
Wani lokaci bayan rubutu , Inda na sarrafa jsonnet da gitlab, na gane cewa bututun bututun suna da kyau, amma ba dole ba ne masu rikitarwa da rashin dacewa.
A mafi yawan lokuta, ana buƙatar aiki na yau da kullun: "ƙirƙira YAML kuma sanya shi cikin Kubernetes." A zahiri, wannan shine abin da Argo CD yayi kyau sosai.
Argo CD yana ba ku damar haɗa ma'ajiyar Git kuma aika jiharsa zuwa Kubernetes. Ta hanyar tsoho, akwai tallafi don nau'ikan aikace-aikace da yawa: Kustomize, Helm Charts, Ksonnet, bare Jsonnet, ko kundayen adireshi kawai tare da bayyanar YAML/JSON.
Wannan saitin zai isa ga yawancin masu amfani, amma ba ga kowa ba. Domin biyan bukatun kowa da kowa, Argo CD yana da ikon yin amfani da kayan aiki na al'ada.
Da farko, Ina sha'awar yiwuwar ƙara tallafi и , waɗanda aka tattauna sosai a labarin da ya gabata.
Kafin ka fara daidaitawa, da farko kuna buƙatar fahimtar ainihin yadda Argo CD ke aiki.
Ga kowane ƙarin aikace-aikacen, yana da matakai biyu:
- init - shirye-shiryen farko kafin turawa, komai na iya faruwa a nan: zazzage abubuwan dogaro, buɗe abubuwan sirri, da ƙari.
- samar da - aiwatar da umarnin tsarar da bayyanuwa kai tsaye, fitarwa dole ne ya zama ingantaccen rafin YAML, wannan shine ainihin abin da za a yi amfani da shi a gungu.
Abin mamaki shine cewa Argo yana amfani da wannan hanyar zuwa kowane nau'in aikace-aikacen, gami da Helm. Wato, a cikin Argo CD Helm ba ya aika da sakewa zuwa gungu, amma ana amfani da shi kawai don haifar da bayyanar.
A nasa bangare, Argo na iya aiwatar da ƙugiya na Helm na asali, wanda ke ba shi damar keta dabarun aiwatar da sakewa.
QBEC
Qbec yana ba ku damar siffanta aikace-aikacen da kyau ta amfani da jsonnet, kuma ƙari yana da ikon yin ginshiƙi na Helm, kuma tunda Argo CD na iya aiwatar da ƙugiya na Helm kullum, ta amfani da wannan fasalin tare da CD ɗin Argo yana ba ku damar samun ƙarin sakamako daidai.
Don ƙara tallafin qbec zuwa argocd kuna buƙatar abubuwa biyu:
- A cikin saitin CD na Argo, plugin ɗin ku na al'ada da umarni don ƙirƙirar bayyanar dole ne a bayyana.
- dole ne binaries da ake bukata su kasance a cikin hoton argocd-repo-server.
Aiki na farko kyakkyawa mai sauki:
# cm.yaml
data:
configManagementPlugins: |
- name: qbec
generate:
command: [sh, -xc]
args: ['qbec show "$ENVIRONMENT" -S --force:k8s-namespace "$ARGOCD_APP_NAMESPACE"'](Tawagar init ba a amfani)
$ kubectl -n argocd patch cm/argocd-cm -p "$(cat cm.yaml)"Don ƙara binaries ana ba da shawarar , ko amfani :
# deploy.yaml
spec:
template:
spec:
# 1. Define an emptyDir volume which will hold the custom binaries
volumes:
- name: custom-tools
emptyDir: {}
# 2. Use an init container to download/copy custom binaries into the emptyDir
initContainers:
- name: download-tools
image: alpine:3.12
command: [sh, -c]
args:
- wget -qO- https://github.com/splunk/qbec/releases/download/v0.12.2/qbec-linux-amd64.tar.gz | tar -xvzf - -C /custom-tools/
volumeMounts:
- mountPath: /custom-tools
name: custom-tools
# 3. Volume mount the custom binary to the bin directory (overriding the existing version)
containers:
- name: argocd-repo-server
volumeMounts:
- mountPath: /usr/local/bin/qbec
name: custom-tools
subPath: qbec
- mountPath: /usr/local/bin/jsonnet-qbec
name: custom-tools
subPath: jsonnet-qbec$ kubectl -n argocd patch deploy/argocd-repo-server -p "$(cat deploy.yaml)"Yanzu bari mu ga yadda aikace-aikacen mu zai yi kama da:
apiVersion: argoproj.io/v1alpha1
kind: Application
metadata:
name: qbec-app
namespace: argocd
spec:
destination:
namespace: default
server: https://kubernetes.default.svc
project: default
source:
path: qbec-app
plugin:
env:
- name: ENVIRONMENT
value: default
name: qbec
repoURL: https://github.com/kvaps/argocd-play
syncPolicy:
automated:
prune: trueA cikin m HAUSA mu wuce sunan yanayin da muke buƙatar samar da bayyanar cututtuka.
