikikere ọ bụla ma ọ ga-ejedebe na 100kbit / sk.
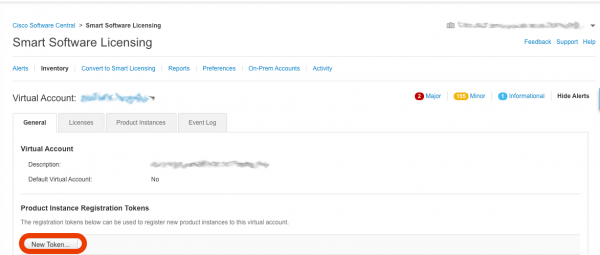
- Iji tinye akwụkwọ ikike, ị ga-ewepụta akara n'ime akaụntụ Smart-Account gị: -> Ịnye ikike ngwa ngwa
- Na mpio mepere emepe, pịa bọtịnụ Ọhụrụ Token

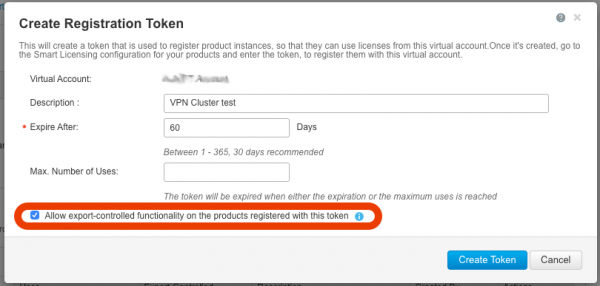
- Jide n'aka na mpaghara dị na mpio mepere emepe na-arụ ọrụ na igbe nlele Kwe ka ọrụ na-achịkwa mbupụ... Enweghị mpaghara a na-arụ ọrụ, ị gaghị enwe ike iji ọrụ nzuzo siri ike na, ya mere, VPN. Ọ bụrụ na mpaghara a anaghị arụ ọrụ, biko kpọtụrụ ndị otu akaụntụ gị ka ị rịọ ka e mee ya.

- Mgbe ịpịchara bọtịnụ ahụ Mepụta Token, A ga-emepụta akara nke anyị ga-eji nweta ikike maka ASAv, detuo ya:

- Ka anyị kwugharịa usoro C,D,E maka ASAv nke ọ bụla etinyere.
- Iji mee ka ọ dịkwuo mfe iṅomi token, ka anyị mee telnet nwa oge. Ka anyị hazie ASA ọ bụla (ihe atụ dị n'okpuru na-egosi ntọala na ASA-1). telnet si n'èzí anaghị arụ ọrụ, ọ bụrụ na ịchọrọ ya n'ezie, gbanwee ọkwa nchekwa na 100 gaa n'èzí, wee gbanwee ya azụ.
! ciscoasa(config)# int gi0/0 ciscoasa(config)# nameif outside ciscoasa(config)# ip address 192.168.31.30 255.255.255.0 ciscoasa(config)# no shut ! ciscoasa(config)# int gi0/1 ciscoasa(config)# nameif inside ciscoasa(config)# ip address 192.168.255.2 255.255.255.0 ciscoasa(config)# no shut ! ciscoasa(config)# telnet 0 0 inside ciscoasa(config)# username admin password cisco priv 15 ciscoasa(config)# ena password cisco ciscoasa(config)# aaa authentication telnet console LOCAL ! ciscoasa(config)# route outside 0 0 192.168.31.1 ! ciscoasa(config)# wr !- Iji debanye aha akara na igwe ojii Smart-Account, ị ga-enyerịrị ASA ohere ịntanetị, .
Na nkenke, ASA chọrọ:
- Nweta ịntanetị site na HTTPS;
- oge mmekọrịta (n'ụzọ ziri ezi site na NTP);
- Ihe nkesa DNS edebanyere aha;
- Anyị na-aga site na telnet na ASA anyị wee mee ntọala iji mee ka ikike rụọ ọrụ site na Smart-Account.
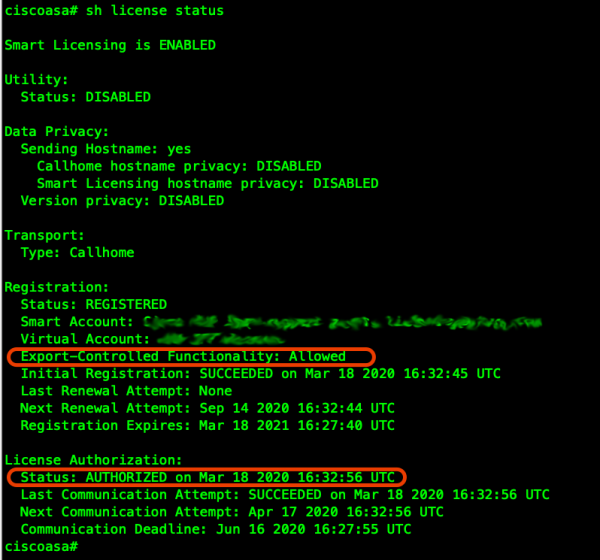
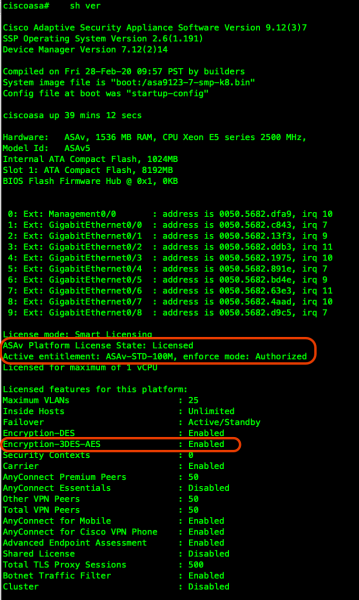
! ciscoasa(config)# clock set 19:21:00 Mar 18 2020 ciscoasa(config)# clock timezone MSK 3 ciscoasa(config)# ntp server 192.168.99.136 ! ciscoasa(config)# dns domain-lookup outside ciscoasa(config)# DNS server-group DefaultDNS ciscoasa(config-dns-server-group)# name-server 192.168.99.132 ! ! Проверим работу DNS: ! ciscoasa(config-dns-server-group)# ping ya.ru Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 87.250.250.242, timeout is 2 seconds: !!!!! ! ! Проверим синхронизацию NTP: ! ciscoasa(config)# show ntp associations address ref clock st when poll reach delay offset disp *~192.168.99.136 91.189.94.4 3 63 64 1 36.7 1.85 17.5 * master (synced), # master (unsynced), + selected, - candidate, ~ configured ! ! Установим конфигурацию нашей ASAv для Smart-Licensing (в соответствии с Вашим профилем, в моем случае 100М для примера) ! ciscoasa(config)# license smart ciscoasa(config-smart-lic)# feature tier standard ciscoasa(config-smart-lic)# throughput level 100M ! ! В случае необходимости можно настроить доступ в Интернет через прокси используйте следующий блок команд: !call-home ! http-proxy ip_address port port ! ! Далее мы вставляем скопированный из портала Smart-Account токен (<token>) и регистрируем лицензию ! ciscoasa(config)# end ciscoasa# license smart register idtoken <token>- Anyị na-enyocha na ngwaọrụ ahụ edebanyela akwụkwọ ikike nke ọma yana nhọrọ nzuzo dị:


Na-ahazi SSL-VPN isi n'ọnụ ụzọ ọ bụla
- Ọzọ, anyị na-ahazi ohere site na SSH na ASDM:
ciscoasa(config)# ssh ver 2 ciscoasa(config)# aaa authentication ssh console LOCAL ciscoasa(config)# aaa authentication http console LOCAL ciscoasa(config)# hostname vpn-demo-1 vpn-demo-1(config)# domain-name ashes.cc vpn-demo-1(config)# cry key gen rsa general-keys modulus 4096 vpn-demo-1(config)# ssh 0 0 inside vpn-demo-1(config)# http 0 0 inside ! ! Поднимем сервер HTTPS для ASDM на порту 445 чтобы не пересекаться с SSL-VPN порталом ! vpn-demo-1(config)# http server enable 445 !- Ka ASDM rụọ ọrụ, ị ga-ebu ụzọ budata ya na cisco.com, n'ọnọdụ m ọ bụ faịlụ a:

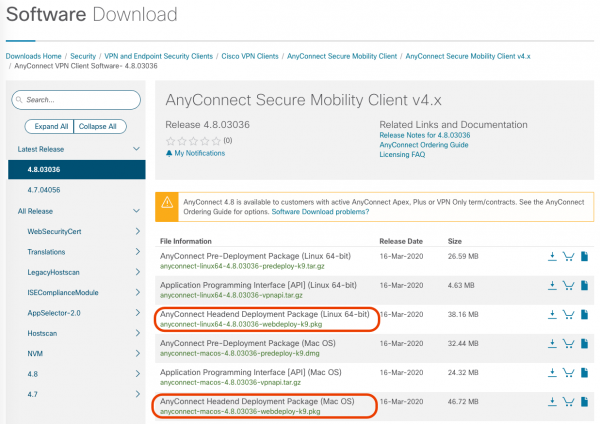
- Maka onye ahịa AnyConnect ka ọ rụọ ọrụ, ịkwesịrị ibudata onyonyo na ASA ọ bụla maka desktọọpụ ndị ahịa ọ bụla ejiri (emebere iji Linux/Windows/MAC), ị ga-achọ faịlụ nwere. Ngwungwu ibunye isi N'aha:

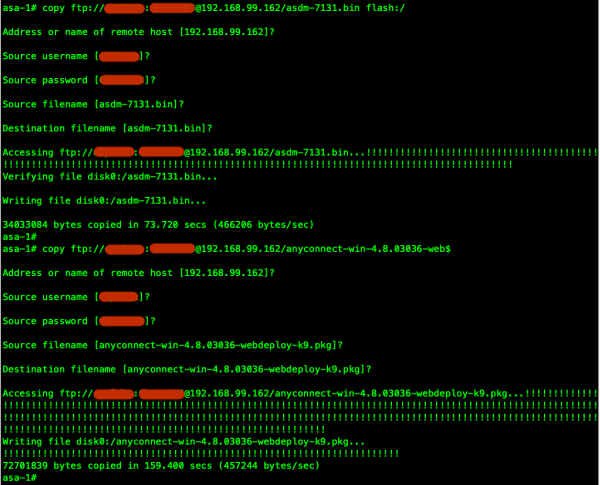
- Enwere ike ibugo faịlụ ebudatara, dịka ọmụmaatụ, na sava FTP wee bulite ya na ASA onye ọ bụla:

- Anyị na-ahazi ASDM na asambodo nke onwe maka SSL-VPN (a na-atụ aro ka iji akwụkwọ ntụkwasị obi na mmepụta). FQDN guzobere nke ụyọkọ Virtual Address (vpn-demo.ashes.cc), yana FQDN ọ bụla metụtara adreesị mpụga nke ọnụ ụyọkọ ọ bụla ga-edozirịrị na mpaghara DNS mpụga gaa na adreesị IP nke interface OUTSIDE (ma ọ bụ gaa na adreesị mapụtara ma ọ bụrụ na ejiri udp/443 mbugharị ọdụ ụgbọ mmiri (DTLS) na tcp/443 (TLS)). Nkọwa zuru ezu na ihe achọrọ maka akwụkwọ ahụ akọwapụtara na ngalaba Akwụkwọ Asambodo akwụkwọ.
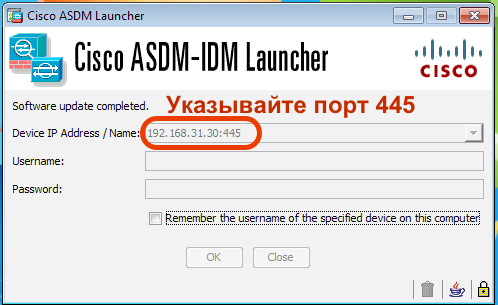
! vpn-demo-1(config)# crypto ca trustpoint SELF vpn-demo-1(config-ca-trustpoint)# enrollment self vpn-demo-1(config-ca-trustpoint)# fqdn vpn-demo.ashes.cc vpn-demo-1(config-ca-trustpoint)# subject-name cn=*.ashes.cc, ou=ashes-lab, o=ashes, c=ru vpn-demo-1(config-ca-trustpoint)# serial-number vpn-demo-1(config-ca-trustpoint)# crl configure vpn-demo-1(config-ca-crl)# cry ca enroll SELF % The fully-qualified domain name in the certificate will be: vpn-demo.ashes.cc Generate Self-Signed Certificate? [yes/no]: yes vpn-demo-1(config)# ! vpn-demo-1(config)# sh cry ca certificates Certificate Status: Available Certificate Serial Number: 4d43725e Certificate Usage: General Purpose Public Key Type: RSA (4096 bits) Signature Algorithm: SHA256 with RSA Encryption Issuer Name: serialNumber=9A439T02F95 hostname=vpn-demo.ashes.cc cn=*.ashes.cc ou=ashes-lab o=ashes c=ru Subject Name: serialNumber=9A439T02F95 hostname=vpn-demo.ashes.cc cn=*.ashes.cc ou=ashes-lab o=ashes c=ru Validity Date: start date: 00:16:17 MSK Mar 19 2020 end date: 00:16:17 MSK Mar 17 2030 Storage: config Associated Trustpoints: SELF CA Certificate Status: Available Certificate Serial Number: 0509 Certificate Usage: General Purpose Public Key Type: RSA (4096 bits) Signature Algorithm: SHA1 with RSA Encryption Issuer Name: cn=QuoVadis Root CA 2 o=QuoVadis Limited c=BM Subject Name: cn=QuoVadis Root CA 2 o=QuoVadis Limited c=BM Validity Date: start date: 21:27:00 MSK Nov 24 2006 end date: 21:23:33 MSK Nov 24 2031 Storage: config Associated Trustpoints: _SmartCallHome_ServerCA- Iji lelee ọrụ ASDM, echefula ịkọwapụta ọdụ ụgbọ mmiri, dịka ọmụmaatụ:

- Ka anyị mee ntọala ọwara isi:
- Anyị ga-eme ka ụlọ ọrụ netwọk nweta site a ọwara, na jikọọ na Ịntanetị ozugbo (ọ bụghị usoro kachasị nchebe na enweghị usoro nchebe na njikọ njikọ, ọ ga-ekwe omume ịbanye site na onye nwe ụlọ na-ebute ọrịa na mmepụta data ụlọ ọrụ, nhọrọ. gbawara-ọwara-atụmatụ tunnelall ga-ekwe ka okporo ụzọ ndị ọbịa niile banye n'ọwara ahụ. Ka o sina dị Kewara-Ọwara na-eme ka o kwe omume iwepụ ọnụ ụzọ VPN ma ghara ịhazi okporo ụzọ ịntanetị).
- Anyị ga-enye ndị ọbịa n'ọwara a adreesị sitere na subnet 192.168.20.0/24 (ọdọ mmiri nke adreesị 10 ruo 30 (maka ọnụ #1)). Ọnụ ọ bụla dị na ụyọkọ ahụ ga-enwerịrị ọdọ mmiri VPN nke ya.
- Ka anyị jiri onye ọrụ emebere mpaghara na ASA rụọ nyocha isi (anaghị akwado nke a, nke a bụ usoro kachasị mfe), ọ ka mma ịme nyocha site na. LDAP/RADIUS, ma ọ bụ ka mma, tie Nyocha ọtụtụ ihe (MFA)dịka ọmụmaatụ Cisco DUO.
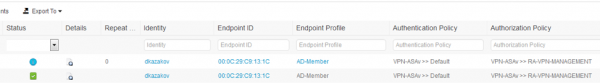
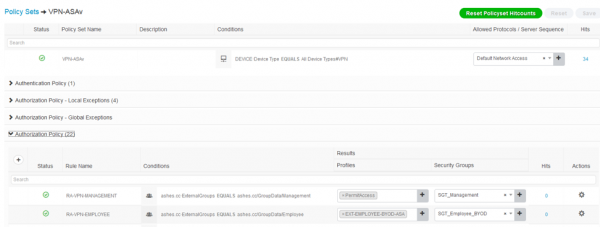
! vpn-demo-1(config)# ip local pool vpn-pool 192.168.20.10-192.168.20.30 mask 255.255.255.0 ! vpn-demo-1(config)# access-list split-tunnel standard permit 192.168.0.0 255.255.0.0 ! vpn-demo-1(config)# group-policy SSL-VPN-GROUP-POLICY internal vpn-demo-1(config)# group-policy SSL-VPN-GROUP-POLICY attributes vpn-demo-1(config-group-policy)# vpn-tunnel-protocol ssl-client vpn-demo-1(config-group-policy)# split-tunnel-policy tunnelspecified vpn-demo-1(config-group-policy)# split-tunnel-network-list value split-tunnel vpn-demo-1(config-group-policy)# dns-server value 192.168.99.132 vpn-demo-1(config-group-policy)# default-domain value ashes.cc vpn-demo-1(config)# tunnel-group DefaultWEBVPNGroup general-attributes vpn-demo-1(config-tunnel-general)# default-group-policy SSL-VPN-GROUP-POLICY vpn-demo-1(config-tunnel-general)# address-pool vpn-pool ! vpn-demo-1(config)# username dkazakov password cisco vpn-demo-1(config)# username dkazakov attributes vpn-demo-1(config-username)# service-type remote-access ! vpn-demo-1(config)# ssl trust-point SELF vpn-demo-1(config)# webvpn vpn-demo-1(config-webvpn)# enable outside vpn-demo-1(config-webvpn)# anyconnect image disk0:/anyconnect-win-4.8.03036-webdeploy-k9.pkg vpn-demo-1(config-webvpn)# anyconnect enable !- (Nhọrọ): N'ihe atụ dị n'elu, anyị na-eji onye ọrụ mpaghara na firewall iji nyochaa ndị ọrụ dịpụrụ adịpụ, nke na-abaghị uru ma e wezụga na ụlọ nyocha. Aga m enye ihe atụ otu esi eme ngwa ngwa megharịa ntọala maka nyocha na okirikiri ihe nkesa, eji atụ Cisco Identity Services Engine:
vpn-demo-1(config-aaa-server-group)# dynamic-authorization vpn-demo-1(config-aaa-server-group)# interim-accounting-update vpn-demo-1(config-aaa-server-group)# aaa-server RADIUS (outside) host 192.168.99.134 vpn-demo-1(config-aaa-server-host)# key cisco vpn-demo-1(config-aaa-server-host)# exit vpn-demo-1(config)# tunnel-group DefaultWEBVPNGroup general-attributes vpn-demo-1(config-tunnel-general)# authentication-server-group RADIUS !Ngwakọta a mere ka ọ bụghị naanị ijikọ usoro nyocha ngwa ngwa na ọrụ ndekọ aha AD, kamakwa ịmata ma kọmputa ejikọrọ ọ bụ nke AD, ghọta ma ọ bụ ngwaọrụ ụlọ ọrụ ma ọ bụ nkeonwe, wee chọpụta ọnọdụ nke ejikọrọ. ngwaọrụ.


