Pikeun sababaraha alesan, perlu pikeun ngatur sambungan VPN antara jaringan di VMWare Awan Diréktur jeung mesin Ubuntu misah dina awan. Catetan henteu pura-pura janten pedaran lengkep, éta ngan ukur cara leutik.
Hiji-hijina tulisan ngeunaan topik ieu ti 2015 kapanggih dina Internét "".
Hanjakalna, éta henteu tiasa dianggo sacara langsung, sabab ... Abdi hoyong énkripsi langkung dipercaya, sanés sertipikat anu ditandatanganan diri, sareng konfigurasi anu dijelaskeun henteu bakal damel di tukangeun NAT.
Ku alatan éta, kuring kungsi diuk turun jeung delve kana dokuméntasi.
Salaku dadasar, abdi nyandak hiji config yén kuring geus lila ngagunakeun, anu ngamungkinkeun kuring pikeun nyambungkeun ti ampir sagala OS, tur saukur ditambahkeun sapotong eta anu ngamungkinkeun kuring pikeun nyambung ka NSX Tepi.
Kusabab masang sareng ngonpigurasikeun server Strongswan sapinuhna saluareun wengkuan catetan ieu, hayu atuh tingal .
Janten, hayu urang ngalih langsung ka setélan.
diagram sambungan urang bakal kasampak kawas kieu:
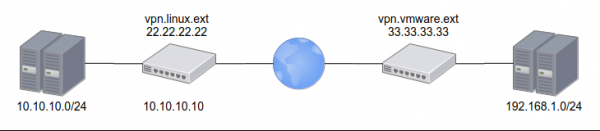
со стороны VMWare внешний адрес 33.33.33.33 и внутренняя сеть 192.168.1.0/24
со стороны Linux внешний адрес 22.22.22.22 и внутренняя сеть 10.10.10.0/24
также понадобится настроить Let's encrypt сертификат для адреса vpn.linux.ext
PSK с обеих сторон: ChangeMeNow!Konfigurasi tina NSX Edge:
Téks
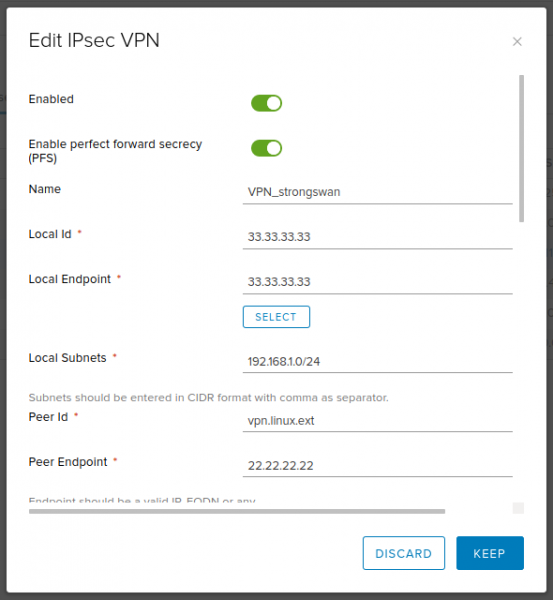
Enabled: yes
Enable perfect forward secrecy (PFS): yes
Name: VPN_strongswan (любое, по вашему выбору)
Local Id: 33.33.33.33
Local Endpoint: 33.33.33.33
Local Subnets: 192.168.1.0/24
Peer Id: vpn.linux.ext
Peer Endpoint: 22.22.22.22
Peer Subnets: 10.10.10.0/24
Encryption Algorithm: AES256
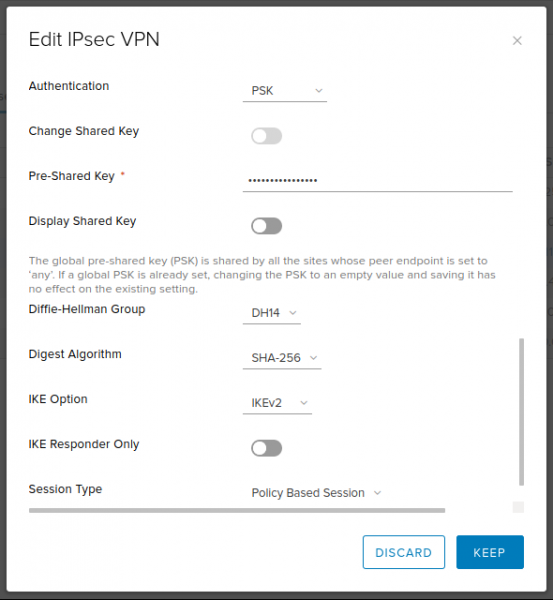
Authentication: PSK
Pre-Shared Key: ChangeMeNow!