mu yi amfani da shi mu ga abin da muka samu:
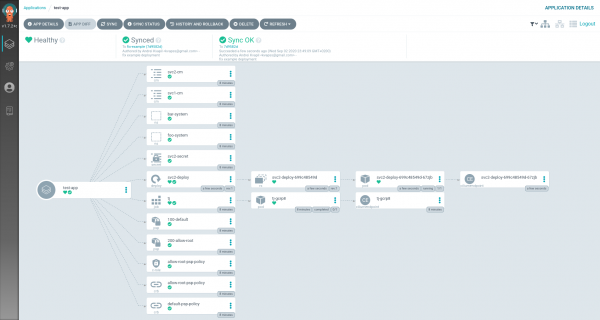
An tura aikace-aikacen, mai girma!
git-crypt
Git-crypt yana ba ku damar saita ɓoye bayanan sirri don ma'ajiyar ku. Hanya ce mai sauƙi kuma amintaccen don adana mahimman bayanai kai tsaye a cikin git.
Aiwatar da git-crypt ya zama mafi wahala.
A ka'ida za mu iya yi git-crypt unlock a matakin farko na plugin ɗin mu na al'ada, amma wannan bai dace sosai ba, tunda ba zai ƙyale amfani da hanyoyin turawa na asali ba. Misali, game da Helm da Jsonnet, mun rasa madaidaicin GUI mai sauƙi wanda ke ba mu damar sauƙaƙe tsarin aikace-aikacen (fayilolin ƙimar, da sauransu).
Wannan shine dalilin da ya sa na so in buga ma'ajiyar a wani mataki na farko, a lokacin cloning.
Tunda a halin yanzu Argo CD baya ba da ikon kwatanta kowane ƙugiya don daidaita ma'ajiyar, dole ne mu kusanci wannan iyakance tare da rubutun harsashi mai rikitarwa wanda ya maye gurbin umarnin git:
#!/bin/sh
$(dirname $0)/git.bin "$@"
ec=$?
[ "$1" = fetch ] && [ -d .git-crypt ] || exit $ec
GNUPGHOME=/app/config/gpg/keys git-crypt unlock 2>/dev/null
exit $ecArgo CD yayi git fetch kowane lokaci kafin aikin turawa. Wannan umarni ne za mu sanya kisa git-crypt unlock don buɗe ma'ajiyar.
