I-Ryuk yenye yezona zinto zidumileyo zokukhetha i-ransomware kwiminyaka embalwa edlulileyo. Ekubeni yaqala ukubonakala ehlobo lika-2018, iqokelele , ngokukodwa kwindawo yoshishino, eyona nto ijoliswe kuyo ekuhlaselweni kwayo.
1. Ulwazi ngokubanzi
Olu xwebhu luqulethe uhlalutyo lokwahluka kweRyuk ransomware, kunye nomlayishi onoxanduva lokulayisha i-malware kwinkqubo.
I-Ryuk ransomware yaqala ukubonakala ehlotyeni le-2018. Omnye umahluko phakathi kwe-Ryuk kunye nenye i-ransomware kukuba ijolise ekuhlaseleni iindawo zenkampani.
Embindini wonyaka ka-2019, amaqela e-cybercriminal ahlasele inani elikhulu leenkampani zaseSpain zisebenzisa le ntlawulo.

Irayisi. 1: Isicatshulwa esivela ku-El Confidencial malunga nohlaselo lwe-Ryuk ransomware [1]

Irayisi. 2: Isicatshulwa esivela ku-El País malunga nohlaselo olwenziwe kusetyenziswa iRyuk ransomware [2]
Kulo nyaka, uRyuk uhlasele inani elikhulu leenkampani kumazwe ahlukeneyo. Njengoko ubona kumanani angezantsi, iJamani, iChina, iAlgeria kunye neIndiya yayiyeyona nto inzima kakhulu.
Ngokuthelekisa inani lokuhlaselwa kwe-cyber, sinokubona ukuba i-Ryuk iye yachaphazela izigidi zabasebenzisi kwaye ibeka esichengeni isixa esikhulu sedatha, okukhokelela ekulahlekelweni okukhulu kwezoqoqosho.
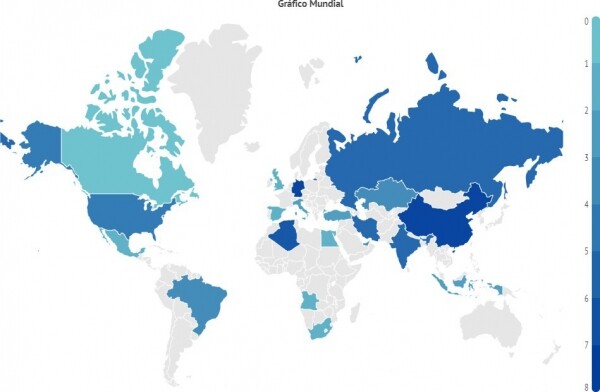
Irayisi. 3: Umzekeliso womsebenzi kaRyuk kwihlabathi jikelele.
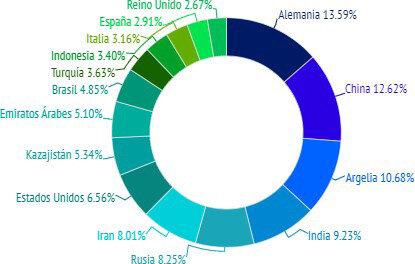
Irayisi. I-4: Amazwe e-16 achaphazeleka kakhulu yiRyuk
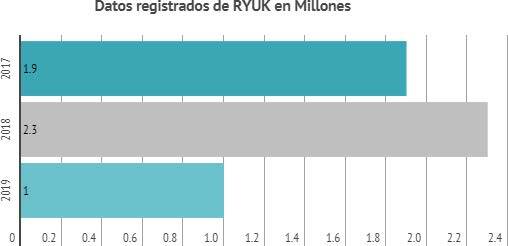
Irayisi. 5: Inani labasebenzisi abahlaselwe yiRyuk ransomware (kwizigidi)
Ngokomgaqo oqhelekileyo wokusebenza wezoyikiso ezinjalo, le ntlawulo, emva kokuba i-encryption igqityiwe, ibonisa ixhoba isaziso sentlawulelo esimele sihlawulwe kwii-bitcoins kwidilesi echaziweyo ukubuyisela ukufikelela kwiifayile ezifihliweyo.
Le malware itshintshile ukusukela oko yaziswa okokuqala.
Ukwahluka kwesi soyikiso esihlalutywe kolu xwebhu kwafunyanwa ngexesha lokuzama ukuhlasela ngoJanuwari ka-2020.
Ngenxa yokuntsokotha kwayo, le malware idla ngokubalelwa kumaqela olwaphulo-mthetho olulungelelanisiweyo, aziwa njengamaqela e-APT.
Inxalenye yekhowudi ye-Ryuk inokufana okubonakalayo kwikhowudi kunye nesakhiwo senye i-ransomware eyaziwayo, iHermes, apho babelana khona ngenani lemisebenzi efanayo. Kungenxa yoko le nto uRyuk wayedityaniswa okokuqala neqela laseNyakatho Korea uLazaro, ngelo xesha kwakurhanelwa ukuba usemva kweHermes ransomware.
Inkonzo ye-CrowdStrike's Falcon X emva koko yaqaphela ukuba i-Ryuk ngokwenene yenziwe liqela le-WIZARD SPIDER [4].
Kukho ubungqina obuxhasa le ngcinga. Okokuqala, le ransomware yapapashwa kwiwebhusayithi exploit.in, eyaziwa ngokuba yindawo yokuthengisa ye-malware yaseRashiya kwaye sele inxulunyaniswe namaqela athile e-APT aseRashiya.
Le nyaniso ilawula ingcamango yokuba i-Ryuk yayinokuthi iphuhliswe liqela likaLazaro APT, kuba ayihambelani nendlela iqela elisebenza ngayo.