Diffie-Hellman Group: 14 (2048 bit — приемлемый компромисс между скоростью и безопасностью. Но если хотите, можете поставить больше)
Digest Algorithm: SHA256
IKE Option: IKEv2
IKE Responder Only: no
Session Type: Policy Based Session Potret layar
Setup ti Strongswan:
ipsec.conf
# /etc/ipsec.conf
config setup
conn %default
dpdaction=clear
dpddelay=35s
dpdtimeout=300s
fragmentation=yes
rekey=no
ike=aes256gcm16-aes256gcm12-aes128gcm16-aes128gcm12-sha256-sha1-modp2048-modp4096-modp1024,aes256-aes128-sha256-sha1-modp2048-modp4096-modp1024,3des-sha1-modp1024!
esp=aes128gcm12-aes128gcm16-aes256gcm12-aes256gcm16-modp2048-modp4096-modp1024,aes128-aes256-sha1-sha256-modp2048-modp4096-modp1024,aes128-sha1-modp2048,aes128-sha1-modp1024,3des-sha1-modp1024,aes128-aes256-sha1-sha256,aes128-sha1,3des-sha1!
left=%any
leftsubnet=10.10.10.0/24
leftcert=certificate.pem
leftfirewall=yes
leftsendcert=always
right=%any
rightsourceip=192.168.1.0/24
rightdns=77.88.8.8,8.8.4.4
eap_identity=%identity
# IKEv2
conn IPSec-IKEv2
keyexchange=ikev2
auto=add
# BlackBerry, Windows, Android
conn IPSec-IKEv2-EAP
also="IPSec-IKEv2"
rightauth=eap-mschapv2
# macOS, iOS
conn IKEv2-MSCHAPv2-Apple
also="IPSec-IKEv2"
rightauth=eap-mschapv2
leftid=vpn.linux.ext
# Android IPsec Hybrid RSA
conn IKEv1-Xauth
keyexchange=ikev1
rightauth=xauth
auto=add
# VMWare IPSec VPN
conn linux-nsx-psk
authby=secret
auto=start
leftid=vpn.linux.ext
left=10.10.10.10
leftsubnet=10.10.10.0/24
rightid=33.33.33.33
right=33.33.33.33
rightsubnet=192.168.1.0/24
ikelifetime=28800
keyexchange=ikev2
lifebytes=0
lifepackets=0
lifetime=1hipsec.rusiah
# /etc/ipsec.secrets
: RSA privkey.pem
# Create VPN users accounts
# ВНИМАНИЕ! После логина сначала пробел, потом двоеточие.
user1 : EAP "stongPass1"
user2 : EAP "stongPass2"
%any 33.33.33.33 : PSK "ChangeMeNow!"sanggeus éta, ngan ulang maca config nu, ngamimitian sambungan jeung pariksa yen eta geus ngadegkeun:
ipsec update
ipsec rereadsecrets
ipsec up linux-nsx-psk
ipsec status Kuring miharep catetan saeutik ieu mantuan sarta ngahemat batur sababaraha jam.
sumber: www.habr.com