don gwaje-gwajen da za ku iya amfani da su wanda ya riga ya sami duk abin da kuke buƙata:
$ kubectl -n argocd set image deploy/argocd-repo-server argocd-repo-server=docker.io/kvaps/argocd-git-crypt:v1.7.3Yanzu muna buƙatar yin tunanin yadda Argo zai lalata ma'ajiyar mu. Wato, samar da maɓallin gpg don shi:
$ kubectl exec -ti deploy/argocd-repo-server -- bash
$ printf "%sn"
"%no-protection"
"Key-Type: default"
"Subkey-Type: default"
"Name-Real: YOUR NAME"
"Name-Email: YOUR EMAIL@example.com"
"Expire-Date: 0"
> genkey-batch
$ gpg --batch --gen-key genkey-batch
gpg: WARNING: unsafe ownership on homedir '/home/argocd/.gnupg'
gpg: keybox '/home/argocd/.gnupg/pubring.kbx' created
gpg: /home/argocd/.gnupg/trustdb.gpg: trustdb created
gpg: key 8CB8B24F50B4797D marked as ultimately trusted
gpg: directory '/home/argocd/.gnupg/openpgp-revocs.d' created
gpg: revocation certificate stored as '/home/argocd/.gnupg/openpgp-revocs.d/9A1FF8CAA917CE876E2562FC8CB8B24F50B4797D.rev'Mu ajiye mabuɗin suna 8CB8B24F50B4797D don ƙarin matakai. Fitar da maɓallin da kanta:
$ gpg --list-keys
gpg: WARNING: unsafe ownership on homedir '/home/argocd/.gnupg'
/home/argocd/.gnupg/pubring.kbx
-------------------------------
pub rsa3072 2020-09-04 [SC]
9A1FF8CAA917CE876E2562FC8CB8B24F50B4797D
uid [ultimate] YOUR NAME <YOUR EMAIL@example.com>
sub rsa3072 2020-09-04 [E]
$ gpg --armor --export-secret-keys 8CB8B24F50B4797DKuma ƙara shi azaman sirri daban:
# argocd-gpg-keys-secret.yaml
apiVersion: v1
kind: Secret
metadata:
name: argocd-gpg-keys-secret
namespace: argocd
stringData:
8CB8B24F50B4797D: |-
-----BEGIN PGP PRIVATE KEY BLOCK-----
lQVYBF9Q8KUBDACuS4p0ctXoakPLqE99YLmdixfF/QIvXVIG5uBXClWhWMuo+D0c
ZfeyC5GvH7XPUKz1cLMqL6o/u9oHJVUmrvN/g2Mnm365nTGw1M56AfATS9IBp0HH
O/fbfiH6aMWmPrW8XIA0icoOAdP+bPcBqM4HRo4ssbRS9y/i
=yj11
-----END PGP PRIVATE KEY BLOCK-----$ kubectl apply -f argocd-gpg-keys-secret.yamlAbin da ya rage mana shi ne mu jefa shi a cikin akwati argocd-repo-server, don yin wannan, shirya turawa:
$ kubectl -n argocd edit deploy/argocd-repo-serverKuma za mu maye gurbin wanda yake gpg ku girma a kan projected, inda muke nuna sirrinmu:
spec:
template:
spec:
volumes:
- name: gpg-keys
projected:
defaultMode: 420
sources:
- secret:
name: argocd-gpg-keys-secret
- configMap:
name: argocd-gpg-keys-cmArgo CD yana loda maɓallan gpg ta atomatik daga wannan directory lokacin da kwantena ya fara, don haka zai loda maɓallin sirrinmu.
mu duba:
$ kubectl -n argocd exec -ti deploy/argocd-repo-server -- bash
$ GNUPGHOME=/app/config/gpg/keys gpg --list-secret-keys
gpg: WARNING: unsafe ownership on homedir '/app/config/gpg/keys'
/app/config/gpg/keys/pubring.kbx
--------------------------------
sec rsa2048 2020-09-05 [SC] [expires: 2021-03-04]
ED6285A3B1A50B6F1D9C955E5E8B1B16D47FFC28
uid [ultimate] Anon Ymous (ArgoCD key signing key) <noreply@argoproj.io>
sec rsa3072 2020-09-03 [SC]
9A1FF8CAA917CE876E2562FC8CB8B24F50B4797D
uid [ultimate] YOUR NAME <YOUR EMAIL@example.com>
ssb rsa3072 2020-09-03 [E]Mai girma, an loda maɓalli! Yanzu kawai muna buƙatar ƙara Argo CD zuwa ma'ajiyar mu a matsayin mai haɗin gwiwa kuma zai iya yanke shi ta atomatik akan tashi.
Shigo maɓallin zuwa kwamfutar gida:
$ gpg --armor --export-secret 8CB8B24F50B4797D > 8CB8B24F50B4797D.pem
$ gpg --import 8CB8B24F50B4797D.pemMu saita matakin amana:
$ gpg --edit-key 8CB8B24F50B4797D
trust
5Bari mu ƙara argo a matsayin mai haɗin gwiwa zuwa aikinmu:
$ git-crypt add-gpg-user 8CB8B24F50B4797DHanyoyin haɗi:
source: www.habr.com