Ukongezelela, i-Ryuk yapapashwa njenge-ransomware engayi kusebenza kwiinkqubo zaseRashiya, e-Ukraine naseBelarusian. Oku kuziphatha kugqitywa ngumsebenzi ofunyenwe kwezinye iinguqulelo ze-Ryuk, apho ihlola ulwimi lwenkqubo apho i-ransomware isebenza khona kwaye iyayimisa ukuba ingaqhubeki ukuba inkqubo inolwimi lwesiRashiya, isi-Ukrainian okanye isiBelarusian. Ekugqibeleni, uhlalutyo lobuchwephesha bomatshini obuqhekezwe liqela le-WIZARD SPIDER libonise "izinto zakudala" ezininzi ezithi zisetyenziswe ekuphuhliseni iRyuk njengokwahluka kweHermes ransomware.
Ngakolunye uhlangothi, iingcali uGabriela Nicolao kunye noLuciano Martins bacebise ukuba i-ransomware ingaba yaphuhliswa liqela le-APT CryptoTech [5].
Oku kulandela ukuba kwiinyanga ezimbalwa ngaphambi kokubonakala kweRyuk, eli qela lithumele ulwazi kwiforum yendawo efanayo ukuba baphuhlise inguqu entsha yeHermes ransomware.
Abasebenzisi abaninzi beforum babuza ukuba ngaba i-CryptoTech ngokwenene yakha iRyuk. Iqela ke lazithethelela kwaye lathi linobungqina bokuba baye baphuhlisa i-100% ye-ransomware.
2. Iimpawu
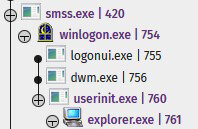
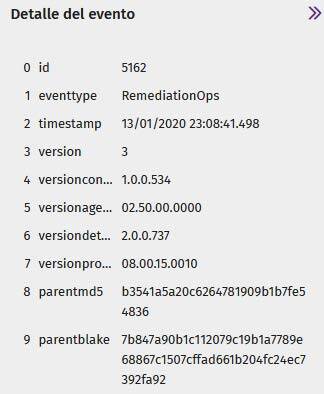
Siqala nge-bootloader, umsebenzi wayo kukuchonga inkqubo ekhoyo ukuze inguqulelo "echanekileyo" ye-Ryuk ransomware iqaliswe.
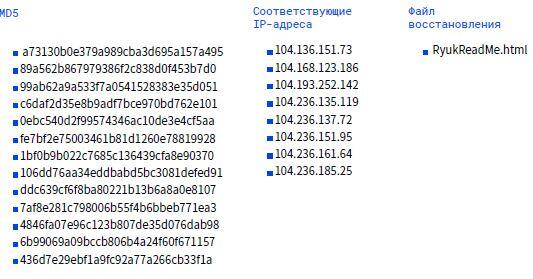
I-hash ye-bootloader ihamba ngolu hlobo lulandelayo:
MD5 A73130B0E379A989CBA3D695A157A495
SHA256 EF231EE1A2481B7E627921468E79BB4369CCFAEB19A575748DD2B664ABC4F469
Enye yeempawu zalo mkhupheli kukuba ayinayo nayiphi na i-metadata, okt. Abadali bale malware abafakanga naluphi na ulwazi kuyo.
Ngamanye amaxesha zibandakanya idatha ephosakeleyo ukukhohlisa umsebenzisi ukuba acinge ukuba baqhuba isicelo esisemthethweni. Nangona kunjalo, njengoko siza kubona kamva, ukuba usulelo alubandakanyi ukusebenzisana komsebenzisi (njengoko kunjalo ngale ntlangulo), ke abahlaseli ababoni kuyimfuneko ukusebenzisa imethadatha.

Irayisi. 6: Isampulu yedatha yeMeta
Isampulu ihlanganiswe kwifomathi ye-32-bit ukwenzela ukuba isebenze kuzo zombini iinkqubo ze-32-bit kunye ne-64-bit.
3. Vector yokungena
Isampulu ekhuphela kwaye iqhube i-Ryuk ingene kwinkqubo yethu ngoqhagamshelo olukude, kwaye iiparamitha zokufikelela zifunyenwe ngohlaselo lokuqala lwe-RDP.
Irayisi. I-7: Irejista yokuhlaselwa
Umhlaseli ukwazile ukungena kwisistim ekude. Emva koko, wenza ifayile ephunyezwayo kunye nesampulu yethu.
Le fayile ephunyezwayo ivalwe sisisombululo se-antivirus phambi kokuba isebenze.

Irayisi. 8: Isitshixo sepateni
Irayisi. 9: Isitshixo sepateni
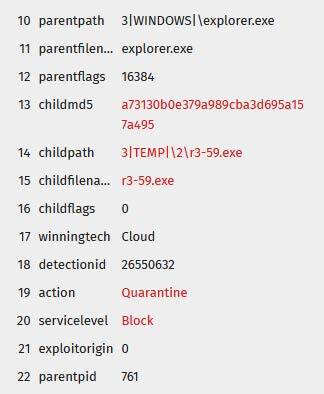
Xa ifayile enobungozi ivaliwe, umhlaseli uzame ukukhuphela uguqulelo olufihliweyo lwefayile ephunyeziweyo, nayo ivaliwe.
Irayisi. 10: Iseti yeesampulu umhlaseli azame ukuziqhuba
Ekugqibeleni, wazama ukukhuphela enye ifayile ekhohlakeleyo nge-encrypted console
I-PowerShell yokugqitha ukhuseleko lwe-antivirus. Kodwa naye wavinjwa.