- Ka anyị hazie Transparent NAT ka ọ ghara igbochi okporo ụzọ dị n'etiti onye ahịa na akụrụngwa netwọkụ nke netwọkụ ụlọ ọrụ:
vpn-demo-1(config-network-object)# subnet 192.168.20.0 255.255.255.0 ! vpn-demo-1(config)# nat (inside,outside) source static any any destination static vpn-users vpn-users no-proxy-arp- (Nhọrọ): Iji kpughee ndị ahịa anyị na ịntanetị site na ASA (mgbe ị na-eji tunnelall nhọrọ) site na iji PAT, ma pụọ na otu interface ahụ dị na mpụga ebe ejikọrọ, ịkwesịrị ịme ntọala ndị a.
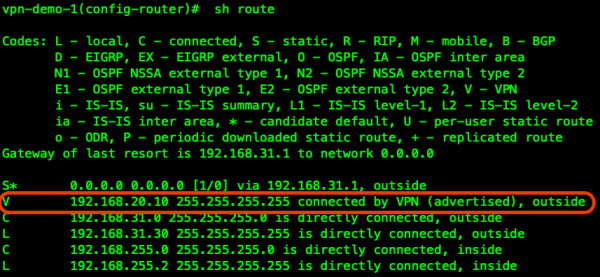
vpn-demo-1(config-network-object)# nat (outside,outside) source dynamic vpn-users interface vpn-demo-1(config)# nat (inside,outside) source dynamic any interface vpn-demo-1(config)# same-security-traffic permit intra-interface !- Ọ dị oke mkpa mgbe ị na-eji ụyọkọ iji mee ka netwọkụ dị n'ime mee ka ọ ghọta nke ASA ga-esi weghachi ndị ọrụ okporo ụzọ; maka nke a ọ dị mkpa iji kesaa ụzọ / adreesị 32 enyere ndị ahịa.
N'oge a, anyị ahazibeghị ụyọkọ ahụ, mana anyị enweelarị ọnụ ụzọ VPN na-arụ ọrụ nke ị nwere ike jikọọ n'otu n'otu site na FQDN ma ọ bụ IP.