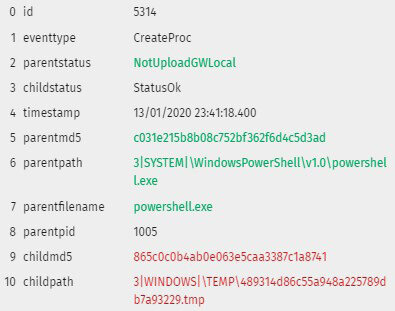
Irayisi. 11: I-PowerShell enomxholo onobungozi ivaliwe

Irayisi. 12: I-PowerShell enomxholo onobungozi ivaliwe
4. Umlayishi
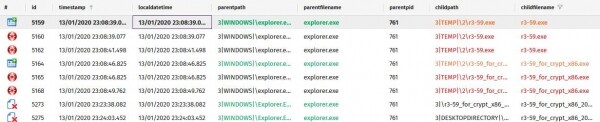
Xa iphumeza, ibhala ifayile yeReadMe kwisiqulathi seefayili % yexeshana%, eqhelekileyo kwiRyuk. Le fayile linqaku lentlawulelo eliqulethe idilesi ye-imeyile kwisizinda seprotonmail, exhaphake kakhulu kolu sapho lwe-malware: msifelabem1981@protonmail.com
![]()

Irayisi. 13: Imfuneko Yentlawulelo
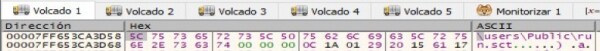
Ngelixa i-bootloader isebenza, uyabona ukuba iqalisa iifayile ezininzi eziphunyeziweyo ezinamagama angaqhelekanga. Zigcinwa kwifolda efihliweyo LOLUNTU, kodwa ukuba ukhetho alusebenzi kwindlela yokusebenza "Bonisa iifayile ezifihliweyo kunye neefolda", ngoko ziya kuhlala zifihliwe. Ngaphezu koko, ezi fayile ziyi-64-bit, ngokungafaniyo nefayile yomzali, eyi-32-bit.
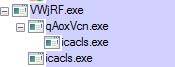
Irayisi. I-14: Iifayile eziphunyeziweyo eziqaliswe yisampuli
Njengoko unokubona kumfanekiso ongentla, i-Ryuk isungula icacls.exe, eya kusetyenziswa ukuguqula zonke ii-ACLs (Uluhlu lolawulo lokufikelela), ngaloo ndlela iqinisekisa ukufikelela kunye nokuguqulwa kweeflegi.
Ifumana ukufikelela ngokupheleleyo phantsi kwabo bonke abasebenzisi kuzo zonke iifayile kwisixhobo (/ T) kungakhathaliseki iimpazamo (/ C) kwaye ngaphandle kokubonisa nayiphi na imiyalezo (/ Q).
![]()
Irayisi. I-15: Iiparamitha zokwenziwa kwe-icacls.exe ziqaliswe yisampuli
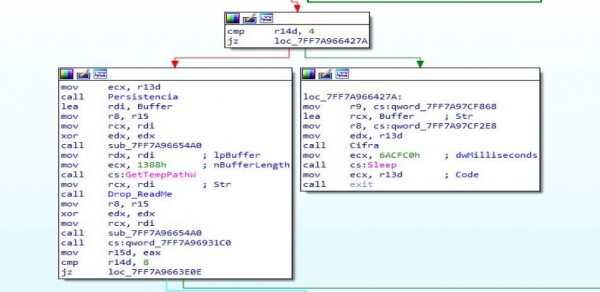
Kubalulekile ukuqaphela ukuba iRyuk ijonga ukuba yeyiphi na inguqulelo yeWindows oyisebenzisayo. Ngenxa yoko
yenza uqwalaselo loguqulelo usebenzisa GetVersionExW, apho ijonga ixabiso leflegi lpVersionInformationebonisa ukuba uguqulelo lwangoku lweWindows lutsha kune XP Windows.
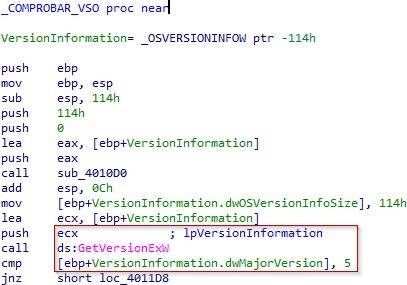
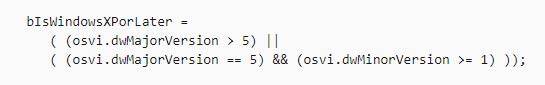
Kuxhomekeka ekubeni usebenzisa uguqulelo mva kune Windows XP, umlayishi wesiqalo uya kubhala kulawulo lomsebenzisi wasekhaya - kulo mzekelo ukuya kwincwadi eneenkcukacha. Uluntu%.
![]()
Irayisi. 17: Ukujonga uguqulelo lwenkqubo yokusebenza
Ifayile ebhaliweyo nguRyuk. Emva koko iyayiqhuba, igqithisa idilesi yayo njengeparamitha.
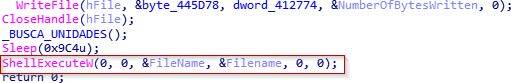
Irayisi. 18: Phumeza iRyuk ngeShellExecute
Into yokuqala eyenziwa nguRyuk kukufumana iiparamitha zokufaka. Ngeli xesha kukho iiparameters zegalelo ezimbini (i-executable ngokwayo kunye nedilesi yedropha) ezisetyenziselwa ukususa umkhondo wayo.
![]()
![]()
Irayisi. 19: Ukudala Inkqubo
Ungabona kwakhona ukuba xa sele iqhube ukuphunyezwa kwayo, izicima ngokwayo, ngaloo ndlela ingashiyi mkhondo wobukho bayo kwincwadi apho yenziwe khona.
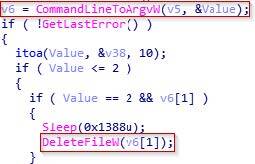
Irayisi. 20: Ukucima ifayile
5. I-RYUK
5.1 Ubukho
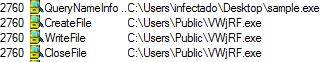
I-Ryuk, njengenye i-malware, izama ukuhlala kwinkqubo ixesha elide. Njengoko kubonisiwe ngasentla, enye indlela yokufezekisa le njongo kukudala ngokufihlakeleyo kwaye usebenzise iifayile eziphunyeziweyo. Ukwenza oku, eyona nto ixhaphakileyo kukutshintsha iqhosha lokubhalisa UkuGqibela ngoku.
Kule meko, unokubona ukuba ngenxa yale njongo ifayile yokuqala eza kusungulwa VWjRF.exe
(igama lefayile lenziwe ngokungenamkhethe) indululwa cmd.exe.
![]()
Irayisi. 21: Ukwenza i-VWjRF.exe
Emva koko faka umyalelo RUN Ngegama"iisvchos". Ngaloo ndlela, ukuba ufuna ukukhangela izitshixo zokubhalisa nangaliphi na ixesha, unokuphosakela ngokulula olu tshintsho, unikwe ukufana kweli gama kunye ne-svchost. Ndiyabulela kwesi sitshixo, i-Ryuk iqinisekisa ubukho bayo kwinkqubo. Ukuba inkqubo ayizange Ususulelekile , ngoko xa uqala kwakhona inkqubo, ephunyeziweyo izakuzama kwakhona.
![]()
Irayisi. 22: Isampuli iqinisekisa ubukho kwiqhosha lokubhalisa
Singabona kwakhona ukuba oku kuphunyezwa kumisa iinkonzo ezimbini:
"umakhi we-audioendpoint", ethi, njengoko igama layo libonisa, ihambelana nenkqubo yomsindo,
![]()
Irayisi. 23: Isampulu imisa inkonzo yomsindo wenkqubo
и Samss, eyinkonzo yolawulo lweakhawunti. Ukumisa ezi nkonzo zimbini luphawu lweRyuk. Kule meko, ukuba inkqubo iqhagamshelwe kwinkqubo ye-SIEM, iransomware izama ukuyeka ukuthumela kuyo naziphi na izilumkiso. Ngale ndlela, ukhusela amanyathelo akhe alandelayo kuba ezinye iinkonzo ze-SAM aziyi kukwazi ukuqala umsebenzi wazo ngokuchanekileyo emva kokwenza iRyuk.
![]()
Irayisi. 24: Isampulu iyeka inkonzo ye-Samss
5.2 Amalungelo awodwa
Ngokubanzi, iRyuk iqala ngokuhamba ecaleni ngaphakathi kwenethiwekhi okanye iqaliswe yenye i-malware enje okanye , ethi, kwimeko yokunyuka kwamalungelo, idlulisele la malungelo aphakamileyo kwi-ransomware.
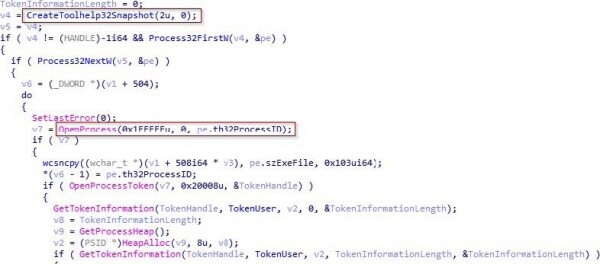
Ngaphambili, njengesandulela senkqubo yokuphunyezwa, simbona eqhuba inkqubo Zifanise, okuthetha ukuba imixholo yokhuseleko yophawu lofikelelo iya kugqithiselwa kumsinga, apho iya kufunyanwa ngokukhawuleza kusetyenziswa. GetCurrentTread.
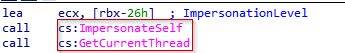
Irayisi. 25: Fowunela Uzenze
Emva koko siyabona ukuba iya kudibanisa ithokheni yokufikelela kunye nomsonto. Siyabona kwakhona ukuba enye yeeflegi DesiredAccess, enokusetyenziswa ukulawula ukufikelela apho umsonto uya kuba nawo. Kule meko ixabiso eliza kufumana i-edx kufuneka libe TOKEN_ALL_ACESS okanye ngenye indlela- TOKEN_BHALA.
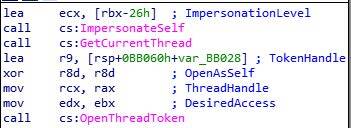
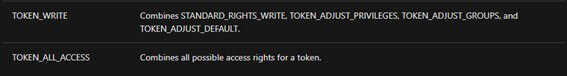
Irayisi. I-26: Ukudala iToken Flow
Emva koko uya kusebenzisa SeDebugPrivilege kwaye izakwenza umnxeba ukufumana iimvume ze Debug kumsonto, okukhokelela kwi PROCESS_ALL_FIKELELO, uya kukwazi ukufikelela kuyo nayiphi na inkqubo efunekayo. Ngoku, ngenxa yokuba i-encryptor sele inomsinga olungisiweyo, konke okuseleyo kukuqhubela phambili kwinqanaba lokugqibela.
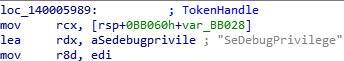
Irayisi. I-27: Ukubiza i-SeDebugPrivilege kunye nomsebenzi wokunyusa i-Privilege
Kwelinye icala, sine LookupPrivilegeValueW, esinika ulwazi oluyimfuneko malunga namalungelo esifuna ukuwandisa.