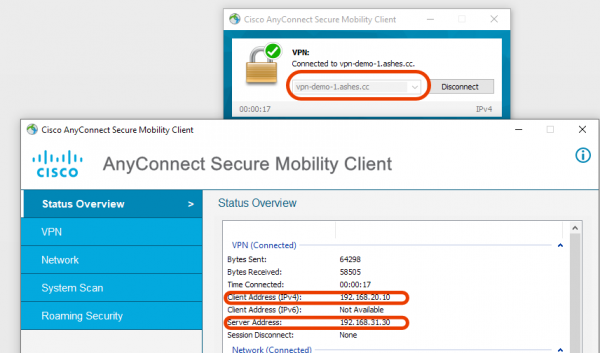
Anyị na-ahụ onye ahịa ejikọrọ na tebụl ntụgharị nke ASA mbụ:

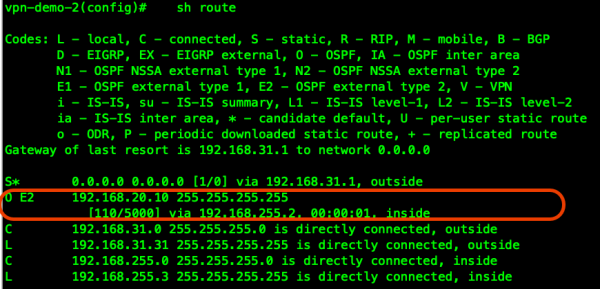
Ka ụyọkọ VPN anyị niile na netwọkụ ụlọ ọrụ mara ụzọ ndị ahịa anyị ga-esi aga, anyị ga-ekesa prefix nke ndị ahịa ka ọ bụrụ usoro ngagharị siri ike, dịka ọmụmaatụ OSPF:
! vpn-demo-1(config)# route-map RMAP-VPN-REDISTRIBUTE permit 1 vpn-demo-1(config-route-map)# match ip address VPN-REDISTRIBUTE ! vpn-demo-1(config)# router ospf 1 vpn-demo-1(config-router)# network 192.168.255.0 255.255.255.0 area 0 vpn-demo-1(config-router)# log-adj-changes vpn-demo-1(config-router)# redistribute static metric 5000 subnets route-map RMAP-VPN-REDISTRIBUTEUgbu a, anyị nwere ụzọ gaa na onye ahịa site na ọnụ ụzọ ASA-2 nke abụọ na ndị ọrụ ejikọrọ na ọnụ ụzọ VPN dị iche iche n'ime ụyọkọ ahụ nwere ike, dịka ọmụmaatụ, na-ekwurịta okwu ozugbo site na ekwentị ụlọ ọrụ, dị ka nloghachi okporo ụzọ site na akụrụngwa nke onye ọrụ rịọrọ ga-abata. n'ọnụ ụzọ VPN chọrọ:

Ka anyị gaa n'ihu n'ịtọlite ụyọkọ Load-Balancing.
A ga-eji adreesị 192.168.31.40 mee ihe dị ka IP mebere (VIP - ndị ahịa VPN niile ga-ejikọ ya na mbụ), site na adreesị a, Cluster Master ga-atụgharị gaa na ọnụ ụyọkọ dị obere. Echefula ịdebanye aha zipu ma tụgharịa ndekọ ndekọ DNS ma maka adreesị mpụga ọ bụla/FQDN nke ọnụ ụyọkọ ọ bụla, yana maka VIP.
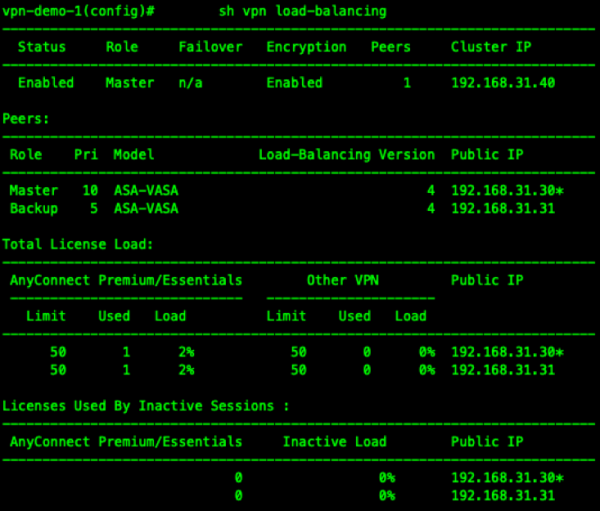
vpn-demo-1(config)# vpn load-balancing vpn-demo-1(config-load-balancing)# interface lbpublic outside vpn-demo-1(config-load-balancing)# interface lbprivate inside vpn-demo-1(config-load-balancing)# priority 10 vpn-demo-1(config-load-balancing)# cluster ip address 192.168.31.40 vpn-demo-1(config-load-balancing)# cluster port 4000 vpn-demo-1(config-load-balancing)# redirect-fqdn enable vpn-demo-1(config-load-balancing)# cluster key cisco vpn-demo-1(config-load-balancing)# cluster encryption vpn-demo-1(config-load-balancing)# cluster port 9023 vpn-demo-1(config-load-balancing)# participate vpn-demo-1(config-load-balancing)#- Anyị na-eji ndị ahịa abụọ ejikọrọ na-elele ọrụ nke ụyọkọ ahụ:

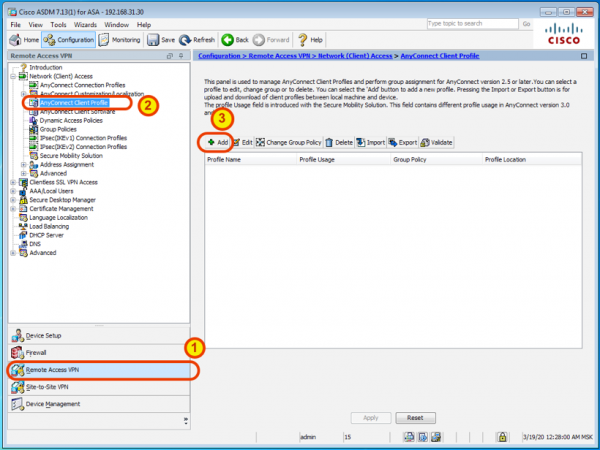
- Ka anyị mee ka ahụmịhe onye ahịa dịkwuo mma site na profaịlụ AnyConnect ebudatara na-akpaghị aka site na ASDM.

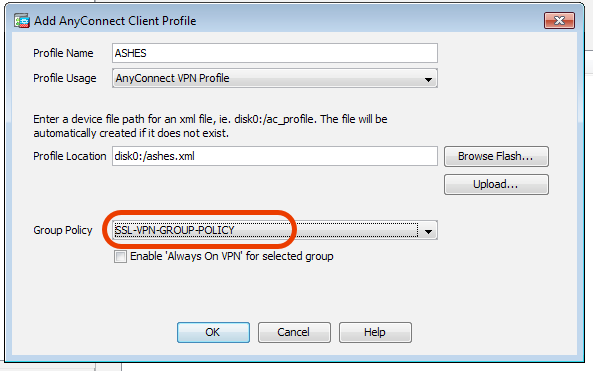
Anyị na-akpọ profaịlụ ahụ n'ụzọ dabara adaba wee jikọta amụma otu anyị na ya:

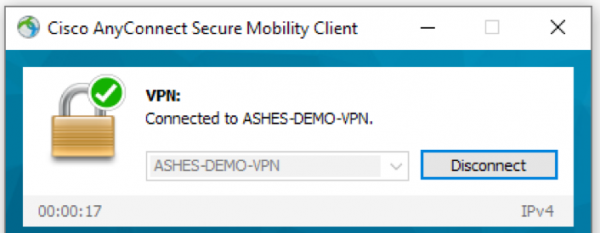
Mgbe njikọ ndị ahịa na-esote, a ga-ebudata profaịlụ a na-akpaghị aka ma tinye ya na onye ahịa AnyConnect, yabụ ọ bụrụ na ịchọrọ ijikọ, naanị ị ga-ahọrọ ya na listi:

Ebe ọ bụ na iji ASDM anyị mepụtara profaịlụ a na naanị otu ASA, echefula ịmegharị usoro na ASA ndị fọdụrụ na ụyọkọ ahụ.
Mmechi: Yabụ, anyị wepụrụ ụyọkọ ọtụtụ ọnụ ụzọ VPN ngwa ngwa nwere ndozi ibu akpaka. Ịtinye ọnụ ọhụrụ na ụyọkọ ahụ dị mfe, na-enweta nhịahụ dị mfe site na ibugharị igwe ASAv mebere ọhụrụ ma ọ bụ iji ASA ngwaike. Onye ahịa AnyConnect bara ọgaranya nwere ike ime ka ike njikọ ime obodo gị dịkwuo mma site na iji Ọkwa (ntụle steeti), kasị dị irè na-eji na njikọ na a centralized ohere njikwa na ndekọ usoro Igwe ọrụ njirimara.
isi: www.habr.com