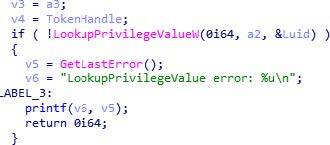
Irayisi. 28: Cela ulwazi malunga namalungelo okunyuka kwamalungelo
Kwelinye icala, sinako AdjustTokenPrivileges, esivumela ukuba sifumane amalungelo ayimfuneko kumjelo wethu. Kule meko, eyona nto ibalulekileyo iNewState, iflegi yabo iya kunika amalungelo.
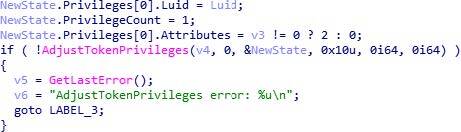
Irayisi. 29: Ukumisela iimvume zophawu
5.3 Ukuphunyezwa
Kweli candelo, siya kubonisa indlela isampuli eyenza ngayo inkqubo yokuphunyezwa ekhankanywe ngaphambili kule ngxelo.
Injongo ephambili yenkqubo yokuphunyezwa, kunye nokunyuka, kukufumana ukufikelela iikopi zesithunzi. Ukwenza oku, kufuneka asebenze ngentambo enamalungelo aphezulu kunalawo omsebenzisi wendawo. Nje ukuba izuze amalungelo aphakamileyo, iya kucima iikopi kwaye yenze utshintsho kwezinye iinkqubo ukuze yenze kube nzima ukubuyela kwindawo yokubuyisela kwangaphambili kwinkqubo yokusebenza.
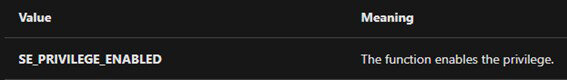
Njengoko kuqhelekile kolu hlobo lwe-malware, luyasebenzisa CreateToolHelp32Snapshotngoko ke ithatha umfanekiso okhawulezayo weenkqubo ezisebenzayo kwaye izama ukufikelela kwezo nkqubo isebenzisa OpenProcess. Emva kokuba ifumene ukufikelela kwinkqubo, iphinda ivule ithokheni ngolwazi lwayo ukuze ifumane iiparameters zenkqubo.
Irayisi. 30: Ukufumana iinkqubo kwikhompyuter
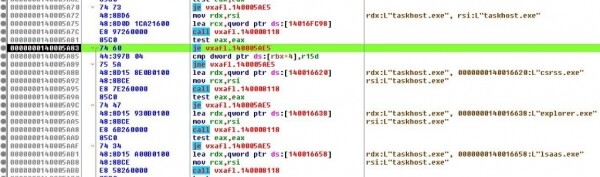
Singabona ngamandla ukuba ilufumana njani uluhlu lweenkqubo ezisebenzayo ngokwesiqhelo 140002D9C usebenzisa i-CreateToolhelp32Snapshot. Emva kokuwafumana, uya kuluhlu, ezama ukuvula iinkqubo nganye nganye usebenzisa i-OpenProcess ade aphumelele. Kule meko, inkqubo yokuqala awakwazi ukuyivula yayi "i-taskhost.exe".
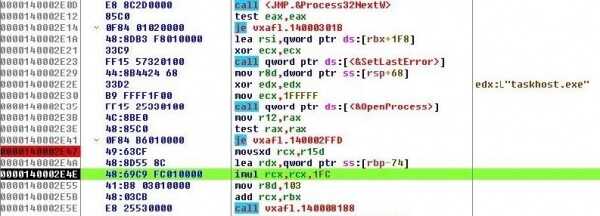
Irayisi. 31: Yenza inkqubo yokuFumana inkqubo
Siyabona ukuba emva koko ifunda inkqubo yolwazi lwethokheni, ngoko iyabiza OpenProcessToken ngeparameter"20008"
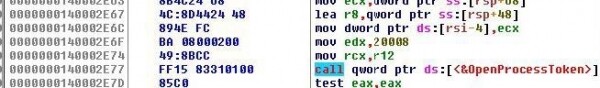
Irayisi. 32: Funda ulwazi lwethokheni yenkqubo
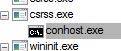
Ikwajonga kwakhona ukuba inkqubo eza kugalelwa kuyo ayikho na csrs.exe, explorer.exe, lsaas.exe okanye uneqela lamalungelo Igunya le-NT.
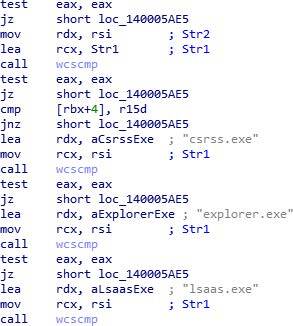
Irayisi. 33: Iinkqubo ezingabandakanywayo
Siyakwazi ukubona ngamandla ukuba yenza njani kuqala itshekhi usebenzisa ulwazi lwenkqubo yophawu kwi 140002D9C ukuze ufumanise ukuba i-akhawunti emalungelo asetyenziswayo ukwenza inkqubo yi-akhawunti NT IGUNYA.
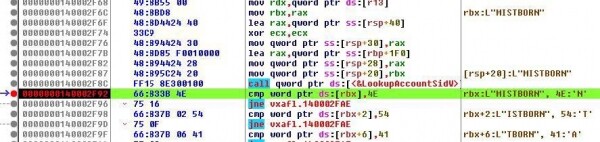
Irayisi. 34: NT UGUNYAZISO khangela
Kwaye kamva, ngaphandle kwenkqubo, ujonga ukuba oku akunjalo csrss.exe, explorer.exe okanye lsaas.exe.
Irayisi. 35: NT UGUNYAZISO khangela
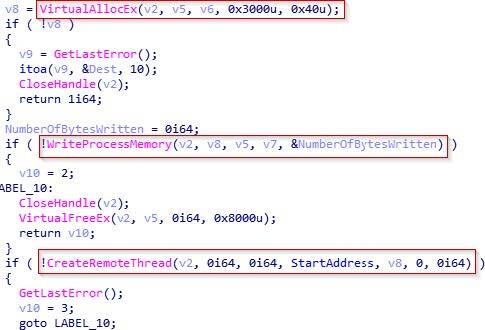
Emva kokuba ethathe i-snapshot yeenkqubo, wavula iinkqubo, kwaye waqinisekisa ukuba akukho namnye kubo ongabandakanyiweyo, ulungele ukubhala kwimemori iinkqubo eziya kujovwa.
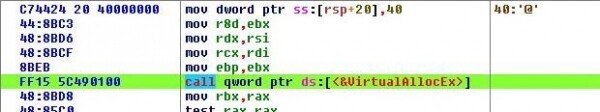
Ukwenza oku, kuqala igcina indawo kwinkumbulo (VirtualAllocEx), ubhala kuyo (WriteProcessmemory) kwaye yenza umsonto (Yenza iRemoteThread). Ukusebenza ngale misebenzi, isebenzisa ii-PID zeenkqubo ezikhethiweyo, ezifunyenwe ngaphambili CreateToolhelp32Snapshot.
Irayisi. 36: Ikhowudi yokulungisa
Apha sinokujonga ngamandla indlela esisebenzisa ngayo inkqubo ye-PID ukubiza umsebenzi VirtualAllocEx.
Irayisi. 37: Tsalela umnxeba VirtualAllocEx
5.4 Uguqulelo oluntsonkothileyo
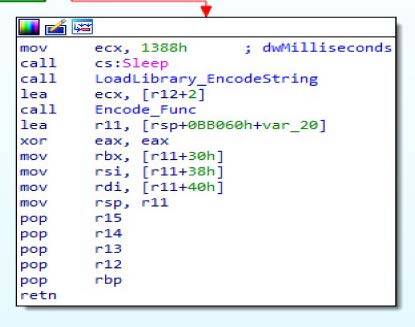
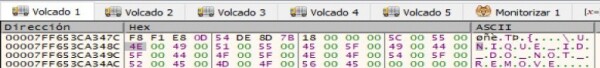
Kweli candelo, siza kujonga inxalenye yoguqulelo oluntsonkothileyo yale sampuli. Kulo mfanekiso ulandelayo unokubona ii-subroutines ezimbini ezibizwa ngokuba "LayishaLibrary_EncodeString"Kwaye"Encode_Func", abanoxanduva lokwenza inkqubo yoguqulelo oluntsonkothileyo.
Irayisi. 38: Iinkqubo zofihlo
Ekuqaleni sinokubona indlela elayisha ngayo umtya eya kuthi kamva isetyenziswe ukwenza i-deobfuscate yonke into efunekayo: ukungenisa, iiDLL, imiyalelo, iifayile kunye neeCSP.
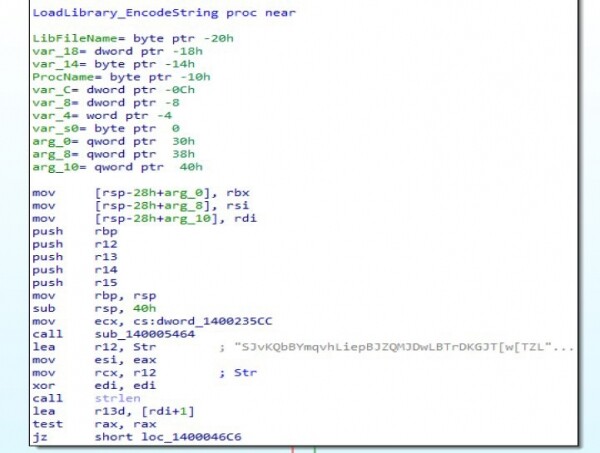
Irayisi. 39: Isekethe ye-deobfuscation
Lo mzobo ulandelayo ubonisa into yokuqala yokungeniswa ngaphandle kwelizwe iyenza ibe lula kwirejista ye-R4. Umthwalo weLayibrari. Oku kuya kusetyenziswa kamva ukulayisha iiDLL ezifunekayo. Kwakhona sinokubona omnye umgca kwirejista ye-R12, esetyenziswa kunye nomgca wangaphambili ukwenza i-deobfuscation.
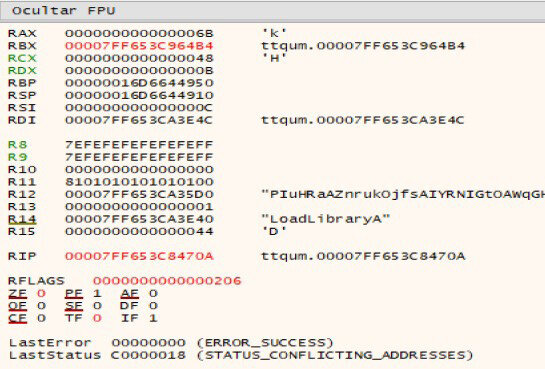
Irayisi. 40: I-deobfuscation enamandla
Iyaqhubeka nokukhuphela imiyalelo eya kuqhuba kamva ukukhubaza ii-backups, ukubuyisela amanqaku, kunye neendlela ezikhuselekileyo zokuqalisa.
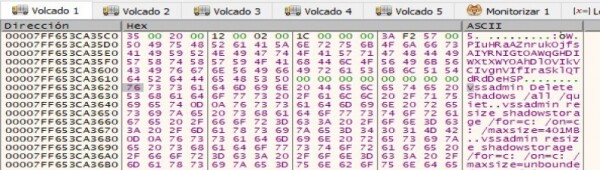
Irayisi. 41: Ilayisha imiyalelo
Emva koko ilayisha indawo apho iya kulahla iifayile ezi-3: Windows.bat, run.sct и qala.bat.
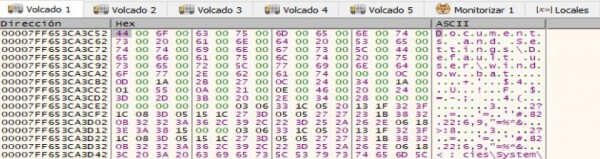
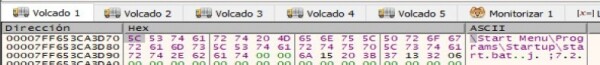
Irayisi. 42: Iindawo zeefayile
Ezi fayile zi-3 zisetyenziselwa ukujonga amalungelo apho indawo nganye enayo. Ukuba amalungelo afunekayo awafumaneki, uRyuk uyayeka ukubulawa.
Iyaqhubeka nokulayisha imigca ehambelana neefayile ezintathu. Ekuqaleni, DECRYPT_INFORMATION.html, iqulethe ulwazi oluyimfuneko ukubuyisela iifayile. Isibini, LOLUNTU, iqulethe isitshixo sikawonke-wonke saseRSA.
Irayisi. 43: Umgca DECRYPT INFORMATION.html
Isithathu, UNIQUE_ID_DO_NOT_REMOVE, iqulethe iqhosha elifihliweyo eliza kusetyenziswa kwindlela elandelayo ukwenza uguqulelo oluntsonkothileyo.
Irayisi. 44: Umgca UNIQUE ID SUKUSUSA
Okokugqibela, ikhuphela iilayibrari ezifunekayo kunye nezinto ezifunwayo ngaphandle kunye neeCSPs (Microsoft Ephuculweyo RSA и I-AES Cryptographic Provider).
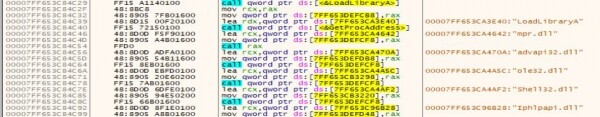
Irayisi. 45: Ukulayisha amathala eencwadi
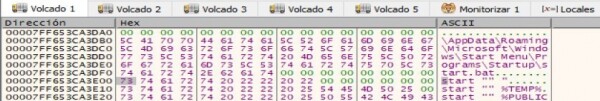
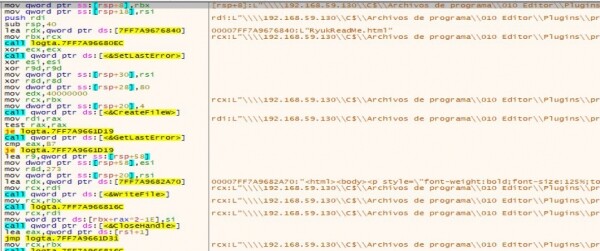
Emva kokuba yonke i-deobfuscation igqityiwe, iqhubela phambili ukwenza izenzo ezifunekayo kuguqulelo oluntsonkothileyo: ukubala zonke iidrive ezinengqiqo, ukwenza oko kwakulayishwe kwindlela yangaphambili, ukomeleza ubukho kwinkqubo, ukuphosa ifayile yeRyukReadMe.html, uguqulelo oluntsonkothileyo, ukubala zonke iidrive zenethiwekhi. , ukutshintshela kwizixhobo ezichongiweyo kunye ne-encryption yazo.
Yonke into iqala ngokulayisha"cmd.exe" kunye neerekhodi eziphambili zoluntu zaseRSA.
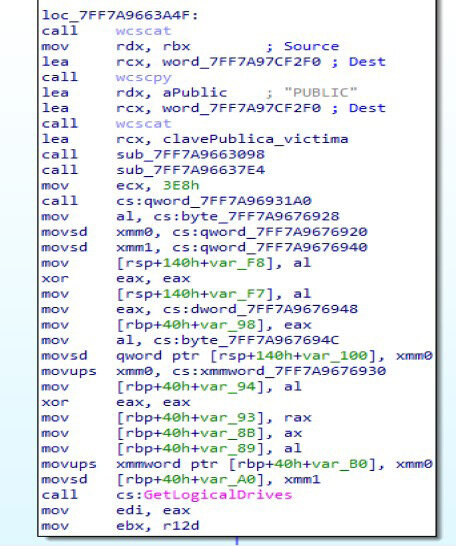
Irayisi. 46: Ukulungiselela uguqulelo oluntsonkothileyo
Emva koko ifumana zonke iidrive ezinengqiqo usebenzisa GetLogicalDrives kwaye ikhubaza zonke ii-backups, ukubuyisela amanqaku kunye neendlela ezikhuselekileyo zokuqalisa.
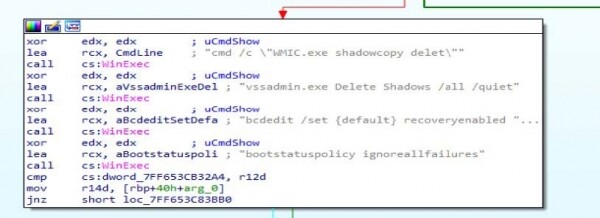
Irayisi. I-47: Ukucima izixhobo zokubuyisela
Emva koko, iqinisa ubukho bayo kwinkqubo, njengoko sibonile ngasentla, kwaye ibhala ifayile yokuqala RyukReadMe.html в I-TEMP.
Irayisi. 48: Ukupapasha isaziso sentlawulelo
Kulo mfanekiso ulandelayo unokubona indlela eyenza ngayo ifayile, ukhuphele umxholo kwaye uwubhale:
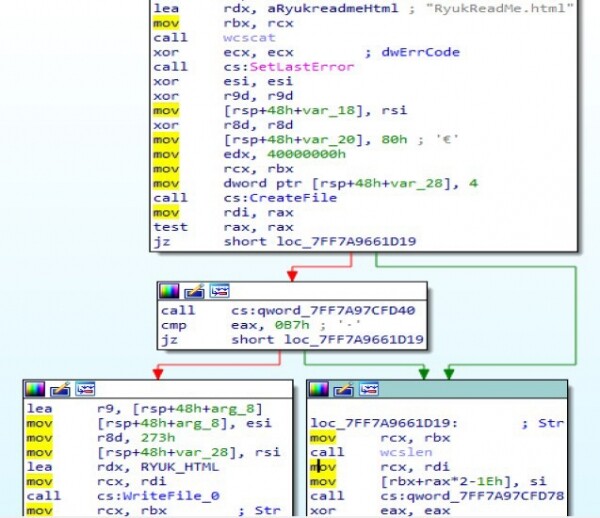
Irayisi. 49: Ukulayisha nokubhala imixholo yeefayile
Ukuze ukwazi ukwenza izenzo ezifanayo kuzo zonke izixhobo, usebenzisa
"icacls.exe", njengoko sibonisile ngasentla.

Irayisi. 50: Ukusebenzisa icalcls.exe
Kwaye ekugqibeleni, iqala ukufihla iifayile ngaphandle kwe "* .exe", "* .dll" iifayile, iifayile zenkqubo kunye nezinye iindawo ezichazwe ngendlela yoluhlu olumhlophe olufihliweyo. Ukwenza oku, isebenzisa iimveliso ezivela ngaphandle: CryptAcquireContextW (apho kukhankanyiwe ukusetyenziswa kwe-AES neRSA), CryptDeriveKey, CryptGenKey, I-CryptDestroyKey njl. Ikwazama ukwandisa ukufikelela kwayo kwizixhobo zenethiwekhi ezifunyenweyo zisebenzisa i-WNetEnumResourceW kwaye emva koko zifihlwe.
Irayisi. 51: Iifayile zenkqubo yokufihla
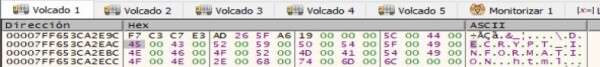
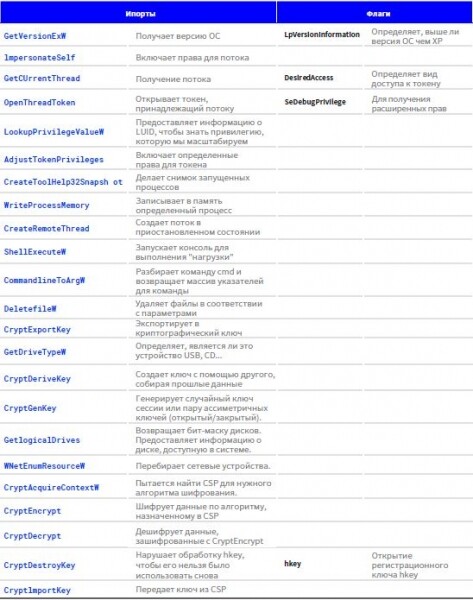
6. Ukungenisa kunye neeflegi ezihambelanayo
Ngezantsi ludweliso lwetheyibhile edwelisa ezona mpahla zisuka ngaphandle kunye neeflegi ezisetyenziswe yisampuli:
7. IOC
iimbekiselo
- abasebenzisiPublicrun.sct
- Qalisa iMenuProgramsStartupstart.bat AppDataRoamingMicrosoftWindowsStart
- MenuProgramsStartupstart.bat

Ingxelo yobugcisa kwi-Ryuk ransomware yaqulunqwa ziingcali ezivela kwi-antivirus laboratory PandaLabs.
8. Amakhonkco
1. “Everis y Prisa Radio sufren un grave ciberataque que secuestra sus sistemas.”https://www. elconfidencial.com/tecnologia/2019-11-04/everis-la-ser-ciberataque-ransomware-15_2312019/, Publicada el 04/11/2019.
2. “Un virus de origen ruso ataca a importantes empresas españolas.” https://elpais.com/tecnologia/2019/11/04/actualidad/1572897654_ 251312.html, Publicada el 04/11/2019.
3. “Iphepha le-VB2019: impindezelo kaShinigami: umsila omde weRyuk malware.” https://securelist.com/story-of-the-year-2019-cities-under-ransomware-siege/95456/, Publicada el 11 /12/2019
4. "Ukuzingela umdlalo omkhulu kunye ne-Ryuk: Enye i-LucrativebTargeted Ransomware."https://www. crowdstrike.com/blog/big-game-hunting-with-ryuk-another-lucrative-targeted-ransomware/, Publicada el 10/01/2019.
5. “Iphepha le-VB2019: impindezelo kaShinigami: umsila omde weRyuk malware.” https://www. virusbulletin.com/virusbulletin/2019/10/ vb2019-paper-shinigamis-revenge-long-tail-r
umthombo: www.habr.com


